- The paper introduces an AI-driven framework for adaptive post-quantum cryptography in V2X systems, ensuring quantum-resilient and low-latency communications.
- It rigorously analyzes TCPS vulnerabilities and benchmarks lattice-, code-, and hash-based schemes against sub-100 ms latency targets in resource-constrained environments.
- The study demonstrates that AI enables real-time threat prediction and resource optimization, reducing energy consumption by up to 30% in vehicular networks.
AI-Driven Post-Quantum Cryptography for Cyber-Resilient V2X Communication in Transportation Cyber-Physical Systems
Introduction
This paper presents a comprehensive analysis of the integration of post-quantum cryptography (PQC) and AI to secure Vehicle-to-Everything (V2X) communications within Transportation Cyber-Physical Systems (TCPS). The authors systematically dissect the architecture of TCPS, enumerate the vulnerabilities inherent in current communication protocols, and critically evaluate the limitations of classical cryptographic primitives in the face of quantum adversaries. The work then advances the discussion by detailing the landscape of PQC algorithms, their trade-offs, and the unique challenges of deploying them in latency- and resource-constrained vehicular environments. The central thesis is that AI-driven orchestration of PQC can enable context-aware, adaptive, and cyber-resilient security for TCPS, addressing both current and emergent threats.
TCPS Architecture and Communication Vulnerabilities
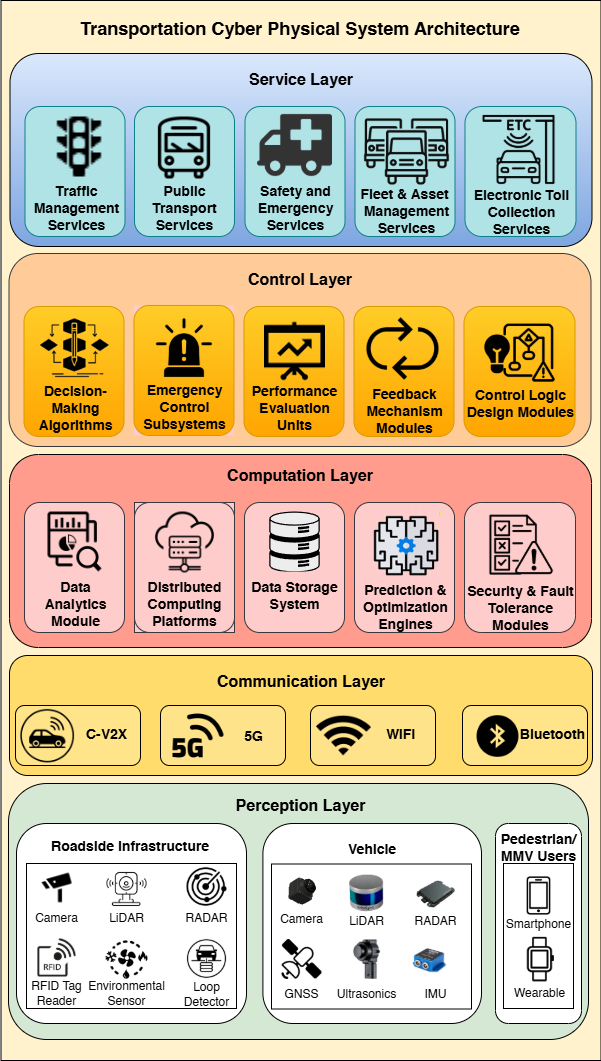
TCPS are characterized by a multilayered architecture integrating perception, communication, computation, control, and service layers. The communication backbone—V2X—encompasses V2V, V2I, V2N, and V2P modalities, each with distinct latency, bandwidth, and security requirements. The architecture supports real-time data exchange for safety, mobility, and efficiency applications.
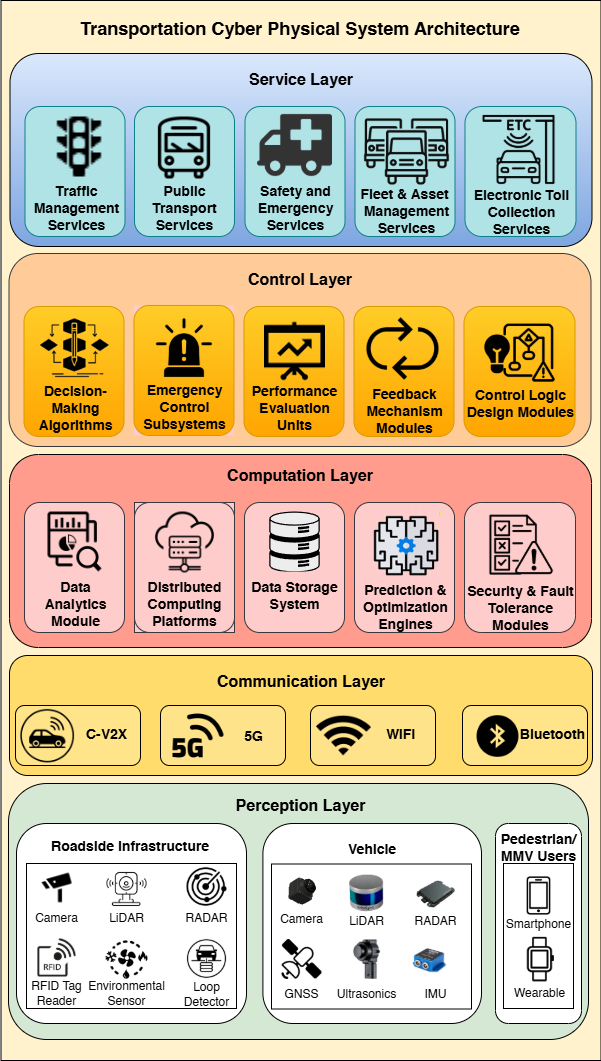
Figure 1: TCPS Architecture, illustrating the layered integration of sensing, communication, computation, control, and service functionalities.
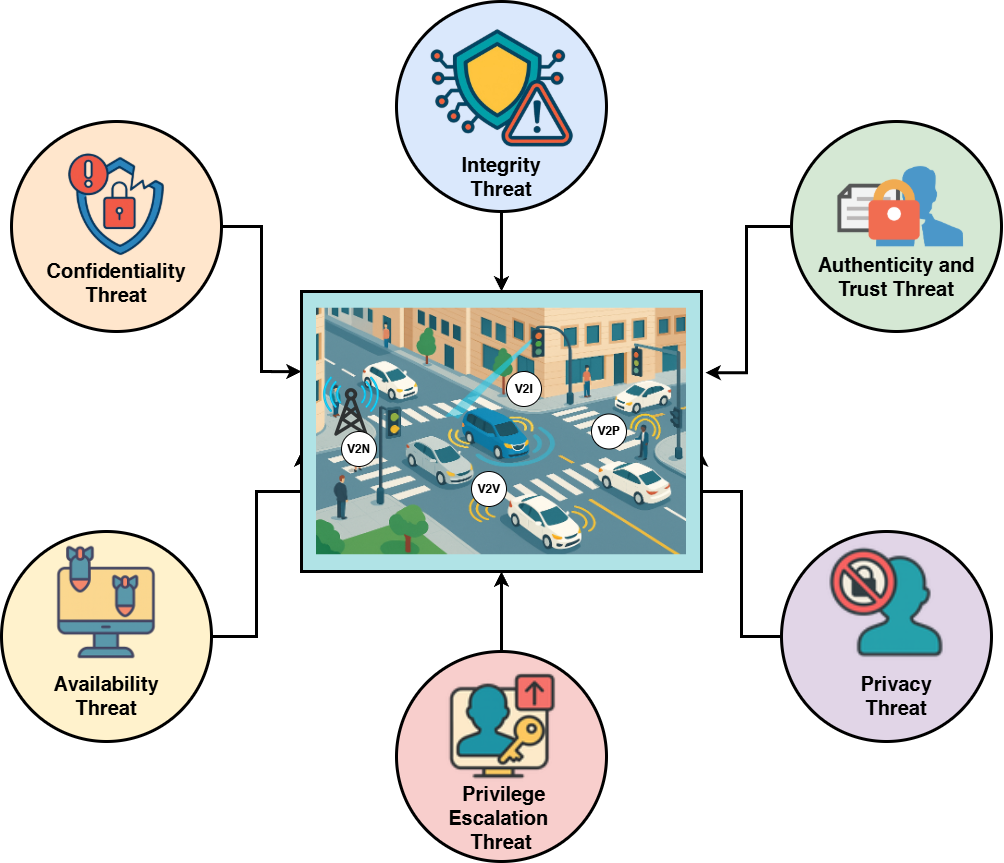
The attack surface in TCPS is broad, with adversaries targeting confidentiality, integrity, authenticity, availability, privacy, and privilege escalation. Concrete exploits include passive eavesdropping, message tampering, Sybil attacks, RF jamming, and side-channel key leakage. The paper highlights that even with robust cryptographic primitives, metadata analysis and implementation flaws can compromise privacy and control, underscoring the need for holistic, multi-layered defenses.
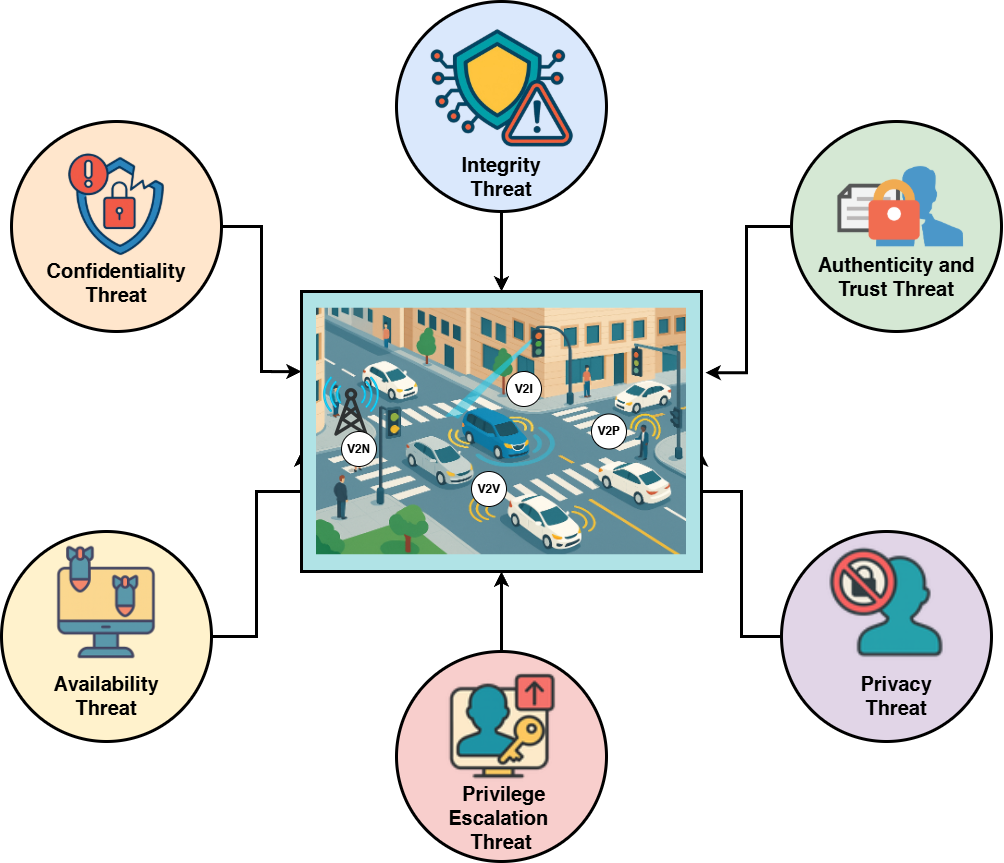
Figure 2: TCPS Vulnerabilities, mapping attack strategies to security properties and illustrating the multifaceted threat landscape.
Limitations of Classical Cryptography in the Quantum Era
Current TCPS deployments rely on RSA, ECC, AES, and SHA-2/3 for key exchange, authentication, encryption, and integrity. The security of these primitives is predicated on the intractability of integer factorization and discrete logarithms for classical computers. However, Shor’s algorithm renders all widely deployed public-key schemes (RSA, DH, ECC) insecure in polynomial time on a sufficiently large quantum computer. Grover’s algorithm halves the effective security of symmetric ciphers and hash functions, necessitating larger key and output sizes to maintain equivalent security margins.
The paper emphasizes that while symmetric primitives can be hardened by increasing key sizes (e.g., AES-256), there is no practical mitigation for the collapse of public-key cryptography aside from migration to PQC. This creates an urgent imperative for TCPS stakeholders to transition to quantum-resistant algorithms to preserve the integrity and trustworthiness of vehicular communications.
Post-Quantum Cryptography: Algorithmic Landscape and Deployment Trade-offs
The authors provide a detailed taxonomy of PQC algorithm families:
- Lattice-based (e.g., Kyber, Dilithium, Falcon): Offer strong security and moderate key/signature sizes, with efficient arithmetic operations. These are the current NIST standards for KEM and digital signatures.
- Code-based (e.g., Classic McEliece, HQC): Feature large public keys but fast encryption/decryption and a long security track record.
- Hash-based (e.g., SPHINCS+, XMSS): Rely solely on hash function security, yielding large signatures and slower verification, but minimal cryptographic assumptions.
- Multivariate polynomial and isogeny-based schemes: Once promising for compactness or efficiency, but recent cryptanalysis has broken all NIST finalist candidates in these families.
The paper notes that lattice-based schemes are the most practical for V2X safety messaging and certificate provisioning, while code-based and hash-based schemes are better suited for backend authorities and infrequent operations. However, PQC primitives generally incur higher computational and bandwidth overheads than their classical counterparts, challenging the strict latency (e.g., sub-100 ms for safety messages) and resource constraints of TCPS.
AI-Driven PQC: Adaptive Security and Resource Optimization
The core contribution of the paper is the proposal and analysis of AI-driven frameworks for PQC deployment in TCPS. The authors identify several key roles for AI:
- Adaptive Algorithm Selection: ML models (e.g., KNN, RL) dynamically select cryptographic primitives and parameters based on context (CPU load, channel conditions, threat level), optimizing the trade-off between security and performance.
- Threat Prediction and Proactive Defense: AI ingests threat intelligence and system telemetry to forecast quantum risk and automate migration to stronger cryptographic profiles as needed.
- Resource Optimization: RL-based schedulers and Bayesian optimization allocate cryptographic workloads, offload heavy computations to edge/cloud, and tune parameters to meet latency and energy budgets.
- Anomaly and Intrusion Detection: Deep learning models (CNN, LSTM) detect replay, spoofing, and side-channel attacks in real time, providing a second line of defense against implementation-level exploits.
- Hybrid Cryptosystem Orchestration: AI manages the transition from classical to PQC, deciding when to use hybrid signatures/certificates and automating key rotation and trust-anchor retirement.
The paper presents empirical evidence and literature benchmarks showing that AI-driven PQC can maintain sub-100 ms latency for safety-critical V2X messages, reduce energy consumption by up to 30% in wireless sensor networks, and adaptively harden security posture in response to detected threats or system anomalies.
The deployment of AI-driven PQC in TCPS requires:
- Profiling of cryptographic primitives on target hardware (OBUs, RSUs, edge servers) to determine feasible parameter sets.
- Integration of ML inference engines with cryptographic libraries, ensuring real-time decision-making without introducing unacceptable overhead.
- Secure and verifiable AI models, as adversarial manipulation of the AI layer could itself become a new attack vector.
- Hybrid certificate and key management infrastructure to support phased migration and backward compatibility.
Performance metrics of interest include cryptographic operation latency, message size overhead, CPU/memory utilization, energy consumption, and detection accuracy/false positive rates for anomaly detection modules. The paper reports that, after parameter tuning and selective offloading, Kyber and Dilithium can meet the 100 ms safety-latency target in most scenarios, but dense traffic or high message rates may still stress embedded CPUs and radio channels.
Implications and Future Research Directions
The integration of AI and PQC in TCPS has both practical and theoretical implications:
- Practical: Enables quantum-safe, cyber-resilient vehicular networks that can adapt to evolving threats and heterogeneous deployment environments. Facilitates compliance with emerging NIST and industry standards for post-quantum security.
- Theoretical: Opens new research avenues in lightweight PQC design, formal verification of adaptive security policies, AI-augmented hybrid cryptosystems, and side-channel attack resilience.
The paper identifies several open challenges: designing PQC primitives tailored for low-latency, resource-constrained environments; developing formally verified, adaptive security protocols; orchestrating large-scale pilot deployments; and ensuring the robustness of AI models against adversarial manipulation.
Conclusion
This work provides a rigorous, system-level analysis of the challenges and opportunities in securing TCPS against quantum-enabled adversaries. The authors demonstrate that classical cryptography is fundamentally inadequate for long-term TCPS security, and that PQC—while necessary—introduces new performance and integration challenges. AI-driven orchestration emerges as a critical enabler, allowing TCPS to dynamically balance security, performance, and resource constraints. The synergy of PQC and AI is positioned as essential for the future of secure, resilient, and intelligent transportation systems. Continued research in lightweight PQC, adaptive AI security frameworks, and large-scale field validation will be pivotal in realizing quantum-safe mobility infrastructure before the advent of practical quantum attacks.