- The paper’s main contribution is a user-centric approach that combines selective encryption with data fragmentation to secure EHR data in MCPS.
- It integrates SHA-256 hashing and pseudorandom number generation to enhance security while reducing computational latency compared to AES-128.
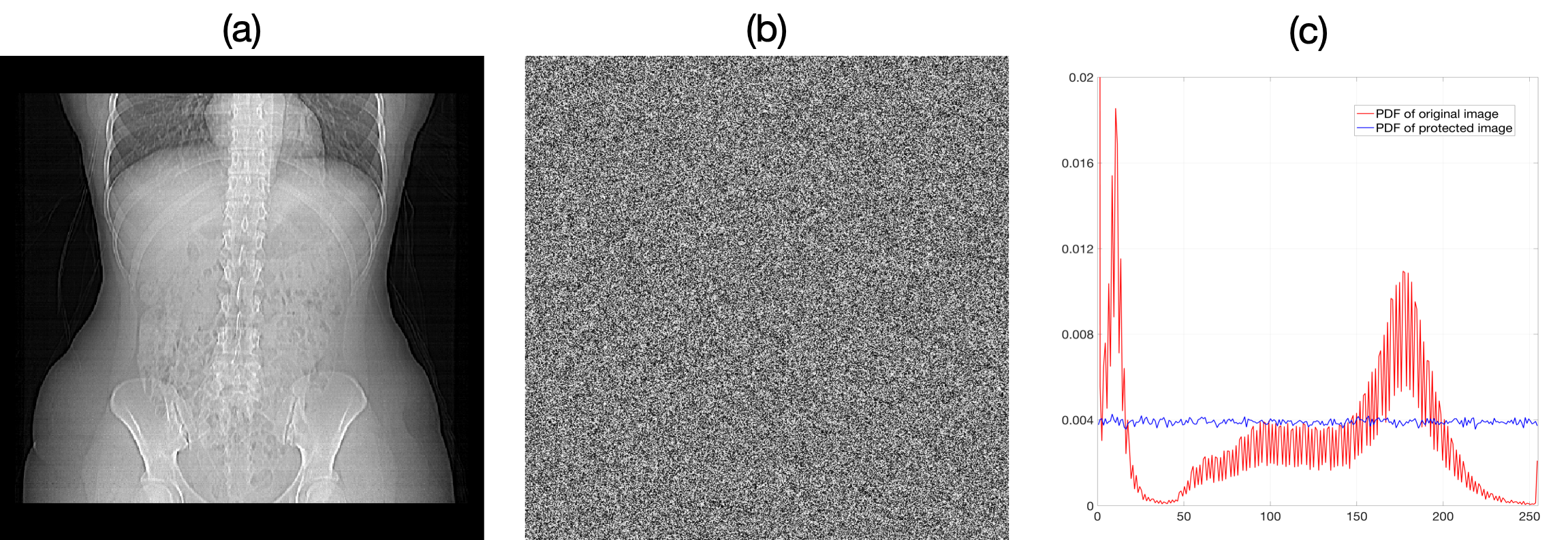
- Leveraging Mobile Edge Computing, the method ensures real-time protection and is validated using entropy tests and PDF analysis on DICOM images.
Privacy-preserving Health Data Sharing for Medical Cyber-Physical Systems
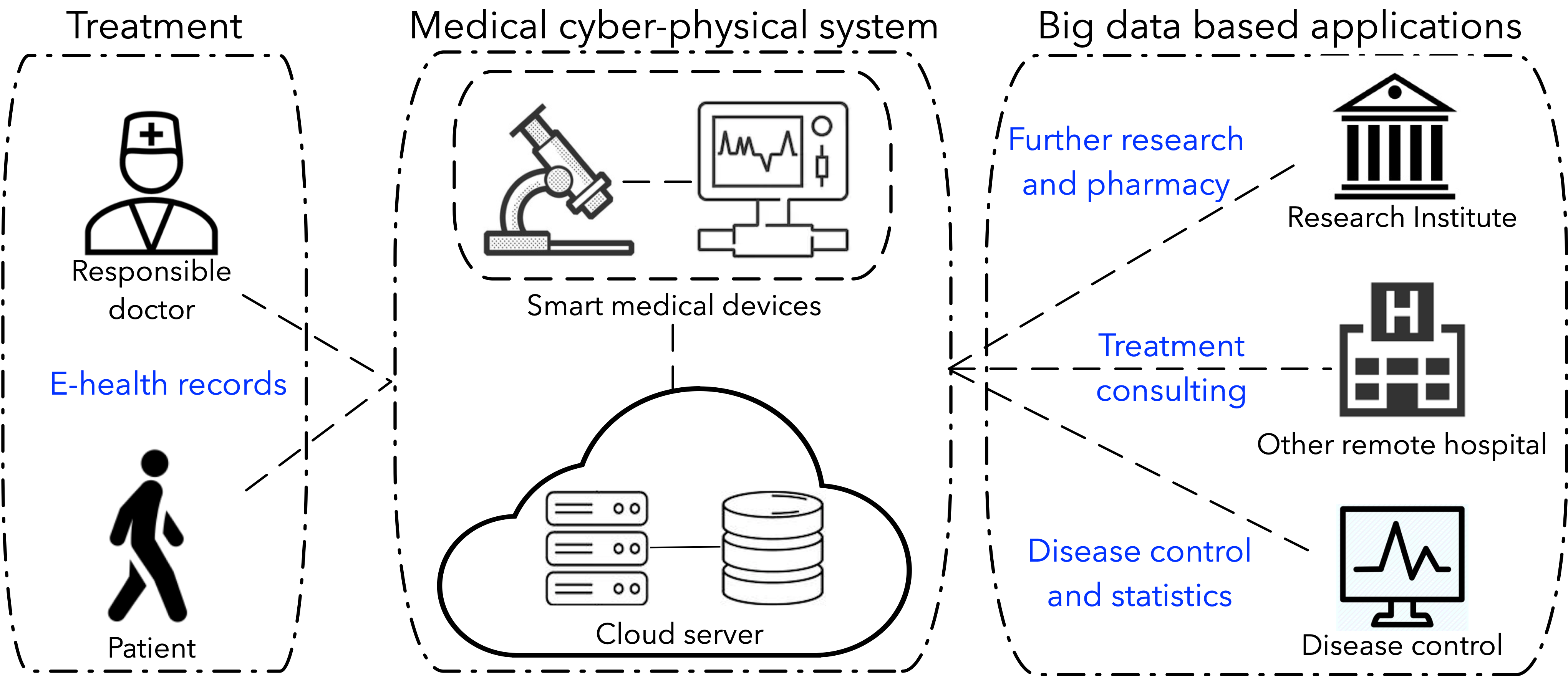
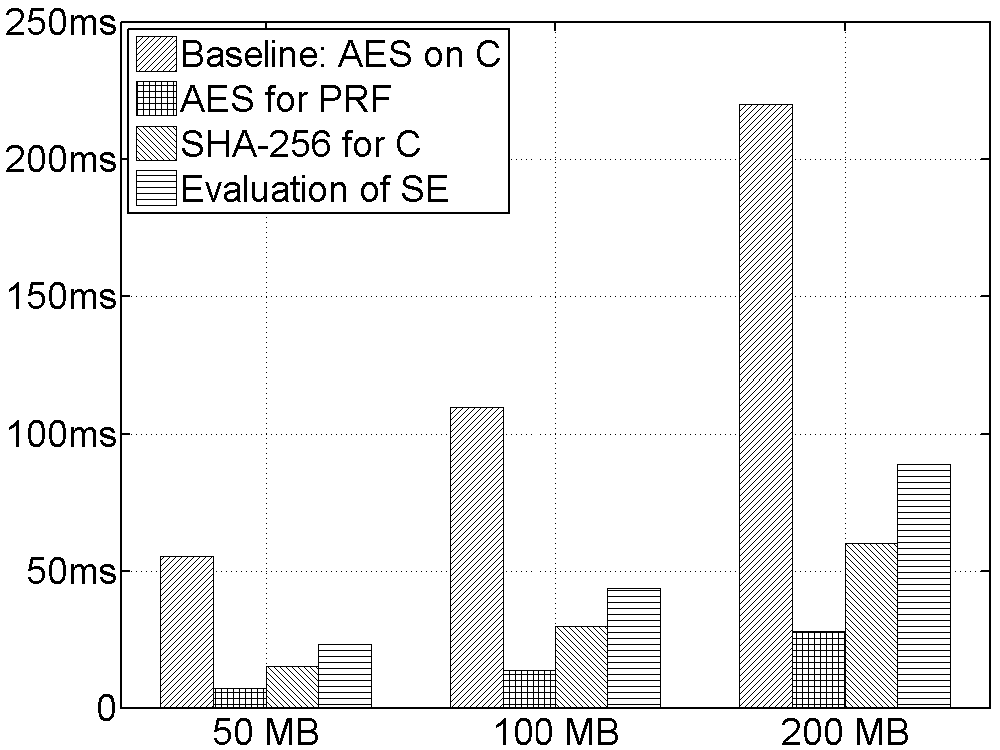
This paper discusses the development of a privacy-preserving method for health data sharing in Medical Cyber-Physical Systems (MCPS), which are integrated systems incorporating computational capabilities alongside physical processes in a medical context, such as cloud computing for Electronic Health Records (EHR).
Introduction
Medical Cyber-Physical Systems (MCPS) integrate medical devices and computing infrastructure for enhanced healthcare delivery, often employing cloud-based storage solutions for vast EHR datasets. The security challenge arises from the ubiquitous storage and transmission of sensitive patient data, which creates vulnerabilities to cyber-attacks. This paper proposes a novel Secure Data Storage and Sharing method that combines a Selective Encryption (SE) algorithm with fragmentation and dispersion techniques. This user-centric approach ensures data protection even when encryption keys and cloud servers are compromised.
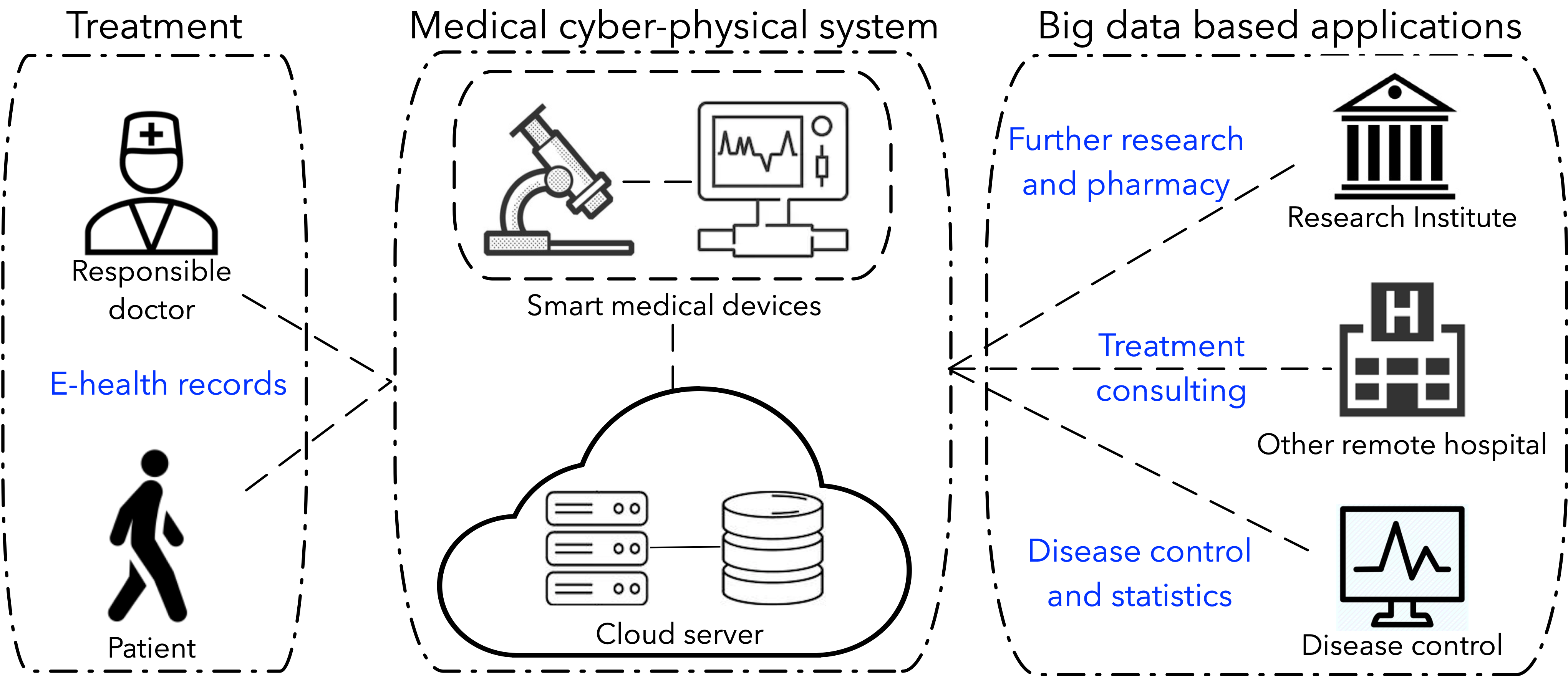
Figure 1: Medical Cyber-Physical System (MCPS) use cases and applications based on big data.
Research Background
Problem Definition and Threat Models
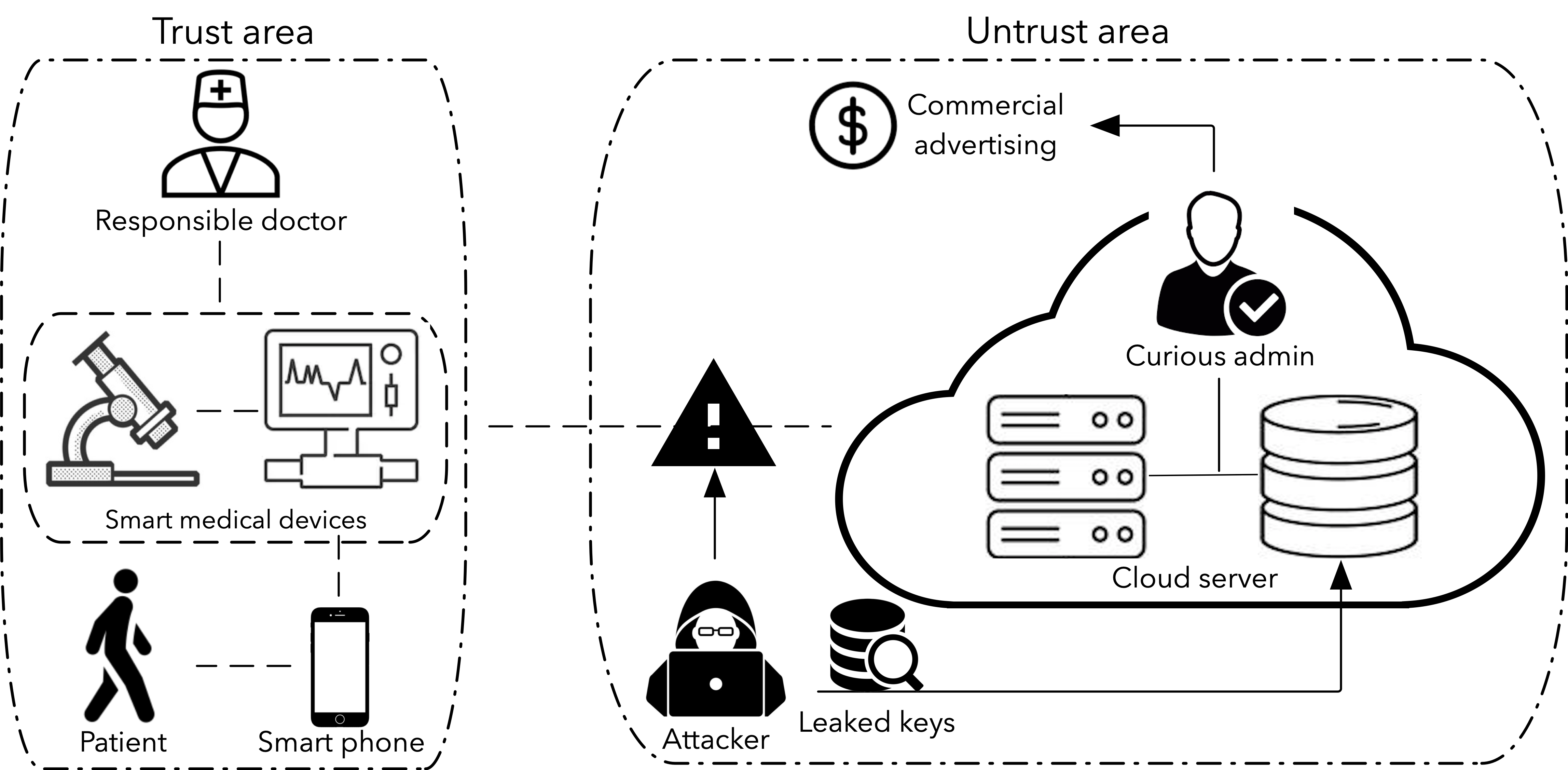
Cloud-based MCPS systems offer efficient and economical data management solutions but simultaneously expose EHR data to significant security risks. Critical threats identified include eavesdropping on public communication channels, brute-force attacks targeting repeated keys, and privacy violations by cloud service providers.
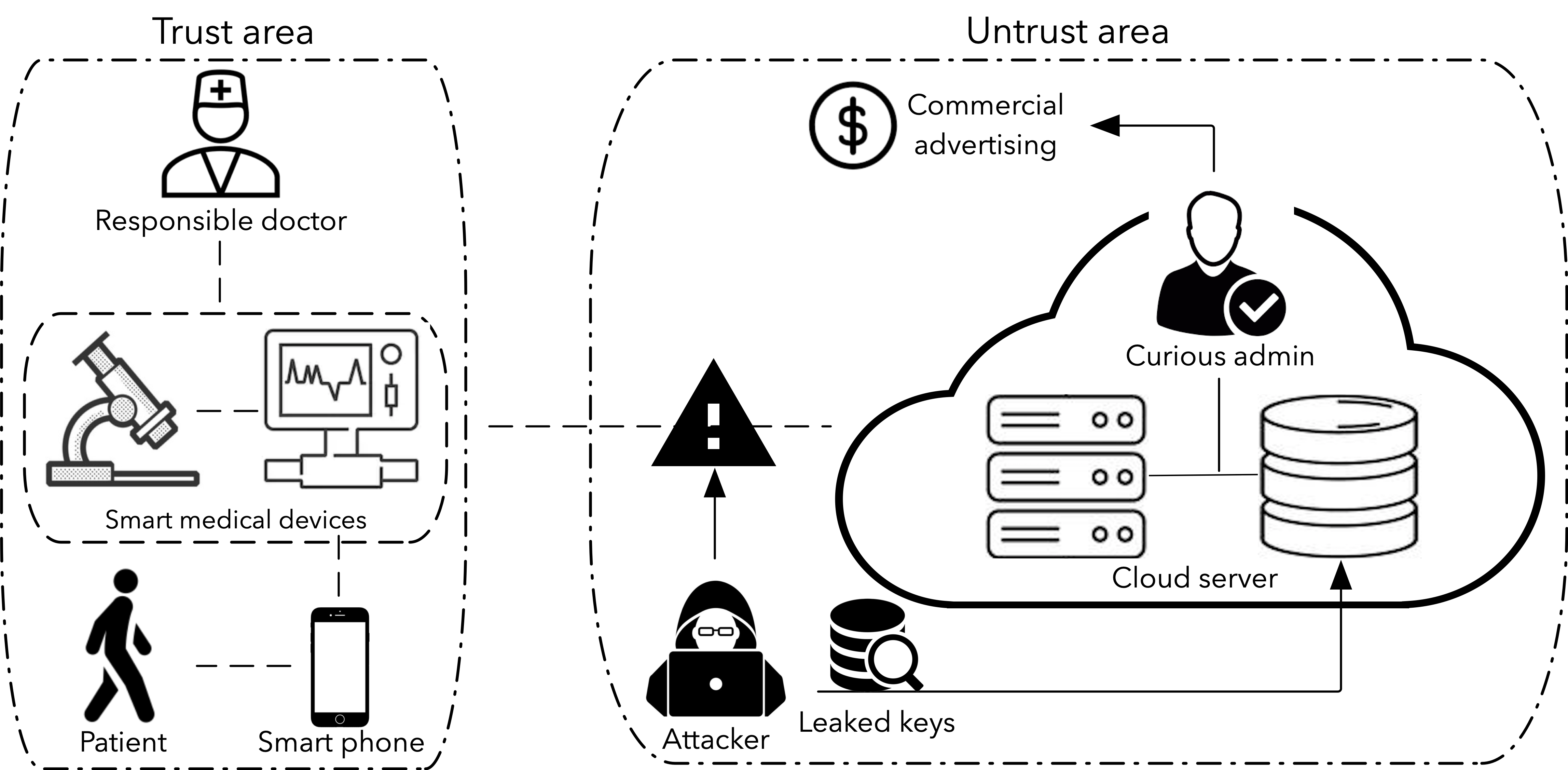
Figure 2: A brief example for threats modes of EHR data on cloud based MPCS.
Research Motivation
Given the potential exposure of encryption keys due to user behavior such as frequent password reuse, a robust data protection mechanism beyond traditional encryption paradigms is required. This paper's approach assumes the trustworthiness of users' physical devices, such as smartphones, for local data protection, leveraging Mobile Edge Computing (MEC) to secure data pre-outsourcing.
Design and Implementation
System Architecture
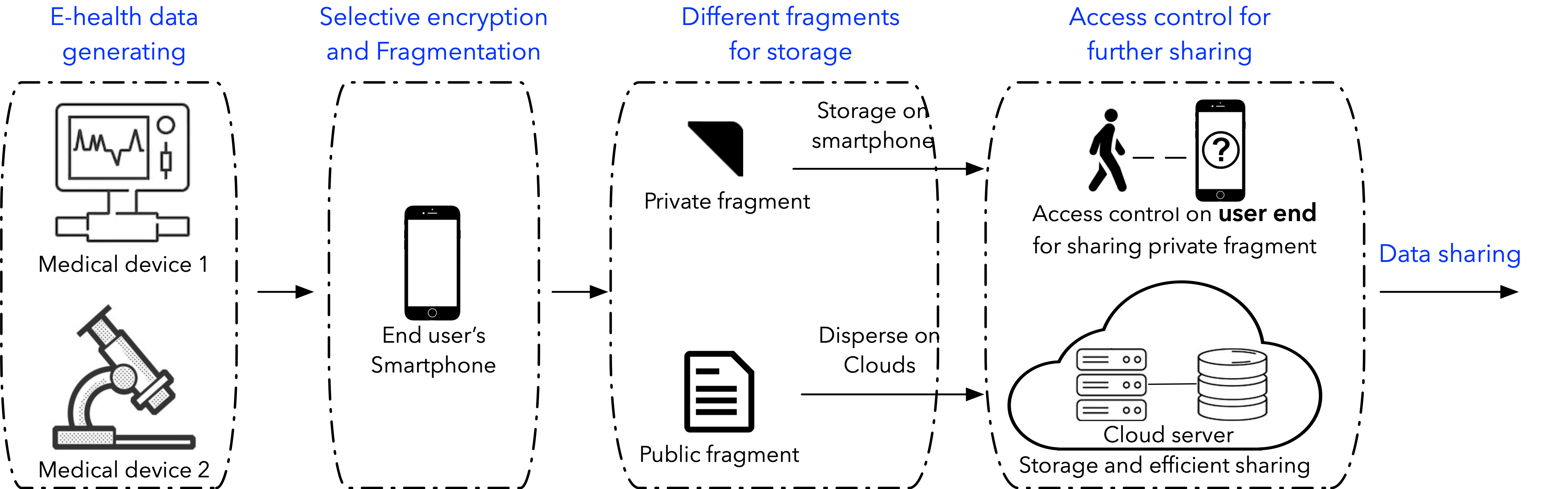
The architecture leverages user-centric design principles, distributing private and public data fragments across trusted devices and cloud servers, respectively. This ensures that the data stored in the cloud lacks sufficient information content for recovery, even if keys are compromised.
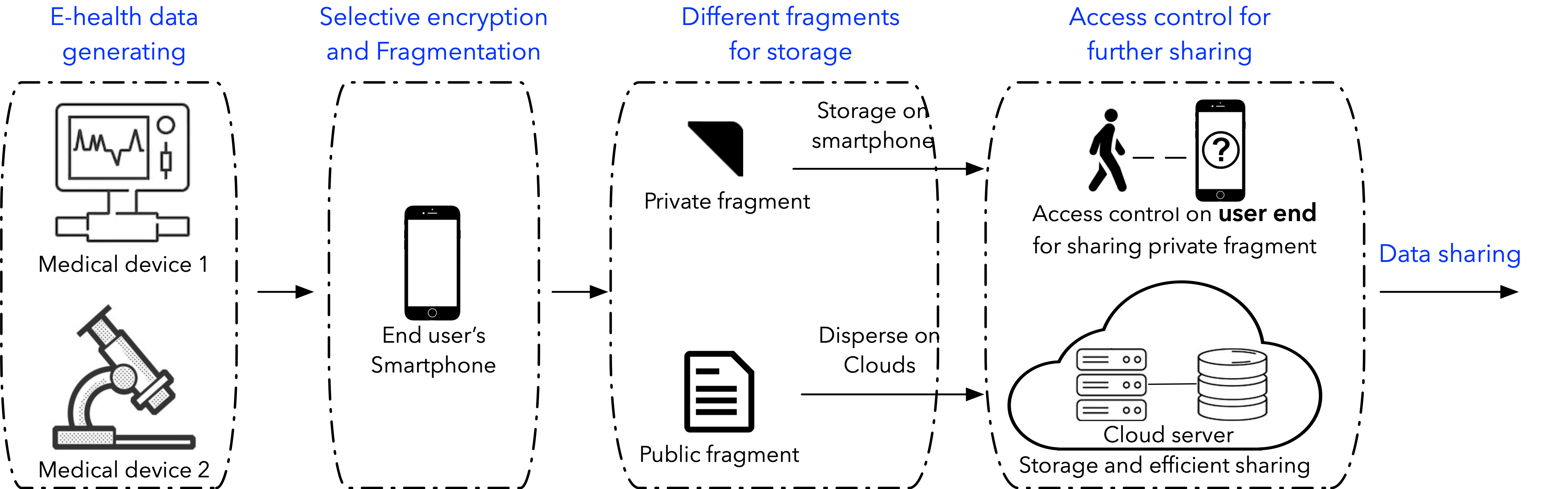
Figure 3: System architecture based on user-centric viewpoint.
Selective Encryption Algorithm
The SE algorithm selectively encrypts critical data fragments stored locally and disperses less sensitive fragments on the cloud. Importantly, this method employs SHA-256 hashing alongside a pseudorandom number generator for enhanced data security.
Mobile Edge Computing
MEC facilitates data protection by enabling computation on devices physically controlled by the user, which circumvents potential data breaches stemming from cloud or communication channel vulnerabilities.
Protection Analysis
Statistical Analysis
The protection mechanism's effectiveness is validated using entropy tests and PDF analysis on transformed DICOM images, demonstrating high randomness in public fragments, indicative of data irrecoverability on cloud servers.
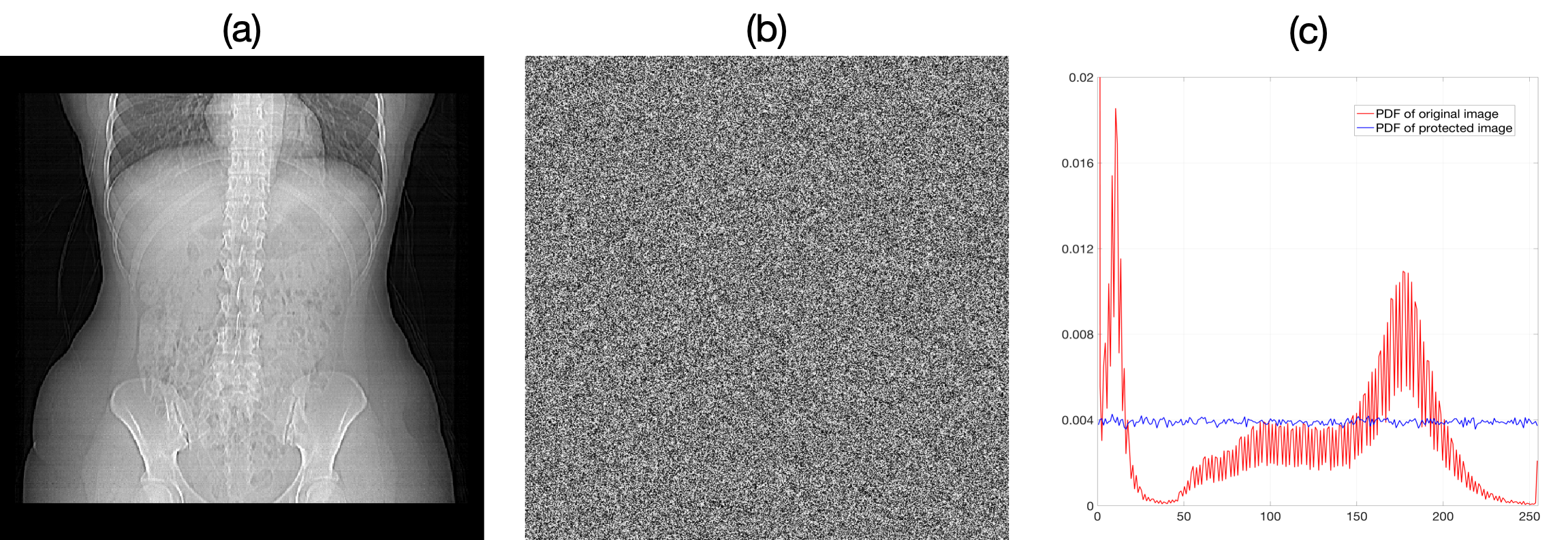
Figure 4: (a) Original DICOM image, (b) protected DICOM image, and (c) their PDFs.
Evaluations on a smartphone platform reveal that the SE algorithm notably reduces computational latency compared to baseline AES-128 encryption. This latency reduction is critical for real-time MCPS, where data responsiveness directly impacts medical decision-making.
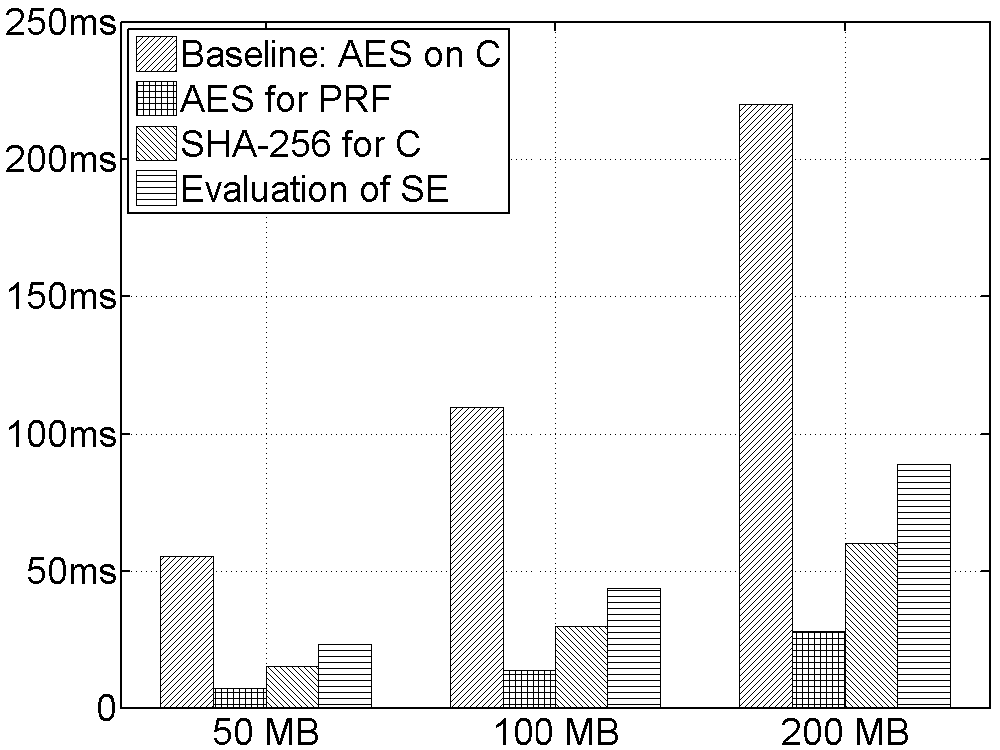
Figure 5: Evaluated performance comparison between proposed SE algorithm with the AES-128.
Future Work and Conclusion
Subsequent research will investigate multi-cloud deployments, exploring optimal trust level allocations and assessing cross-platform performance metrics for diverse smartphone architectures. The paper contributes a pivotal advancement in securing EHR data sharing, offering a resilient solution that considers both technological and behavioral challenges in MCPS environments.