- The paper introduces a deep learning system that integrates a stacked autoencoder within SDN, achieving 95.65% accuracy in multi-class DDoS detection.
- It employs modular components such as a traffic collector, feature extractor, and classifier to differentiate seven distinct DDoS attack types.
- The study demonstrates reduced false positives and suggests future work in hybrid processing models and on-the-fly feature extraction for enhanced scalability.
Deep Learning-Based DDoS Detection in Software-Defined Networking
Introduction
The paper "A Deep Learning Based DDoS Detection System in Software-Defined Networking (SDN)" provides a comprehensive approach to detecting Distributed Denial of Service (DDoS) attacks by leveraging the capabilities of deep learning within an SDN environment. SDN's centralized control and programmability create an optimal setting for deploying adaptive cybersecurity measures. The study integrates a Stacked Autoencoder (SAE) deep learning model with SDN to enhance real-time detection and classification of multi-vector DDoS attacks, a growing concern for networked systems.
System Architecture and Methodology
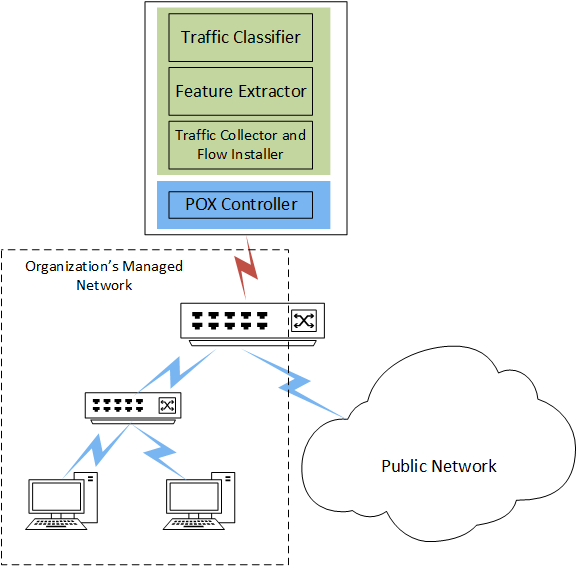
The detection system proposed is implemented as an application on the SDN controller and is composed of three main modules:
- Traffic Collector and Flow Installer (TCFI): This module captures network traffic, extracts relevant packet headers, and assesses flow rules. The algorithm prioritizes the installation of flows with evident symmetrical traffic patterns to avoid unnecessary rule installations, hence mitigating potential flow table exhaustion attacks on the switches.
- Feature Extractor (FE): It operates periodically, converting raw captured data into feature sets for analysis. This includes a comprehensive extraction from TCP, UDP, and ICMP traffic, resulting in a high-dimensional feature space from which the SAE model performs feature reduction.
- Traffic Classifier (TC): The SAE-based classifier distinguishes between normal and attack traffic, categorizing attacks into one of seven DDoS types. The reduced feature set from the SAE enhances classification accuracy and efficiency.
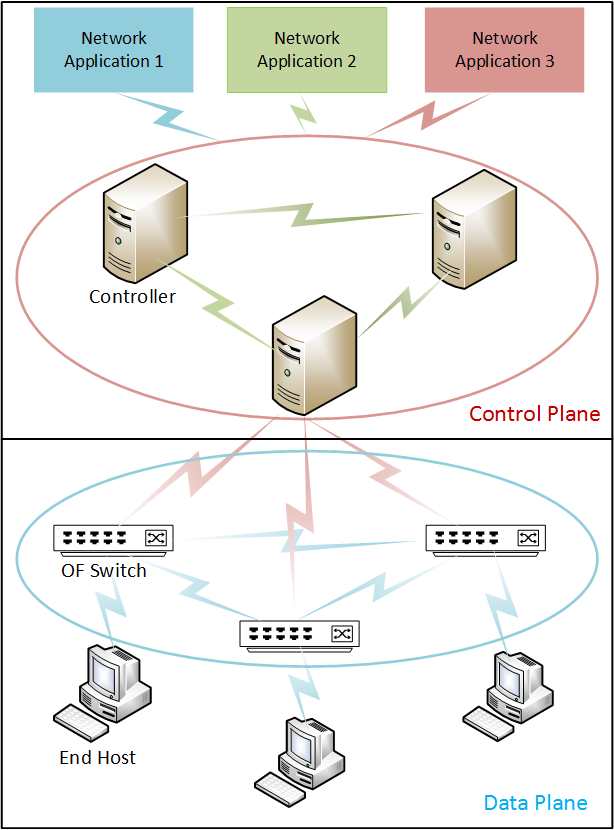
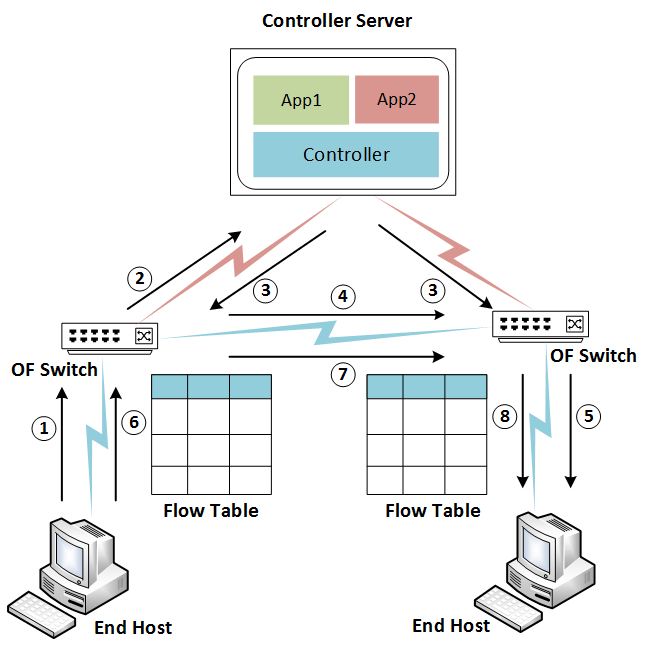
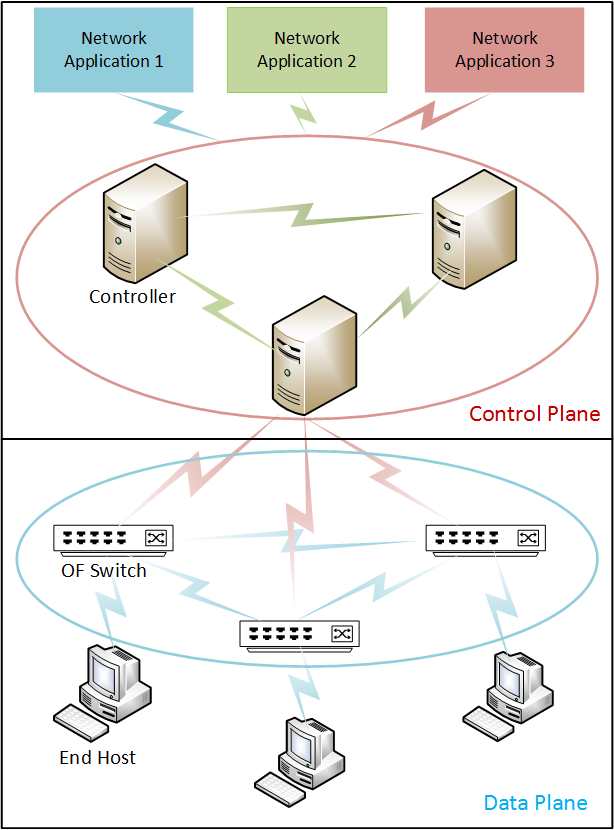
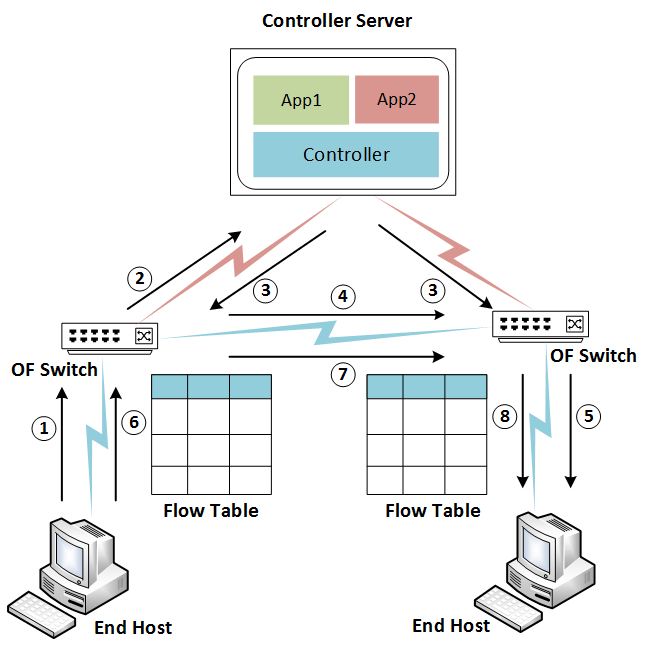
Figure 1: An SDN architecture and basic traffic flow in SDN.
Experimental Evaluation
The experiments conducted utilized a dual environnement setup involving a real-world home wireless network and a controlled testbed for generating DDoS attack scenarios. This hybrid approach allowed for a comprehensive dataset blending authentic network behavior with synthetic attack patterns.
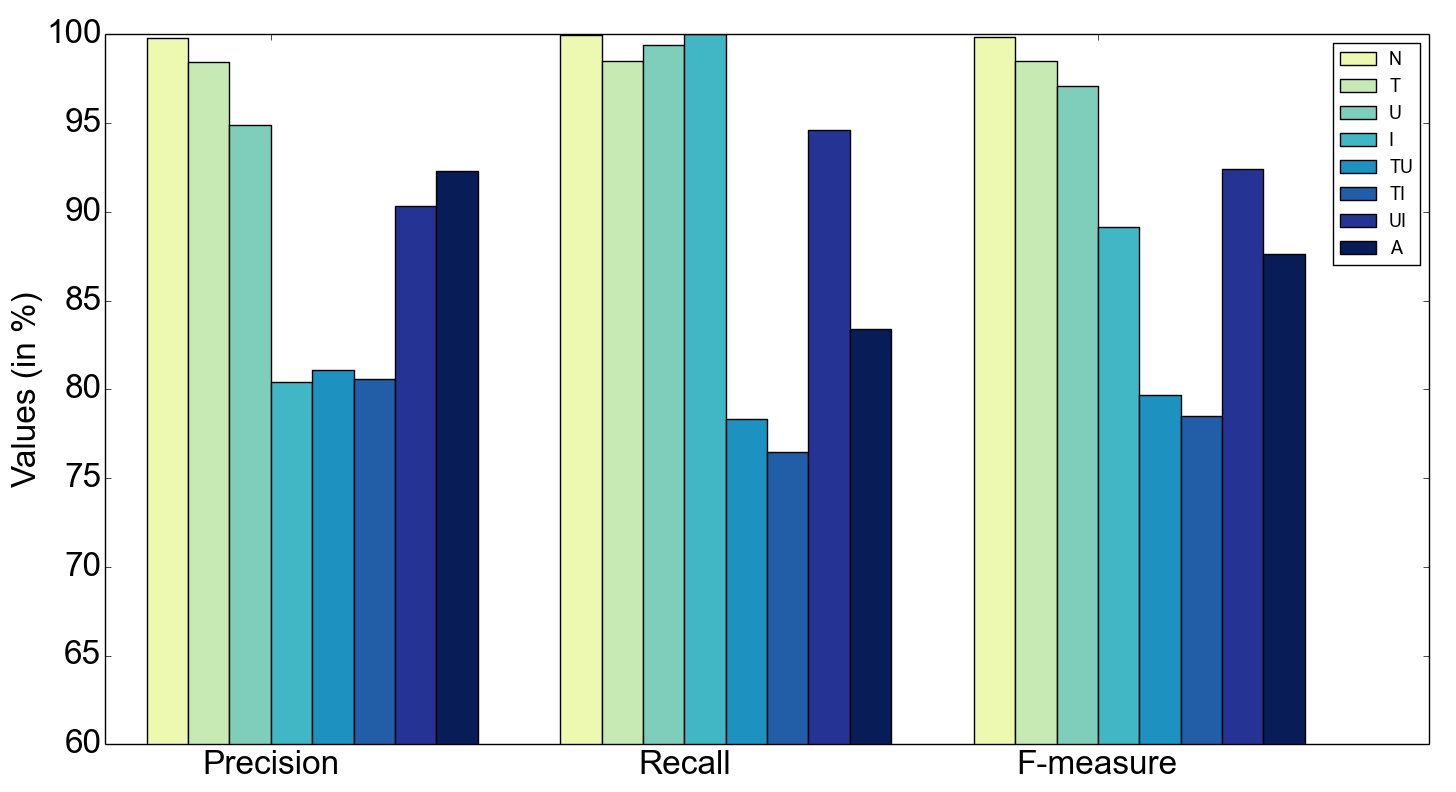
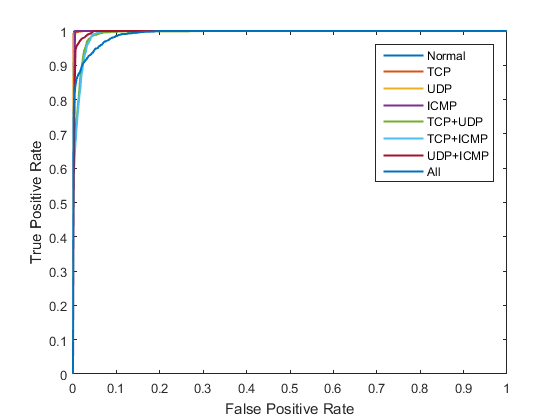
Performance Metrics: SAE demonstrated superior performance compared to baseline models such as the soft-max and standard neural networks, achieving an overall classification accuracy of 95.65% for multi-class attack detection and 99.82% for binary classification between normal and attack traffic.
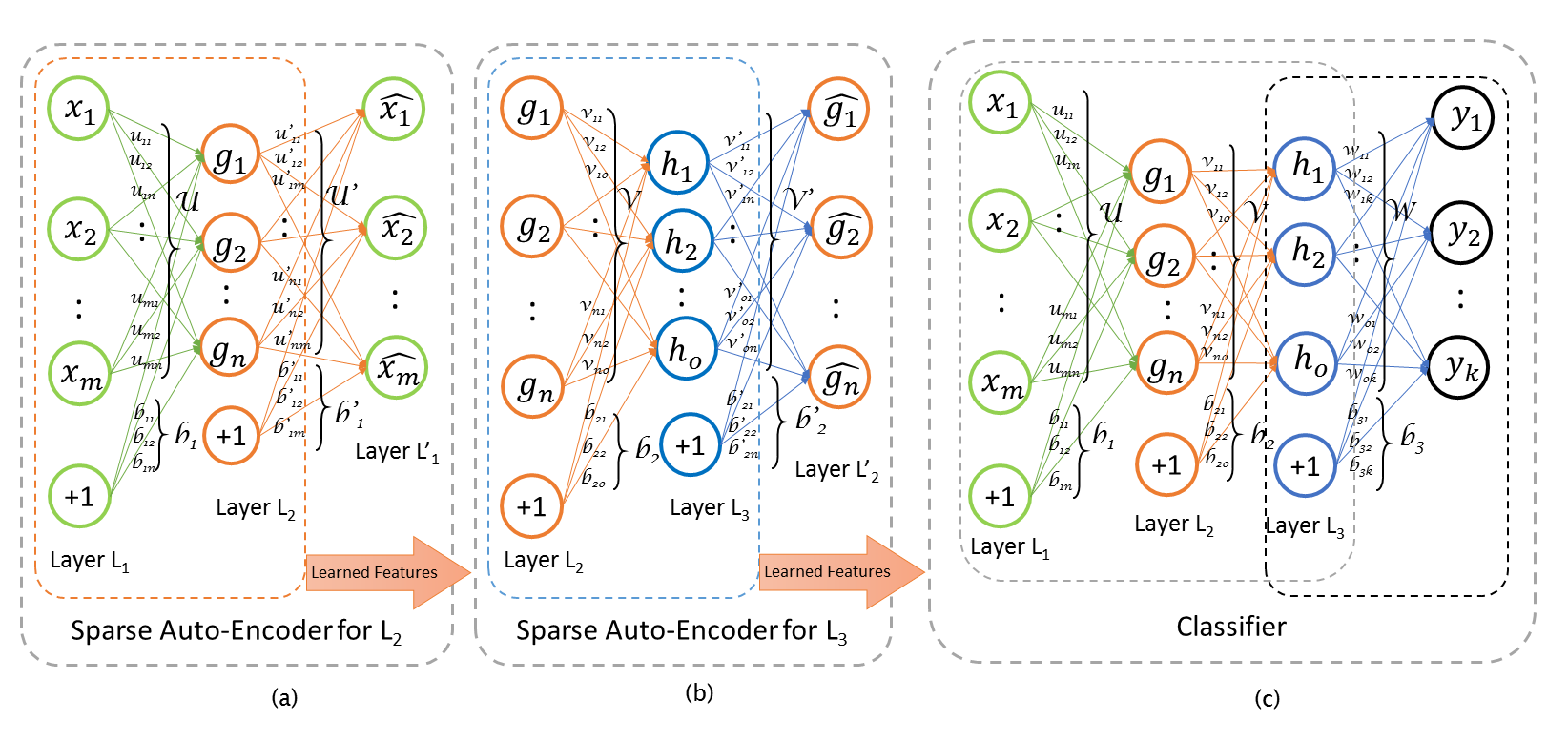
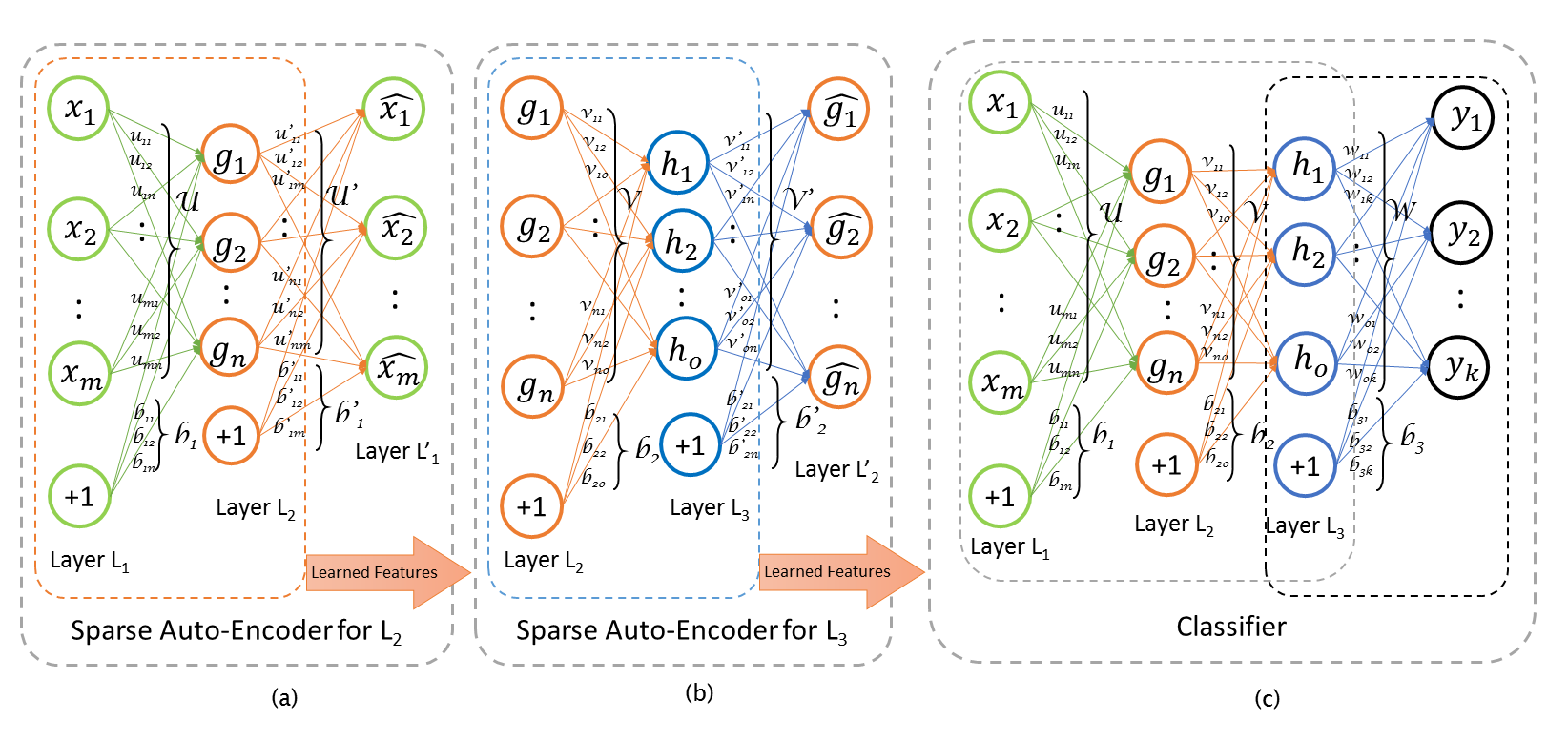
Figure 2: A stacked autoencoder based deep learning model.
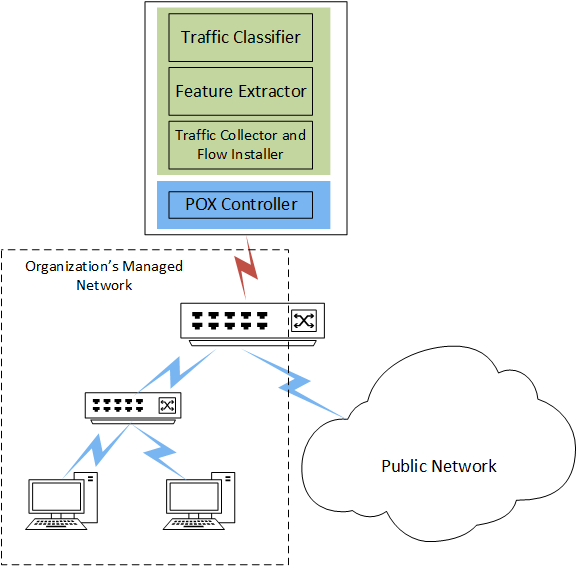
Figure 3: A DDoS detection system implemented in SDN.
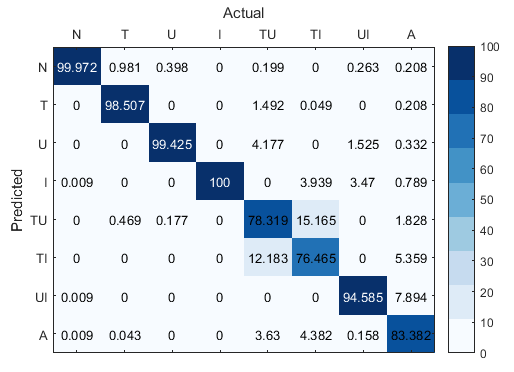
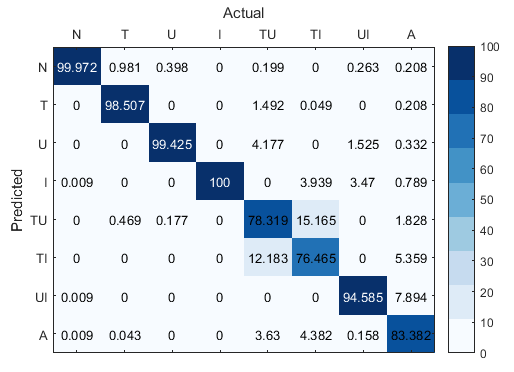
Figure 4: Confusion matrix for 8-class classification in the SAE model.
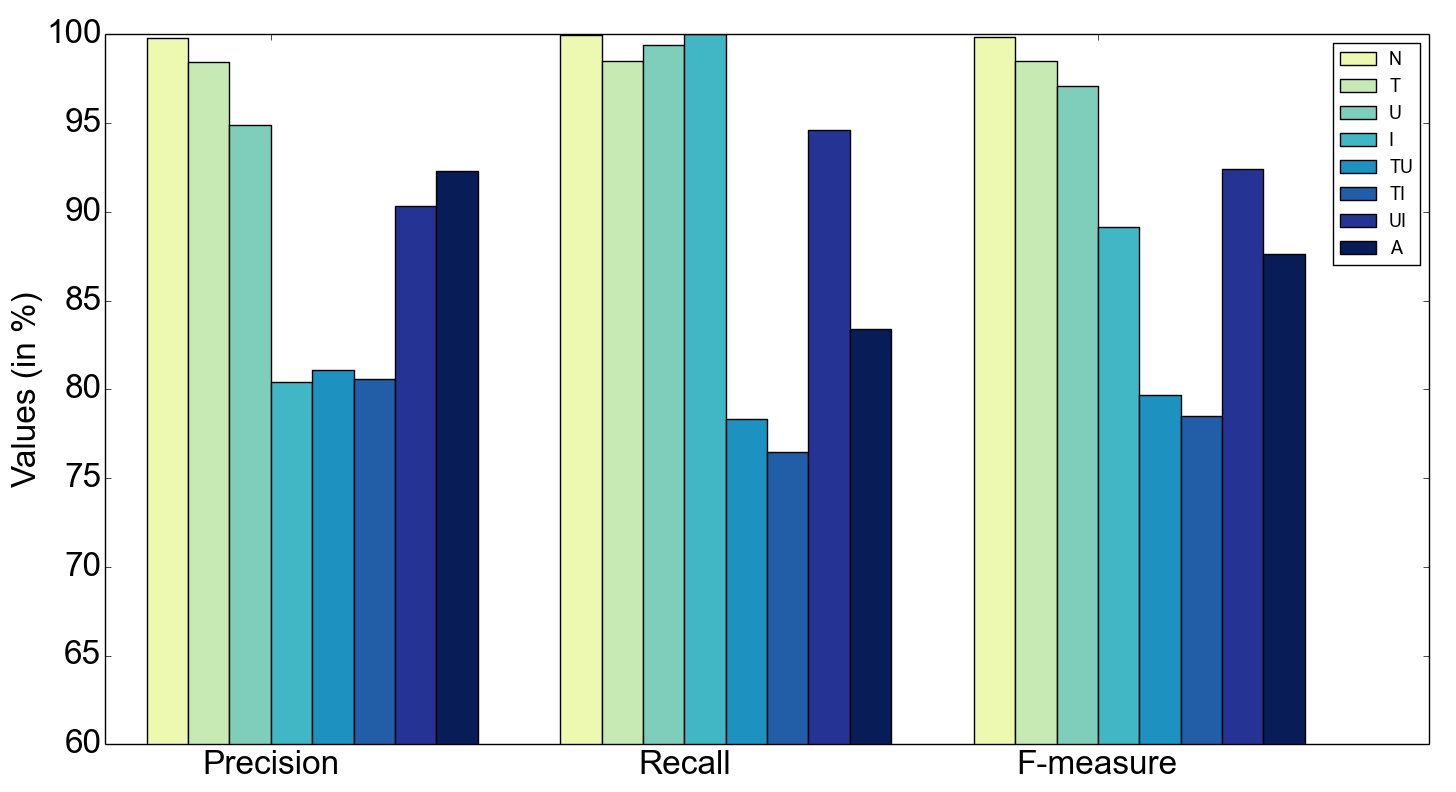
Figure 5: Precision, recall, and f-measure for 8-class.
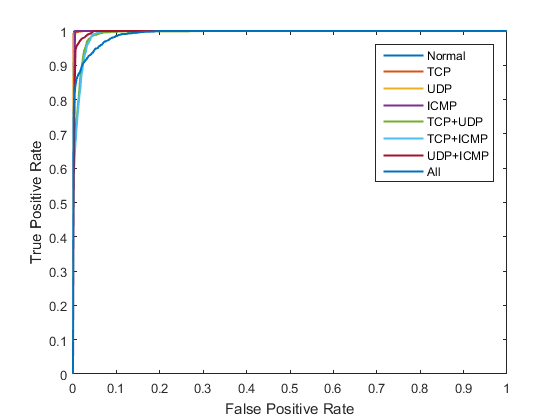
Figure 6: ROC curve for 8-class classification.
Implications and Future Work
This research highlights the potential of integrating deep learning frameworks within SDN to create an agile and robust network defense. The efficacy of SAE in feature reduction contributes significantly to minimizing false-positive rates—a critical factor in real-world deployment. The paper also suggests potential scalability issues with the processing of full traffic data, proposing future exploration into hybrid or distributed processing models. Additionally, the prospect of using deep learning for raw data feature extraction remains an open area for advancing network intrusion detection systems (NIDS).
Conclusion
The integration of SDN with deep learning techniques such as SAE offers a powerful methodology for addressing complex security challenges posed by DDoS attacks. While achieving high detection accuracy, the research also elucidates pathways for enhancing system performance and reducing computational overhead in larger networks. Future directions include broader attack detection, optimized processing efficiency, and leveraging deep learning for on-the-fly feature extraction from raw network data, potentially setting a new benchmark in the domain of network security.