Distributed Routing in a Quantum Internet
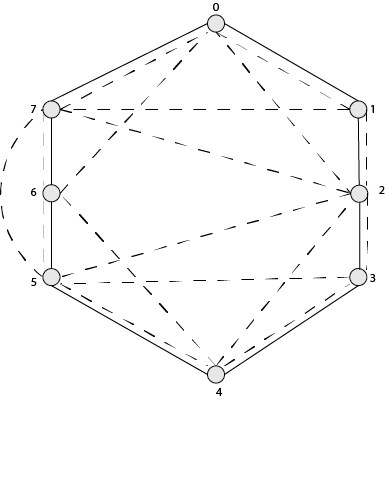
Abstract: We develop new routing algorithms for a quantum network with noisy quantum devices such that each can store a small number of qubits. We thereby consider two models for the operation of such a network. The first is a continuous model, in which entanglement between a subset of the nodes is produced continuously in the background. This can in principle allows the rapid creation of entanglement between more distant nodes using the already pre-generated entanglement pairs in the network. The second is an on-demand model, where entanglement production does not commence before a request is made. Our objective is to find protocols, that minimise the latency of the network to serve a request to create entanglement between two distant nodes in the network. We propose three routing algorithms and analytically show that as expected when there is only a single request in the network, then employing them on the continuous model yields a lower latency than on the on-demand one. We study the performance of the routing algorithms in a ring, grid, and recursively generated network topologies. We also give an analytical upper bound on the number of entanglement swap operations the nodes need to perform for routing entangled links between a source and a destination yielding a lower bound on the end to end fidelity of the shared entangled state. We proceed to study the case of multiple concurrent requests and show that in some of the scenarios the on-demand model can outperform the continuous one. Using numerical simulations on ring and grid networks we also study the behaviour of the latency of all the routing algorithms. We observe that the proposed routing algorithms behave far better than the existing classical greedy routing algorithm. The simulations also help to understand the advantages and disadvantages of different types of continuous models for different types of demands.
Paper Prompts
Sign up for free to create and run prompts on this paper using GPT-5.
Top Community Prompts
Knowledge Gaps
Below is a single, consolidated list of concrete knowledge gaps, limitations, and open questions that remain unresolved in the paper. Each point is phrased to guide future research toward actionable next steps.
- Physical-layer realism: Entanglement swap is assumed deterministic and instantaneous, and swap errors and timings are ignored; incorporate realistic swap error models, finite operation times, and classical feed-forward delays to assess routing performance and fidelity under practical conditions.
- Classical control overhead: Classical signaling and coordination latencies (for path discovery, heralding, reservations, and swap orchestration) are neglected; quantify their impact on end-to-end latency and success probability, and design control-plane protocols that scale with network size and dynamics.
- Memory lifetime assumption: The analysis assumes “T_th ≫ diam(G_ph)”, which is likely unrealistic for near-term quantum memories; study algorithm behavior and latency when memory lifetimes are comparable to or shorter than classical path discovery times.
- Noise modeling: The storage noise model uses symmetric depolarizing channels with parameter
p, ignoring amplitude/phase damping, correlated noise, crosstalk, and device-dependent heterogeneity; develop routing analyses under realistic noise processes and heterogeneous memory hardware. - Entanglement generation model: Elementary link generation is modeled with a single, per-time-step success probability
P0and independence across steps/links; incorporate distance-dependent loss, asymmetric link success rates, and temporal correlations, and evaluate their impact on routing and overlay design. - Fidelity degradation along paths: End-to-end fidelity is lower bounded using noiseless swap and multiplicative
F1 F2assumptions; derive tight fidelity bounds under noisy swap, repeated operations, and memory decoherence, and link them to route selection metrics (e.g., fidelity-aware cost functions). - Distillation and error correction: The analysis explicitly omits entanglement distillation and quantum error correction; investigate how these techniques change routing decisions, affect the continuous/on-demand trade-off, and enable longer viable
d_thwith acceptable fidelity. - Loop-freedom and convergence: The distributed path discovery procedures (modified greedy and local best effort) lack formal guarantees of loop-freedom, termination, and convergence under stale or partial information; prove correctness or add mechanisms (visited sets, backtracking, TTLs) to prevent routing loops and dead ends.
- Optimality and competitiveness: No formal bounds are provided on the path stretch or competitiveness of the proposed local algorithms relative to shortest paths (in physical or virtual graphs); establish tight performance guarantees and conditions under which local routing approximates optimal routes.
- Multi-demand analysis: Performance with multiple concurrent demands is evaluated only via simulations (ring/grid) without analytical queueing or contention models; develop tractable analytical frameworks (queueing theory, conflict graphs) to characterize latency, throughput, and fairness under multi-demand contention.
- Congestion control and fairness: There is no scheduling or prioritization of demands, nor policies to prevent starvation; design distributed contention control, admission control, and fairness mechanisms tailored to expiring entanglement resources.
- Capacity modeling: Nodes can generate
capEPR pairs per neighbor in parallel, but contention across neighbors and global memory constraints are not modeled; introduce realistic per-node/per-link capacity limits, memory allocation policies, and link-refresh scheduling to manage scarce resources. - Hybrid continuous/on-demand policy: While continuous outperforms on-demand for low demand and may be inferior under heavy demand, no decision rule is given; derive traffic- and topology-dependent policies (thresholds on demand intensity,
cap,T_th,P0) to switch or blend continuous and on-demand modes adaptively. - Virtual neighbor selection: Virtual links are chosen deterministically or via uniform/power-law distributions within
d_thradius, independent of traffic; co-design overlay selection with observed demand patterns, success probabilities, and memory constraints to optimize latency and resource use. - Parameter selection and sensitivity: The paper introduces several design parameters (
d_th,alpha,k,cap,P0,p,F_th) without methods to estimate or tune them; perform sensitivity analyses and provide parameter calibration strategies based on hardware characterization and traffic statistics. - Connectivity and percolation: With bounded
d_thand expiring links, the virtual graph may be disconnected; analyze connectivity thresholds (percolation conditions) for different topologies and neighbor selection schemes to ensure high-probability reachability. - Edge-disjoint multi-paths: The text hints that for
D_{s,e} > capit is better to find edge-disjoint paths but does not provide algorithms or analysis; develop distributed multi-path routing, capacity splitting strategies, and fidelity aggregation (e.g., via distillation) for bulk entanglement delivery. - Realistic topologies: Results focus on ring, grid, and recursively generated graphs; extend evaluation to realistic network topologies (random geometric, ISP/backbone, scale-free) with heterogeneous link lengths, loss rates, and node capabilities.
- NoN knowledge scope: NoN local best effort assumes 2-hop neighbor knowledge but not the costs for maintaining such information under link expiry and churn; quantify the control overhead and evaluate the latency/overhead trade-off across different knowledge radii.
- Classical greedy baseline: Comparison is primarily with a classical greedy algorithm not tailored to expiring, consumable entanglement; include baselines that incorporate reservation awareness, capacity constraints, and expiration to ensure fair performance comparisons.
- Asynchronous operations and timing granularity: The discrete-time model ties one step to a maximum physical link communication time, potentially over-coarse; move to continuous/asynchronous timing models that support pipelining of generation, swapping, and classical messaging.
- Failure handling and rerouting: If reserved links decohere before swaps complete, the demand “waits” without proactive rerouting; design reactive rerouting and repair mechanisms that exploit alternative paths or link-refresh policies to reduce stall times.
- Metrics beyond latency: Evaluation focuses on average latency; add success probability, throughput, resource utilization, energy/overhead, and end-to-end fidelity metrics to provide a multi-objective assessment of routing strategies.
- Security and application constraints: Application-layer requirements (e.g., QKD rate, reliability, deadlines) are not integrated into routing decisions; incorporate QoS constraints and security considerations into route selection and resource reservation.
- Incomplete bounds and typos: The table of entanglement swap counts includes apparent formatting/parenthesis errors and lacks rigorous proofs of tightness; correct and tighten these bounds and provide complete derivations for both ring and grid cases.
- Partial topology knowledge: Algorithms assume each node “stores the information about the physical graph topology,” which is challenging at scale; design scalable discovery/learning mechanisms for partial topology knowledge and quantify their impact on routing quality.
- Interaction with network coding: Prior quantum network coding approaches are not considered; explore hybrid routing-coding strategies and conditions under which coding provides latency/fidelity advantages in realistic noisy networks.
Collections
Sign up for free to add this paper to one or more collections.