- The paper presents MoveScanner, a static analysis tool that achieves an 88.2% detection accuracy in uncovering vulnerabilities in Move smart contracts.
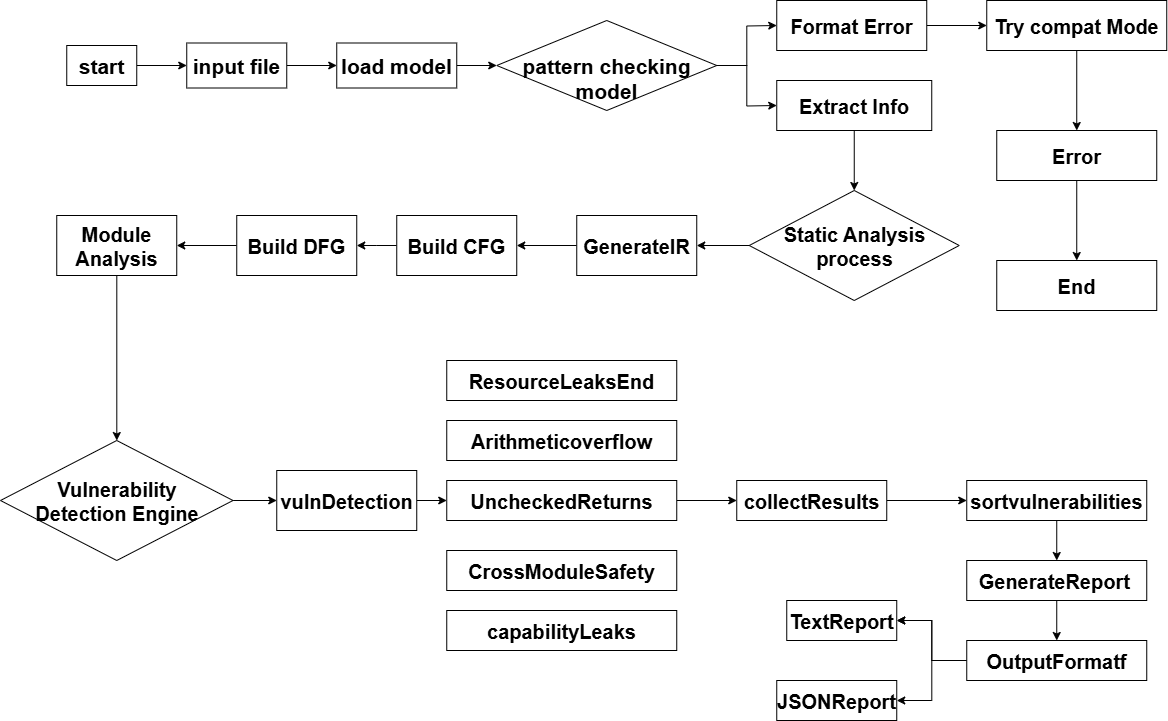
- It employs control flow, data flow, and cross-module analysis techniques to pinpoint issues from resource leaks to arithmetic overflows.
- The research highlights the need to integrate formal verification with dynamic analysis to enhance security in modular blockchain systems.
MoveScanner: Analysis of Security Risks of Move Smart Contracts
The paper "MoveScanner: Analysis of Security Risks of Move Smart Contracts" offers a comprehensive exploration of the security vulnerabilities inherent in smart contracts written in the Move language. This language, while designed with security as a foundational principle, still faces challenges stemming from programming errors and complex interactions across modules. The study introduces MoveScanner, a static analysis tool aimed at identifying and addressing these vulnerabilities, leveraging novel techniques to enhance accuracy and efficacy.
Move Language and Security Challenges
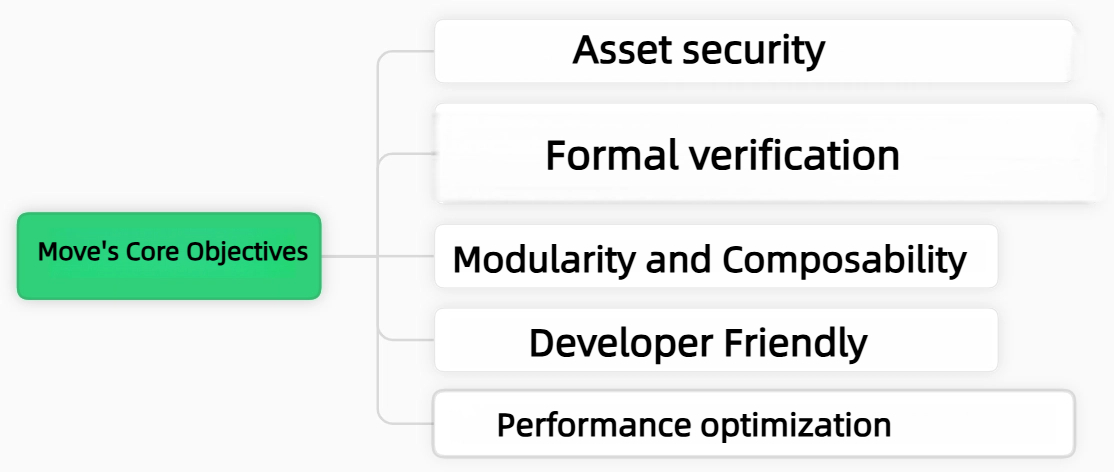
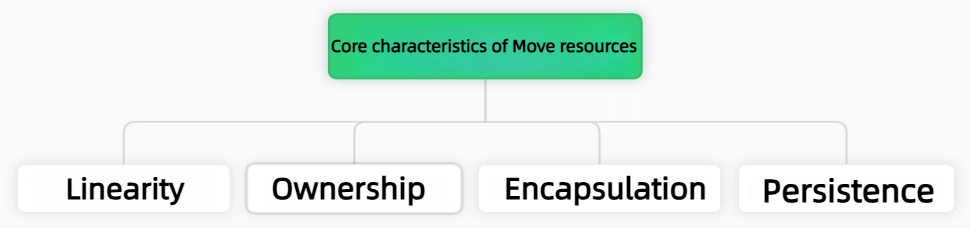
Move is a smart contract language built with a focus on secure digital asset management. Its core innovations include a unique resource model and a linear type system that prevent common security issues such as double-spending and resource leakage at the language level. Despite these advantages, Move smart contracts are susceptible to vulnerabilities due to developer errors and complex logic. The paper emphasizes the importance of addressing new security threats that arise from the modular architecture and cross-module interactions endemic to Move.
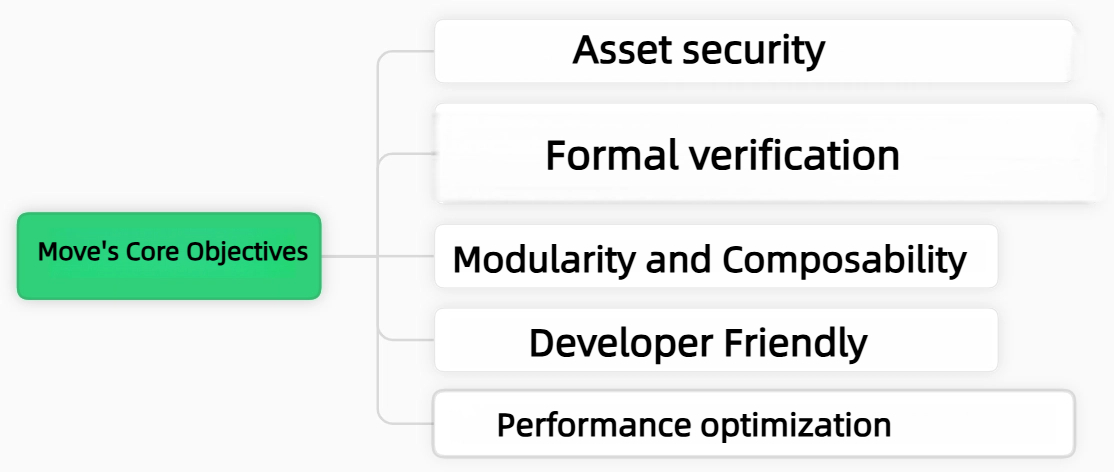
Figure 1: Move's Core Objectives
The paper highlights the comparisons between Move and Solidity, underscoring how Move's treatment of digital assets as first-class citizens using resource types intrinsically prevents asset duplication and loss. This structural difference grants Move a significant advantage in security but also presents developmental challenges due to its less mature ecosystem compared to Solidity.
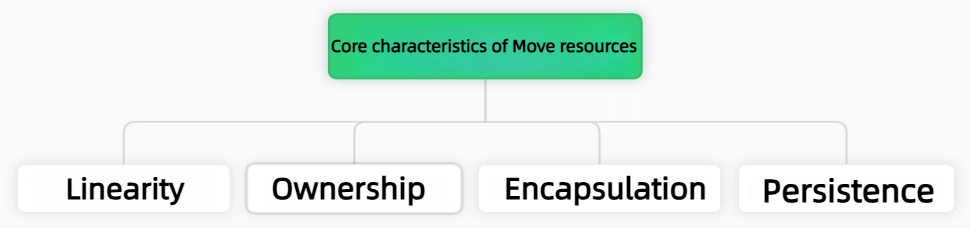
Figure 2: Move Resource Core Features
Move Smart Contract Execution Environment
The paper describes the execution environment of Move, particularly MoveVM's role in handling bytecode. The execution strategy focuses on pre-deployment static analysis to ensure compliance with security requirements. Different implementations, such as those for Diem, Sui, and Aptos, illustrate the diversification in execution models, each optimizing resource management and transaction processing uniquely.
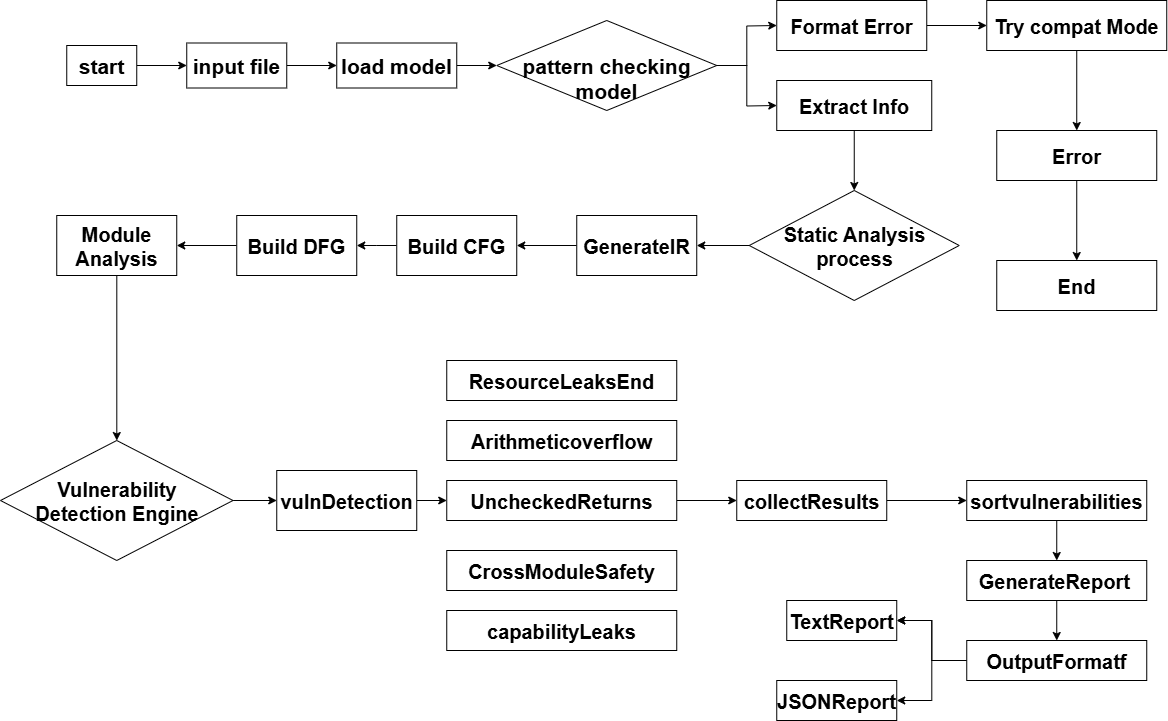
Figure 3: Movescanner Overall Design
Core Analysis Technology
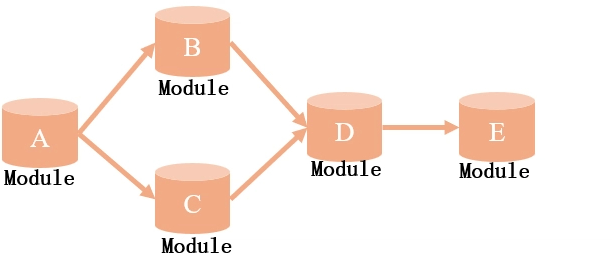
MoveScanner employs control flow analysis, data flow analysis, and cross-module analysis to detect vulnerabilities. The analysis approaches include reaching definitions and live variable analysis to ensure resource security. The cross-module analysis, utilizing a call graph, aids in identifying permission leaks and unauthorized access, providing a global perspective on resource management.
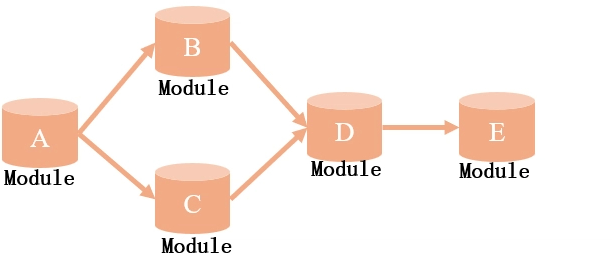
Figure 4: Cross-module analysis
The core analysis techniques are grounded in mathematical formulations for reaching definitions and live variable systems, ensuring rigorous tracking of potential vulnerabilities.
Implementation and Optimization
The tool’s architecture is modular, supporting bytecode-level analysis and multi-chain adaptation. MoveScanner is optimized for performance with a CLI interface that provides flexibility in vulnerability detection configuration. Through dynamic loading and version-compatible deserialization, the tool ensures compatibility across different blockchain environment variations.
Evaluation
Experimental results demonstrate MoveScanner's efficiency and accuracy, achieving an 88.2% detection accuracy rate against benchmark datasets. The tool excels in identifying resource leaks and arithmetic overflow vulnerabilities while reducing false positives significantly. The analysis extends to open-source projects and production datasets, revealing patterns of vulnerabilities prevalent in the Move contracts used on platforms like Aptos.
The paper concludes with insights into improving smart contract security mechanisms, advocating for the integration of formal verification and dynamic analysis to enhance vulnerability detection and safeguard contract integrity across lifecycle phases.
Conclusion
The MoveScanner tool represents a significant advancement in identifying and mitigating security risks in Move smart contracts. By fostering more reliable resource management and addressing interactions at modular and cross-module levels, this research provides essential contributions to the ongoing development of secure blockchain ecosystems. Future research should aim to integrate these methods with broader security frameworks and scalable detection systems to enhance robustness and reliability in blockchain applications.