- The paper demonstrates that incorporating Rust into Linux kernel development significantly reduces memory safety vulnerabilities while maintaining competitive performance.
- The study employs a systematic literature review to analyze diverse integration approaches, including greenfield implementations and incremental rewrites.
- The paper identifies challenges such as increased binary sizes and interoperability issues, advocating for hybrid verification techniques and broader community consensus.
Rusty Linux: Advances in Rust for Linux Kernel Development
Introduction
The paper "Rusty Linux: Advances in Rust for Linux Kernel Development" explores the incorporation of Rust into Linux kernel development as a solution to tackle prevalent memory safety vulnerabilities associated with traditional C-based systems programming. Rust's strong memory safety guarantees, absence of a garbage collector, and performance efficiency make it a compelling candidate for kernel development. This paper presents a comprehensive literature review and provides insights into the state of Rust's integration into kernel development and its implications on system security and reliability.
Research Methodology
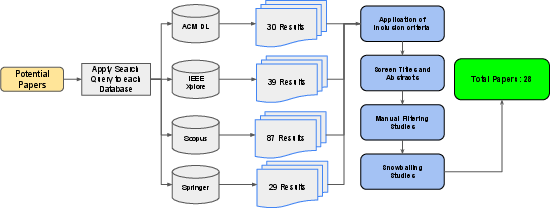
For this study, a systematic literature review (SLR) was conducted, following the Kitchenham and Charters methodology. The review involved selecting papers from ACM Digital Library, IEEE Xplore, Scopus, and Springer Link databases using keyword-based queries. The research questions focused on examining existing approaches for implementing operating system kernels in Rust, analyzing performance implications, identifying challenges and limitations, and synthesizing lessons learned.
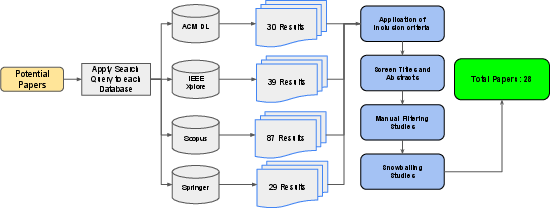
Figure 1: Process Diagram for Paper selection
Existing Approaches
The paper identifies various approaches to integrate Rust into kernel development, including greenfield implementations, incremental integration into existing kernels like Linux, and porting existing C-based kernels to Rust. Greenfield projects like Theseus OS utilize Rust's properties to enforce isolation, minimizing runtime checks. Incremental integration involves gradually rewriting existing C components in Rust for improved safety without drastically altering the system architecture. Finally, initiatives like rewriting HermitCore into RustyHermit as a unikernel demonstrate Rust's applicability in specialized kernel environments.
Highlighting performance assessments, early results show that Rust can achieve comparable performance to C in certain driver implementations, albeit with some overheads due to factors like increased binary sizes and unique Rust features. The paper discusses implications on throughput and latency, noting potential optimizations and real-time improvements enabled by Rust despite its relatively recent adoption in kernel space.
Challenges and Limitations
The integration of Rust faces several challenges, notably binary size expansion due to monomorphization, missing language features, and interoperability issues with existing C components. Rust's unique type system can introduce limitations in kernel space, necessitating unsafe code for hardware interactions and emphasizing the need for new verification techniques. Additional complexity arises from ensuring type safety and maintaining the hybrid code flow of modules written in both C and Rust.
Lessons Learned
Rust’s influence in kernel development emphasizes leveraging its type system for increase code safety and avoiding pitfalls like unsynchronized global states and undefined behavior due to exhaustive unsafe code regions. Lessons learned from implementations like Theseus highlight the benefits and limitations of Rust’s intralingual design and advocate for hybrid verification approaches using SMT solvers alongside Rust’s type system.
Conclusion
The paper underscores Rust's potential to enhance system reliability by addressing memory vulnerabilities endemic to C-based kernels. While Rust's full-scale adoption in the kernel environment remains challenging, its capacity to reduce security risks presents significant benefits. Ongoing research and practical efforts are crucial in overcoming the integration challenges, refining interoperability, and supporting the development community to harness Rust's advantages in system programming. Future work should concentrate on expanding empirical evidence supporting Rust's impact in kernel spaces and stimulate community consensus on its implementation strategies.
Overall, Rust’s incorporation into kernel development is a promising shift toward more reliable and secure operating systems, marking a notable advancement in kernel programming practices.