- The paper shows that electromagnetic fault injection can induce unique micro-architectural faults in SoCs, disrupting cache and MMU functions.
- It employs a sophisticated experimental setup using high-frequency Keysight instruments to analyze fault behaviors in both bare-metal and OS environments.
- The study underscores the need for integrated hardware security measures, such as proactive MAC verifications, to mitigate emerging faults.
Electromagnetic Fault Injection against System-on-Chip
Introduction
The paper "Electromagnetic fault injection against a System-on-Chip, toward new micro-architectural fault models" (1910.11566) explores the vulnerabilities of modern System-on-Chips (SoCs) to electromagnetic fault injection (EMFI) techniques. Traditional fault attacks have predominantly targeted simple microcontrollers; however, this research investigates the application of EMFI to complex SoCs, such as the Broadcom BCM2837 used in the Raspberry Pi 3B.
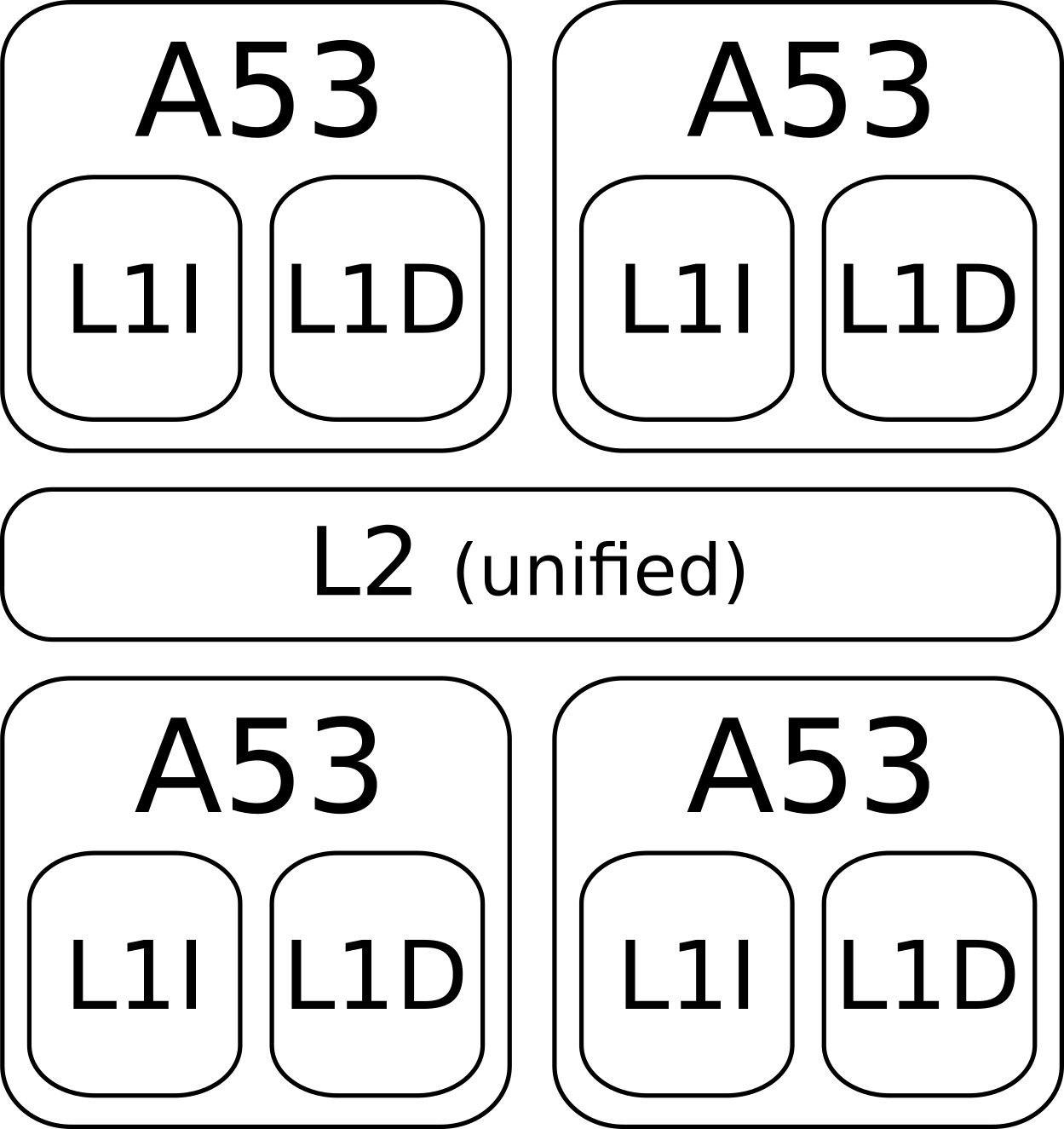
EMFI is a technique used to inject faults into hardware systems by disrupting the electromagnetic environment. This disruption can lead to altered chip behavior, which can undermine security architectures. The paper provides an experimental setup to create and analyze faults within the SoC's microarchitecture. This setup highlights differences in fault effects between SoCs and microcontrollers, emphasizing the distinct susceptibility of components like L1 and L2 caches and the Memory Management Unit (MMU) to targeted electromagnetic interference.
Experimental Setup and Approach
The study employs EMFI to target the BCM2837's cache and MMU subsystems using a highly configurable experimental setup that functions at higher frequencies to accommodate the complexities of modern SoCs. This setup features apparatus such as a Keysight 33509B for delay control and a Keysight 81160A for generating sinusoidal signals, which are amplified and applied using a probe to affect the SoC's metallic wiring and induce faults.
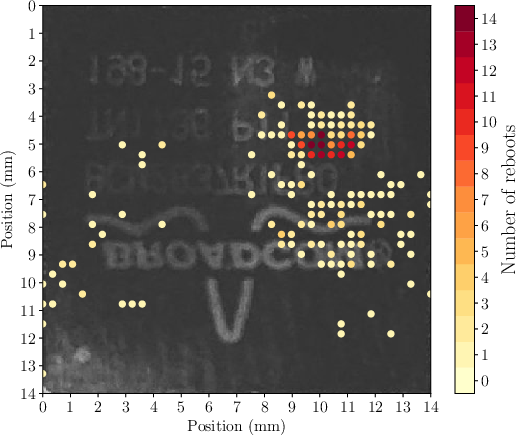
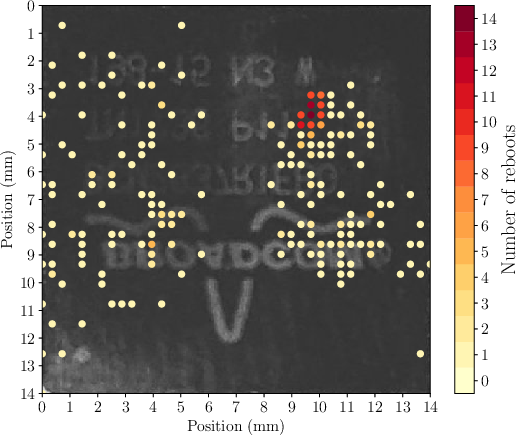
An in-depth analysis is conducted by observing the SoC with and without an operating system (OS), demonstrating how the software layer can affect hardware's vulnerability to faults. Notably, faults occurring on a bare-metal setup show that micro-architectural components are directly impacted, while faults within an OS environment manifest at an instruction level.
Observed Fault Models
The paper identifies distinct fault models occurring due to EMFI, which diverge from those observed in microcontrollers:
- Instruction Cache Faults: EMFI alters instruction cache values, leading to persistent faults or the non-execution of specific instructions when the cache is invalidated. This behavior parallels traditional instruction skip models.
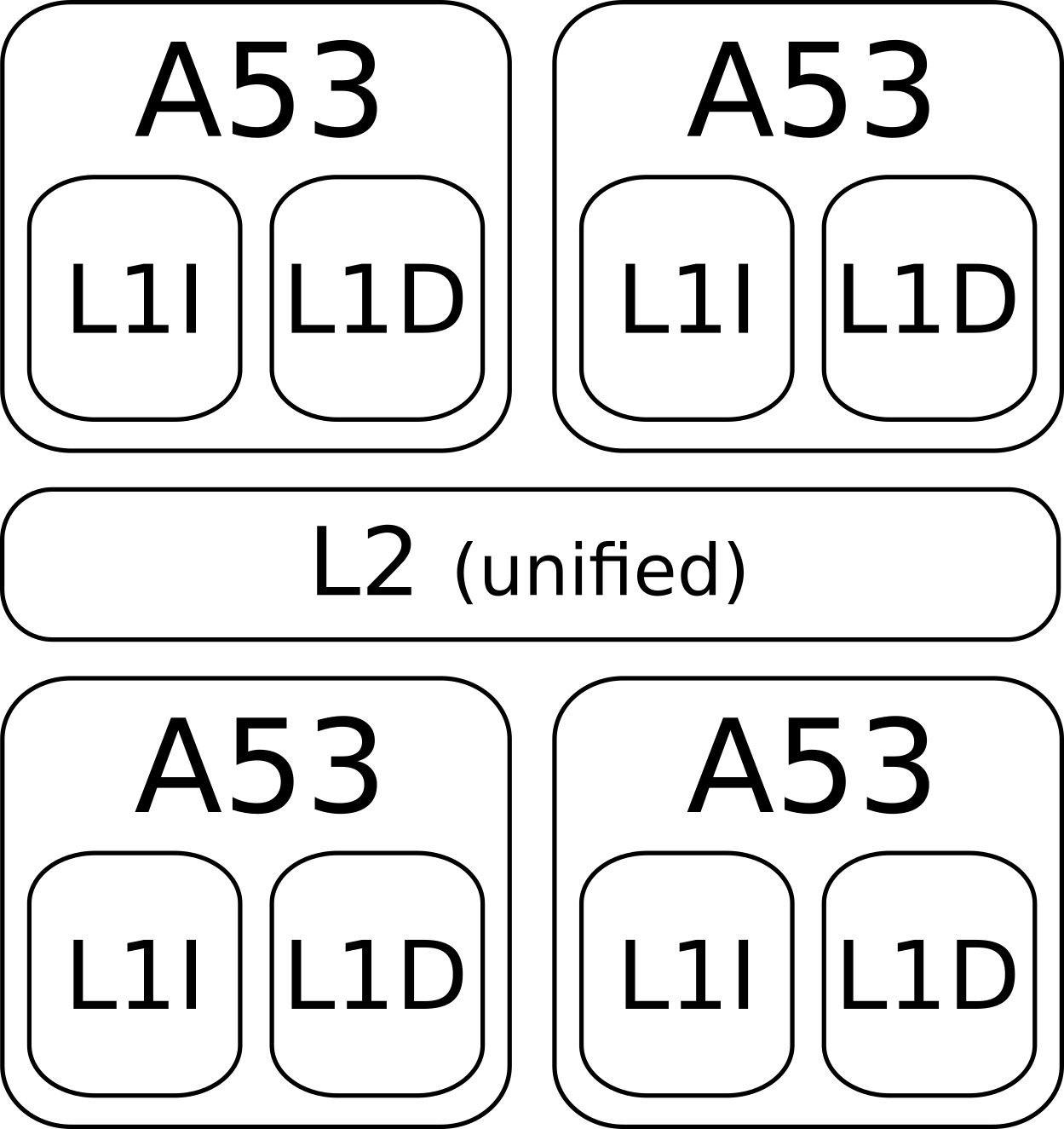
Figure 1: Memory hierarchy for the BCM2837.
- MMU Faults: EMFI modifies virtual to physical memory mappings in an uncontrolled manner, potentially disrupting memory isolation guarantees crucial for security. These alterations are detected by examining discrepancies in page table entries and mappings.
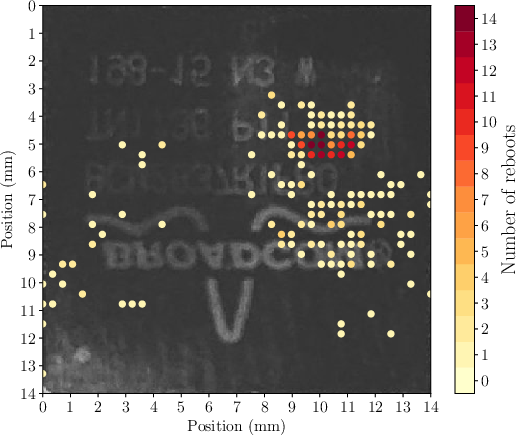
Figure 2: Bare metal sensitivity map.
- L2 Cache Faults: Shifting data chunks in L2 cache indicate that memory transfers between components can be faulted, resulting in shifted or erroneous data and instruction execution.
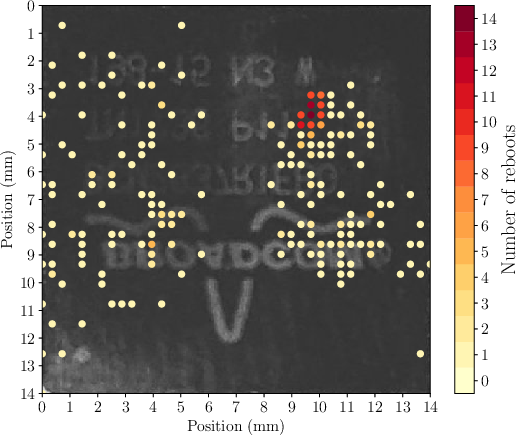
Figure 3: Linux sensitivity map.
These fault models highlight weaknesses in the physical and logical separation of memory and processor instructions. They exploit vulnerabilities that arise from the design of cache and MMU subsystems under EMFI.
Implications and Countermeasures
The identified vulnerabilities challenge the assumption that SoCs can be secured solely through software layers. The hardware susceptibility to EMFI requires robust countermeasures, mainly through ensuring integrity and authenticity of signals in the chip using redundancy methods or cryptographic techniques like Message Authentication Codes (MACs).
Potential countermeasures include proactive integrity checks within the memory hierarchy and just-in-time MAC verifications to ensure anomalies are detected promptly and do not propagate through the system.
Conclusion
The research presents significant insight into the EMFI vulnerabilities inherent in modern SoCs. It emphasizes a need for a holistic approach to security that incorporates hardware-level protections, not just software. With the costs and complexity of EMFI attacks decreasing, these findings have practical implications for future SoC designs, underscoring the necessity to integrate secure core functionalities that provide robust defenses against physical tampering. As the landscape of computational security evolves, ensuring hardware integrity will become as crucial as software fortification in maintaining systemic security.