- The paper introduces HoneyIoT, an adaptive high-interaction honeypot that uses reinforcement learning to realistically emulate IoT devices.
- It employs a Markov Decision Process framework and Proximal Policy Optimization to dynamically generate authentic responses based on live attack traces.
- Evaluation shows HoneyIoT outperforms traditional honeypots with longer attack sessions and increased malware collection, demonstrating improved deception and resilience.
Summary of "HoneyIoT: Adaptive High-Interaction Honeypot for IoT Devices Through Reinforcement Learning" (2305.06430)
Introduction
The proliferation of IoT devices across various sectors has led to significant security concerns due to inherent vulnerabilities in these devices. Traditional honeypots used to collect attack data and analyze attack methodologies are limited by their inability to mimic the varied and dynamic nature of IoT devices accurately. The paper introduces "HoneyIoT," a novel high-interaction honeypot that employs reinforcement learning (RL) to adaptively and covertly interact with attackers, learn from attack patterns, and generate authentic responses that can deceive sophisticated reconnaissance and evasion techniques utilized by modern attackers.
Background and Motivation
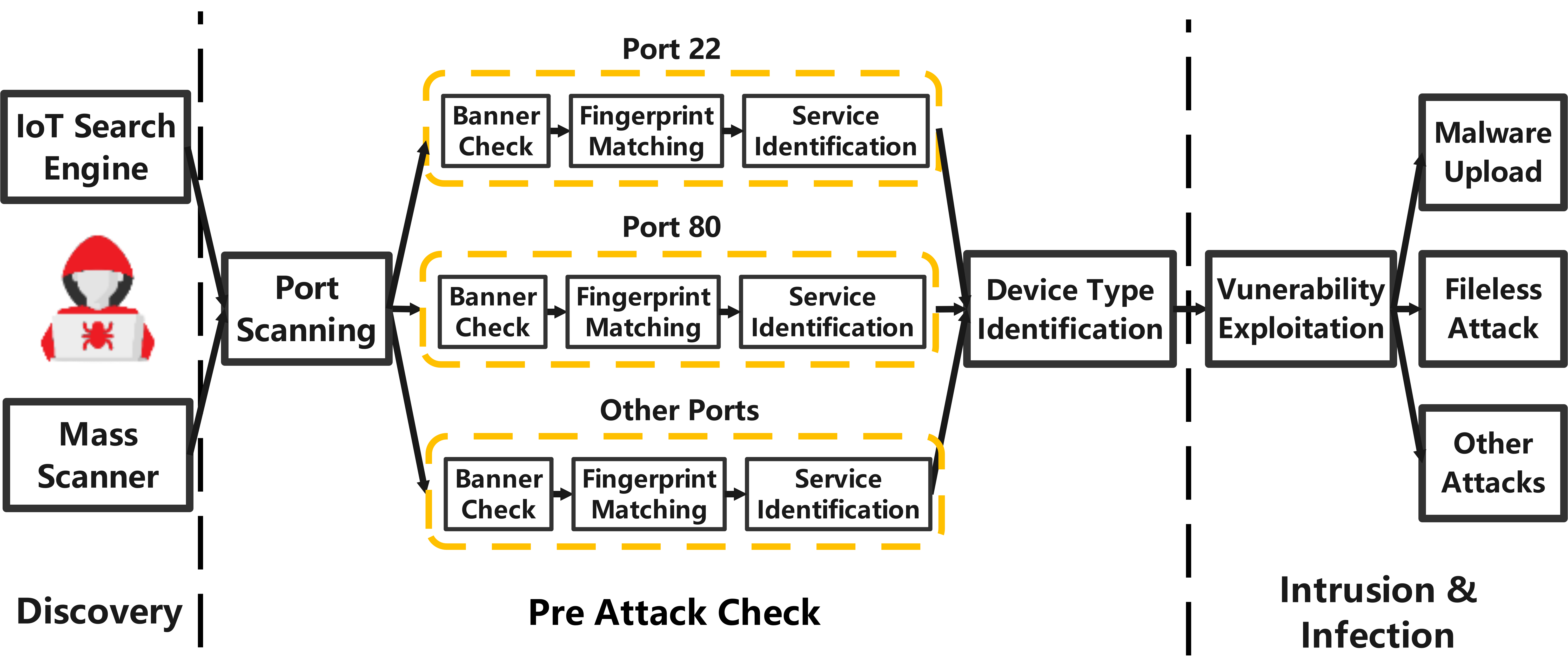
IoT devices are frequent targets for attackers, primarily due to vulnerabilities arising from outdated security measures. Conventional honeypots fail in the IoT context due to their static nature and inability to represent the heterogeneity of IoT systems. To address these challenges, HoneyIoT deploys an adaptive RL-based system to dynamically engage with attackers. This adaptability is key to deceiving attackers' pre-attack checks that typically exploit vulnerabilities unique to specific IoT device types or firmware.
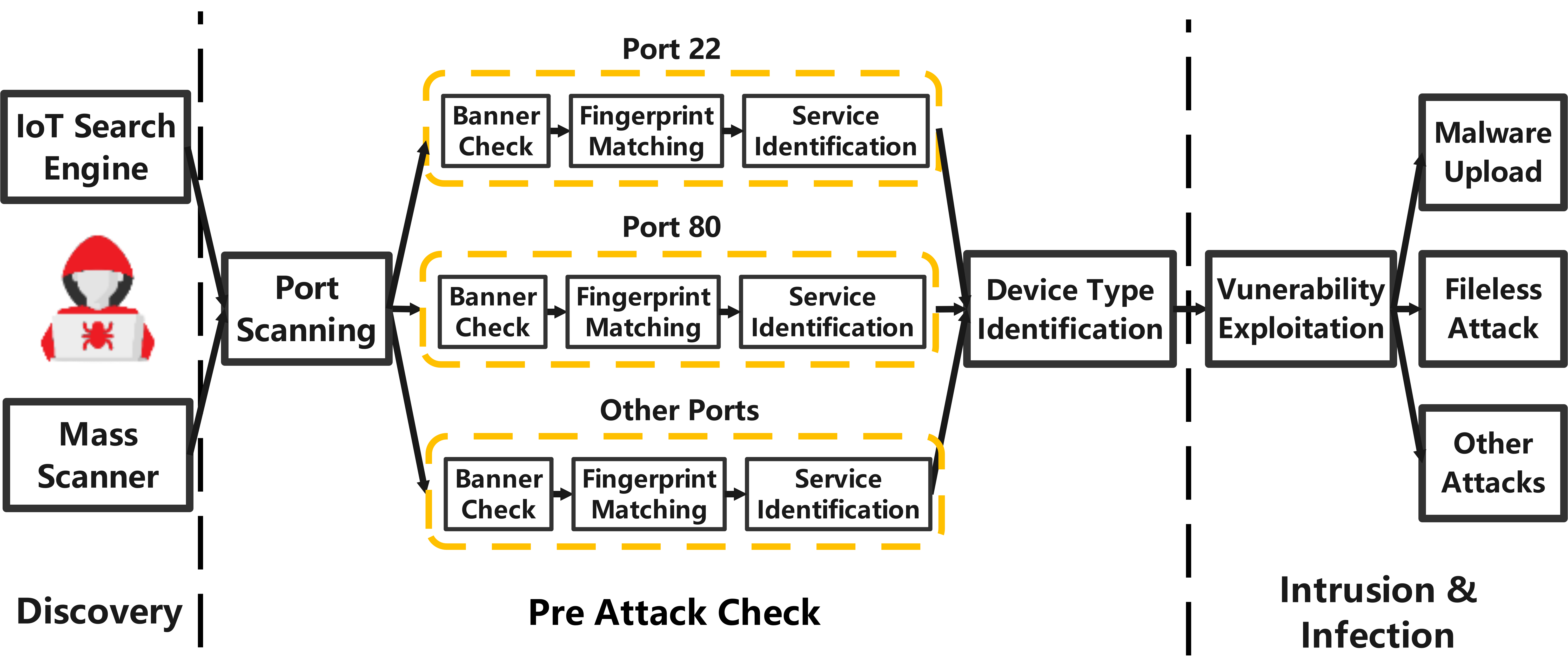
Figure 1: Attacks against IoT devices.
Attack Trace Collection
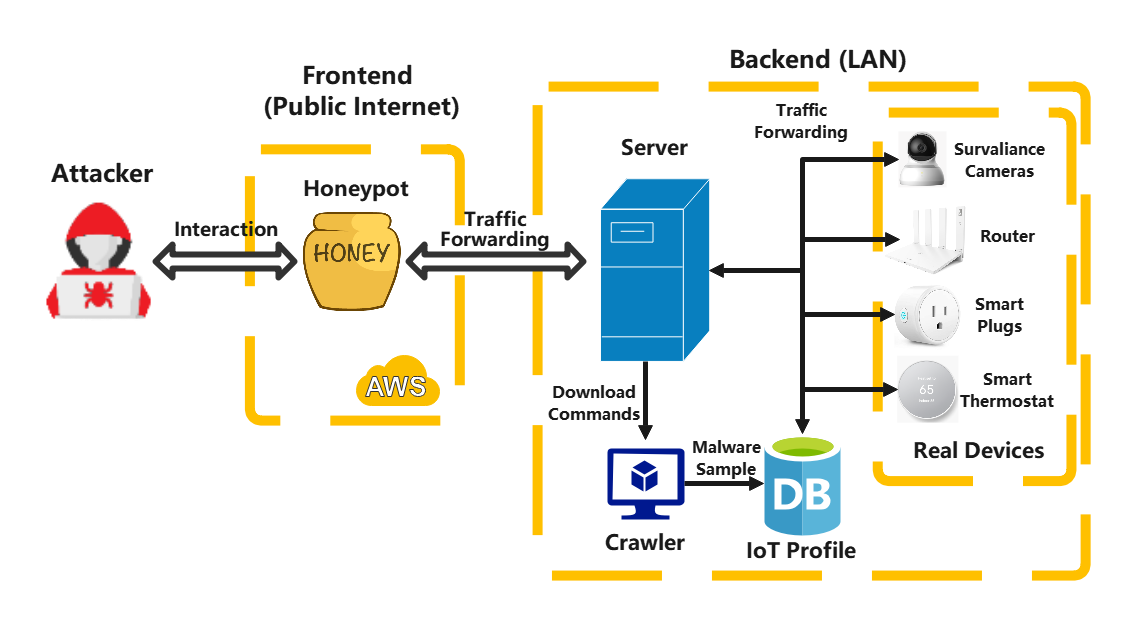
HoneyIoT's effectiveness hinges on a comprehensive attack trace collection process, involving real IoT devices subjected to live Internet attacks. By redirecting attack traffic to an array of actual devices, HoneyIoT captures diverse attack traces that reflect authentic attacker strategies, the details of which are crucial in modeling attack behaviors within a Markov Decision Process (MDP).
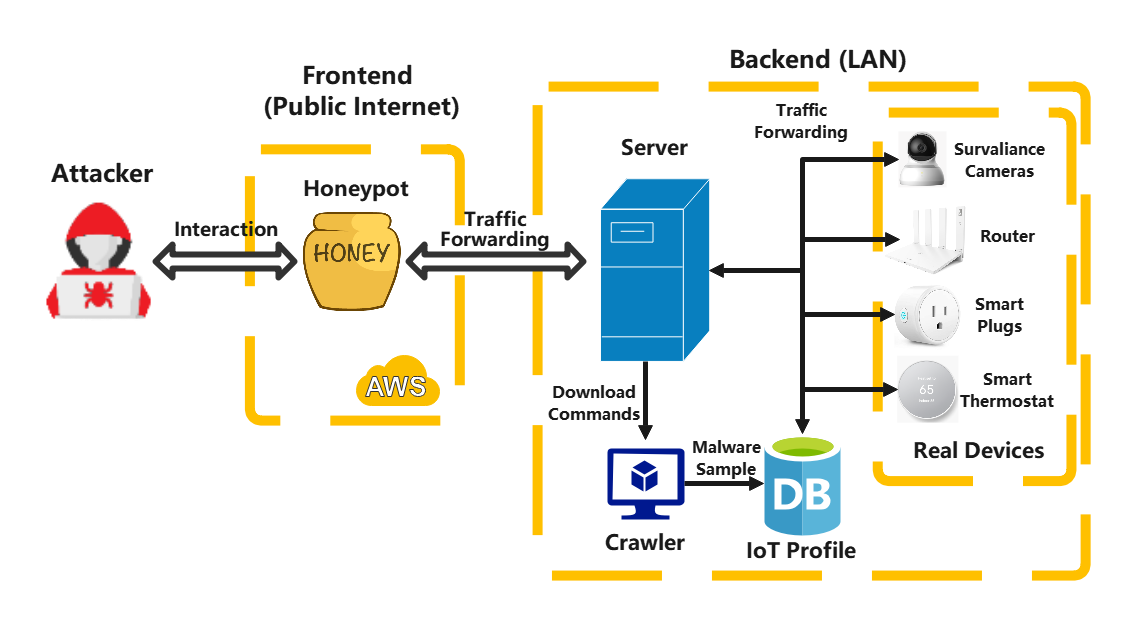
Figure 2: Attack trace collection based on real IoT devices.
Adaptive Honeypot Design
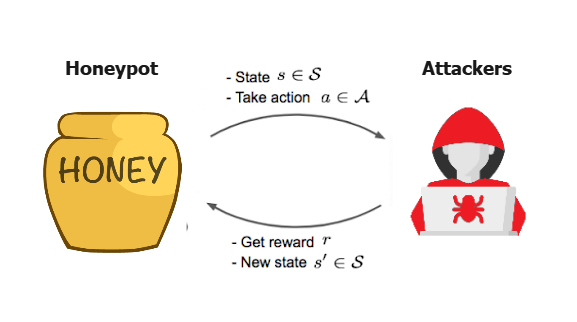
HoneyIoT utilizes a RL framework to maximize engagement with attackers. It models the interaction between attackers and honeypots as an MDP, where states represent the attacker's requests, actions correspond to possible honeypot responses, and rewards are based on the attacker's behavior, such as malware upload attempts. The training of the RL agent leverages various algorithms, with Proximal Policy Optimization (PPO) outperforming others in efficiency and adaptability.
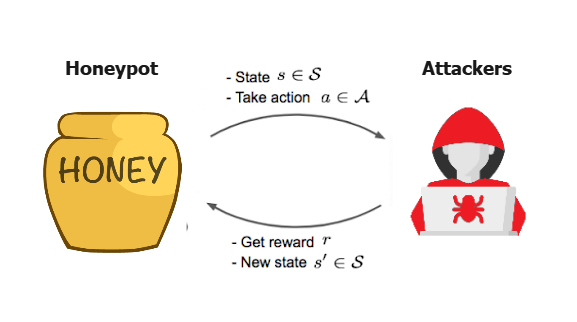
Figure 3: Reinforcement learning model.
Content Mutation Strategy for High Fidelity
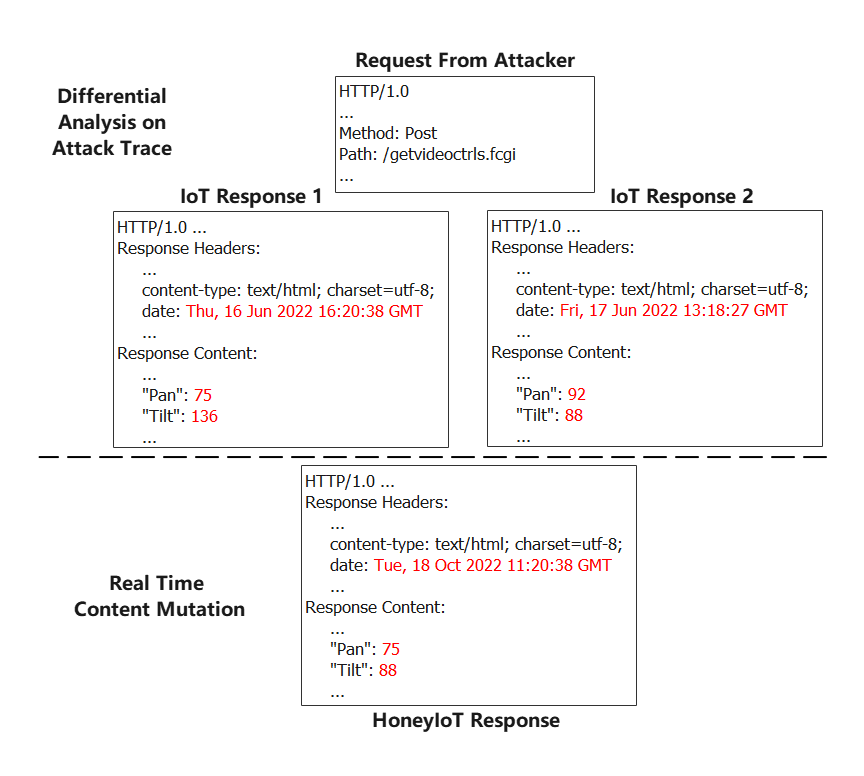
HoneyIoT employs differential analysis to continuously mutate response content, thwarting fingerprinting attacks commonly used to identify honeypots. By analyzing variations in responses from real devices, HoneyIoT identifies mutation fields that are dynamically adjusted to maintain response authenticity. Categories include timing, system, and random fields, all of which contribute to crafting responses that are virtually indistinguishable from those generated by legitimate devices.
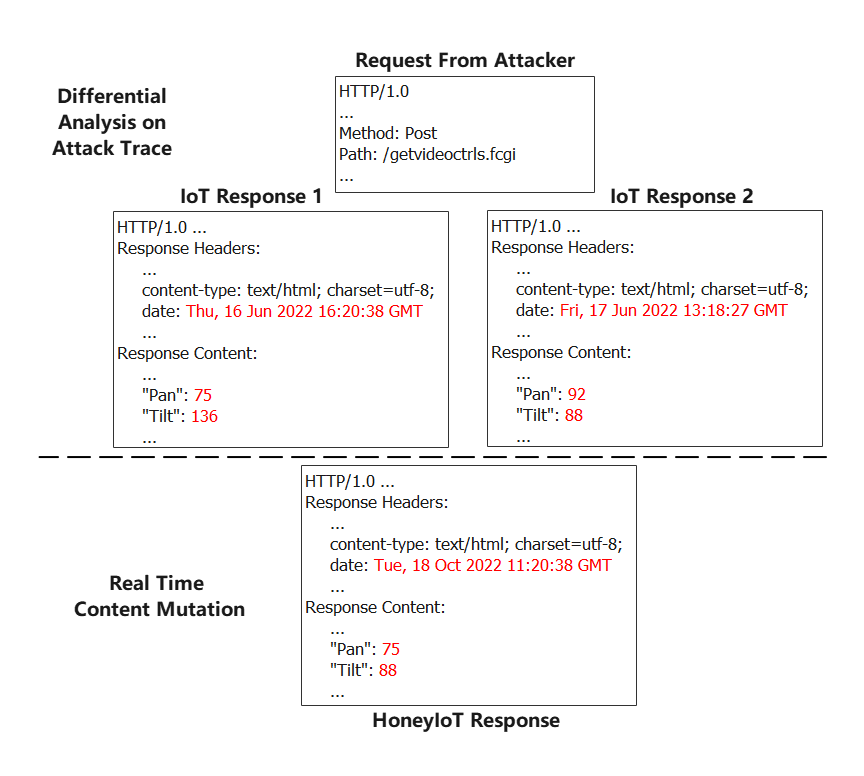
Figure 4: An example of using differential analysis to update the mutation field.
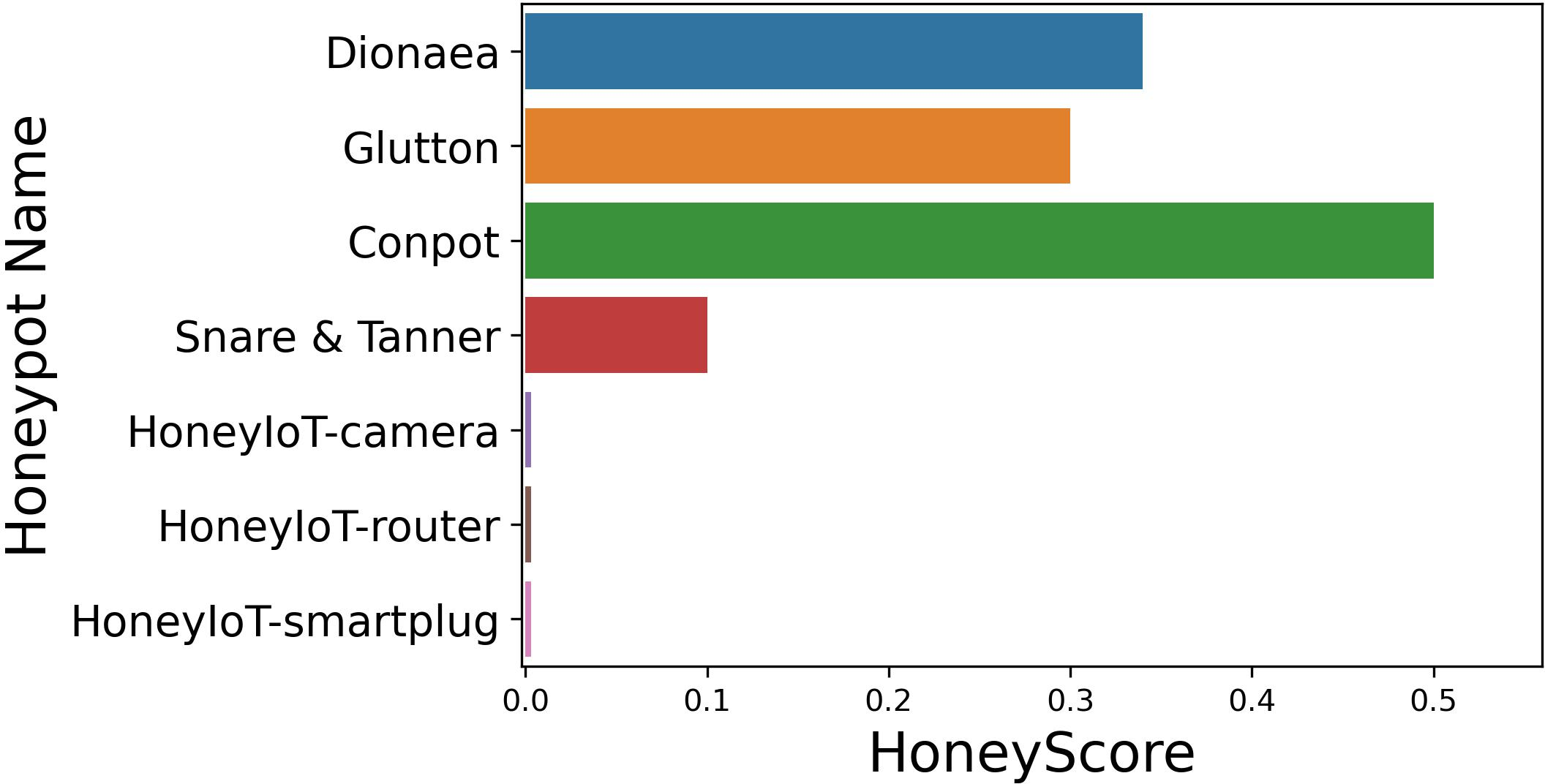
HoneyIoT was evaluated against conventional and next-generation reconnaissance tools by deploying instances on the public Internet. It demonstrated robust performance, engaging attackers more convincingly than both existing honeypots and a controlled baseline setting. Metrics such as average session length and malware collection volume substantiate HoneyIoT's effectiveness. Furthermore, it remains covert against detection tools like Shodan's honeyscore, confirming its resilience.
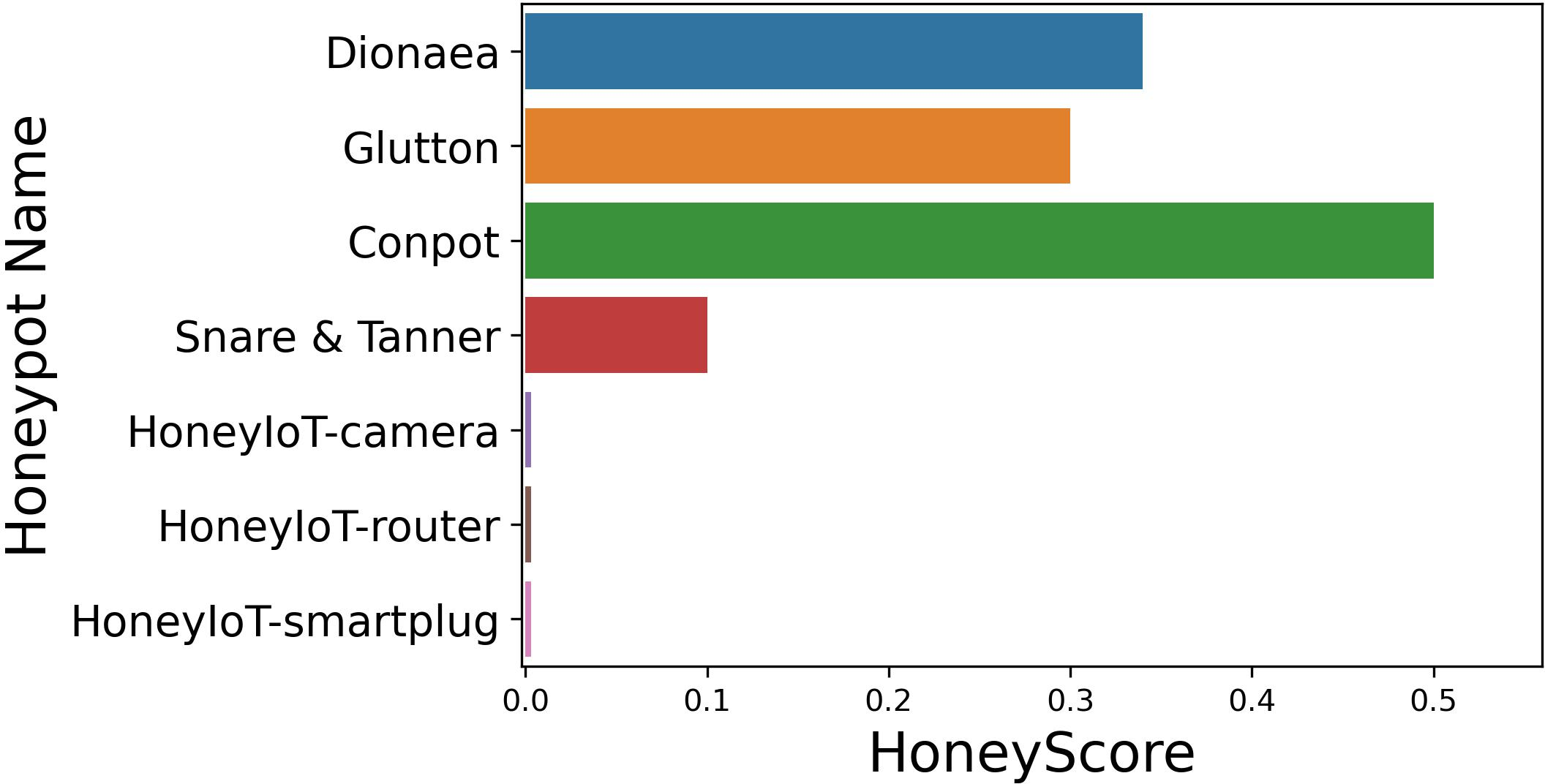
Figure 5: Honey Score for existing honeypots and HoneyIoT.
Conclusion and Future Work
The introduction of HoneyIoT represents a significant advancement in IoT security honeypots, providing adaptive high-fidelity interactions that mislead attackers while gathering valuable attack data. Future directions include refining response consistency and expanding HoneyIoT's capabilities to emulate a broader spectrum of IoT devices across different environments. The ultimate aim is to use the collected data to proactively identify emerging threats and zero-day exploits.
In conclusion, HoneyIoT addresses significant challenges in IoT security by leveraging machine learning to enhance honeypot interaction fidelity, demonstrating potential for wider IoT device protection through adaptive and realistic emulation.