- The paper introduces a framework that analyzes obfuscated fund transfer operations in Ethereum smart contracts using bytecode-level analysis and a Z-score ranking system.
- It identifies seven obfuscation techniques that complicate detection and reveals that obfuscated contracts can double inbound funds compared to non-obfuscated ones.
- The study underscores the urgent need for improved detection methods and regulatory measures to combat financial exploitation in the blockchain ecosystem.
Understanding and Characterizing Obfuscated Funds Transfers in Ethereum Smart Contracts
This paper presents an in-depth analysis and characterization of obfuscated fund transfer operations in Ethereum smart contracts, particularly focusing on their impact and prevalence within the blockchain ecosystem. The study systematically uncovers the techniques used for obfuscating transaction logic in smart contracts, thereby aiding malicious activities like scams and MEV bot operations. The authors propose a comprehensive framework to analyze bytecode-level obfuscation mechanisms and utilize a Z-score ranking system to quantify the level of obfuscation complexity.
Obfuscation Techniques
Obfuscation Taxonomy
The taxonomy developed in this paper distinguishes seven strategies for obfuscating fund transfer operations. These include multi-step address generation, complex string operations, external contract calls, and control-flow complexity, among others. By obfuscating critical elements such as recipient addresses, transaction values, and execution contexts, these techniques significantly hinder conventional detection algorithms.
Detailed Analysis and Implementation
The analysis tool, , converts smart contract bytecode into static single-assignment (SSA) intermediate representation (IR) via Rattle, detecting fund transfer operations and extracting features for obfuscation. The Z-score representation model then quantifies the obfuscation degree to pinpoint contracts employing extensive concealment tactics.
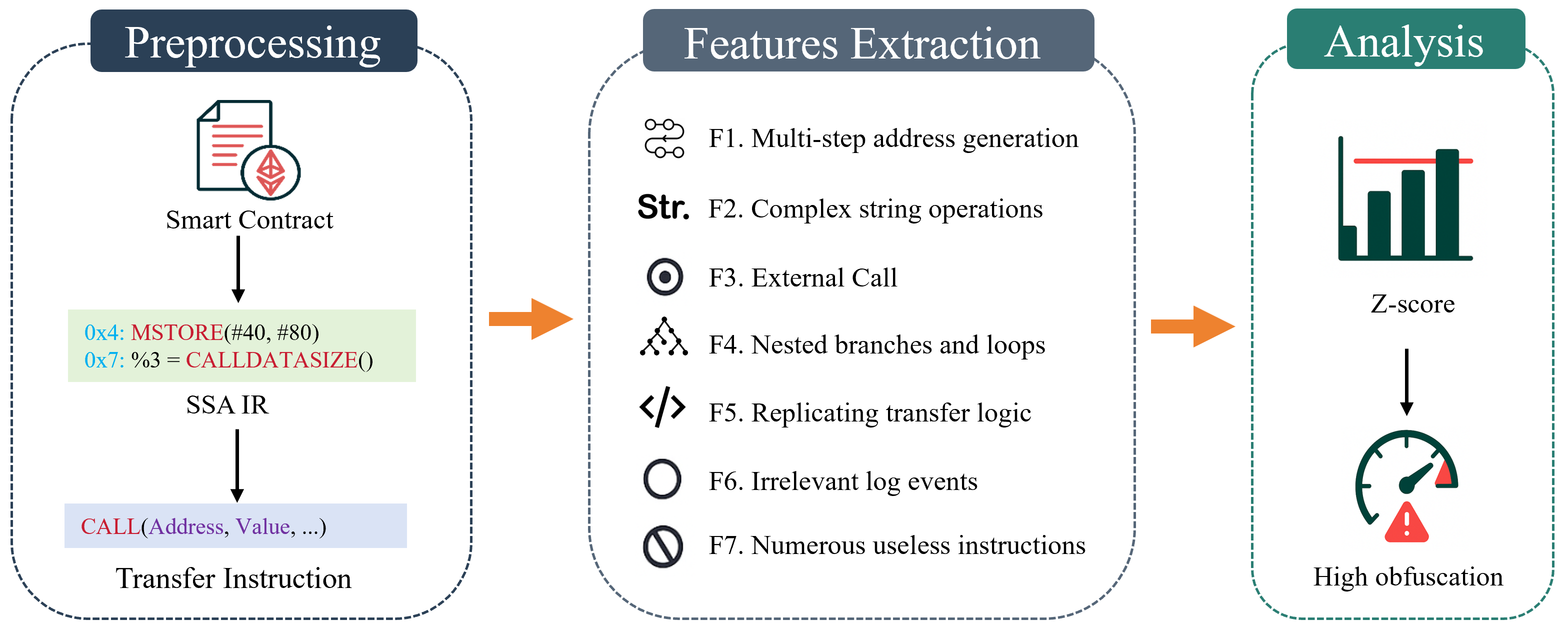
Figure 1: Overview of .
Prevalence and Financial Impact
Prevalence Study
In a comprehensive examination of over one million smart contracts, the study identifies a substantial fraction (approximately 0.3%) exhibiting significant obfuscation. This underscores the widespread adoption of obfuscation in smart contract practices, necessitating advanced detection strategies.
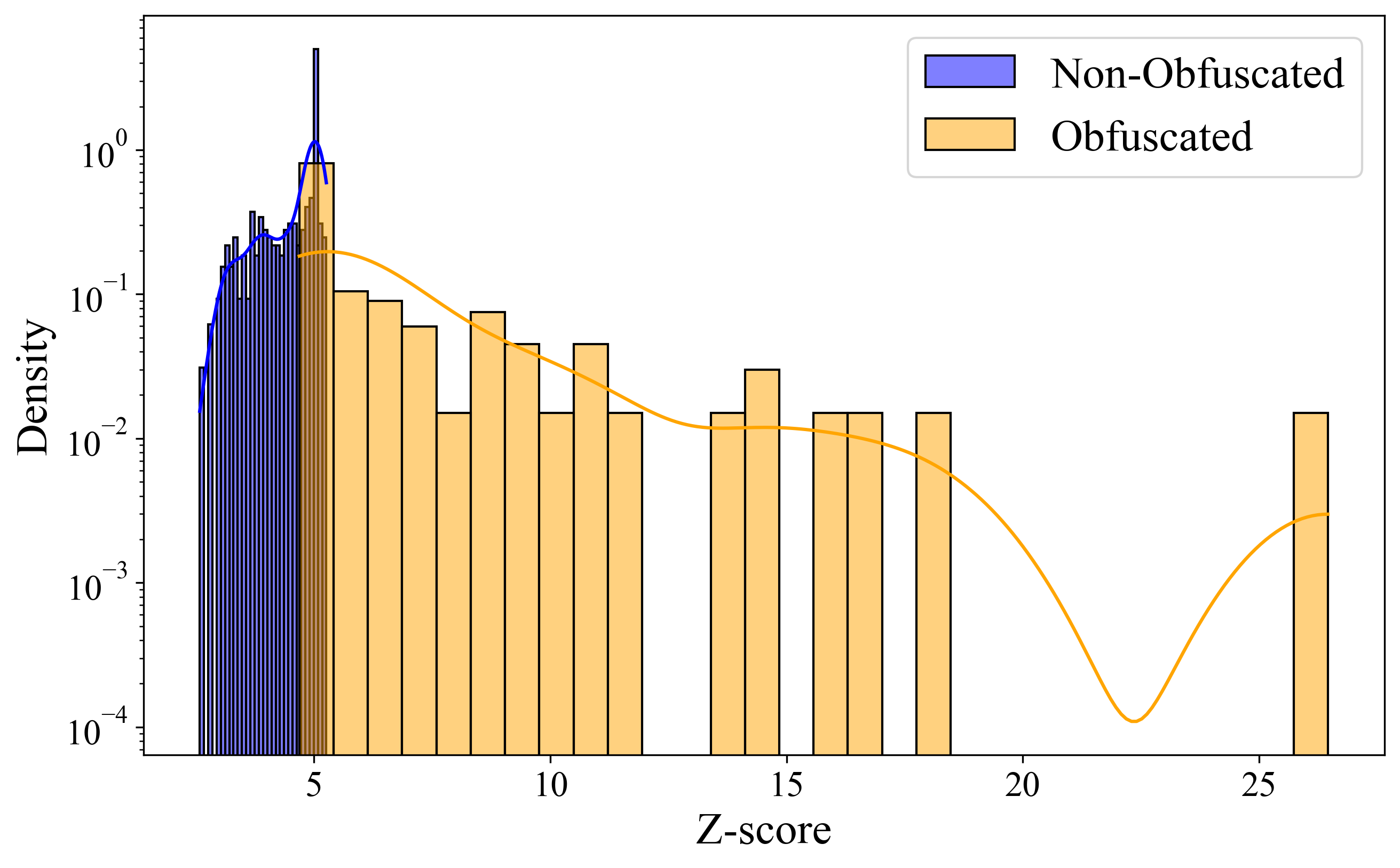
Figure 2: Z-score Distribution.
Financial Impact Analysis
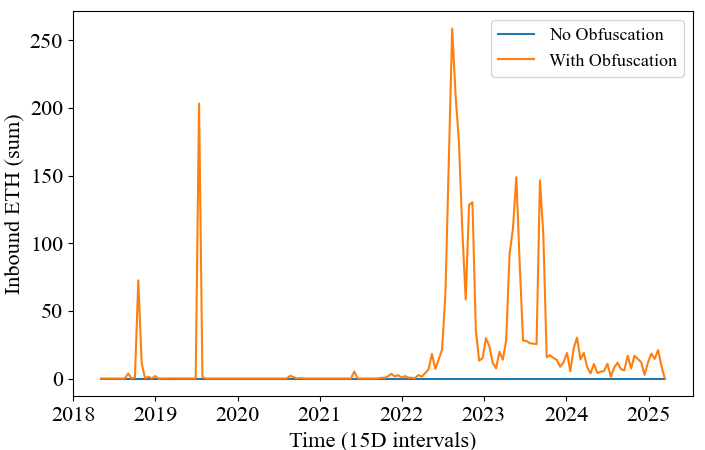
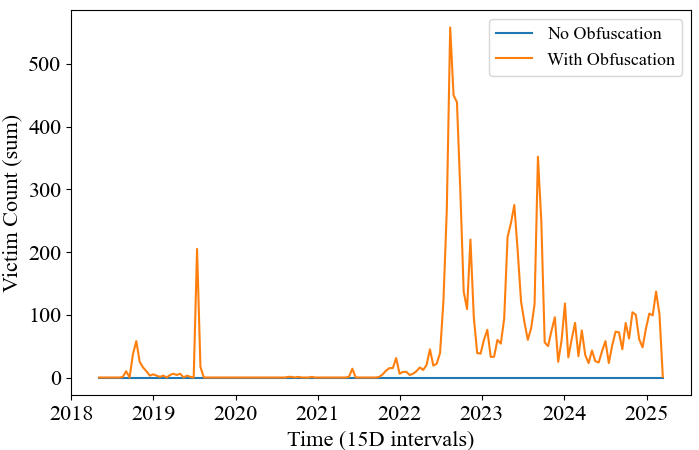
The study highlights the stark contrast between obfuscated and non-obfuscated contracts. Obfuscated contracts show a much higher capacity for financial extraction, with maximum inbound funds nearly doubling those of non-obfuscated counterparts. Temporal analysis further reveals recurrent victimization patterns associated with obfuscated contracts.
Figure 3: The Z-score Distribution on the Ethereum Mainnet. The dashed red line marks the top 0.3\% cutoff.
Figure 4: Time Series Analysis of transaction Volumes.
Figure 5: Aggregated Inbound Ether Analysis.
The obfuscation techniques identified significantly degrade the effectiveness of existing smart contract analysis tools. The accuracy of SourceP, a prominent Ponzi scheme detection tool, falls drastically in scenarios involving heavily obfuscated contracts. This highlights an urgent need for research focused on enhancing detection methodologies for obfuscated smart contracts.
Discussion
The prevalent use of obfuscation in smart contracts poses challenges for auditing and regulatory practices. The findings call for concerted efforts in developing robust analysis frameworks that can accommodate the sophistications introduced by obfuscation practices. Additionally, the insights gained could guide legislative measures to mitigate potential vulnerabilities in DeFi ecosystems.
Conclusion
The study provides a robust framework for understanding and detecting obfuscation in Ethereum smart contracts, facilitating improved transparency and security evaluations within the blockchain domain. By elucidating obfuscation's role in exacerbating financial disputes, the findings emphasize the need for innovation in analytical tools to keep pace with evolving obfuscation practices.
Figure 6: Temporal Analysis of Victim Counts.
The insights from this paper not only emphasize the pervasiveness of obfuscation in smart contracts but also stress its implications for security and regulatory frameworks. Enhancing detection and analysis capabilities remains imperative for safeguarding blockchain ecosystems against financial exploitation.