Leveraging Machine Learning for Accurate IoT Device Identification in Dynamic Wireless Contexts
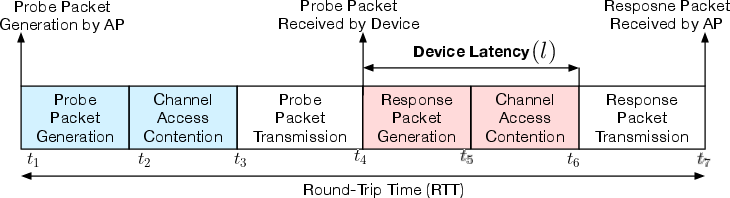
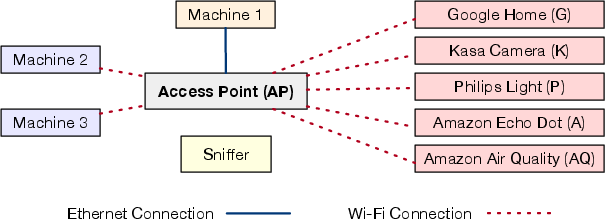
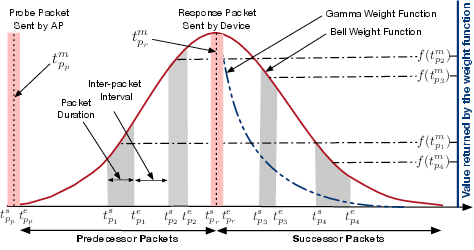
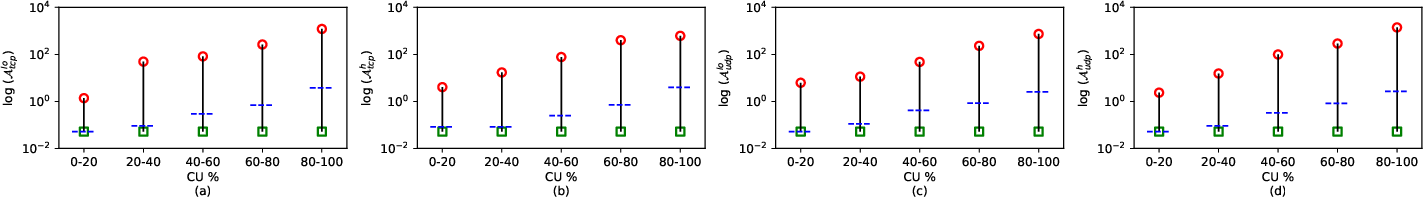
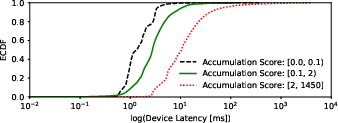
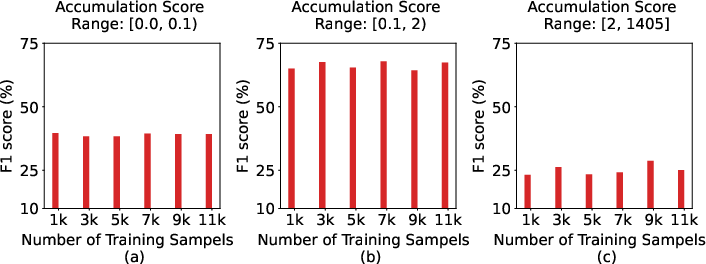
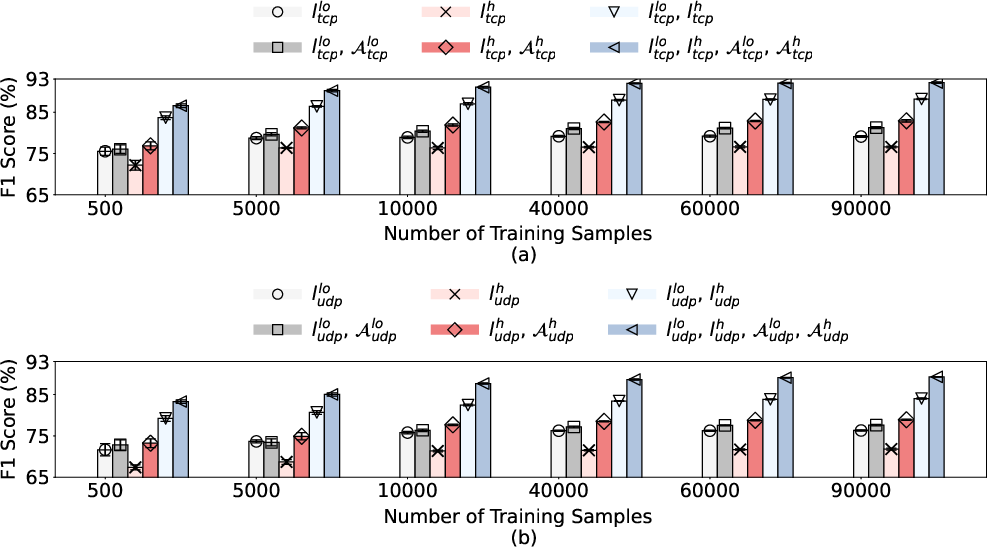
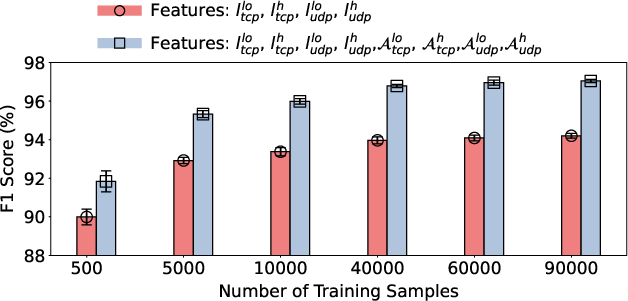
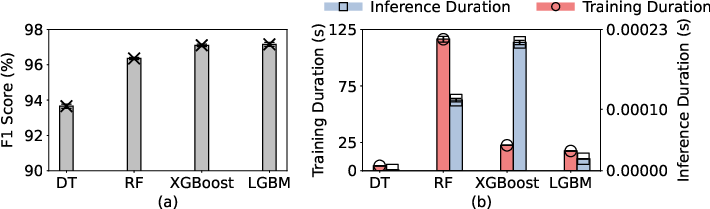
Abstract: Identifying IoT devices is crucial for network monitoring, security enforcement, and inventory tracking. However, most existing identification methods rely on deep packet inspection, which raises privacy concerns and adds computational complexity. More importantly, existing works overlook the impact of wireless channel dynamics on the accuracy of layer-2 features, thereby limiting their effectiveness in real-world scenarios. In this work, we define and use the latency of specific probe-response packet exchanges, referred to as "device latency," as the main feature for device identification. Additionally, we reveal the critical impact of wireless channel dynamics on the accuracy of device identification based on device latency. Specifically, this work introduces "accumulation score" as a novel approach to capturing fine-grained channel dynamics and their impact on device latency when training machine learning models. We implement the proposed methods and measure the accuracy and overhead of device identification in real-world scenarios. The results confirm that by incorporating the accumulation score for balanced data collection and training machine learning algorithms, we achieve an F1 score of over 97% for device identification, even amidst wireless channel dynamics, a significant improvement over the 75% F1 score achieved by disregarding the impact of channel dynamics on data collection and device latency.
- IoT Analytics. (2023) State of IoT 2023. https://iot-analytics.com/number-connected-iot-devices.
- Wi-Fi Alliance. (2023) Wi-Fi by the numbers: Technology momentum in 2023. https://www.wi-fi.org/beacon/the-beacon/wi-fi-by-the-numbers-technology-momentum-in-2023.
- M. R. Santos, R. M. Andrade, D. G. Gomes, and A. C. Callado, “An efficient approach for device identification and traffic classification in iot ecosystems,” in IEEE Symposium on Computers and Communications (ISCC). IEEE, 2018, pp. 00 304–00 309.
- B. Tushir, Y. Dalal, B. Dezfouli, and Y. Liu, “A quantitative study of ddos and e-ddos attacks on wifi smart home devices,” IEEE Internet of Things Journal, vol. 8, no. 8, pp. 6282–6292, 2020.
- A. Osman, A. Wasicek, S. Köpsell, and T. Strufe, “Transparent microsegmentation in smart home iot networks,” in 3rd USENIX Workshop on Hot Topics in Edge Computing (HotEdge), 2020.
- A. Sivanathan, H. H. Gharakheili, and V. Sivaraman, “Detecting behavioral change of iot devices using clustering-based network traffic modeling,” IEEE Internet of Things Journal, vol. 7, no. 8, pp. 7295–7309, 2020.
- S. Marchal, M. Miettinen, T. D. Nguyen, A.-R. Sadeghi, and N. Asokan, “Audi: Toward autonomous iot device-type identification using periodic communication,” IEEE Journal on Selected Areas in Communications, vol. 37, no. 6, pp. 1402–1412, 2019.
- J. Chen and B. Dezfouli, “Predictable bandwidth slicing with open vswitch,” in 2021 IEEE Global Communications Conference (GLOBECOM). IEEE, 2021, pp. 1–6.
- R. R. Chowdhury, S. Aneja, N. Aneja, and E. Abas, “Network traffic analysis based iot device identification,” in Proceedings of the 4th International Conference on Big Data and Internet of Things, pp. 79–89.
- A. Sivanathan, H. H. Gharakheili, F. Loi, A. Radford, C. Wijenayake, A. Vishwanath, and V. Sivaraman, “Classifying iot devices in smart environments using network traffic characteristics,” IEEE Transactions on Mobile Computing, vol. 18, no. 8, pp. 1745–1759, 2018.
- V. Thangavelu, D. M. Divakaran, R. Sairam, S. S. Bhunia, and M. Gurusamy, “Deft: A distributed iot fingerprinting technique,” IEEE Internet of Things Journal, vol. 6, no. 1, pp. 940–952, 2018.
- N. Ammar, L. Noirie, and S. Tixeuil, “Autonomous identification of iot device types based on a supervised classification,” in IEEE International Conference on Communications (ICC). IEEE, 2020, pp. 1–6.
- M. Miettinen, S. Marchal, I. Hafeez, N. Asokan, A.-R. Sadeghi, and S. Tarkoma, “Iot sentinel: Automated device-type identification for security enforcement in iot,” in IEEE 37th International Conference on Distributed Computing Systems (ICDCS). IEEE, 2017, pp. 2177–2184.
- A. J. Pinheiro, J. d. M. Bezerra, C. A. Burgardt, and D. R. Campelo, “Identifying iot devices and events based on packet length from encrypted traffic,” Computer Communications, vol. 144, pp. 8–17, 2019.
- H. Gordon, C. Batula, B. Tushir, B. Dezfouli, and Y. Liu, “Securing smart homes via software-defined networking and low-cost traffic classification,” in IEEE 45th Annual Computers, Software, and Applications Conference (COMPSAC). IEEE, pp. 1049–1057.
- H. Gordon, C. Park, B. Tushir, Y. Liu, and B. Dezfouli, “An efficient sdn architecture for smart home security accelerated by fpga,” in IEEE International Symposium on Local and Metropolitan Area Networks (LANMAN). IEEE, 2021, pp. 1–3.
- A. Aksoy and M. H. Gunes, “Automated iot device identification using network traffic,” in IEEE International Conference on Communications (ICC). IEEE, 2019, pp. 1–7.
- J. Sheth and B. Dezfouli, “Monfi: A tool for high-rate, efficient, and programmable monitoring of wifi devices,” in 2021 IEEE Wireless Communications and Networking Conference (WCNC). IEEE, 2021, pp. 1–7.
- J. Sheth, V. Ramanna, and B. Dezfouli, “Flip: A framework for leveraging ebpf to augment wifi access points and investigate network performance,” in Proceedings of the 19th ACM International Symposium on Mobility Management and Wireless Access (MobiWac), 2021, pp. 117–125.
- Y. Liu, J. Wang, J. Li, S. Niu, and H. Song, “Machine learning for the detection and identification of internet of things devices: A survey,” IEEE Internet of Things Journal, vol. 9, no. 1, pp. 298–320, 2022.
- R. Doshi, N. Apthorpe, and N. Feamster, “Machine learning ddos detection for consumer internet of things devices,” in IEEE Security and Privacy Workshops (SPW). IEEE, 2018, pp. 29–35.
- F. Pedregosa, G. Varoquaux, A. Gramfort, V. Michel, B. Thirion, O. Grisel, M. Blondel, P. Prettenhofer, R. Weiss, V. Dubourg et al., “Scikit-learn: Machine learning in python,” the Journal of machine Learning research, vol. 12, pp. 2825–2830, 2011.
- Qualcomm. (2020) IPQ8074: High-capacity 802.11ax SoC for Routers, Gateways and Access Points. https://www.qualcomm.com/products/internet-of-things/networking/wi-fi-networks/ipq8074.
- G. Ke, Q. Meng, T. Finley, T. Wang, W. Chen, W. Ma, Q. Ye, and T.-Y. Liu, “Lightgbm: A highly efficient gradient boosting decision tree,” Advances in neural information processing systems, vol. 30, 2017.
- E. Valdez, D. Pendarakis, and H. Jamjoom, “How to discover iot devices when network traffic is encrypted,” in IEEE International Congress on Internet of Things (ICIOT). IEEE, 2019, pp. 17–24.
- A. Aksoy and M. H. Gunes, “Automated iot device identification using network traffic,” in IEEE International Conference on Communications (ICC), 2019, pp. 1–7.
- F. Shaikh, E. Bou-Harb, J. Crichigno, and N. Ghani, “A machine learning model for classifying unsolicited iot devices by observing network telescopes,” in 14th International Wireless Communications & Mobile Computing Conference (IWCMC). IEEE, 2018, pp. 938–943.
- I. Cvitić, D. Peraković, M. Periša, and B. Gupta, “Ensemble machine learning approach for classification of iot devices in smart home,” International Journal of Machine Learning and Cybernetics, vol. 12, no. 11, pp. 3179–3202, 2021.
- O. Salman, I. H. Elhajj, A. Chehab, and A. Kayssi, “A machine learning based framework for iot device identification and abnormal traffic detection,” Transactions on Emerging Telecommunications Technologies, vol. 33, no. 3, p. e3743, 2022.
- H. F. Fakhruldeen, M. J. Saadh, S. Khan, N. A. Salim, N. Jhamat, and G. Mustafa, “Enhancing smart home device identification in wifi environments for futuristic smart networks-based iot,” International Journal of Data Science and Analytics, pp. 1–14, 2024.
- I. Ullah and Q. H. Mahmoud, “Network traffic flow based machine learning technique for iot device identification,” in IEEE International Systems Conference (SysCon). IEEE, 2021, pp. 1–8.
- S. A. Hamad, W. E. Zhang, Q. Z. Sheng, and S. Nepal, “Iot device identification via network-flow based fingerprinting and learning,” in 18th IEEE international conference on trust, security and privacy in computing and communications. IEEE, 2019, pp. 103–111.
Paper Prompts
Sign up for free to create and run prompts on this paper using GPT-5.
Top Community Prompts
Collections
Sign up for free to add this paper to one or more collections.