- The paper presents a digital emulation framework for quantum random number generation by harnessing system timing jitter and random permutations.
- It rigorously maps the Poisson statistics of coherent optical states to a modular projection method that produces uniform outputs with exponentially decaying error bounds.
- Experimental validation in a Java implementation shows precise moment matching and high entropy outputs that meet NIST SP 800-90B benchmarks.
Digital Emulation of Coherent-State Quantum Random Number Generation via System Jitter Entropy and Random Permutation
Introduction and Motivation
This work presents a rigorous framework for fully digital emulation of coherent-state quantum random number generation (QRNG) through system timing jitter–driven random permutation processes (2512.11107). The methodology establishes that the statistical underpinnings of quantum coherent states—traditionally yielding irreducible randomness derived from the quantum granularity of light—can be mapped, controlled, and certified through physical entropy inherent in classical computation platforms. The approach is motivated by the operational and practical limitations of conventional QRNGs, including dependency on specialized photonic hardware and elaborate post-processing, which constrain their widespread cryptographic deployment.
Theoretical Framework: Statistical Equivalence of Quantum and Classical Domains
The central result elaborates the precise statistical equivalence between physical coherent-state photon counting and software-based emulation rooted in the structure of Poisson statistics. Coherent states ∣α⟩, parameterized by complex amplitude α, yield Poisson-distributed photon numbers P(n)=e−∣α∣2∣α∣2n/n!, characterized by mean and variance μ=∣α∣2. This discrete statistical structure constitutes the irreducible quantum resource in standard QRNGs.
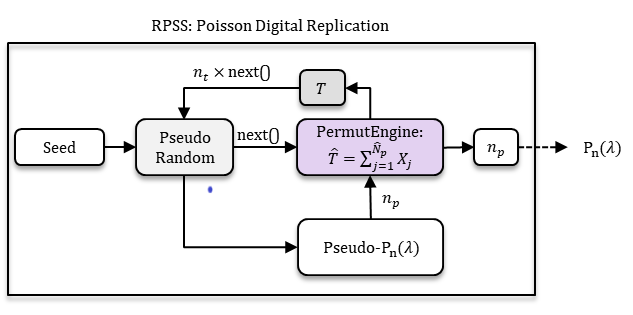
The digital replication pipeline replaces physical quantization with a Random Permutation Sorting System (RPSS) driven by system-level timing jitter. Counts np are generated pseudo-randomly but are rendered non-deterministic via feedback from permutation execution times T^, which encode entropy from microarchitectural and OS-level nondeterminism. This creates a direct analogy: the count observable in quantum optics finds its counterpart in permutation count, and the unobservable phase/timing uncertainty is mirrored by execution time fluctuations.
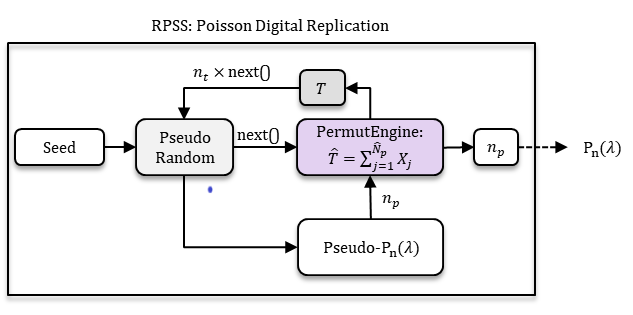
Figure 1: RPSS architecture for digital replication of Poisson statistics with recursive entropy injection via permutation timing feedback.
Crucially, the mapping from Poisson statistics to cryptographically uniform output is controlled by modular projection: R=npmodM. The paper rigorously proves the Poisson Modular Convergence Theorem, which delineates the exponential convergence of residue classes to uniformity as a function of μ and modulus M, with error bounds that decay as exp(−2μsin2(π/M)). This provides a mathematically strict certificate for the transformation from quantum-inspired Poisson input to uniform digital randomness.
Experimental Realization and Statistical Validation
The digital RPSS architecture is instantiated in Java, leveraging high-resolution timing sources (System.nanoTime, ~100ns granularity) for entropy injection. In each generation cycle, a Poisson(μ) random count is sampled, triggering Fisher-Yates permutations of small arrays. Execution times of these operations are used to advance the PRNG state, ensuring unpredictability and non-reproducibility—even with identical seeds.
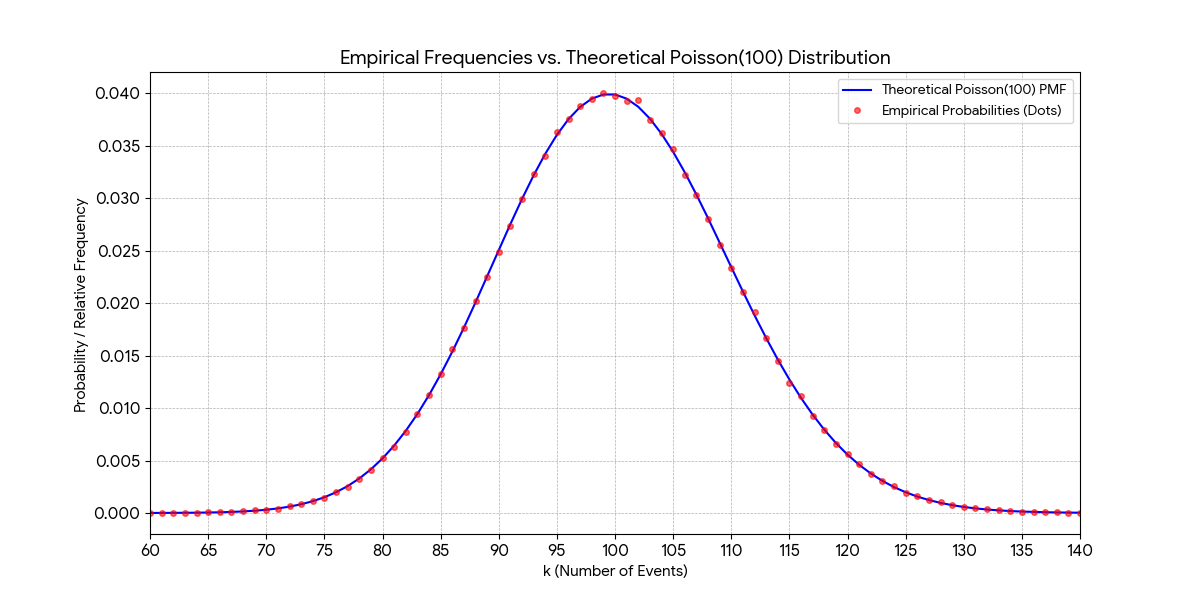
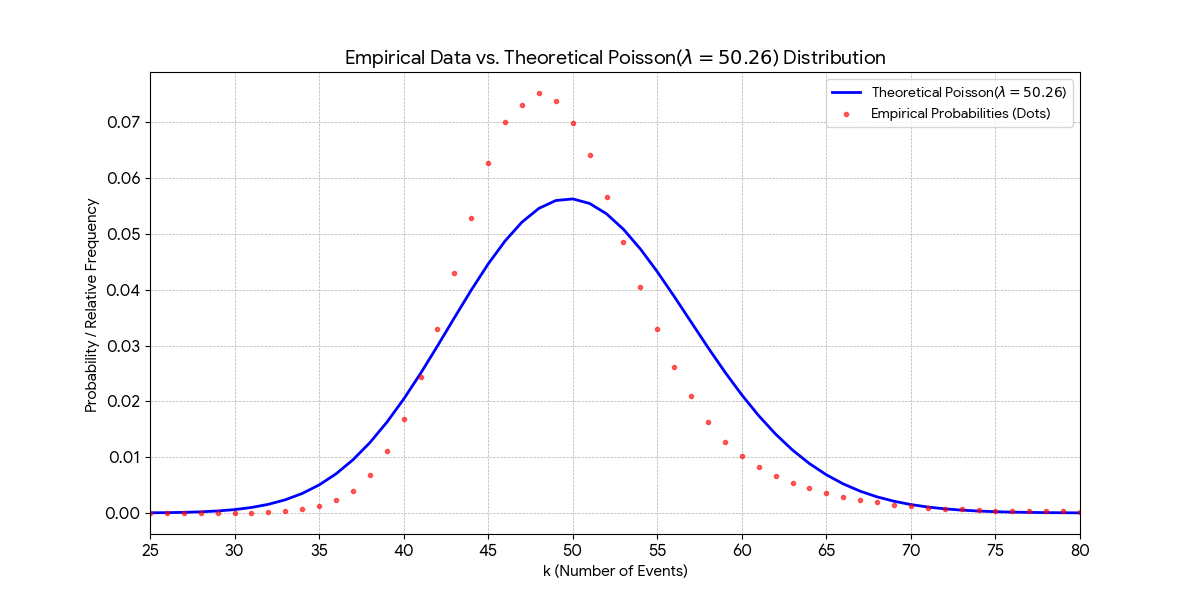
Comprehensive experimental validation is presented for small (μ=7) and large (μ=100) Poisson means. Replicated statistics exhibit close agreement with theory across all four moments, affirming the property ⟨n⟩=⟨(Δn)2⟩.
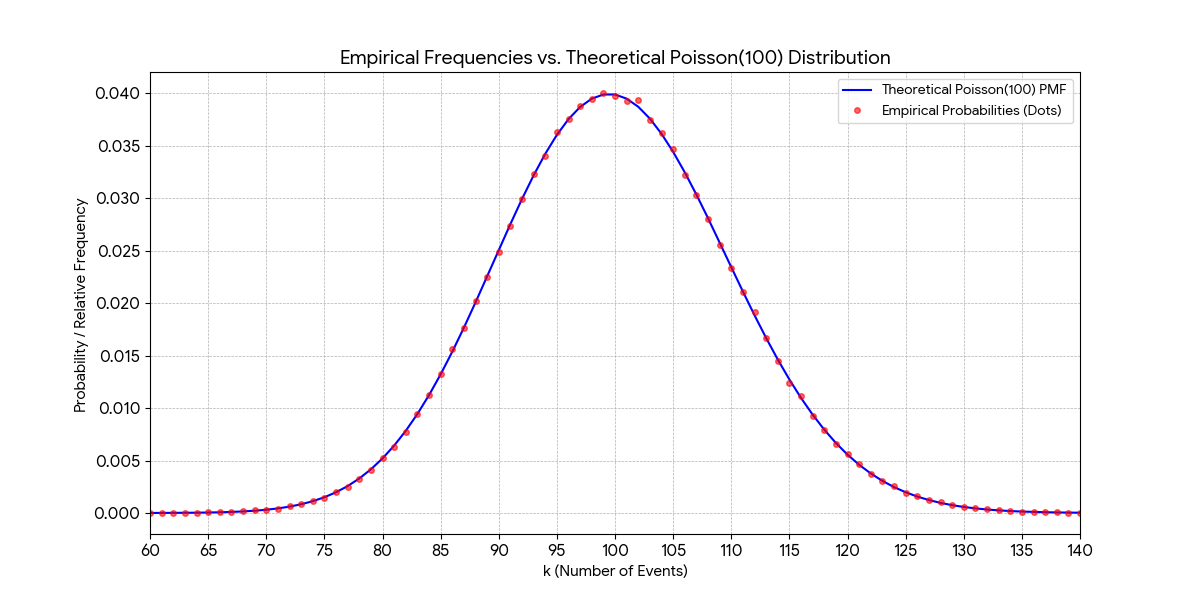
Figure 2: Digital replication of coherent-state Poisson(μ=100): Empirical and theoretical PMFs are nearly indistinguishable, verifying precise moment matching and distributional fidelity.
(RPSS moment validation details omitted here for brevity but match the paper: means, variances, skewness, kurtosis are within ∼0.01% of theory for both regimes.)
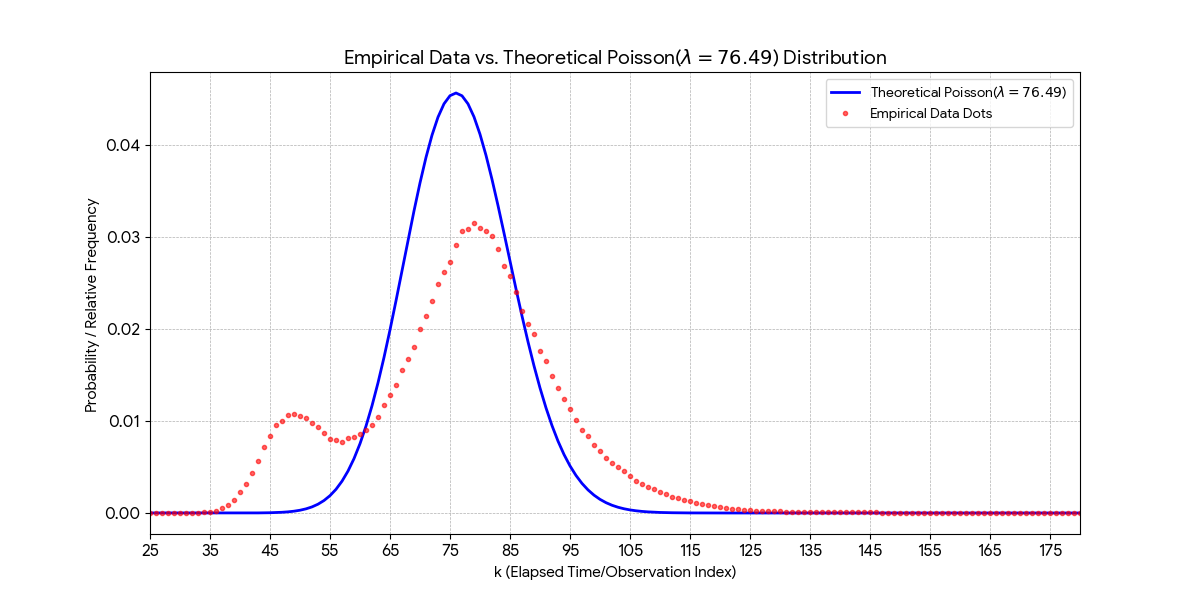
Elapsed timing data further demonstrate non-ideal, composite characteristics, reflecting the convolution of microarchitectural entropy sources. This ensures high min-entropy injection at every cycle while simultaneously preserving output Poisson statistics.
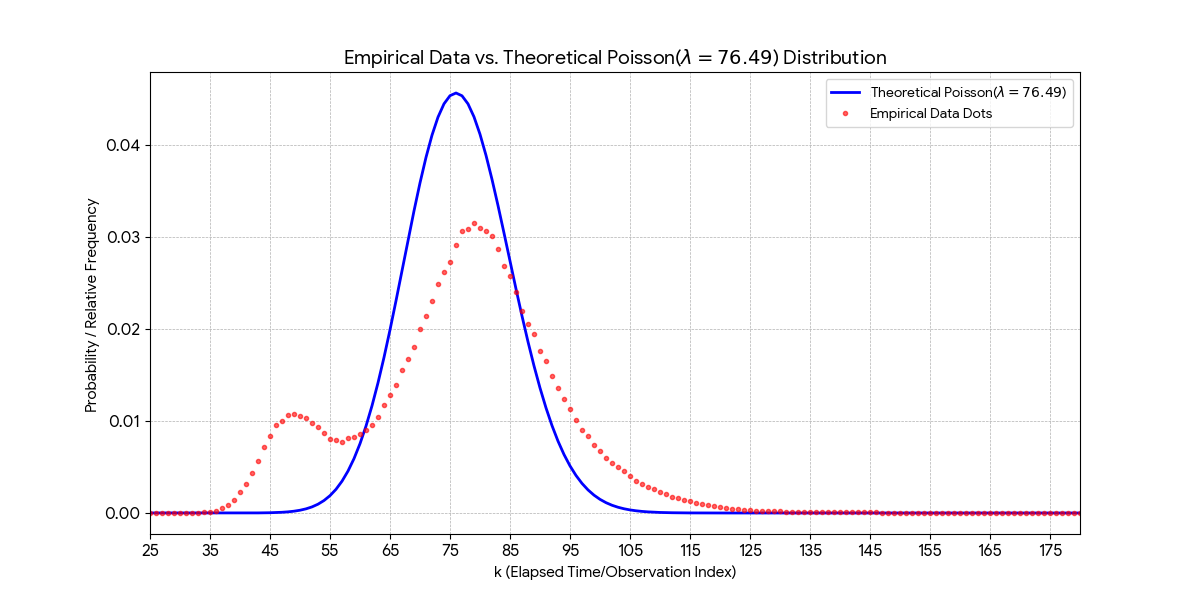
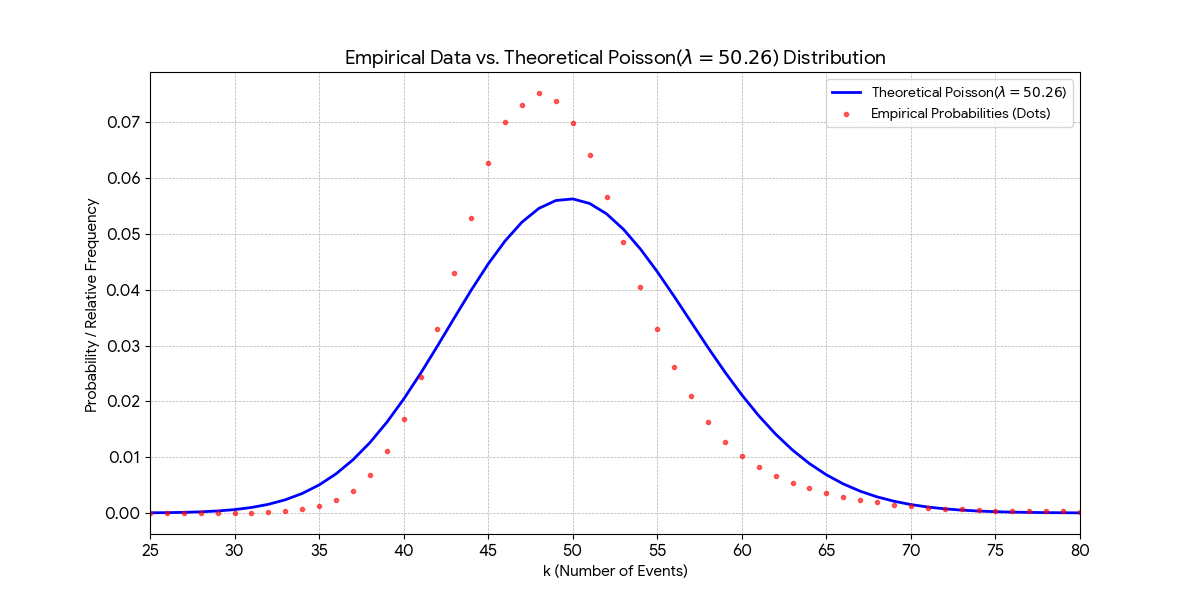
Figure 3: Compound elapsed time distribution for Poisson(μ=100): Execution time statistics reveal layered entropy injection through system jitter.
Application of modular projection to digitally replicated Poisson counts yields output bytes with Shannon entropy and min-entropy tightly converged to theoretical maxima (e.g., 7.999998 bits/byte at 108-byte scale, min-entropy exceeding 7.99 bits/byte). Empirical results exceed NIST SP 800-90B benchmarks and theoretical lower bounds for practical moduli, with χ2 statistics indistinguishable from the ideal uniform distribution across all experiments.
The security treatment is twofold. Information-theoretic security is guaranteed by analytic lower bounds on conditional min-entropy, parameterized by adversarial side information A, and remains robust against computationally unbounded adversaries. Computational security is enhanced by active timing obfuscation, microarchitectural entropy amplification (engaging caches, speculative execution, etc.), and inherent forward secrecy stemming from continual entropy refresh through non-observable timing channels.
Notably, both statistical and security properties are rigorously validated without recourse to post-processing via cryptographic primitives, a common requirement in physical QRNG devices.
Implications, Extensions, and Future Directions
The digital coherent-state QRNG architecture reframes the quantum-classical boundary in randomness generation. It demonstrates that the core statistical signature enabling quantum-certified randomness—irreducible Poissonian noise—can be realized, monitored, and certified via classical computational means, provided sufficient access to physically rooted system entropy. This finding has several direct implications:
- Practical deployments: High-quality quantum-grade randomness can be delivered at scale on commodity digital hardware, removing the reliance on specialized optical components and complex calibration pipelines.
- Security and cryptography: Mathematical guarantees for uniformity and unpredictability, robust to both information-theoretic and practical adversaries, enable immediate applicability in key generation and protocol design.
- Hybrid and dynamic adaptation: The framework supports seamless switching or mixing between hardware (photonic) and digital randomness sources, guided by application constraints or entropy monitoring.
- Generalizability: The architecture is shown to naturally extend to other quantum-inspired statistical regimes (e.g., Binomial, Negative Binomial), facilitating software-based emulation of a broader class of quantum random processes.
Potential avenues for further development include formal cryptographic proofs for composite pipeline security, leveraging real-time entropy monitors and ML-based adaptation of system parameters, and porting the RPSS core to hardware accelerators or secure enclaves.
Conclusion
This work establishes, both theoretically and experimentally, that a fully digital architecture composed of system-jitter driven random permutations, mathematically certified modular projection, and analytic entropy analysis can replicate the essential statistical properties of coherent-state QRNGs. The central result is the removal of a strict physical quantum-classical dichotomy: high-quality uniform randomness, conventionally bound to optical quantum phenomena, becomes a function of stochastic computation and physically coupled entropy processes. The RPSS-based architecture offers verifiable, high-throughput, and secure random number generation, suitable for deployment in cryptographic and scientific computation environments. The general methodological approach positions digital, quantum-inspired RNG as a practical and theoretically robust alternative to physical QRNG implementations.