- The paper demonstrates that container-based environments reproduce vulnerabilities with a Jaccard index of 0.993 compared to traditional VMs.
- It employs a range of security tools, including OpenVAS and Metasploit, to benchmark resource efficiency and performance in cyber range simulations.
- The study highlights limitations such as host OS resource sharing and potential discrepancies in kernel-level exploit reproduction, suggesting areas for future enhancement.
Evaluation of Vulnerability Reproducibility in Container-Based Cyber Range
Introduction
The paper "Evaluation of Vulnerability Reproducibility in Container-Based Cyber Range" explores the application of container-based virtualization to cyber range environments, emphasizing its efficiency in terms of resource consumption. In the context of cybersecurity training and education, cyber ranges provide simulated environments where security professionals can engage in realistic incident response exercises. This paper's primary contribution is a comparative analysis of container and traditional virtualization methods focusing on vulnerability reproducibility, which is crucial for the authenticity of these exercises.
Cyber Range and Virtualization Technologies
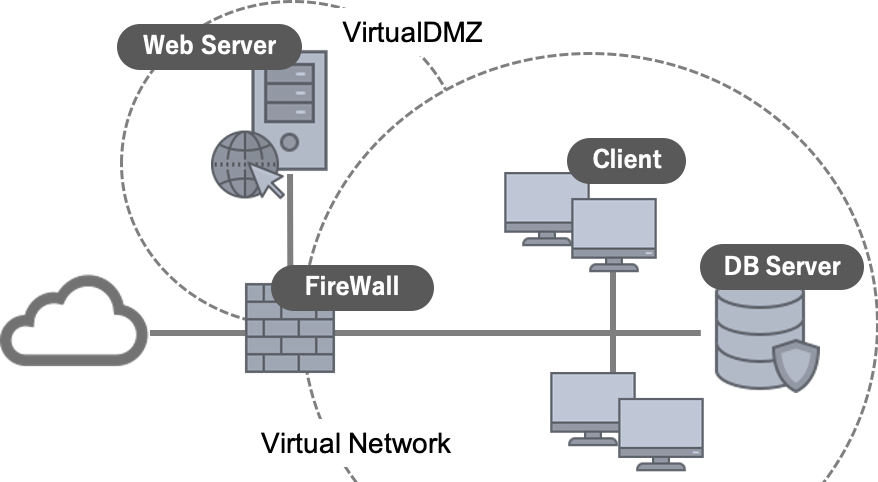
Cyber ranges deliver training environments that replicate real-world scenarios by using virtualized elements to recreate system environments, duplicate and manage exercise scenarios, and reproduce vulnerabilities. Traditional virtualization methods, like hypervisor-based solutions, offer maximum isolation and control but are resource-intensive and costly. Containers, in contrast, are lightweight, sharing the host OS kernel, and achieve scalability and rapid deployment with minimal overhead, leading to lower costs.
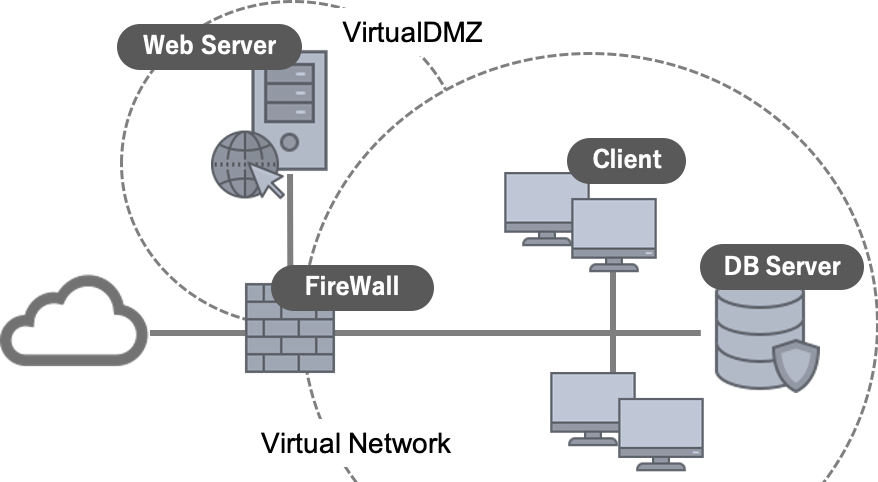
Figure 1: Example of virtual network for cyber range.
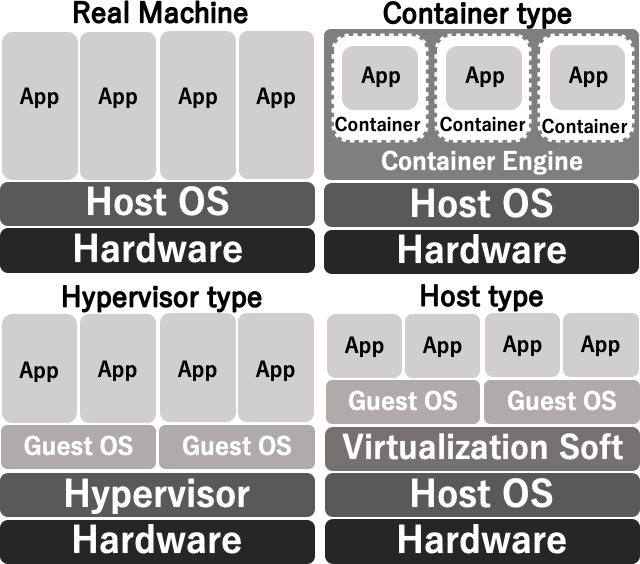
The paper delineates three types of virtualization technologies: hypervisor-based, host-based, and container-based virtualization (Figure 2). Containers, through Dockerization, provide a flexible approach without the need for guest OS installations, thus reducing the computational and storage overhead.
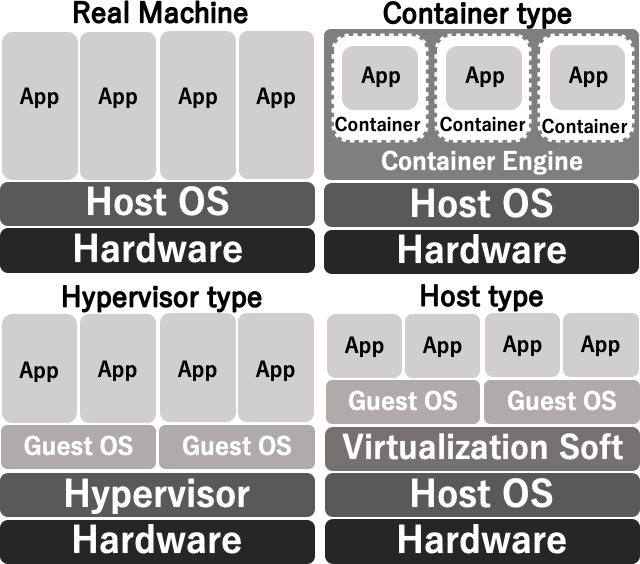
Figure 2: Example of virtual network for cyber range.
Experimental Evaluation
The study conducts extensive experiments to examine the reproducibility of vulnerabilities in containerized environments as compared to virtual machines (VMs). The authors employed a set of vulnerability assessment tools, including OpenVAS, Nmap, OWASP ZAP, and Nikto2, alongside exploit frameworks such as Metasploit, to evaluate the extent to which common vulnerabilities and exploits available in cyber range exercise scenarios could be adequately replicated in containers.
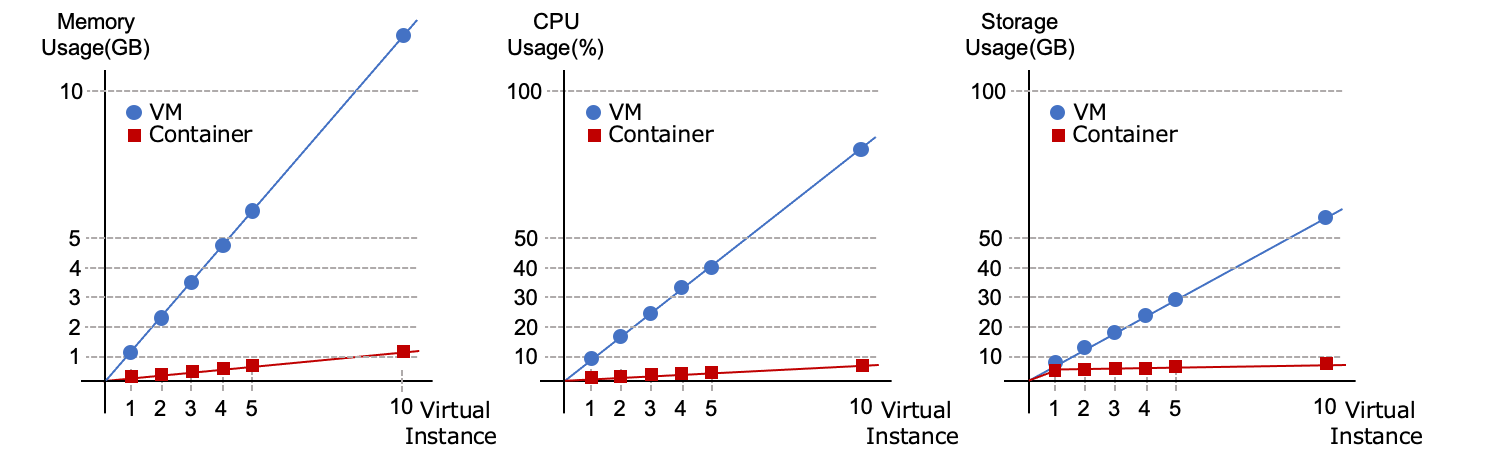
The experiments revealed that containers reproduce vulnerabilities with a Jaccard similarity index of 0.993 when compared to VMs, indicating a minimal discrepancy. The small variances typically arose from the need to adjust configurations or start certain services in container environments. Notably, the experiments consistently showed significant resource savings when using containers (Figure 3).
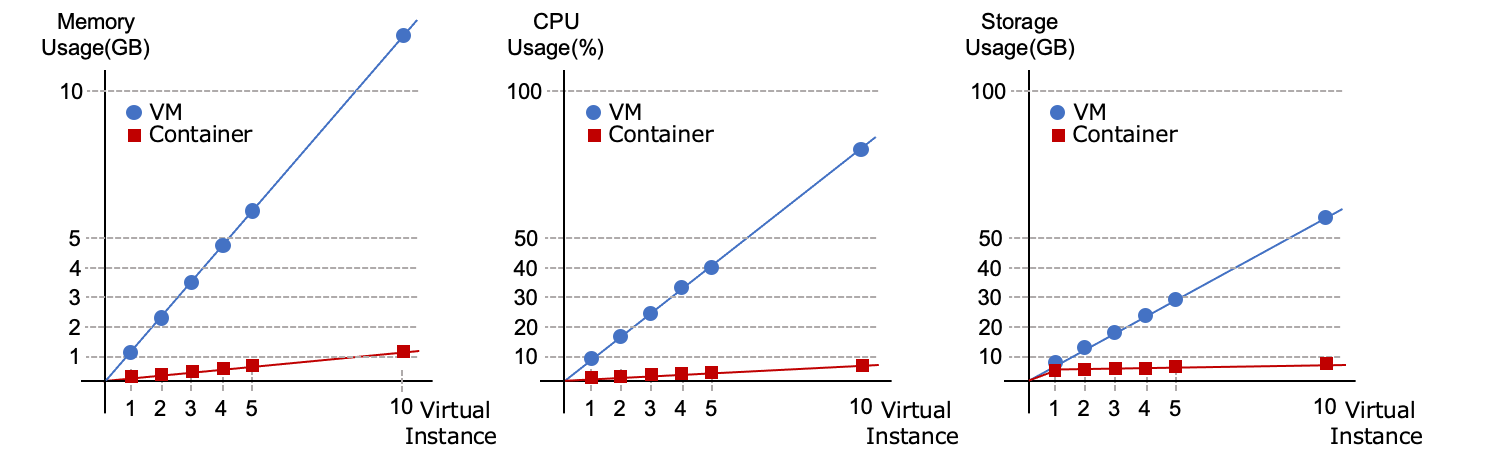
Figure 3: Comparison of resource consumption as the number of virtual instances increases.
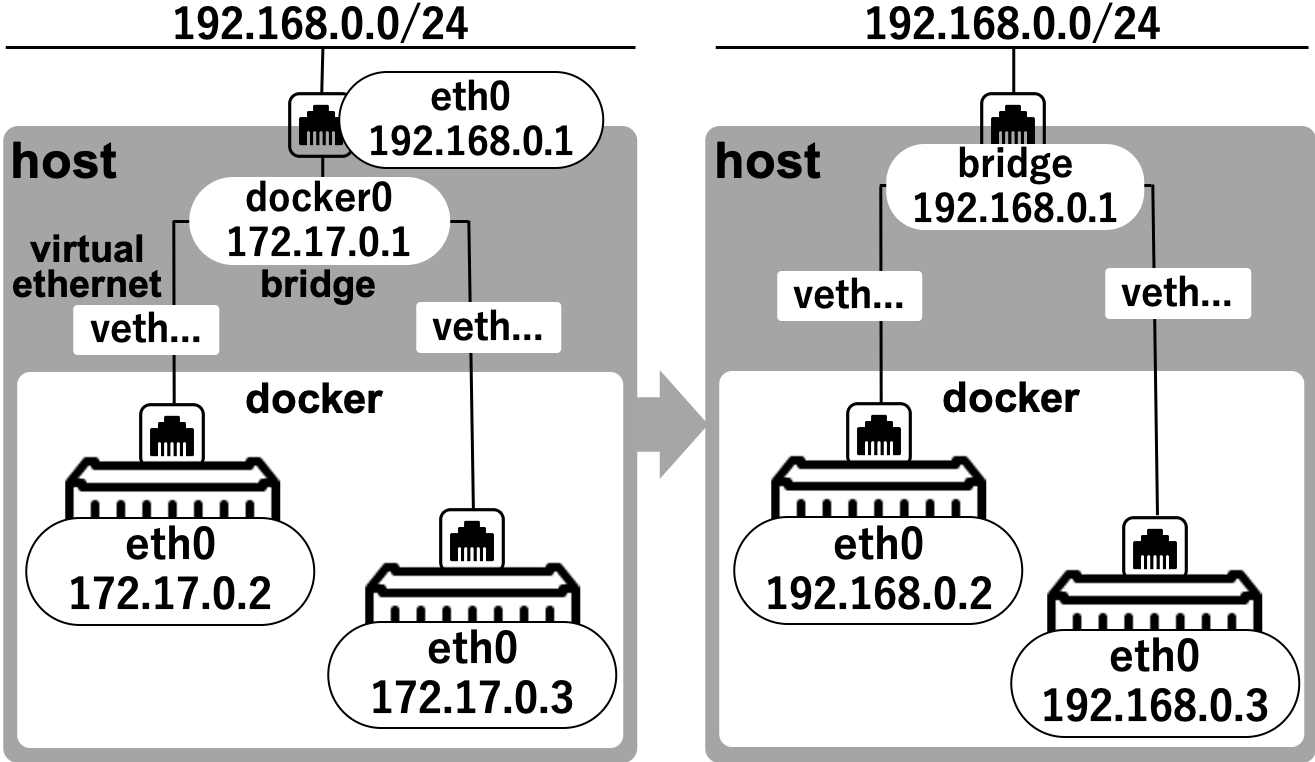
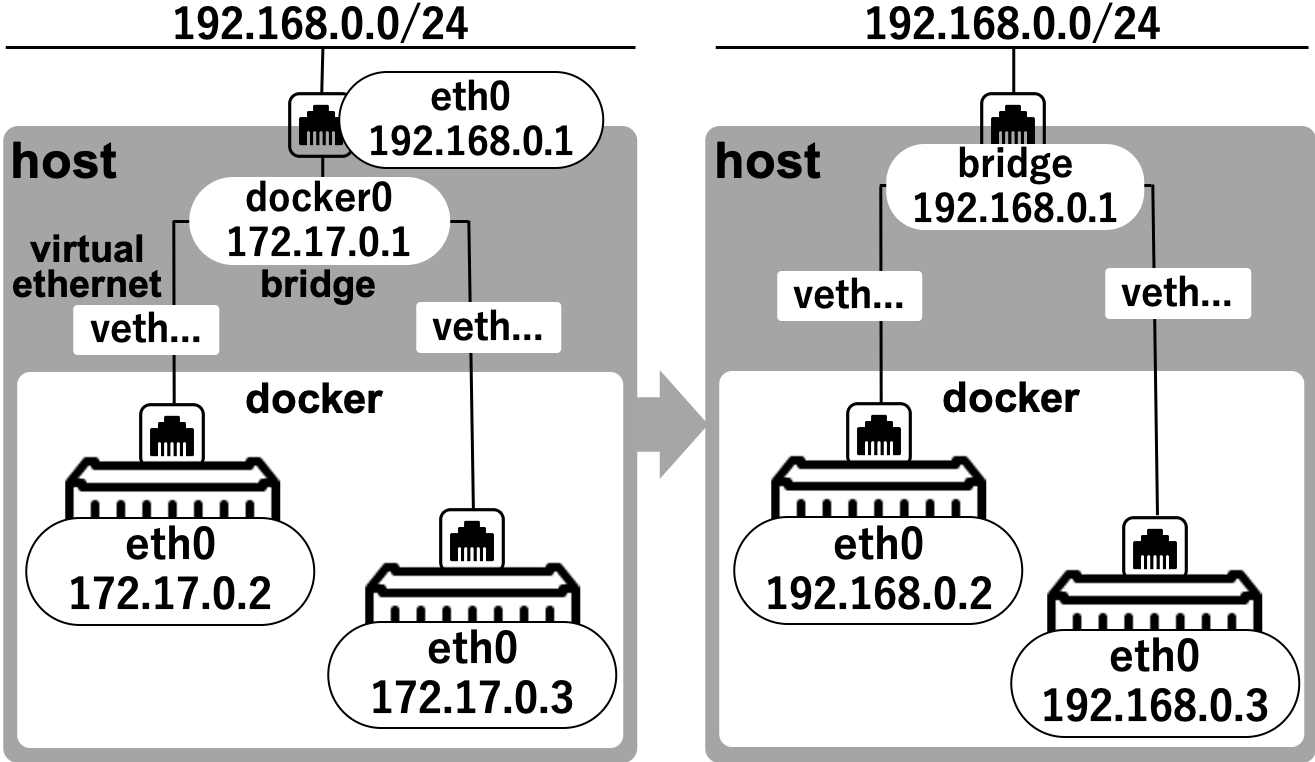
Figure 4: Network Settings on Docker.
Limitations and Considerations
Despite promising results in vulnerability reproduction, the paper notes important limitations in container environments. Containers exhibit different behaviors under certain conditions due to shared resources with the host OS, potentially leading to performance bottlenecks or different operational characteristics compared to VMs. For instance, memory-intensive operations could impact the host OS's performance, a scenario not observed in VM environments.
Furthermore, kernel-level exploits or vulnerabilities reliant on exact hardware emulation may not be equivalently reproducible in containers, potentially affecting scenario authenticity in training exercises. Consequently, careful consideration is necessary in scenario design and execution when opting for container-based cyber ranges.
Implications and Future Work
This research underscores the potential for container technology to transform cyber range deployments. By facilitating a low-cost, scalable, and resource-efficient framework for cybersecurity education, container-based solutions can democratize access to cutting-edge training environments. The verified high similarity in vulnerability reproducibility advocates for broader adoption.
Future work could explore enhancing container isolation capabilities and resource management facilities to mitigate identified limitations further. The integration of container-based cyber ranges in institutional curricula could significantly expedite the training of cybersecurity professionals, addressing the global skills gap in this domain.
Conclusion
In conclusion, the study provides strong empirical evidence supporting the use of container-based virtualization in cyber ranges, highlighting their efficiency and adaptability in emulating real-world environments. These findings pave the way for innovative developments in cybersecurity training, making it more accessible and sustainable without compromising on the quality of educational outcomes.