- The paper introduces a two-stage framework combining a GAN discriminator with a CNN for initial adversarial screening and refined intrusion detection in IoT systems.
- The methodology employs FGSM for generating adversarial examples and leverages the Edge-IIoTset dataset to validate detection performance under various attack scenarios.
- The framework achieves high accuracy, precision, recall, and F1-scores, significantly outperforming traditional CNN models in adversarial settings.
A GAN-Driven Cyber Threat Intelligence Framework for IoT Security
Introduction
The Internet of Things (IoT) transforms the interaction with digital environments, primarily through the provision of high-speed, low-latency communication for an ever-increasing array of connected devices. With the advent of 6G networks, there is potential for even greater connectivity and efficiency across IoT devices, however, they bring along significant security challenges. This paper proposes an innovative two-stage intrusion detection framework leveraging Generative Adversarial Networks (GANs), which ensure higher resilience and robustness against adversarial attacks and intrusions in IoT systems.
Methodology
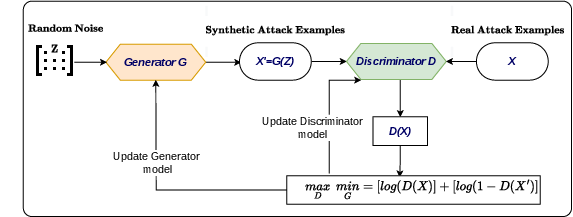
The proposed framework employs GANs to equip IoT systems with robust detection mechanisms against adversarial examples. The GAN model integrates two principal components: the generator and the discriminator. The generator is tasked with creating complex adversarial examples, whereas the discriminator distinguishes between authentic and fabricated anomalies (Figure 1).
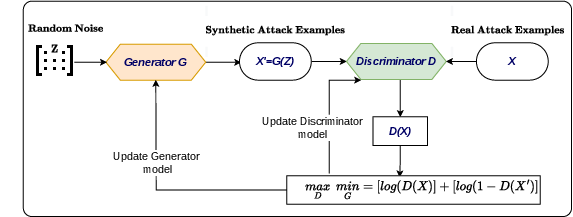
Figure 1: The proposed GAN model training for adversarial examples detection
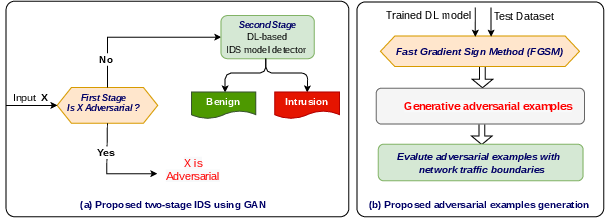
Additionally, a two-phase detection workflow is executed, as illustrated in Figure 2. The first phase utilizes the discriminator for preliminary adversarial detection, followed by a Convolutional Neural Network (CNN) model for detailed intrusion detection of anomalous and regular data.
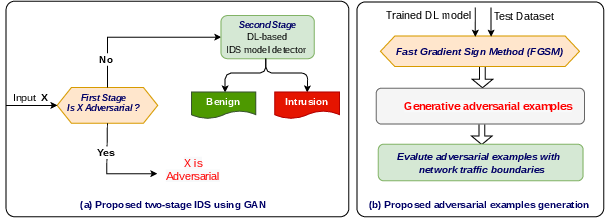
Figure 2: A flow chart of the proposed cyber threat intelligence detection framework using two detectors.
Model Implementation and Training
The methodology capitalizes on the fast-gradient sign method (FGSM) for crafting adversarial examples, which are subsequently evaluated by the GAN discriminator. Using the Edge-IIoTset dataset, a standard for IoT and IIoT applications, the framework performed thorough evaluations. The CNN component of the framework was configured with multiple convolutional layers, fully connected layers, and employed the ReLU and softmax activation functions for effective feature extraction and classification of intrusions.
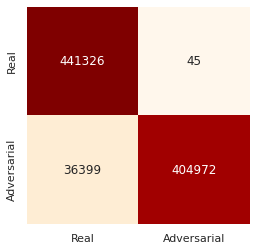
The discriminator's training loss behavior depicts a swift reduction in error rates, confirming its efficiency in apprehending real data representations (Figure 3).
(Figure 3)
Figure 3: Confusion matrix of Adversarial examples detection using GAN discriminator (first-stage detection).
Interestingly, the consensus achieved between the discriminator's predictions and input authenticity points towards competitive performance of the GAN framework in deceptive scenarios.
The evaluation showed that the two-stage framework achieved high accuracy and resistance against adversarial examples, even when exposed to low epsilon perturbations during FGSM generation. The comprehensive confusion matrices highlighted the effectiveness of the GAN-based adversarial detection, displaying a remarkable accuracy gain over conventional CNN models, which suffered drastically under adversarial influence (Figure 4).
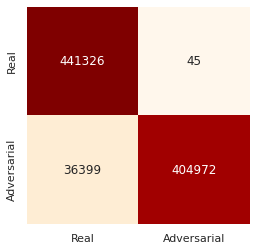
Figure 4: Loss and Accuracy of CNN training and evaluation
Moreover, the classification report the framework achieved includes high precision, recall, and F1-scores across various IoT attack categories, demonstrating robust detection capabilities.
Conclusion
The proposed GAN-driven cyber threat intelligence framework significantly strengthens IoT ecosystems against adversarial and intrusion threats. Ensuring a secure trajectory for IoT operations, the method provides cutting-edge mitigation of adversarial impacts and enhances safe deployment in 6G IoT environments. Recognizing the potential of GANs in adversarial context for other domains opens avenues for future developments in AI security systems.