ECDSA Cracking Methods
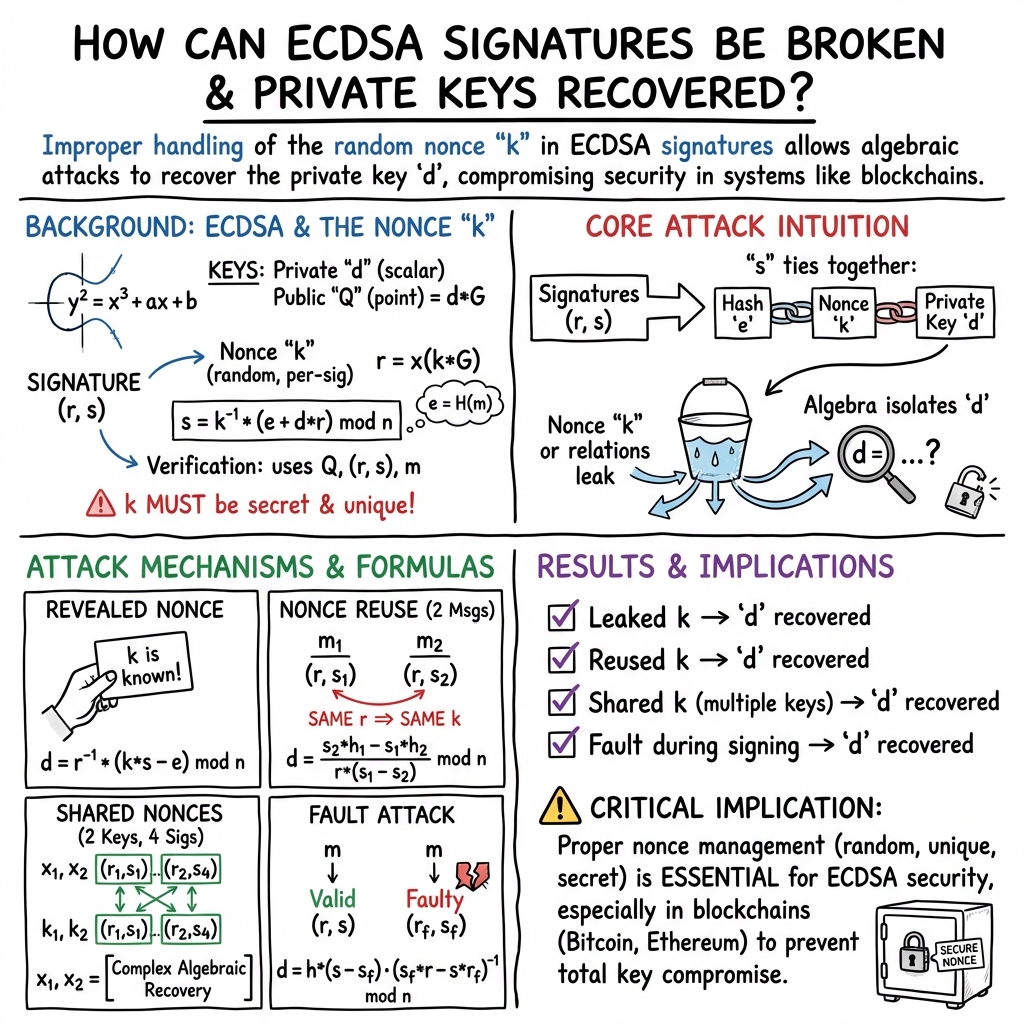
Abstract: The ECDSA (Elliptic Curve Digital Signature Algorithm) is used in many blockchain networks for digital signatures. This includes the Bitcoin and the Ethereum blockchains. While it has good performance levels and as strong current security, it should be handled with care. This care typically relates to the usage of the nonce value which is used to create the signature. This paper outlines the methods that can be used to break ECDSA signatures, including revealed nonces, weak nonce choice, nonce reuse, two keys and shared nonces, and fault attack.
Paper Prompts
Sign up for free to create and run prompts on this paper using GPT-5.
Top Community Prompts
Practical Applications
Immediate Applications
The following applications can be deployed now based on the paper’s methods for breaking ECDSA (revealed nonces, weak nonces via LLL, nonce reuse, shared nonces across keys, and fault attacks), and standard best practices for signature hygiene.
- Blockchain signature auditing and alerting
- Sector: finance, software, blockchain analytics
- Use case: Scan Bitcoin/Ethereum transactions to detect repeated r-values and nonce patterns indicative of reuse or shared nonces; flag high-risk addresses and transactions.
- Potential tools/products/workflows: On-chain analytics modules, node plugins, SIEM integrations that ingest chain data and raise alerts when r repeats; dashboards for exchange risk teams.
- Assumptions/dependencies: Access to full chain data and ECDSA signature components; reliable r extraction; addresses using ECDSA (e.g., secp256k1).
- CI/CD cryptography linting and secure coding enforcement
- Sector: software engineering, DevSecOps
- Use case: Static analysis rules and build-time checks that prevent insecure RNG for ECDSA nonces and enforce deterministic nonce generation (RFC 6979) where appropriate.
- Potential tools/products/workflows: Language-specific linters, secure coding pipelines, pre-commit hooks; policy templates mandating RFC 6979 or FIPS-validated DRBG.
- Assumptions/dependencies: ECDSA libraries support RFC 6979 or strong DRBG; developer buy-in; integration into build pipelines.
- Wallet and HSM hardening for nonce hygiene
- Sector: finance, hardware security, custody
- Use case: Configure wallets/HSMs to use deterministic nonces, enforce nonce uniqueness checks prior to signing, record nonce-health telemetry, and implement anti-fault protections (e.g., glitch detection, redundancy).
- Potential tools/products/workflows: Firmware updates, HSM signing policies, signing-service gateways that intercept and validate nonce behavior.
- Assumptions/dependencies: Vendor support for deterministic k and fault countermeasures; ability to patch or configure devices.
- Penetration testing and red-team playbooks targeting ECDSA misuse
- Sector: cybersecurity services
- Use case: Assess signing systems for nonce leakage, reuse, weak RNG, and susceptibility to fault attacks; demonstrate private key recovery using the equations provided.
- Potential tools/products/workflows: Red-team toolkits to detect repeated r values, lattice-based scripts (LLL) to exploit weak nonces, controlled fault-injection tests on testbeds.
- Assumptions/dependencies: Legal authorization; presence of misconfigurations; safe fault-injection environment.
- Incident response and digital forensics for compromised signing
- Sector: cybersecurity, law enforcement, blockchain forensics
- Use case: Rapid analysis of signatures to determine if nonces were reused or leaked; recover private keys where lawful and feasible to preempt theft or recover assets.
- Potential tools/products/workflows: Forensic scripts applying the paper’s recovery formulas; triage playbooks; chain-of-custody procedures for signature artifacts.
- Assumptions/dependencies: Availability of signature data and evidence of nonce leakage; legal authority; ethical constraints.
- Exchange and custodian risk scoring for ECDSA health
- Sector: finance, compliance
- Use case: Integrate nonce hygiene signals (r collisions, suspected k weaknesses) into AML/fraud risk scoring of addresses and customers.
- Potential tools/products/workflows: Risk models, compliance dashboards; alerts for internal controls and customer outreach.
- Assumptions/dependencies: Access to analytics; mapping of signals to risk; policy frameworks to act on alerts.
- IoT/firmware signing health checks
- Sector: IoT, robotics, automotive, energy
- Use case: Run self-tests for RNG health; detect repeated r and ensure deterministic/strong nonce generation in device firmware signing workflows.
- Potential tools/products/workflows: Build-time test suites; device telemetry on signature parameters; secure boot validation augmented with nonce-health metrics.
- Assumptions/dependencies: ECDSA used for firmware signing; ability to update tooling; telemetry channels.
- TLS operational hygiene and transient-error monitoring
- Sector: enterprise IT, web security
- Use case: Leverage insights from fault attacks to monitor hardware-induced transient errors that could compromise ECDSA/TLS keys; implement redundancy and error detection.
- Potential tools/products/workflows: Hardware health monitors, signing retries with consistency checks, anomaly detection for signature parameters.
- Assumptions/dependencies: Instrumentation available; TLS stacks exposing necessary data; transient faults present in specific environments.
- Academic teaching labs and reproducible exercises
- Sector: academia, education
- Use case: Course modules demonstrating nonce-reuse key recovery, LLL attacks on weak nonces, and shared-nonce multi-key cracks, using provided equations.
- Potential tools/products/workflows: Jupyter notebooks, classroom datasets, open-source scripts.
- Assumptions/dependencies: Controlled environment; synthetic or safe data; adherence to ethics.
- Internal policy updates for cryptographic governance
- Sector: policy/compliance
- Use case: Mandate deterministic nonces or FIPS-standard DRBG, periodic RNG audits, and fault-resilience checks in signing infrastructure.
- Potential tools/products/workflows: Corporate cryptography standards, audit checklists, vendor qualification criteria.
- Assumptions/dependencies: Executive sponsorship; audit capability; library/vendor support.
- Node and RPC middleware checks for suspicious signatures
- Sector: blockchain infrastructure
- Use case: Enhance nodes or RPC gateways to detect duplicate r within observed mempool/chain traffic and notify operators.
- Potential tools/products/workflows: Middleware that parses signatures, caches r values, and emits alerts.
- Assumptions/dependencies: Performance overhead acceptable; accurate parsing of signature components.
Long-Term Applications
The following applications require further research, development, scaling, or ecosystem agreement to be practical.
- Protocol migration to signature schemes with stronger nonce robustness
- Sector: blockchain, software security
- Use case: Transition from ECDSA to schemes like Schnorr (already present in some Bitcoin updates) or Ed25519 where deterministic nonce handling and aggregated signatures reduce nonce-related risk.
- Potential tools/products/workflows: Consensus changes, wallet upgrades, library migrations, cross-chain compatibility tooling.
- Assumptions/dependencies: Community consensus, backward compatibility strategies, wide library support.
- On-chain nonce-reuse detectors and economic penalties
- Sector: blockchain governance
- Use case: Native chain modules that detect nonce reuse and apply automatic alerts or penalties (e.g., slashing for validators, quarantine lists for addresses).
- Potential tools/products/workflows: Protocol extensions, smart-contract-based monitors, governance policies.
- Assumptions/dependencies: Chain support for signature inspection; agreement on policy enforcement; avoiding false positives.
- Fault-resistant cryptographic hardware architectures
- Sector: semiconductors, HSM vendors
- Use case: Design co-processors with built-in glitch detection, redundant computation, and signature consistency checks to mitigate transient errors leading to key compromise.
- Potential tools/products/workflows: New silicon designs, certification processes (Common Criteria, FIPS), firmware update channels.
- Assumptions/dependencies: R&D investment; performance and cost trade-offs; certification timelines.
- Formal verification of nonce generation and signing paths
- Sector: formal methods, software assurance
- Use case: Prove properties like uniqueness and unpredictability of k, resistance to shared-nonce across keys, and fault-handling correctness.
- Potential tools/products/workflows: Verified libraries, model checking, proofs integrated into build pipelines.
- Assumptions/dependencies: Availability of formal specs; team expertise; time to integrate proofs.
- Machine-learning assisted detection of weak nonces and lattice-attack candidates
- Sector: research, blockchain analytics
- Use case: Train models on signature metadata to identify patterns consistent with weak RNG and prioritize LLL attack attempts.
- Potential tools/products/workflows: Feature engineering from signature streams; hybrid cryptanalytic pipelines combining ML triage with lattice solvers.
- Assumptions/dependencies: High-quality labeled datasets; explainability; avoidance of bias.
- Standardized regulatory frameworks for nonce and RNG health
- Sector: policy/regulation
- Use case: Codify requirements for deterministic nonce usage or validated DRBG, periodic RNG health checks, and fault-resilience for custody and critical infrastructure providers.
- Potential tools/products/workflows: Sector guidelines, audit programs, certification schemes.
- Assumptions/dependencies: Regulatory adoption; harmonization across jurisdictions; industry compliance capacity.
- Managed signing services offering “nonce hygiene SLAs”
- Sector: SaaS/security services
- Use case: Provide signing-as-a-service with contractually guaranteed nonce uniqueness, deterministic generation, and fault protections, plus attestation APIs.
- Potential tools/products/workflows: Cloud HSMs, attestation endpoints, compliance reporting.
- Assumptions/dependencies: Market demand; robust multi-tenant isolation; third-party audits.
- Forensic automation for lawful key recovery
- Sector: law enforcement, cyber incident response
- Use case: Systems that automatically detect nonce-related vulnerabilities and apply the paper’s recovery formulas to assist investigations where permitted.
- Potential tools/products/workflows: Case management integrations, automated derivation pipelines, evidence preservation tooling.
- Assumptions/dependencies: Legal frameworks; strict access controls; ethics and oversight.
- IoT supply-chain attestation with signature health telemetry
- Sector: IoT, manufacturing
- Use case: Embed signature-health signals (e.g., r-reuse rates, RNG tests) into device attestation and lifecycle audits to detect compromised factories or tooling.
- Potential tools/products/workflows: Attestation protocols, telemetry collection, analytics dashboards for OEMs.
- Assumptions/dependencies: Standards for telemetry; secure channels; vendor cooperation.
Collections
Sign up for free to add this paper to one or more collections.