- The paper presents a risk assessment framework that uses ellipsoidal approximations via SDP to define the stealthy reachable set amid noise and uncertainty.
- It introduces two security metrics—the stealthy reachable set volume and the distance to critical states—to quantify resilience against undetectable attacks.
- Numerical evaluations demonstrate that controller/monitor co-design can effectively enhance safety by increasing the separation between attack-induced and critical system states.
Risk Assessment and Security Metrics for Connected Vehicle Platoons under Stealthy V2V Network Attacks
Introduction and Motivation
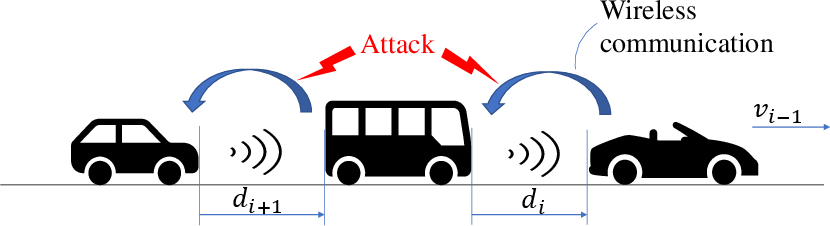
The increasing deployment of Cooperative Adaptive Cruise Control (CACC) in connected and automated vehicles (CAVs) introduces cyber-physical vulnerabilities via Vehicle-to-Vehicle (V2V) communication networks. While CACC architectures deliver string stability and traffic throughput improvements, their reliance on networked inter-vehicle data exchange creates an enlarged attack surface for adversaries. This paper provides a comprehensive risk assessment framework for the impact of stealthy attacks on V2V networks within vehicle platooning, with explicit quantification of attacker-induced system states that evade standard detection mechanisms.
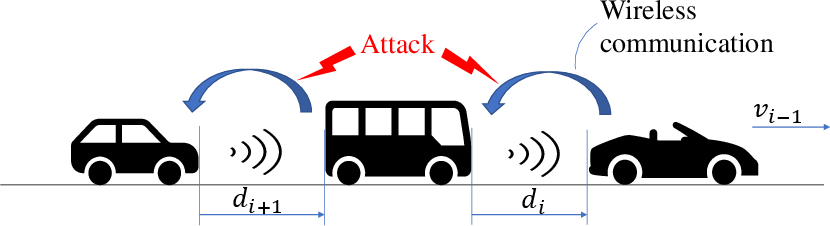
Figure 1: Connected vehicle platoon under network attacks and adversarial signal injection on V2V channels.
Model-Based Detection Framework and Its Limitations
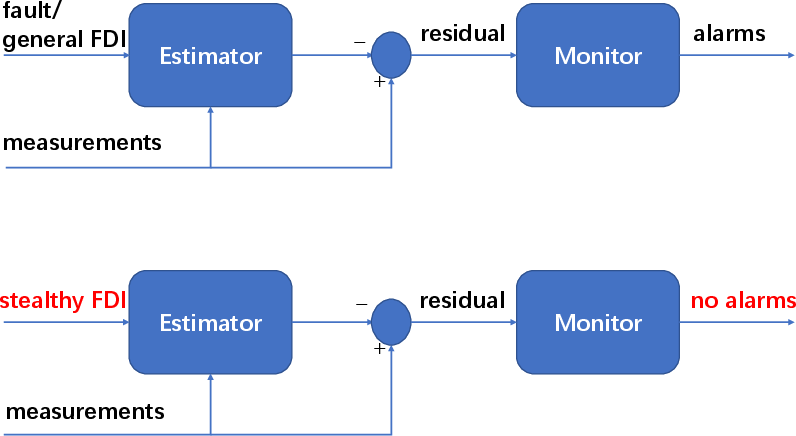
Classical detection schemes for faults and network attacks exploit redundancy between sensor signals and model-based state estimation. The core methodology involves observer-based estimation (via robust discrete-time estimators with Input-to-State Stable error dynamics) and the isolation of anomalies using quadratic residual monitors derived from estimation errors.
However, the paper makes a critical assertion: for CAV platoons subjected to model uncertainties, process/measurement noise, and V2V network effects, even optimally designed estimators yield detection regions that must admit these perturbations. Consequently, attackers can inject false data injection (FDI) signals that remain "stealthy", i.e., undetectable due to overlap with the system’s noise and uncertainty bounds. This is concisely illustrated in:
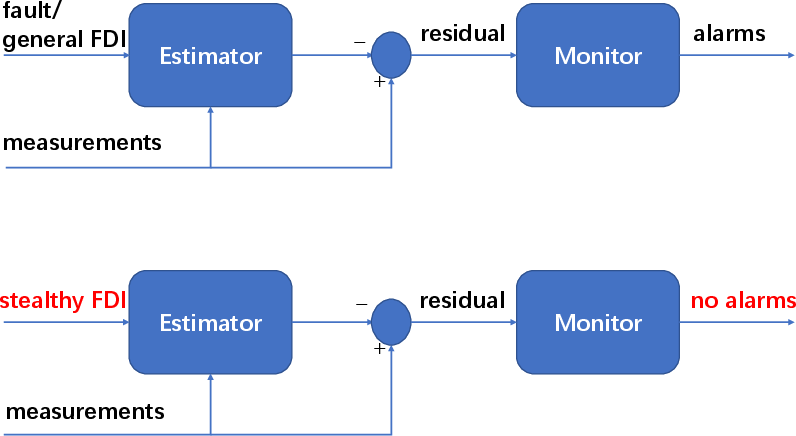
Figure 2: Standard model-based attack detectors capture a wide class of attacks; they fundamentally fail if the attack is stealthy with respect to the model/uncertainty envelope.
The central question addressed is: What are the state trajectories and physical risks that a stealthy adversary can induce, given a specific detection envelope? The answer is provided through two quantitative security metrics:
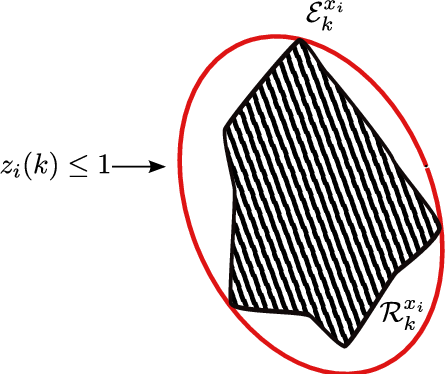
1. Stealthy Reachable Set Volume
The set of possible system states reachable under stealthy attacks (i.e., attacks that do not raise alarms in the residual monitor) is formalized as the stealthy reachable set. Direct computation is intractable; thus, the paper employs outer ellipsoidal approximations computed as a solution to parameterized semidefinite programs (SDPs), optimizing for minimum-volume ellipsoids containing all physically-reachable states. The volume of this ellipsoid serves as a quantifiable security metric for each CAV.
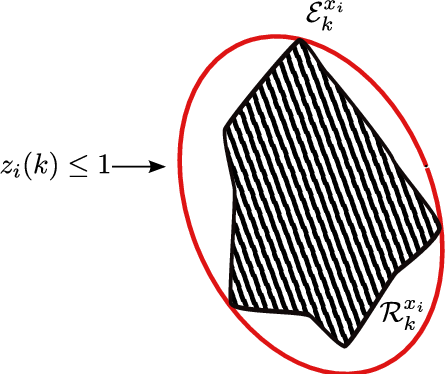
Figure 3: Outer ellipsoidal approximation to the stealthy reachable set for the i-th CAV, capturing all attack-induced states indistinguishable from legitimate system responses.
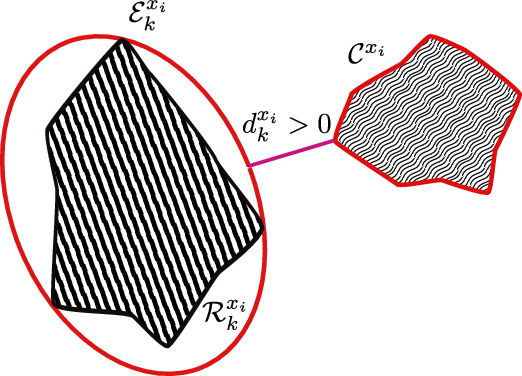
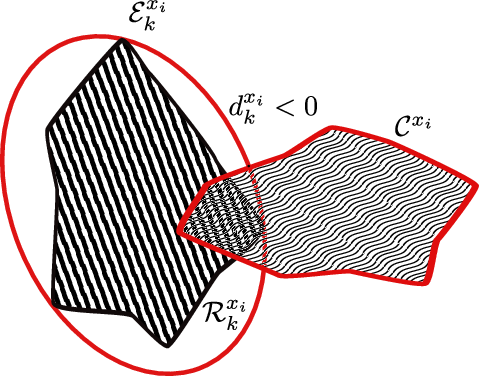
2. Distance to Critical States
The second metric is the minimum Euclidean distance between the ellipsoidal reachable set and a convex set of critical states (e.g., collision, velocity limit violation). For ellipsoid and half-space representations, this minimum distance is obtained in closed form. Positive separation implies that no stealthy attack, as bounded by the detector, can cause system transitions into catastrophic regions. Negative or zero separation denotes physical vulnerability.
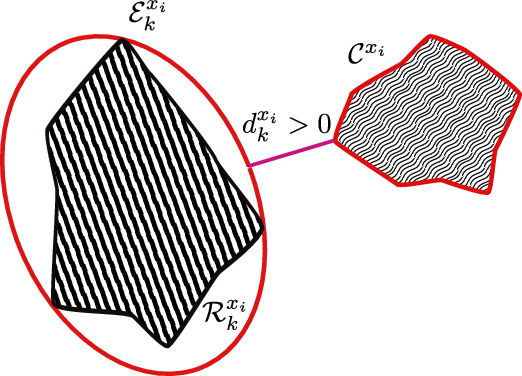
Figure 4: Illustration of a positive minimum distance dk indicating resilience—the attack-induced set does not intersect with crash/overspeed critical states.
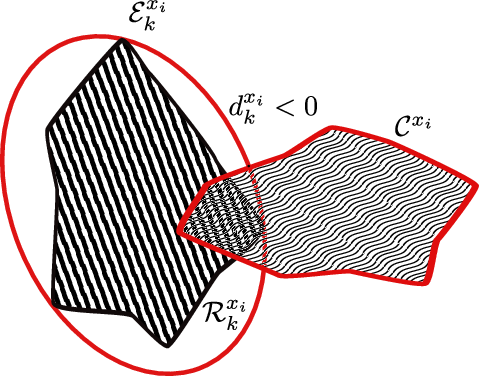
Figure 5: Illustration of negative minimum distance dk, where the reachable set ellipsoid intersects the critical region, indicating physical vulnerability to stealthy attacks.
Convex Synthesis and Observer/Monitor Design
Both the design of the observer gain matrix (to minimize disturbance amplification, as quantified by the ISS gain) and the residual monitor’s threshold ellipsoid (optimized for detection tightness) are formulated as tractable semidefinite programs (SDPs). This allows automated, scalable synthesis applicable to arbitrarily large platoon settings.
The paper demonstrates that the pragmatic construction of estimators and monitors through SDP ensures the residual region is minimal while respecting system noise and modeling uncertainty, leading to optimal detectability of non-stealthy anomalies and maximal restriction of stealthy attacker capabilities.
Numerical Evaluation and Control Redesign Guidance
Simulation experiments on two-vehicle platoons illustrate the machinery:
- For recommended controller parameters (K=[0.2,0.7]) and tight monitor design, both the ellipsoidal reachable set and separation metric confirm resilience against stealthy attacks—no collision or overspeed is physically feasible under stealthy FDI attacks.
- However, for suboptimal controller gain choices (K=[0.9,0.1]), the ellipsoidal set can intersect the critical states for substantial intervals, indicating periods of practical vulnerability.
This analysis directly enables systematic controller/monitor co-design: the control law can be adjusted (e.g., by increasing time headway or redesigning feedback gain) to tune the ellipsoidal set–critical region separation in favor of system safety.
Implications and Theoretical Extensions
The paper establishes the necessity of risk quantification that acknowledges detection limitations due to modeling/system uncertainty. Its SDP-based ellipsoidal containment and distance computation approach is inherently extendable:
- It can be applied to arbitrarily high-dimensional, interconnected CAV platoons without centralized coordination.
- The risk assessment framework is applicable to any CPS where network-induced uncertainties preclude perfect attack detection, including industrial automation and power grid state estimation [e.g., (Viaux et al., 2013)v3], via similar ellipsoidal reachable set techniques.
- The formulation provides provable guarantees: as long as the minimum distance to critical states is positive, the current control/detection scheme is safe against all undetectable attacks; otherwise, mitigation strategies are urgently required.
Additionally, the formalization exposes the fundamental tradeoff between system performance (tight control, fast transient response) and attack resilience in networked feedback systems.
Conclusion
This work provides an explicit, quantitative framework for risk assessment in connected vehicle platoons under adversarial V2V network attacks. By developing tight ellipsoidal approximations to stealthy reachable sets and formulating the control/monitor co-design as convex optimization problems, the authors offer actionable tools to both identify vulnerability to stealthy FDI attacks and guide systematic controller redesign for guaranteed resilience. Future research avenues include scaling the methodology to heterogeneous platoons, time-varying networks, and integration with learning-based anomaly detection, as well as extension to nonlinear dynamics and hybrid system models.