- The paper demonstrates that feedback-driven spoofing using an external IMU sensor effectively neutralizes IMU-based GPS spoofing detection in autonomous vehicles.
- Experimental results show that the proposed method maintains innovation residuals below detection thresholds and achieves a high pattern similarity (≈0.99) in position spoofing.
- The study highlights the vulnerability of EKF sensor fusion frameworks and underscores the need for enhanced, multi-modal security measures in AVs.
Neutralization of IMU-Based GPS Spoofing Detection Using External IMU Sensor and Feedback Methodology
Introduction
This paper presents a comprehensive study on the neutralization of inertial measurement unit (IMU)-based GPS spoofing detection in autonomous vehicles (AVs). The authors propose a novel attack model leveraging an external IMU sensor, coupled with a feedback-driven spoofing mechanism, to systematically bypass prevalent IMU-based anomaly detection techniques within Extended Kalman Filter (EKF) sensor fusion frameworks. The work bridges a significant gap in practical spoofing attack research, improving on prior approaches that either assume high-fidelity attacker knowledge or ignore detection mechanisms altogether.
Background: GPS Spoofing, EKF Sensor Fusion, and Detection
Absolute localization in AVs remains critically dependent on GPS. However, unidirectional GPS communication and the inability to encrypt satellite-based transmissions render GPS inherently susceptible to spoofing attacks, where adversaries transmit stronger counterfeit signals to override legitimate GPS data. While a variety of radio-frequency (RF)–driven detection strategies have been explored, their practical efficacy is limited due to costs and susceptibility to adversarial adaptation.
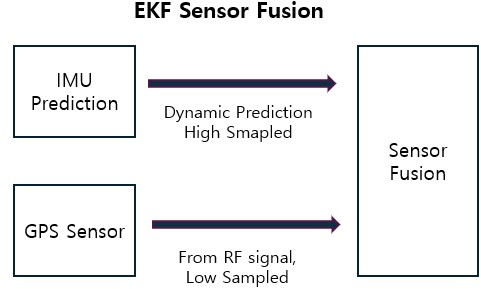
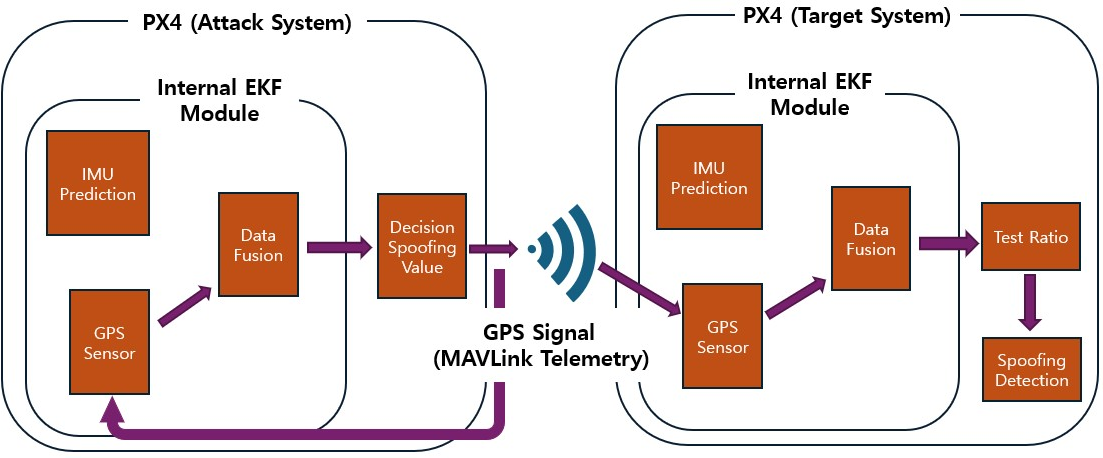
As a countermeasure, IMU-based internal detection mechanisms within EKF sensor fusion frameworks are widely deployed. These methods utilize the divergence (innovation) between GPS updates and IMU-integrated state estimates to signal possible GPS attacks. The EKF maintains internal state predictions using a nonlinear vehicle dynamics model and IMU data, incorporating GPS measurements opportunistically due to asynchronous sensor update rates.
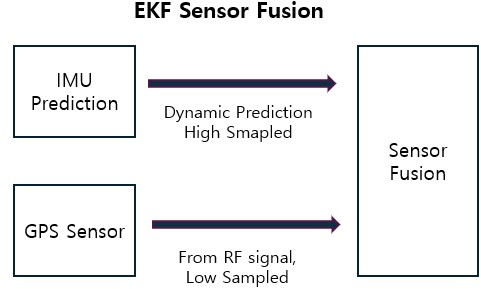
Figure 1: AV state estimation via EKF-based fusion of GPS and IMU data.
Traditional spoofing detection flags attacks by monitoring test ratios—normalized innovations between predicted and measured positions or velocities. Accumulated innovation sums and temporal pattern similarity coefficients offer additional robustness for anomaly identification.
Proposed Attack and Neutralization Model
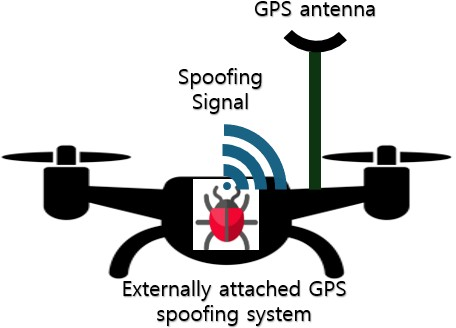
The attack model shifts from remote spoofing paradigms (which require physical proximity or high-resolution localization of the target) to a more feasible scenario where the attacker physically attaches a GPS spoofing system, equipped with its own IMU, to the target AV.
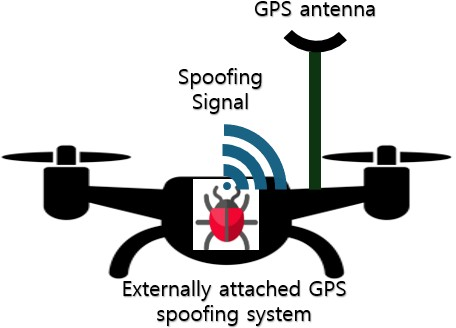
Figure 2: The conventional model—remote GPS spoofing against the AV with no physical presence required.
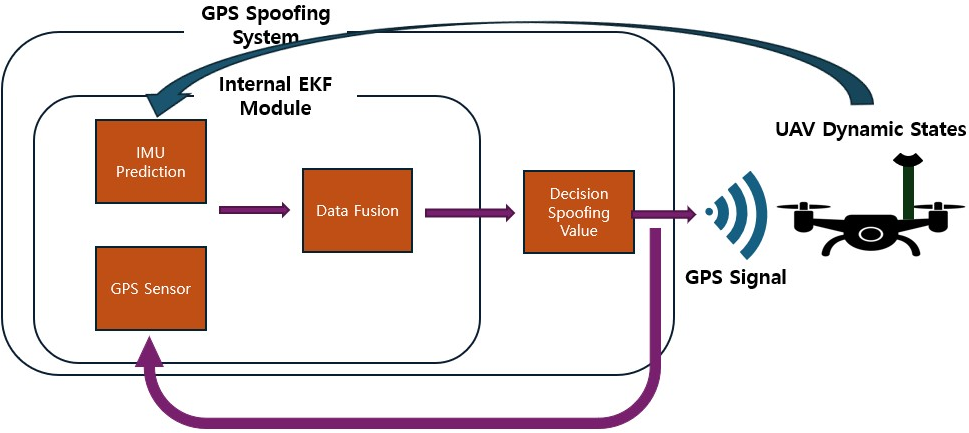
Figure 3: The proposed model—an attacker’s spoofing and IMU system is locally attached to the AV for continuous, precise spoofing.
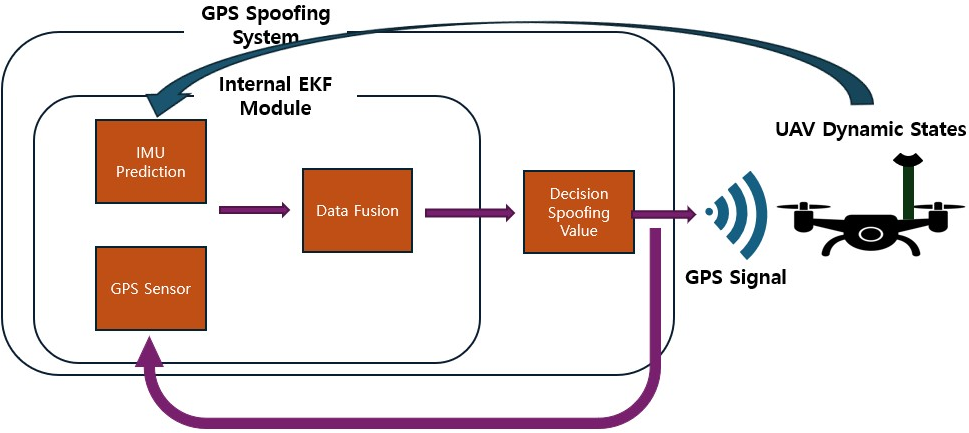
Key to the neutralization strategy is the dynamic adjustment of spoofed GPS values based on continuous feedback from the attacker’s external IMU and previously injected spoof values. This feedback mechanism allows the attacker to closely track and influence the convergence behavior of the AV’s sensor-fusion state estimator, thereby minimizing innovation residuals and evading detection thresholds.
Algorithmically, the spoofing procedure initializes the attack state, predicts dynamic states from the external IMU, fuses prior spoofing values, injects calculated deltas, and integrates observed target system responses to iteratively refine future spoof values.
Experimental Methodology
Given regulatory prohibitions regarding actual RF-based GPS spoofing, the authors use MAVLink telemetry signaling in the PX4 autopilot platform to inject spoofed GPS data at the controller layer.
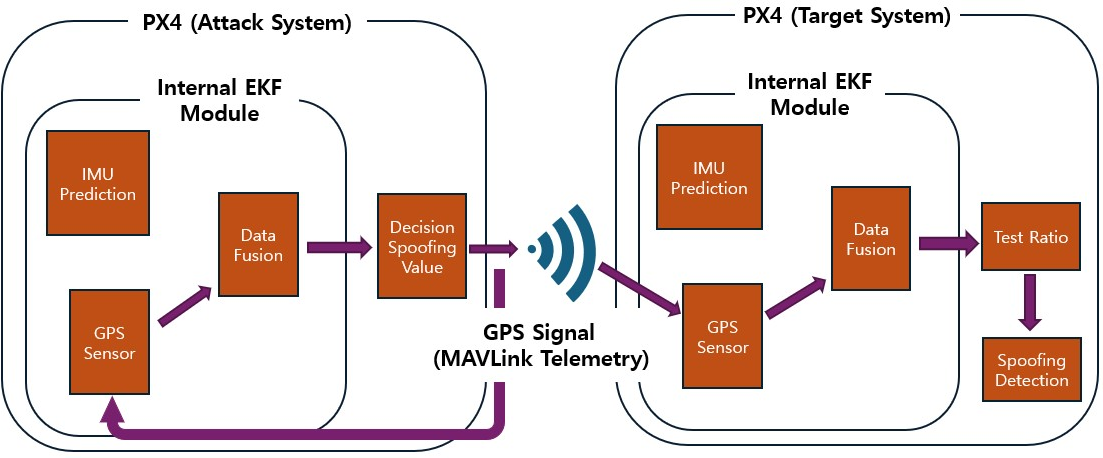
Figure 4: Experimental setup featuring MAVLink-based simulated GPS spoofing within a dual-controller testbed.
Data are collected under multiple conditions: (a) constant-value spoofing, (b) IMU-only spoofing, and (c) feedback-driven spoofing. Further, both position and velocity signals are targeted, with velocity spoofing leveraging direct IMU-based estimation without additional feedback due to the non-integrative nature of velocity in sensor fusion.
Experimental Results
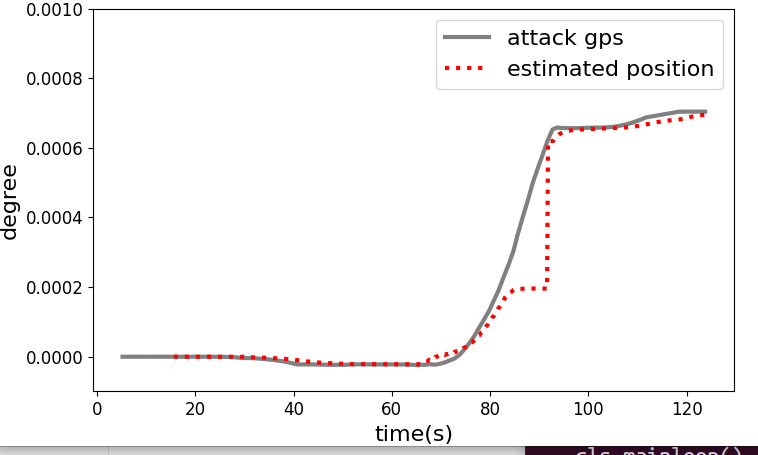
When the attacker sends constant spoofed positions, detection test ratios quickly escalate as innovation residuals accumulate. IMU-only spoofing can initially track target motion, but integration drift rapidly inflates differences, resulting in detectable anomalies.
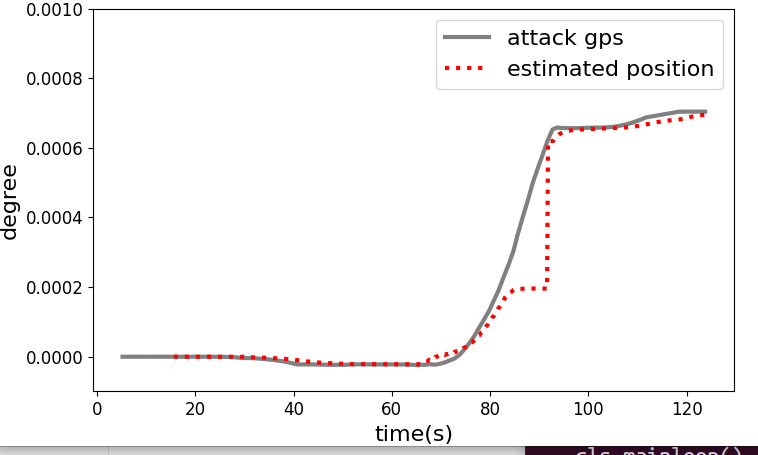
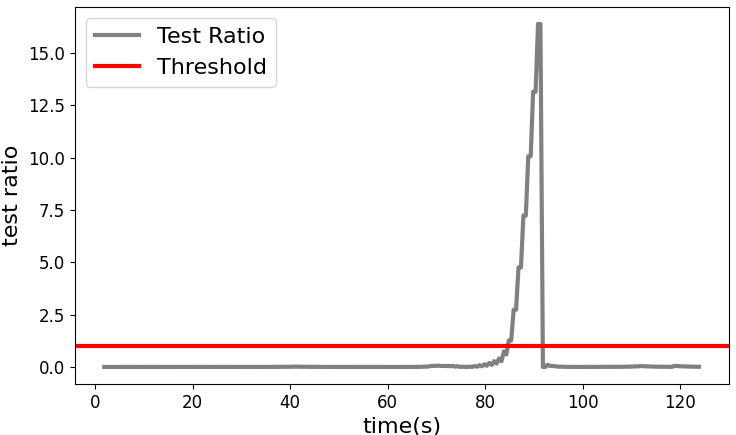
Figure 5: Target latitude dynamics (red) and spoofed GPS latitude (gray) under IMU-only injection—deviation accumulates due to IMU drift.
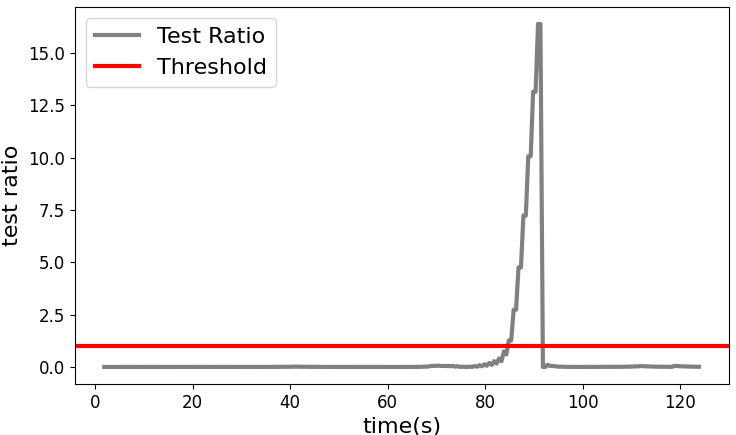
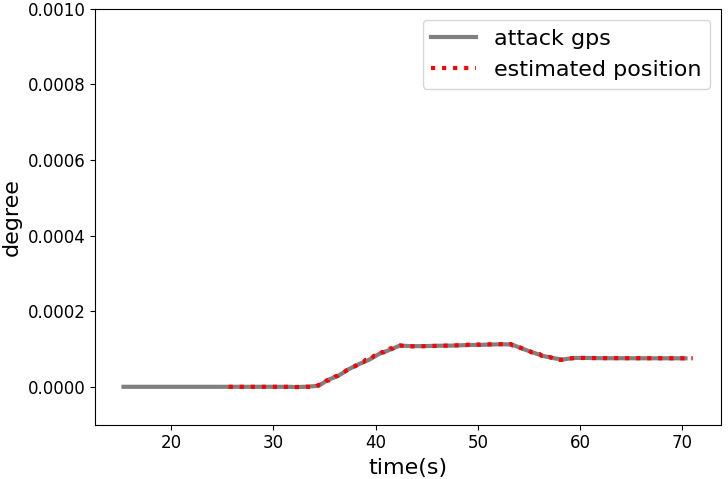
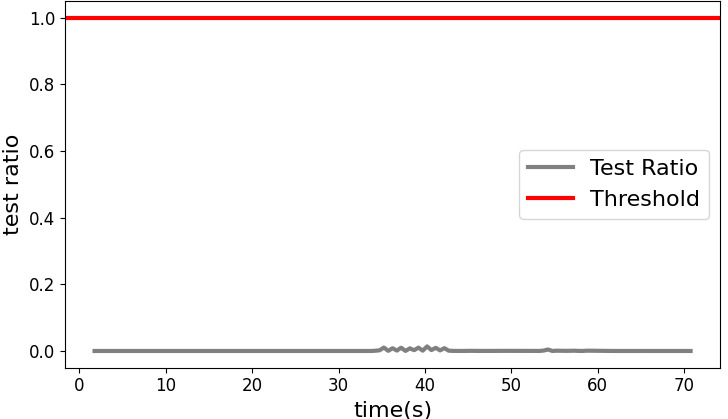
The feedback-based methodology reliably maintains injected values within the AV’s estimated latitude, with test ratios remaining well below conventional detection thresholds (max ≈ 0.014, far below the standard threshold of 1).
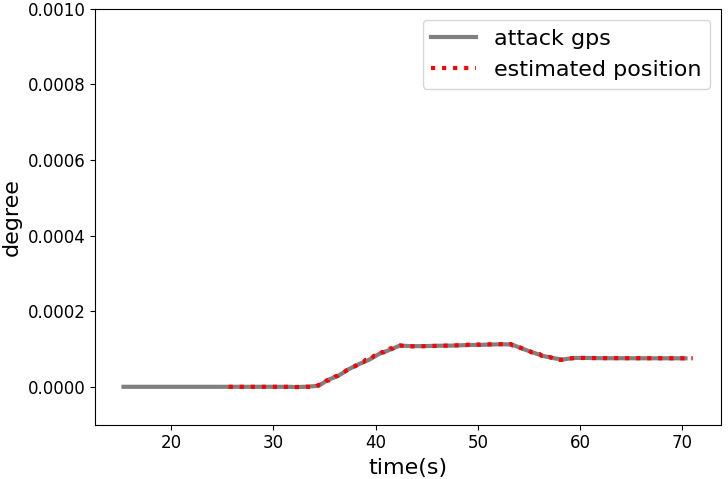
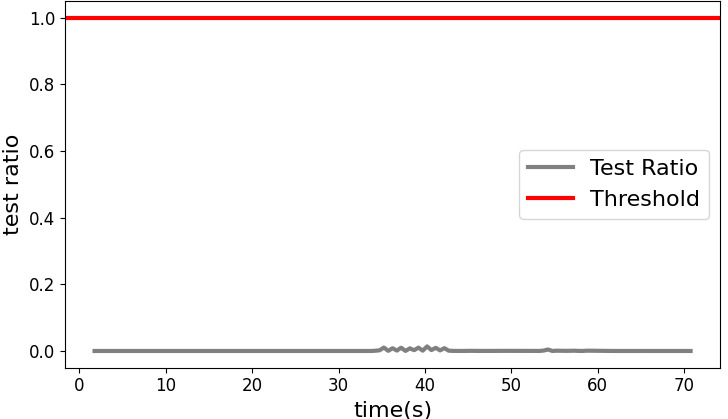
Figure 6: Feedback-based attack maintains close synchronization between target latitude (red) and spoofed GPS latitude (gray), preventing anomaly detection.
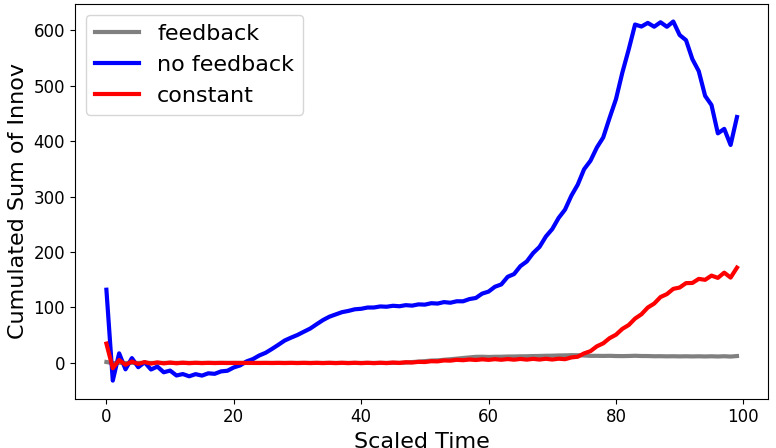
Cumulative sum and pattern similarity analyses substantiate the superiority of feedback-driven spoofing: the feedback method achieves a coefficient of approximately 0.99, indicating high alignment with the internal pattern; the IMU-only method achieves ≈0.97, and constant spoofing fails to follow the internal dynamics entirely.
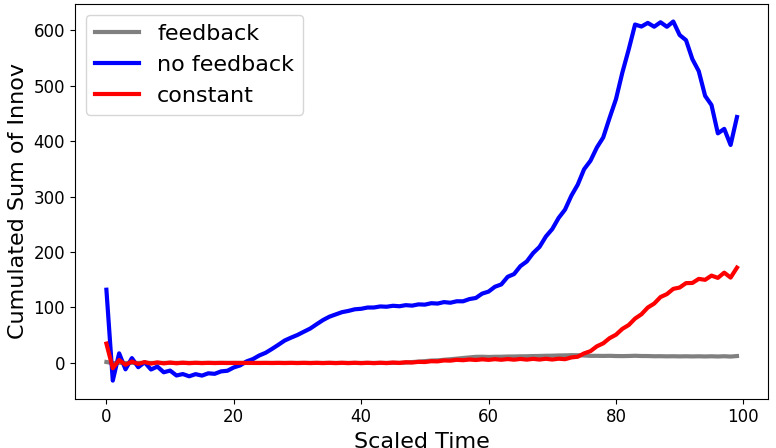
Figure 7: Accumulated error between internal estimates and injected values—feedback-based approach (gray) maintains minimal divergence, outperforming constant (red) and IMU-only (blue) methods.
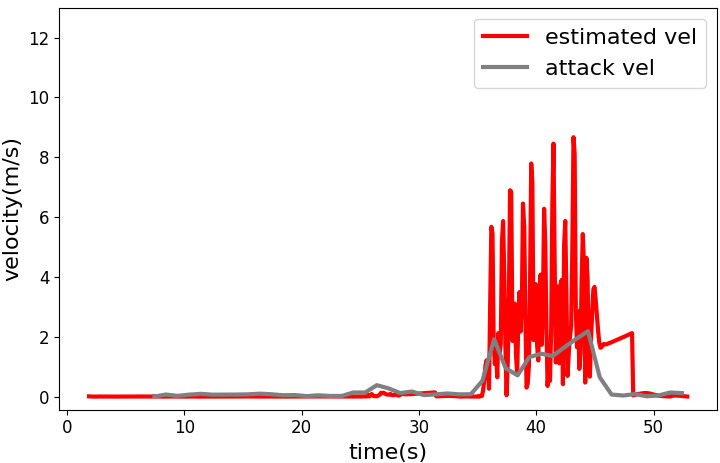
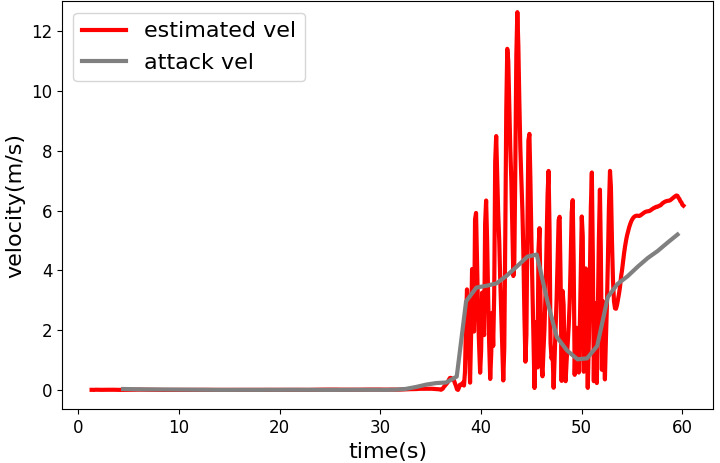
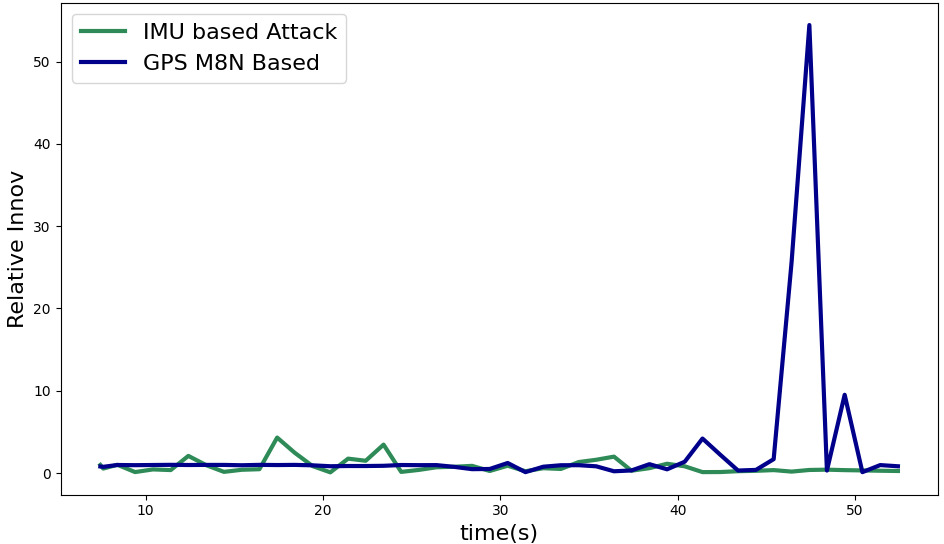
Velocity injection experiments compare estimates from the GPS M8N sensor, the internal controller’s state, and the attacker's IMU. Results show that external IMU-based injection most closely follows the internal controller’s velocity estimates.
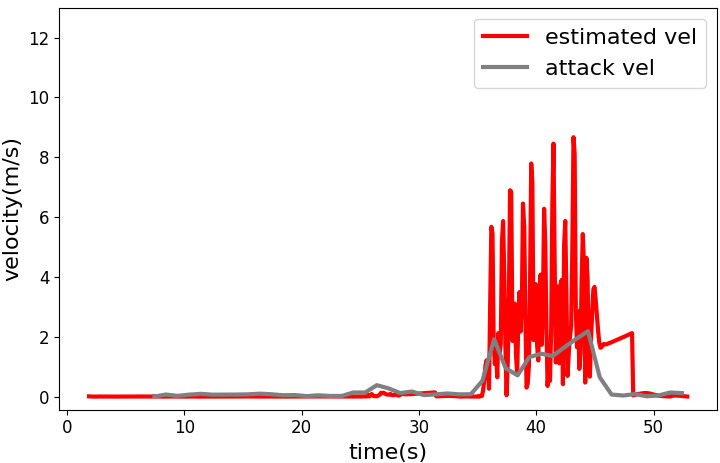
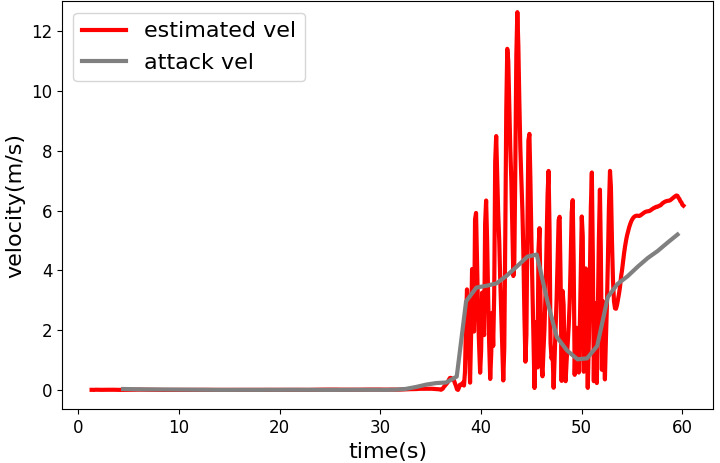
Figure 8: Velocity trace from M8N GPS sensor (gray) versus controller estimate (red); IMU-based estimates offer sharper tracking.
Relative innovation error for IMU-based estimation is consistently lower than for standard GPS, and the pattern similarity coefficient is higher (0.87 for IMU, 0.76 for M8N GPS).
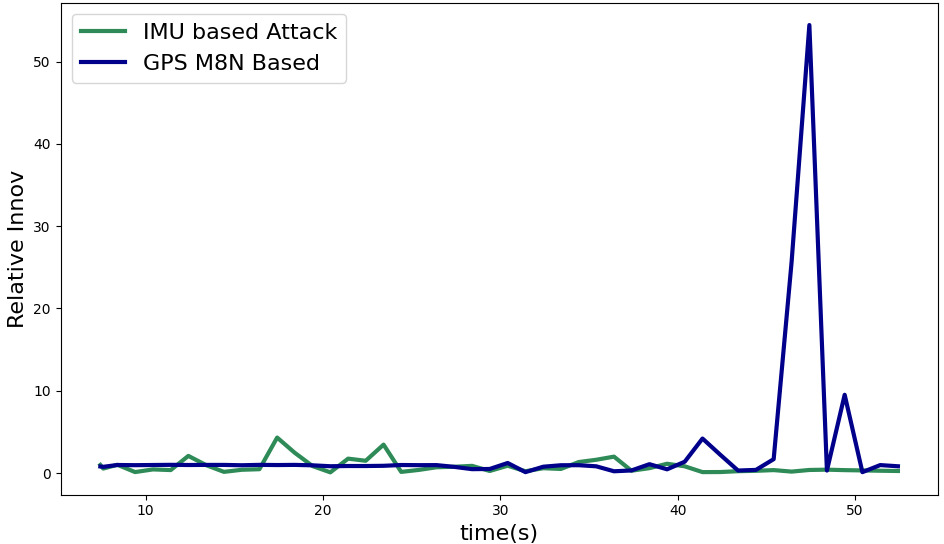
Figure 9: Relative velocity estimation error—external IMU (green) consistently outperforms GPS-based injection (blue) in following internal velocity dynamics.
Discussion
This work effectively demonstrates that IMU-based spoofing detection mechanisms can be systematically neutralized with an external IMU and a closed-loop feedback strategy. The attack method circumvents the need for high-resolution external localization (e.g., radar tracking) and is materially feasible wherever attackers can mount hardware on the target.
By reflecting the dynamic state influence of spoofed values within the fusion algorithm, the feedback-based attack accurately tracks the evolving state of the target’s estimator, evading both instantaneous and accumulated error-based detection schemes. The results are robust across both position and velocity signal channels, with velocity spoofing exhibiting reduced innovation errors and higher correlation with internal estimates when using the external IMU.
These findings challenge a major assumption in AV security: that internal sensor-based detection offers strong protection against GPS spoofing. The approach exposes significant practical vulnerabilities, particularly in environments where physical access to the AV is possible (service depots, supply chain stages, malicious maintenance).
Implications and Future Directions
Theoretically, the paper elucidates the coupled dynamics of sensor fusion under adversarial input and introduces new considerations for the observable state divergence under feedback-driven attacks. Practically, it highlights the urgent need for detection algorithms accounting for sophisticated attacker models equipped with external sensor feedback.
Future defense strategies may require:
- Secure IMU attestation to validate measurement provenance,
- Data-driven anomaly detectors sensitive to non-observable pattern similarities,
- Multi-modal sensor fusion leveraging hard-to-access or cryptographically protected state variables,
- Onboard anomaly detection that leverages unsynchronized or cross-domain sensor modalities.
Further research should investigate resilience under adversarial co-location, extend to other classes of internal sensors, and explore mitigation strategies robust to dynamic, feedback-capable attacks.
Conclusion
This paper establishes that state-of-the-art IMU-based GPS spoofing detection in AVs can be effectively neutralized using an external IMU sensor and an iterative feedback-based spoofing algorithm. The threat model is practically feasible in use cases where attackers can physically access vehicles, and the experimental evidence underscores the inadequacy of standard fused-sensor detection under such attack paradigms. The findings call for re-evaluation of existing detection frameworks and the development of robust, multi-modal security solutions for autonomous navigation systems.
[Original Paper: "Neutralization of IMU-Based GPS Spoofing Detection using external IMU sensor and feedback methodology", (2512.20964)]