- The paper demonstrates that acoustic side-channel vulnerabilities in keyboards can be exploited via timing, frequency, and geometry-based techniques.
- It evaluates various recording media and keyboard types, highlighting the susceptibility of mechanical keyboards to sound-based attacks.
- The study underscores the urgent need for robust countermeasures to protect data integrity in keyboard input systems.
Acoustic Side-Channel Attacks on Keyboards: An Exploration of Vulnerability
Introduction
The study of acoustic side-channel attacks on keyboards highlights a significant vulnerability in security systems, wherein attackers exploit sound emanations produced during keystrokes to decipher sensitive information. With advancements in technology, particularly microphone enhancements, the feasibility and accuracy of these attacks have increased. This essay provides an in-depth analysis of existing research, exploring attack methodologies, threat models, and potential countermeasures within the domain of keyboard-based acoustic side-channel attacks.
Feasibility of Acoustic Side-Channel Attacks
Acoustic side-channel attacks exploit the unique sounds generated when keys on a mechanical keyboard are pressed. The feasibility of these attacks derives from two main factors: the physical acoustics of keyboards and the typing styles of individuals.
Distinct sounds arise from the structural differences between keys, with factors such as key pressure and angle contributing to sound variability (Figure 1). These attributes, combined with the typing habits of users, create possibilities for differentiating keystrokes from recorded acoustic data.




Figure 1: Examples of Physical Proximity scenarios.
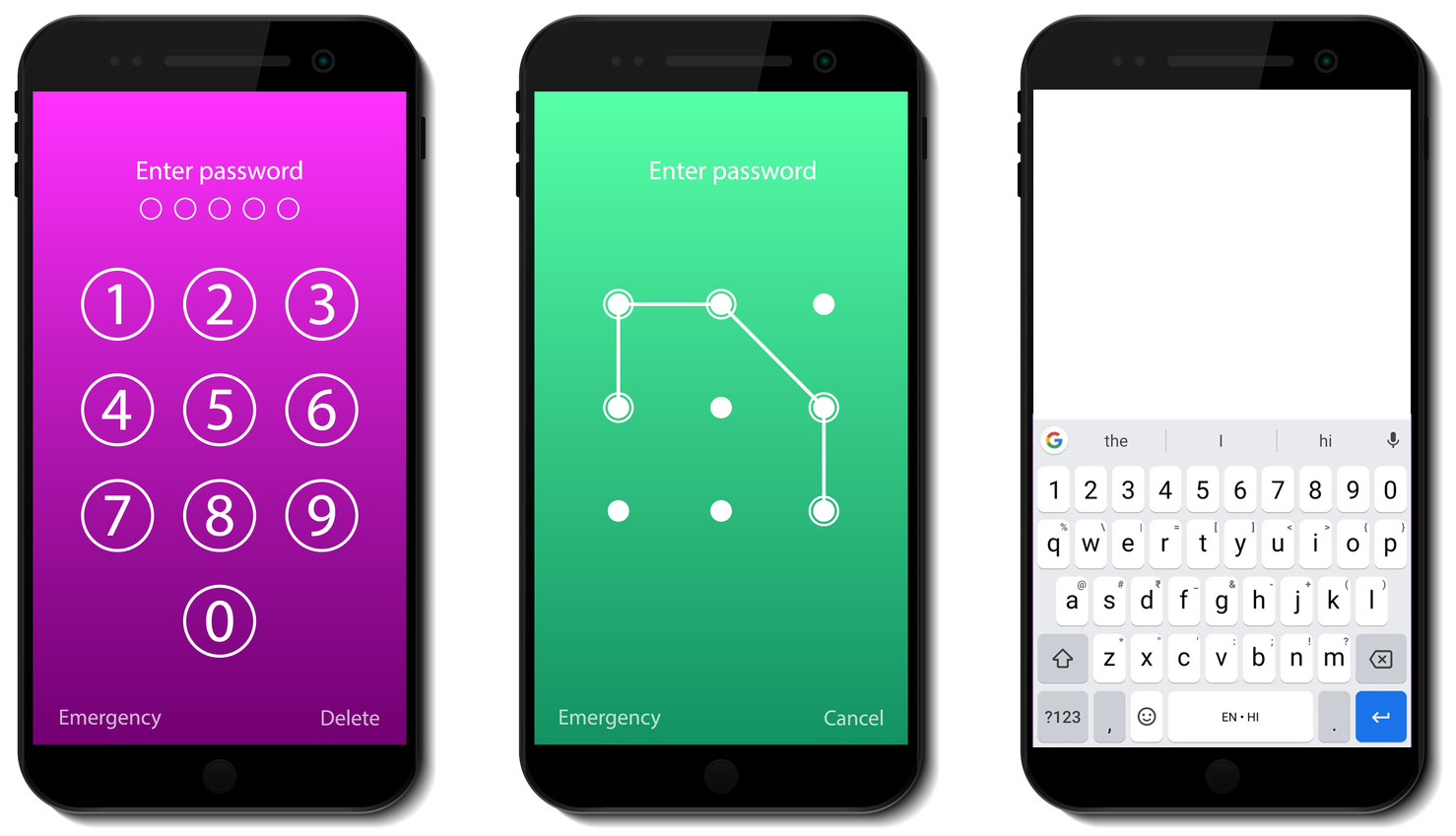
In practice, attackers can record keystroke sounds in scenarios involving close physical proximity or indirect remote access. For instance, an adversary might leave a hidden microphone near a victim's workspace or utilize remote software vulnerabilities to capture ambient sounds during VoIP calls. The emergence of powerful mobile microphones has further facilitated these remote attacks (Figure 2).
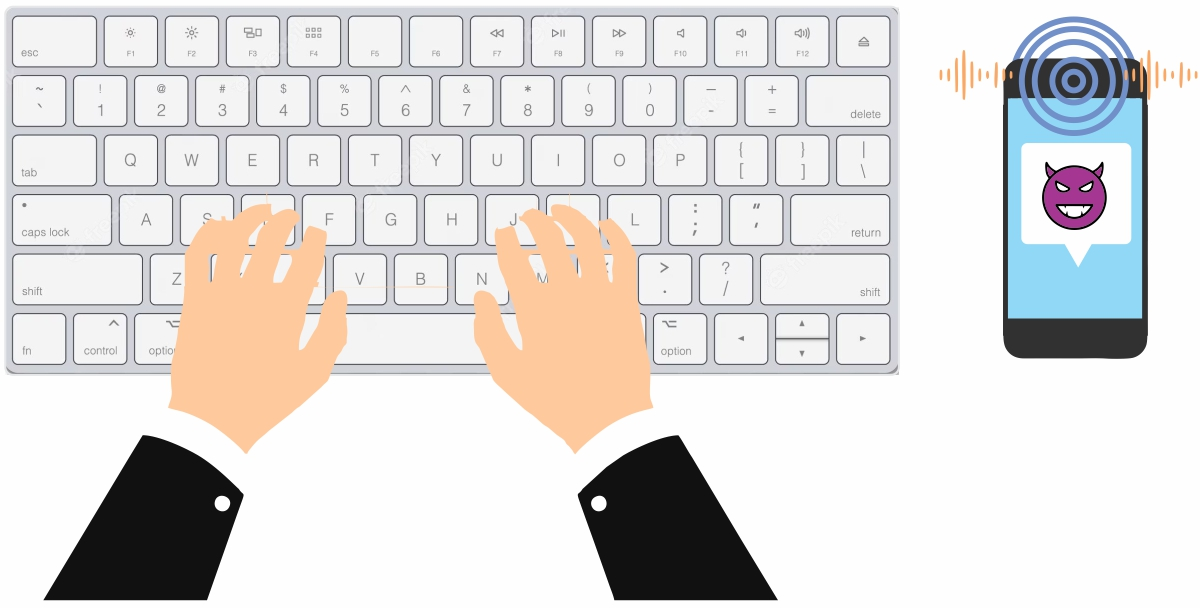


Figure 2: Examples of Remote indirect access.
Attack Surface and Methodologies
Recording Medium
The choice of recording medium greatly affects the success of acoustic side-channel attacks. Common recording devices include:
Keyboard Types
Different keyboard types exhibit varying degrees of vulnerability to acoustic side-channel attacks:
Attack Strategies
Researchers employ diverse strategies to extract data from acoustic signals, categorized broadly into timing-based, frequency-based, and geometry-based analyses.
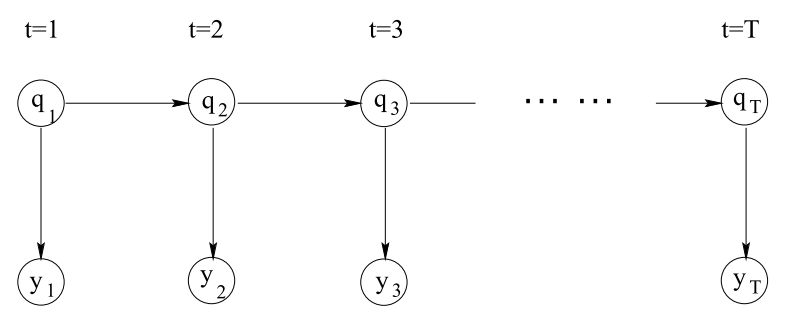
Timing-Based Analysis Utilizing Hidden Markov Models (HMMs)
Drawing on timing information between keystrokes, HMMs are often used to model typing patterns. These models help in estimating keystroke timing sequences and predicting word forms based on inter-keystroke intervals (Figure 5).
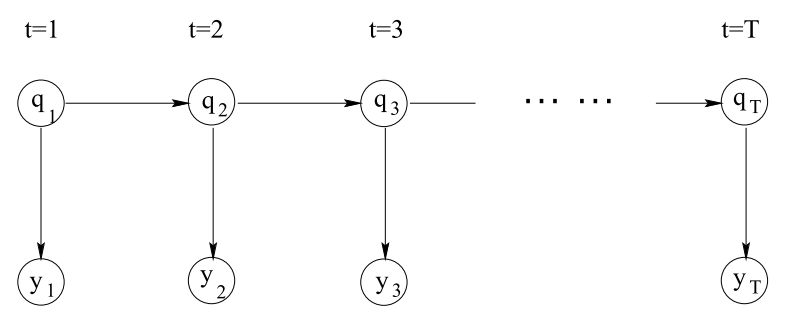
Figure 5: Illustration of a Hidden Markov Model (HMM) trace.
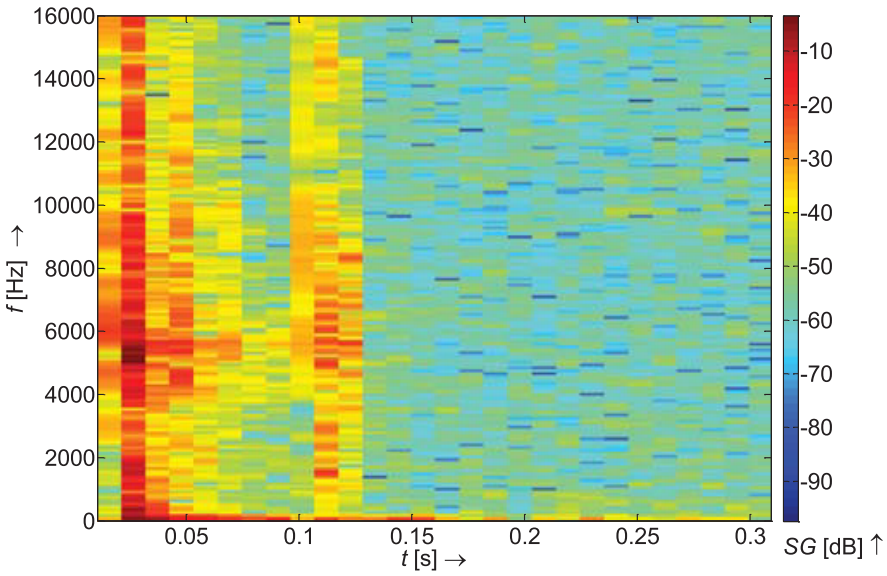
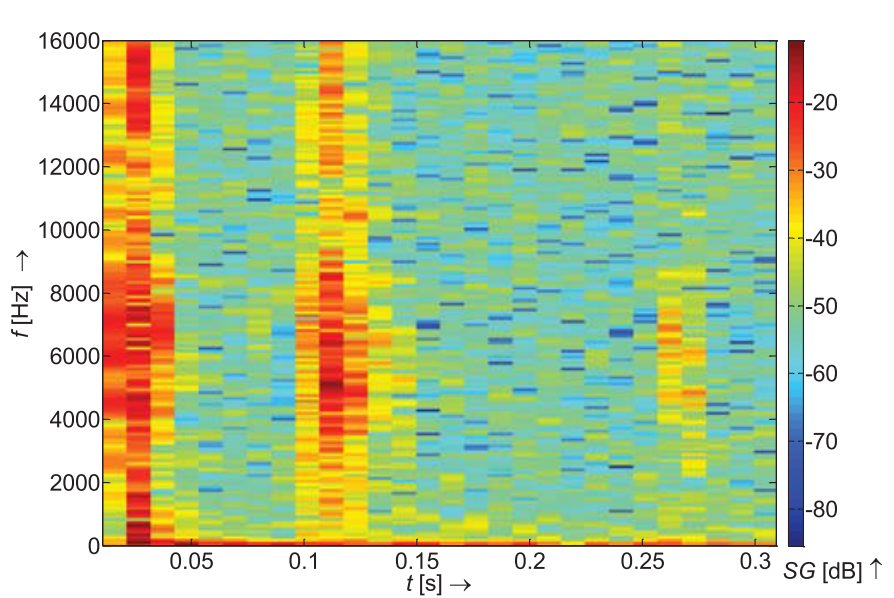
Frequency-Based Analysis Employing Signal Processing Techniques
Frequency-domain analyses typically involve transforming acoustic signals using FFT or cepstrum features, offering insights into the identification of keystroke sounds. Signal processing and machine learning techniques such as SVMs and neural networks enhance the classification accuracy of keystrokes derived from this data (Figure 6).
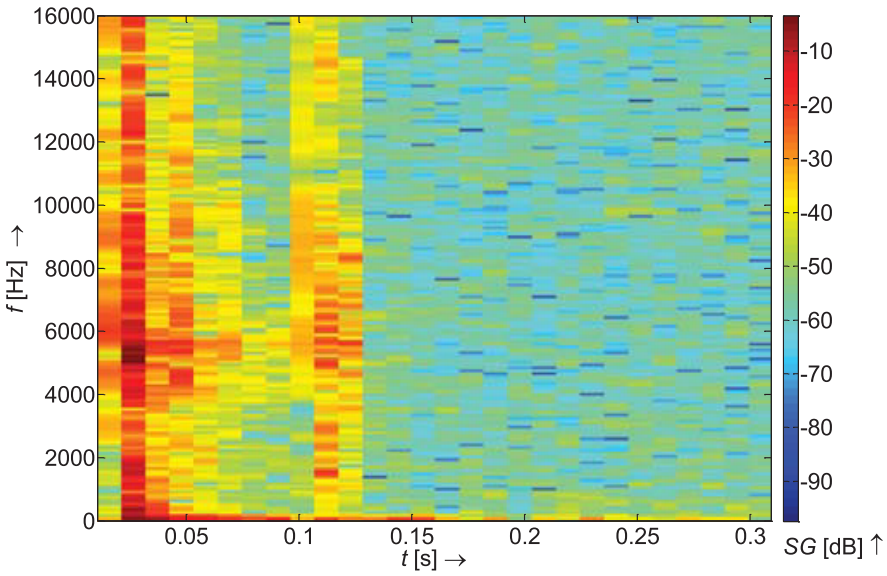
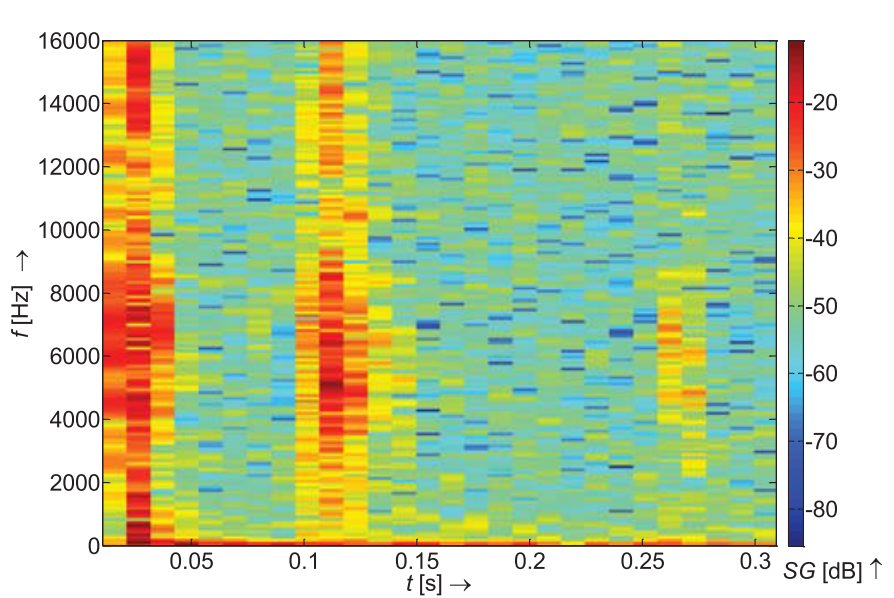
Figure 6: Spectrograms depicting two distinct keystrokes.
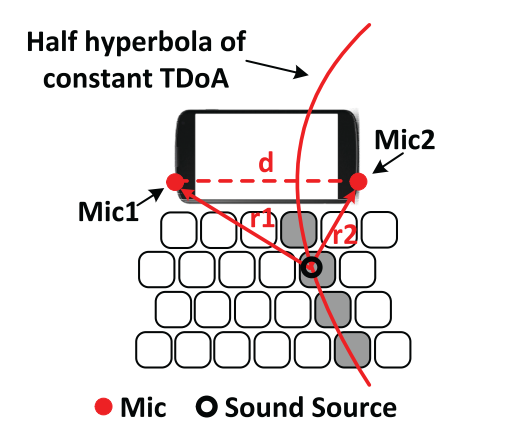
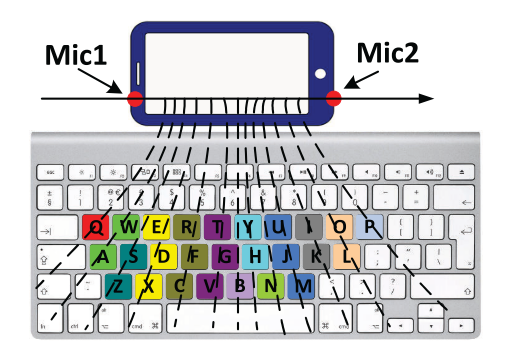
Geometry-Based Approaches Leveraging TDoA and Triangulation
The TDoA method computes arrival times across multiple microphones to estimate keystroke position (Figure 7). Triangulation, often used in conjunction with TDoA, aids in accurate sound localization for keystroke identification.
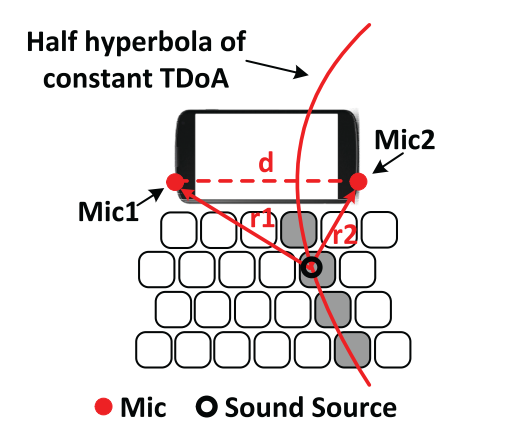
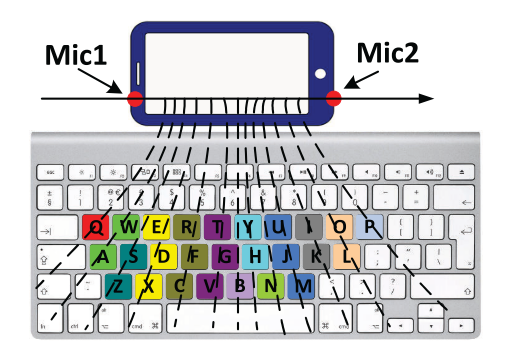
Figure 7: This is an illustration of the geometrical TDoA on a single phone and the theoretical key groups.
Post Processing Technologies
Conclusion
The survey of acoustic side-channel attacks on keyboards sheds light on significant vulnerabilities inherent in sound-based data transmission during keystrokes. The diverse attack methodologies examined herein demonstrate the pressing need for robust mitigation techniques to secure keyboard-based input systems. Through a deeper understanding of these attack vectors and their underlying principles, this research serves as a foundation for developing innovative security solutions aimed at safeguarding sensitive information against acoustic side-channel threats. Ensuring the integrity of data input mechanisms remains essential as researchers continue to explore defensive measures within this crucial domain.