- The paper presents an empirical analysis of 13,000+ ICS devices worldwide, exposing widespread vulnerabilities via OSINT techniques.
- It categorizes risks by vendor and geography, highlighting DoS, data breaches, and tampering issues in major industrial systems.
- The study underscores the urgent need for improved patch management and robust cybersecurity practices to mitigate ICS vulnerabilities.
"The Global State of Security in Industrial Control Systems: An Empirical Analysis of Vulnerabilities around the World" (2111.13862)
Introduction
The study examines the vulnerabilities of Industrial Control Systems (ICS) globally by identifying devices exposed to the public Internet through tools such as Shodan. The presence of these devices online significantly increases the risk of exploitation due to inherent ICS vulnerabilities. The paper provides a comprehensive analysis of various ICS devices' security status, categorizing them by country, vendor, and vulnerability severity based on Common Vulnerabilities and Exposures (CVEs). This analysis offers a compelling view from an attacker's perspective, demonstrating the widespread susceptibility of these systems.
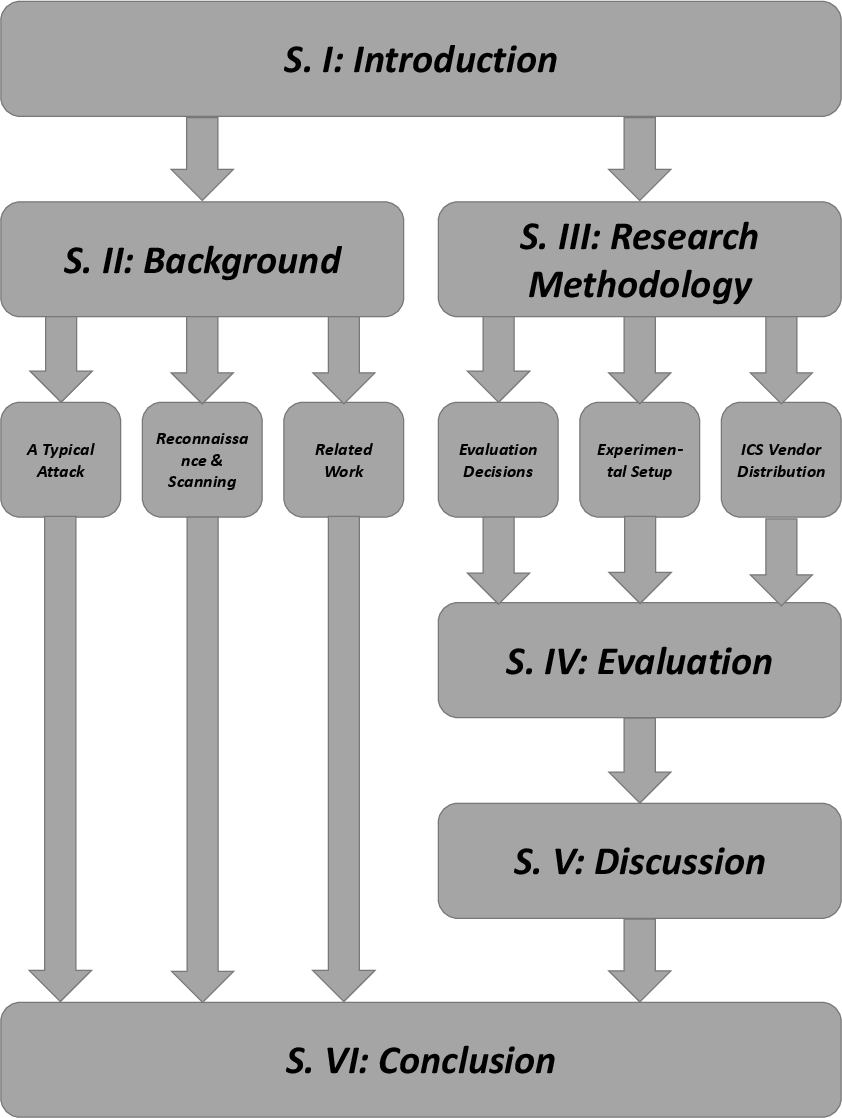
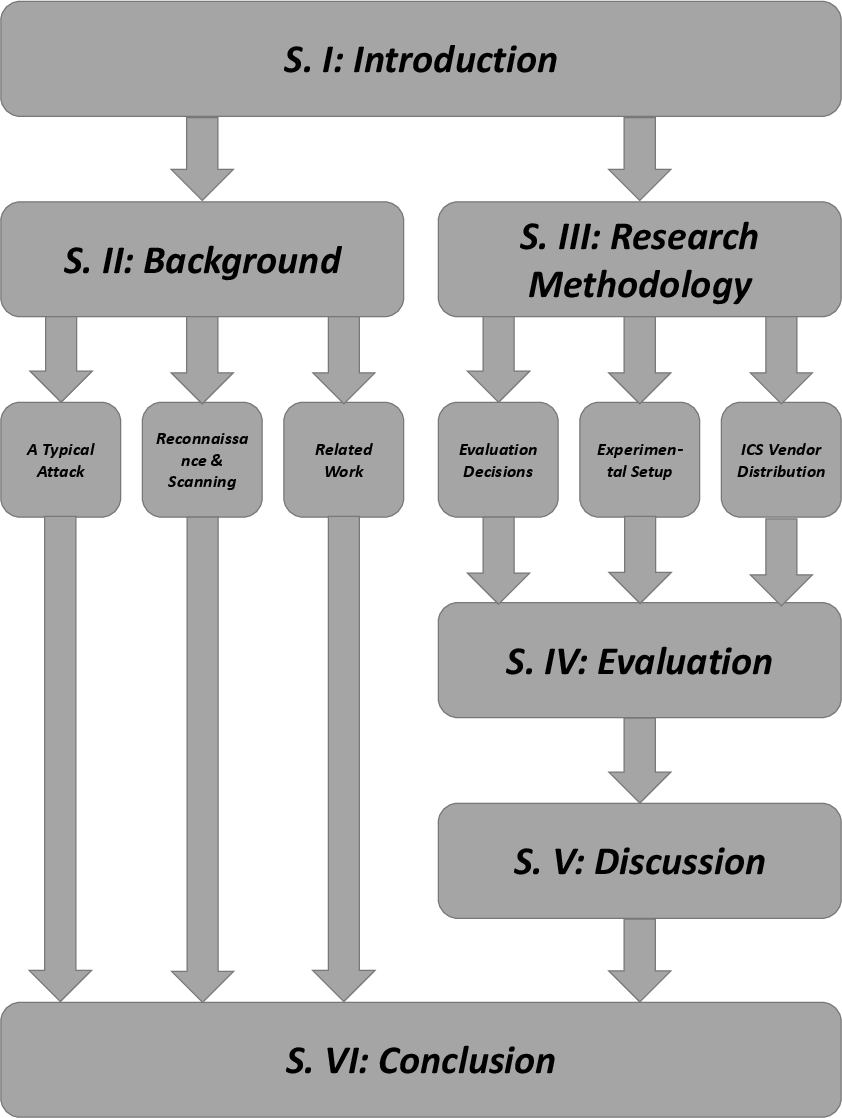
Figure 1: Structure of this Scientific Work.
Methodology
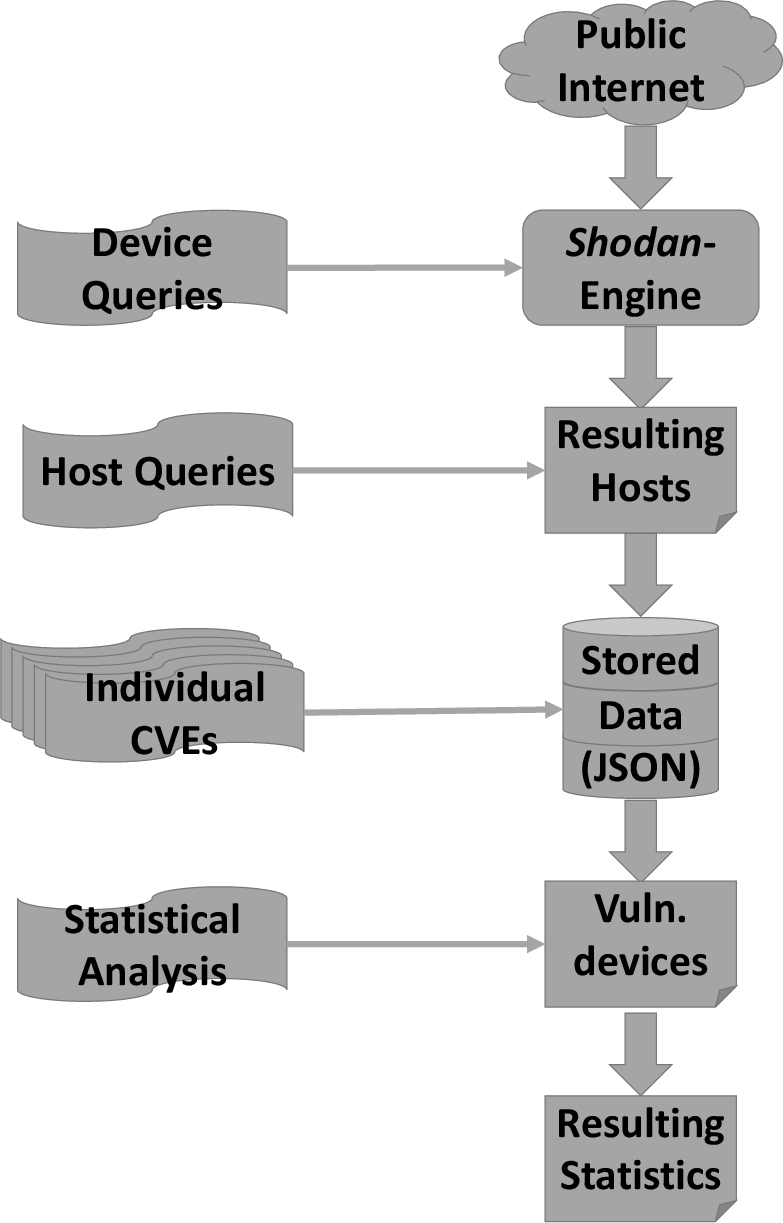
The study employs Open Source Intelligence (OSINT) techniques, primarily leveraging Shodan, an Internet-connected device search engine, to discover and evaluate over 13,000 ICS devices globally. By matching devices to their known vulnerabilities in the National Vulnerability Database (NVD), the research identifies potential security threats. The analysis includes devices from major ICS vendors such as Schneider Electric, Siemens, Omron, Rockwell Automation, and Mitsubishi, providing a broad overview of the ICS security landscape.
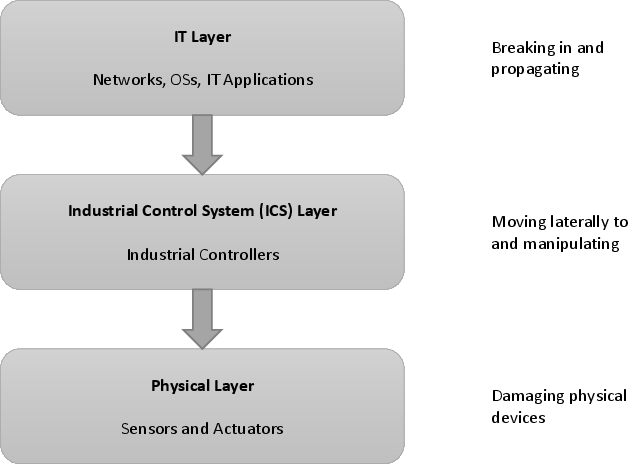
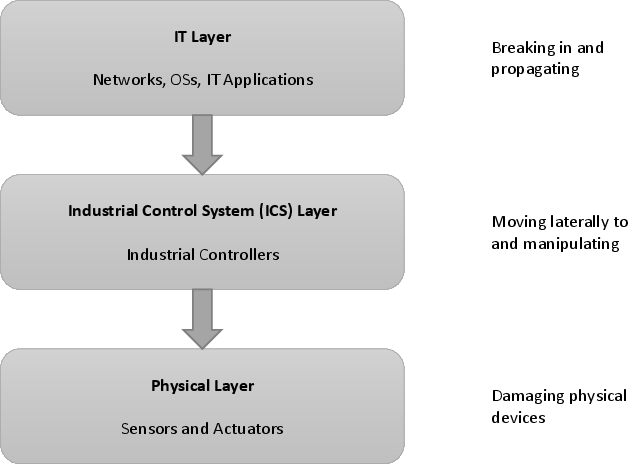
Figure 2: Stages of a Typical Attack on Industrial Applications.
Evaluation
Findings
Schneider Electric BMX P34 Series: Found predominantly in France, with vulnerabilities primarily leading to Denial of Service (DoS) and information disclosure risks.
Siemens S7-300 Series: Largely located in Germany and Italy, these devices exhibit vulnerabilities exposing them to DoS and unauthorized data access.
Omron CJ and CS Series: Predominantly in Spain and France, vulnerabilities here allow for tampering and privilege escalation, posing significant security threats.
Rockwell Automation/Allen-Bradley MicroLogix 1400 Series: Most prevalent in the USA, vulnerabilities include DoS and replay attacks, critical due to their ICS context.
Mitsubishi Melsec Q Series: Mostly found in Japan, showing vulnerabilities mainly leading to DoS conditions.
These findings underline the critical exposure of ICS devices, with DoS being the most common threat across all surveyed systems. The global distribution pattern reflects a significant concentration in European and North American regions.
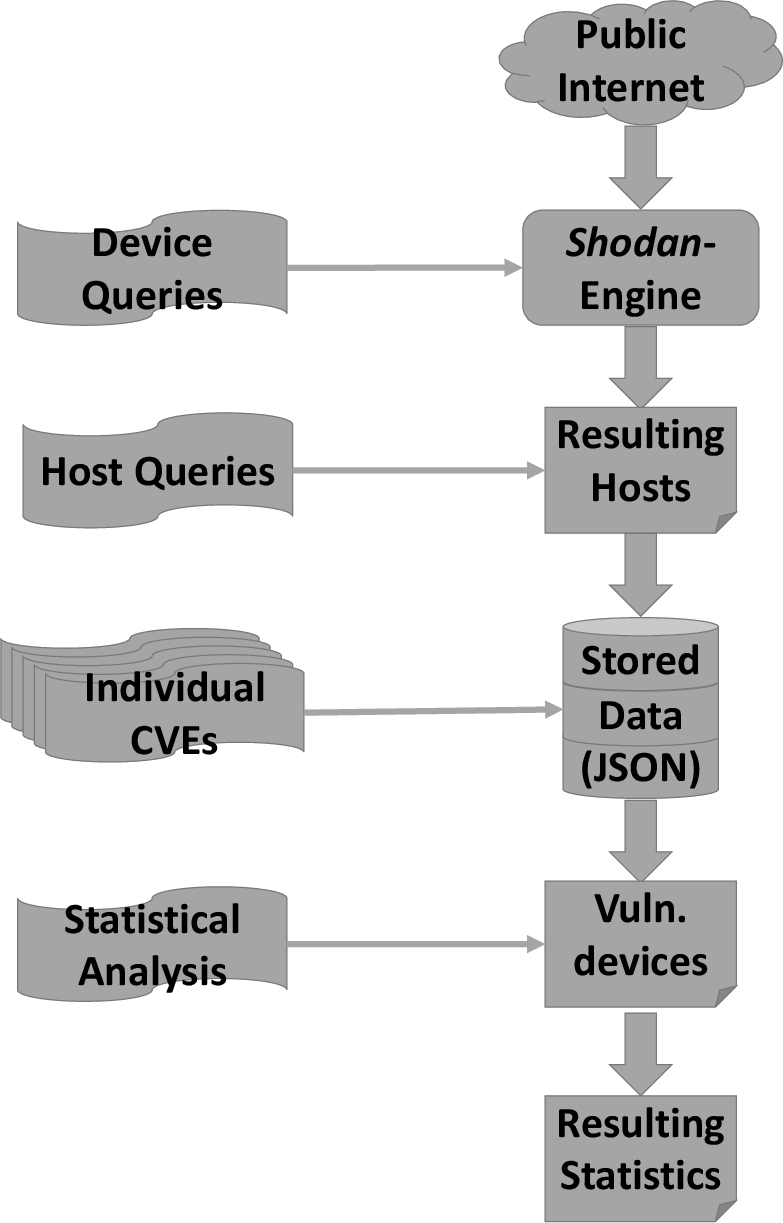
Figure 3: Schematic Overview of Evaluation Process.
Discussion
The analysis confirms the dire state of ICS security globally, where almost every evaluated device has at least one vulnerability. This exposure is exacerbated by poor patch management and the inherent difficulty of updating and securing ICS hardware, which often operate on outdated protocols. The presence of easily exploitable vulnerabilities indicates a lack of adherence to best cybersecurity practices, such as network segmentation and service deactivation.
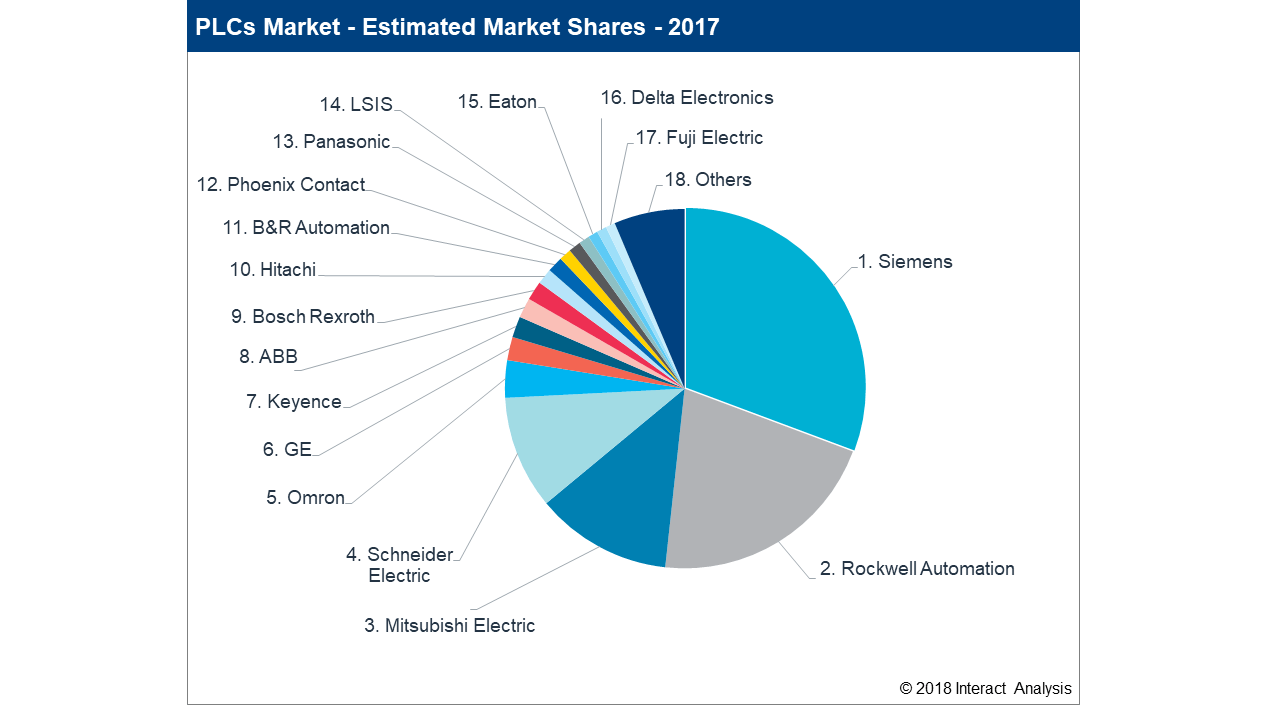
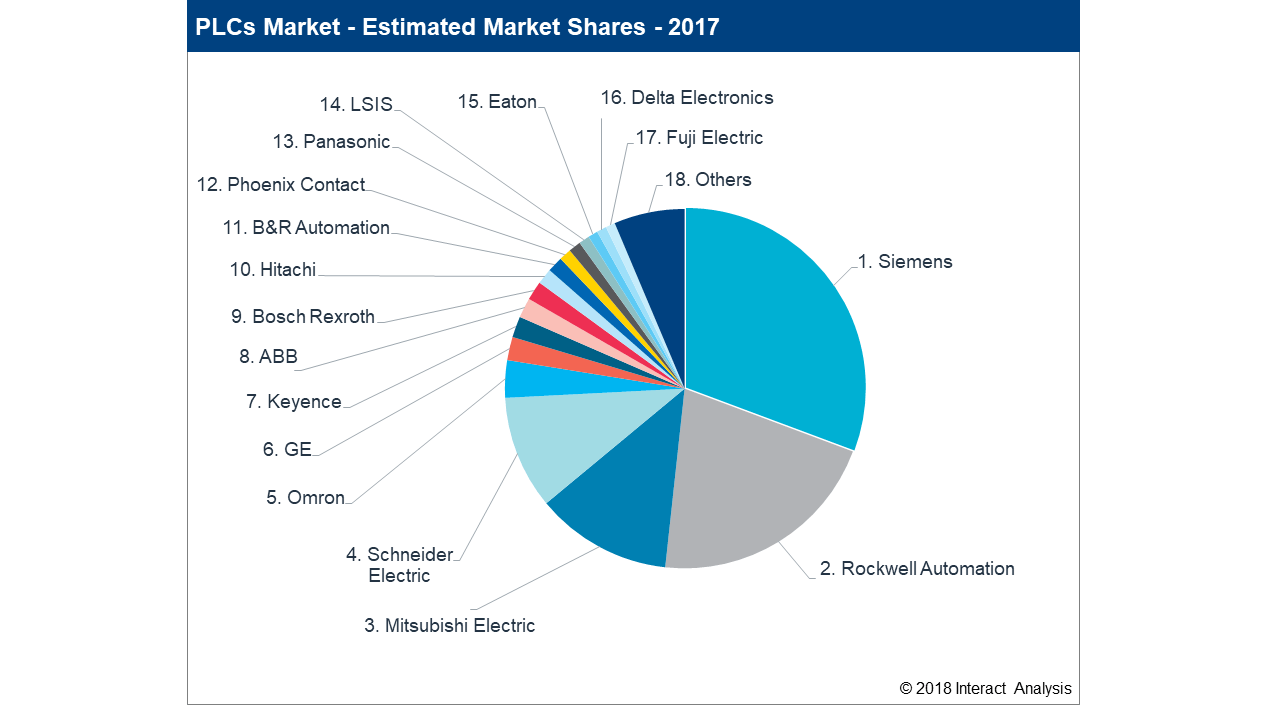
Figure 4: Estimated Market Distribution of PLC vendors according to Dawson [Dawson.2017].
Honeypots are also present, serving as decoys to malicious attackers for research purposes. However, the overall results suggest a genuine widespread exposure rather than artificial signals from such decoys.
Conclusion
The study presents a critical assessment of the ICS security landscape, revealing significant vulnerabilities across major vendors and countries. It underscores the necessity for improved cybersecurity practices, including better patch management and enhanced network security measures. To mitigate these risks, enterprises must prioritize implementing robust cybersecurity frameworks and continually update their ICS to safeguard against potential threats. The findings urge the industry to adopt proactive measures to address these vulnerabilities and enhance the security posture of ICS environments.
The research highlights an urgent need for ICS operators globally to prioritize security and adopt best practices, including isolation from public networks, deactivation of unnecessary services, and regular updates and patches. The comprehensive analysis serves as a call to action for better industrial cybersecurity standards, crucial for preventing potentially disastrous cyber incidents.