Practical quantum teleportation with finite-energy codebooks
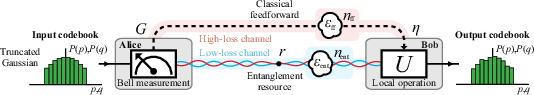
Abstract: Quantum communication exploits non-classical correlations to achieve efficient and unconditionally secure exchange of information. In particular, the quantum teleportation protocol allows for a deterministic and secure transfer of unknown quantum states by using pre-shared quantum entanglement and classical feedforward communication. Quantum teleportation in the microwave regime provides an important tool for high-fidelity remote quantum operations, enabling distributed quantum computing with superconducting circuits and potentially facilitating short-range, open-air microwave quantum communication. In this context, we consider practical application scenarios for the microwave analog quantum teleportation protocol based on continuous-variable states. We theoretically analyze the effect of feedforward losses and noise on teleportation fidelities of coherent states and show that these imperfections can be fully corrected by an appropriate feedforward gain. Furthermore, we consider quantum teleportation with finite-size codebooks and derive modified no-cloning thresholds as a function of the codebook configuration. Finally, we analyze the security of quantum teleportation under public channel attacks and demonstrate that the corresponding secure fidelity thresholds may drastically differ from the conventional no-cloning values. Our results contribute to the general development of quantum communication protocols and, in particular, illustrate the feasibility of using quantum teleportation in realistic microwave networks for robust and unconditionally secure communication.
Paper Prompts
Sign up for free to create and run prompts on this paper using GPT-5.
Top Community Prompts
Explain it Like I'm 14
Overview
This paper is about a way to “teleport” quantum information using microwaves. Instead of moving the physical object, quantum teleportation moves the “state” (the exact way a tiny quantum signal looks) from one place to another. The authors study how to make this work in realistic conditions, where there are losses and noise, and where messages can only use a limited amount of energy. They also look at how secure this teleportation is if someone tries to eavesdrop on the public part of the communication.
Key Questions
- How well does microwave quantum teleportation work when the real world adds losses and noise?
- Can we fix some of these problems just by tuning the “gain” (like a volume knob) of the measurement and feedforward step?
- What happens to security when messages come from a limited “codebook” (a set of allowed signals) instead of an ideal, unlimited one?
- How secure is teleportation if an eavesdropper can listen to the public channel but not the private quantum resource?
Methods and Approach (in everyday language)
Think of two people, Alice and Bob. They want to send a secret quantum “state” without actually sending the state itself.
- Entanglement: Alice and Bob share a special pair of linked microwave signals called a “two‑mode squeezed” state. You can imagine two coins that are magically linked: if you look at one, you learn something about the other, even from far away. In quantum waves, this link shows up as special noise patterns that match in a useful way.
- Continuous variables: Instead of using bits (0 or 1), they use smooth wave properties like amplitude and phase, similar to turning a dimmer switch rather than flipping a light on or off.
- Coherent states: The messages are steady waves with a certain “displacement” in a 2D plane (think of a dot on a map with x and y coordinates). That dot is the information.
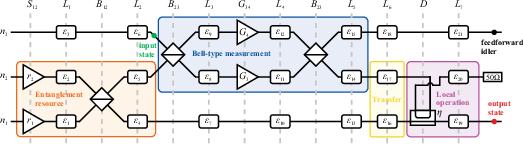
- Bell measurement and feedforward: Alice mixes the incoming message with her half of the entanglement, measures, and gets two numbers. She sends those numbers to Bob over a regular (public) channel. This is called “feedforward.” Bob uses those numbers to adjust his half of the entanglement so that it becomes a copy of the original message state.
- Handling imperfections: In real setups, the feedforward channel and the entanglement channel can lose signal and pick up thermal noise (like static on a radio). The authors model these effects and show when and how to compensate for them.
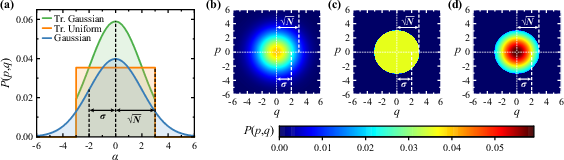
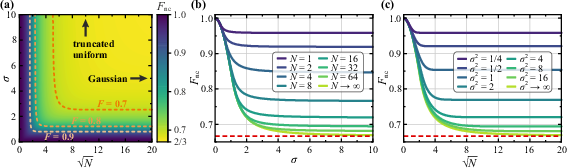
- Codebooks: A “codebook” is the set of allowed messages. Ideal papers often assume an infinite set (which would need infinite energy!). The authors focus on realistic, finite codebooks—either “truncated uniform” (a flat distribution within a circle) or “truncated Gaussian” (a bell curve cut off at a maximum energy). Different codebooks change how hard it is for an eavesdropper to make a good copy.
- Measuring performance: They use a standard measure called “fidelity,” which says how close Bob’s output is to Alice’s input (0 means unrelated, 1 means perfect match). They also use mutual information (how much information Alice and Bob share) and the Holevo quantity (an upper bound on what an eavesdropper could learn).
Main Findings
1) Feedforward losses and noise can be corrected by gain tuning
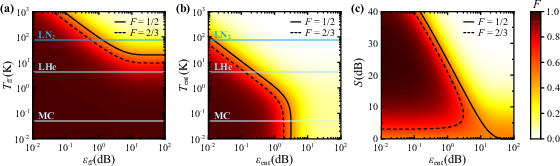
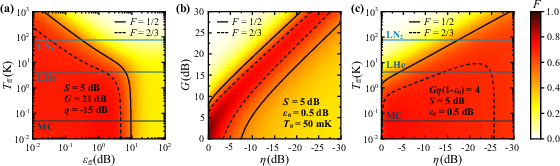
If the feedforward line adds loss or noise, Alice and Bob can choose the right measurement gain and a weak coupling at Bob’s end so that the noise from the public channel doesn’t spoil the teleportation. In simple terms: you can turn the knobs to cancel out the static in the public line. This works especially well for the feedforward path.
- Result: Even if the feedforward channel is warm and lossy, you can still get high fidelity by picking the right gain. In some cases, they show fidelities above the usual “no‑cloning” benchmark (2/3) even when the feedforward channel is at temperatures of many kelvin.
2) Losses in the entanglement path are much harder to fix
If the private entanglement path loses signal or adds noise, you cannot simply amplify it back (that would break quantum rules). This sets a limit on how useful extra squeezing (stronger entanglement) is: after some point, more squeezing doesn’t help because path imbalance dominates.
- Result: There is an optimal squeezing level that depends on how much loss you have in the entanglement path. More isn’t always better.
3) Realistic experiments still show a quantum advantage
Using numbers from real microwave setups (including component losses and amplifier noise), the authors find that teleportation fidelities can beat the “classical” limit (1/2) under realistic conditions—like several decibels of loss and temperatures up to liquid helium. With careful settings, even room‑temperature feedforward lines can be tolerated.
- Practical limit: The measurement devices (Josephson parametric amplifiers, JPAs) have maximum gain and add some gain‑dependent noise. There’s a sweet spot where you get the best fidelity.
4) Finite codebooks change the “no‑cloning” security threshold
The classic no‑cloning threshold (average fidelity > 2/3) applies when the message can be anywhere in an infinite plane. Real messages must be limited to a finite energy. When the codebook is smaller (especially “truncated Gaussian” or “truncated uniform”), the best possible cloning by an eavesdropper gets better, raising the threshold Bob must beat to be sure he’s more accurate than the eavesdropper.
- Result: The no‑cloning threshold depends on the codebook’s size and shape. For very small codebooks, the threshold can approach 1 (meaning even tiny errors matter). For large codebooks, it approaches the usual 2/3.
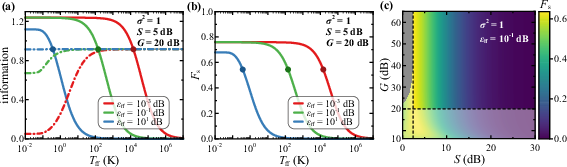
5) Security against a public‑channel eavesdropper can have a different threshold
If an eavesdropper can only access the public feedforward channel—while the entanglement path stays private—the condition for security changes. The authors define a secure fidelity threshold, Fs, based on comparing how much information Alice and Bob share versus how much the eavesdropper could learn.
- Result: In the limit of very strong measurements and strong entanglement, the minimal squeezing needed for security against this public‑channel attacker is about 2.39 dB. The corresponding secure fidelity threshold is lower than the usual 2/3 when entanglement increases (because stronger private correlations favor Alice and Bob). In short, the “safe” fidelity for this kind of attacker can differ a lot from the classic no‑cloning number.
Why This Matters
- For quantum networks based on superconducting circuits, microwave teleportation is a key tool for connecting distant processors without sending fragile quantum states directly through noisy lines.
- The paper shows you can make teleportation robust by adjusting the measurement gain and coupling, especially when dealing with the public feedforward channel. This means short‑range, even open‑air or warmer environment microwave links could be practical.
- It also clarifies how to think about security in the real world. The right security threshold depends on the codebook and on what channels an eavesdropper can actually access. Designers of quantum communication systems should use the adjusted thresholds (not just the textbook 2/3) to judge whether their systems are truly secure.
- Overall, the work points to practical, secure quantum communication over microwaves, helping pave the way for scalable, distributed quantum computing and future quantum networks.
Knowledge Gaps
Knowledge gaps, limitations, and open questions
Below is a concise list of missing, uncertain, or unexplored aspects that future work could address to strengthen and generalize the paper’s conclusions.
- Lack of experimental validation of key theoretical claims:
- No direct experimental demonstration of error correction via feedforward gain for thermal feedforward channels at varying temperatures and losses.
- Absence of experimental tests of modified no-cloning thresholds for truncated codebooks (uniform and Gaussian).
- No empirical verification of secure fidelity thresholds under public-channel eavesdropper models.
- Security model limitations and missing proofs:
- Security is analyzed only against a public feedforward-channel eavesdropper; attacks on the entanglement distribution channel, side channels, and device-level vulnerabilities (e.g., Trojan-horse, detector blinding, pump leakage) are not considered.
- No composable, finite-size security proof; the fidelity thresholds are not mapped to provable secret key rates under general (coherent) attacks.
- The claim that, for genuine teleportation with large gain, the security condition depends only on SNR and is independent of codebook shape lacks a formal proof and counterexample analysis.
- Non-Gaussian eavesdropping strategies beyond entangling cloners are mentioned but not rigorously excluded; the sufficiency of feedforward statistics to rule them out is not formally established.
- Incomplete treatment of truncated codebooks in security analysis:
- The paper does not provide secure fidelity thresholds (Fs) for truncated codebooks under public-channel eavesdropper models; the final discussion is truncated and lacks quantitative results.
- No analytic bounds or closed-form expressions for no-cloning thresholds of truncated distributions; only numerical estimates are given without performance guarantees across parameter ranges.
- No optimization framework for selecting codebook variance σ and cutoff N to jointly maximize throughput and security under energy constraints and hardware limits.
- Hardware and implementation uncertainties:
- Quantitative trade-offs between JPA gain, compression, added noise, and output purity are not modeled; guidelines to optimize G and η in practice are missing.
- Effects of phase noise, pump phase instability, timing jitter, finite bandwidth, and mode mismatch (temporal/spectral) on teleportation fidelity and security are not analyzed.
- Impact of calibration errors and drift (e.g., imperfect displacement matching Gη(1−εff)=4 over time) on fidelity and security margins is not assessed; adaptive gain/η tuning strategies are not proposed.
- The SU(1,1) interferometer’s measurement-device-free regime is assumed to approximate projective measurements at high gain, but its robustness and limitations (e.g., nonlinearity, gain saturation) are not quantified.
- Channel modeling gaps:
- Thermal noise is treated as stationary, Markovian, and white; colored noise, non-Markovian effects, and realistic open-air microwave channel impairments (multipath, atmospheric absorption, interference) are not modeled.
- Entanglement distribution losses are deemed uncompensable by simple amplification/attenuation, but the potential of entanglement distillation, purification, error correction, or asymmetric resource engineering is not explored.
- No distance, latency, or bandwidth scaling analysis for feedforward and entanglement channels; practical constraints on distributed quantum computing use-cases are not quantified.
- Protocol-level outcomes and performance metrics:
- Teleportation fidelity is used as the primary metric; links to symbol error rates, achievable (secret) communication rates, and capacity under finite energy and hardware constraints are absent.
- The relation between average fidelity thresholds and operational key rates with reconciliation and privacy amplification steps (including finite-size, error-correction overheads) is not derived.
- The assertion that feedforward imperfections can be “completely corrected” via small η ignores practical constraints on minimum η due to JPA gain limits, stability, and insertion losses; residual noise floors and their impact on Fs are not quantified.
- Generality and scope of input states and codebooks:
- Analysis is limited to coherent-state input ensembles; extensions to non-Gaussian states (e.g., squeezed, cat states) and their codebooks are not explored, despite potential security/fidelity advantages.
- Only Gaussian and truncated Gaussian/uniform codebooks are considered; practical discrete constellations (e.g., PSK/QAM, lattice codes) and optimal finite-energy ensembles are not analyzed.
- Analytical gaps in finite-gain regimes:
- Secure fidelity Fs is derived analytically only in asymptotic limits (G→∞); closed-form expressions or tight bounds for finite G, εff, and Tff are missing.
- Dependence of Fs on measurement-device imperfections, finite squeezing purity, and asymmetric TMS path losses (beyond the simple εent constraint) is not fully characterized.
- Resource optimization under asymmetric losses:
- The optimal squeezing condition εent cosh²(2r)=1 is presented, but the paper does not propose strategies for asymmetric resource allocation, multi-mode balancing, or active compensation schemes to recover performance at higher S.
- No exploration of network-level resource scheduling (e.g., entanglement swapping, multi-link balancing) to mitigate entanglement distribution bottlenecks.
- Practical deployment considerations:
- Feasibility of open-air microwave teleportation is claimed but not supported by propagation models, regulatory constraints, antenna design, and realistic environmental noise/interference analyses.
- Thermal constraints (e.g., superconducting cable critical temperature) are stated without practical workarounds (e.g., cryogenic feedforward repeaters, hybrid optical–microwave transduction).
- Reproducibility and benchmarking:
- The comparison to Ref. Yam 2025 is qualitative; comprehensive benchmarking with error bars, uncertainty budgets, and sensitivity analyses across components (JPAs, beam splitters, attenuators, cables) is missing.
- Standardized experimental protocols to validate security thresholds (Fs) and no-cloning limits under controlled adversarial conditions are not provided.
Practical Applications
Immediate Applications
The following items translate the paper’s findings into deployable uses, with sector links and feasibility notes.
- Robust microwave teleportation links inside cryogenic labs and quantum computing racks
- What: Use the displacement-matching rule G·η·(1−ε_ff)=4 and small coupling η to suppress public feedforward noise while compensating feedforward loss with gain, keeping fidelities above classical and, in many cases, no-cloning thresholds.
- Sectors: hardware (superconducting quantum computing), research labs.
- Tools/workflows: “Teleportation link budget” calculators; auto-calibration routines that measure ε_ff and tune G and η; real-time fidelity monitors.
- Assumptions/dependencies: Low-loss entanglement distribution at cryogenic temperatures; JPAs with sufficient gain and stability; ability to measure channel loss/noise; coherent-state inputs.
- Security assessment of teleportation links under public feedforward attacks
- What: Compute secure fidelity thresholds F_s(S,G) to decide minimum squeezing and gain (e.g., S≥2.39 dB for projective limit) to ensure I(A:B)>χ_E against any feedforward eavesdropper.
- Sectors: security, policy, hardware.
- Tools/workflows: “Squeezing-aware security profiler” that ingests measured S, G, ε_ff, T_ff and outputs required operating window; compliance dashboards.
- Assumptions/dependencies: Threat model where entanglement distribution is private; Gaussian attack model; calibrated squeezing and measurement gain.
- Codebook-aware security benchmarking and test generation
- What: Use derived no-cloning thresholds F_nc(σ,N) for finite-energy (truncated) codebooks to set acceptance criteria and design energy-feasible alphabets.
- Sectors: standards/certification, R&D, software tooling.
- Tools/workflows: “Finite-codebook designer” that selects (σ,N) to meet energy budgets and target F_nc; conformance tests using truncated distributions.
- Assumptions/dependencies: Eavesdropper knows the codebook; cloning attack modeled via entangling cloner; coherent-state modulation.
- Optimal squeezing selection under asymmetric losses
- What: Apply ε_ent·cosh2(2r)=1 to pick an optimal squeezing S for a given entanglement-path asymmetry, avoiding over-squeezing that degrades fidelity.
- Sectors: engineering (network and system design), hardware.
- Tools/workflows: “S vs loss” planner embedded in system bring-up scripts; design rules-of-thumb for cryostat cabling and components.
- Assumptions/dependencies: Accurate ε_ent estimation; accessible squeezing control; path imbalance known.
- JPA operating point optimization for high-fidelity teleportation
- What: Balance measurement gain versus gain-dependent noise/compression to maximize fidelity under realistic constraints.
- Sectors: hardware (amplifier vendors, integrators), research labs.
- Tools/workflows: “JPA tuner” that characterizes noise vs gain and recommends setpoints; automated compression checks.
- Assumptions/dependencies: Device characterization access; reproducible JPA behavior across thermal cycles; availability of narrowband/wideband paramps.
- Room-temperature tolerant feedforward engineering
- What: Use weak coupling η (e.g., ≈−24 dB) and high gain to maintain quantum advantage even when the public feedforward line is at elevated temperature.
- Sectors: hardware integration, facilities engineering.
- Tools/workflows: Design guides that separate cold entanglement paths from warm feedforward infrastructure; attenuation planning.
- Assumptions/dependencies: Adequate maximum gain; stable displacement-matching; feedforward path characterized.
- Curriculum and testbeds for practical teleportation
- What: Teaching labs and demos that show finite-energy codebook effects, modified no-cloning thresholds, and public-channel security conditions.
- Sectors: education, academia.
- Tools/workflows: Open-source simulators implementing the paper’s covariance-matrix models; lab exercises for G–η calibration and fidelity/security mapping.
- Assumptions/dependencies: Access to simulation tools or small-scale JPA setups; simplified lab hardware.
- Cross-platform adoption in optical CV experiments
- What: Port finite-energy codebook analysis and security thresholds to optical CV teleportation/QKD where infinite Gaussian alphabets are impractical.
- Sectors: photonics, telecom R&D.
- Tools/workflows: Optical teleportation planners with truncated alphabet support; protocol parameter checkers.
- Assumptions/dependencies: Gaussian-state operations; analogous loss/noise models; phase-space modulation control.
Long-Term Applications
These items require further research, scaling, or ecosystem development before broad deployment.
- Distributed superconducting quantum computing across racks/rooms via microwave teleportation
- What: High-fidelity, loss-robust teleportation to entangle or move states between modules, enabling modular architectures.
- Sectors: quantum computing.
- Potential products: “Teleportation backplane” modules; inter-cryostat quantum links; rack-level quantum network switches.
- Assumptions/dependencies: Stable multi-cryostat entanglement distribution at low loss; scalable squeezers (10–20 dB) with low added noise; precision synchronization.
- Microwave CV-QKD with finite-energy codebooks
- What: Use truncated alphabets and F_s-based security to realize secure key distribution in short-range microwave settings (e.g., inter-lab, in-building).
- Sectors: telecom/security.
- Potential products: Microwave QKD appliances; codebook-aware key distillation stacks.
- Assumptions/dependencies: Protocol adaptations for microwaves; privacy amplification/sifting integrated with teleportation; regulatory acceptance.
- Short-range open-air microwave quantum links
- What: Secure, line-of-sight microwave teleportation for campus-scale or facility-internal links leveraging feedforward-noise tolerance.
- Sectors: defense, industrial campuses, research facilities.
- Potential products: Open-air microwave quantum terminals; alignment and channel-compensation systems.
- Assumptions/dependencies: Characterized atmospheric channel at target bands; robust entanglement distribution (likely still cryogenic endpoints); interference management.
- Turnkey teleportation subsystems
- What: Packaged SU(1,1) measurement engines, entanglement sources, and control software as drop-in modules for OEMs.
- Sectors: hardware manufacturing, system integration.
- Potential products: “Teleportation-on-a-card”; cryo-compatible beam-splitter/displacer assemblies; embedded security analyzers.
- Assumptions/dependencies: Component standardization; compact, reliable parametric amplifiers (e.g., JTWPA-based); automated calibration.
- Secure control planes for quantum data centers
- What: Use teleportation to protect command-and-control channels between quantum accelerators and orchestration layers within facilities.
- Sectors: cloud/data center, security.
- Workflows: Microservice APIs that negotiate operating points (S,G,η) and continuously verify fidelity and security margins.
- Assumptions/dependencies: Networked cryostats; seamless classical–quantum orchestration; monitoring infrastructure.
- Networked quantum sensing at microwave frequencies
- What: Teleportation-assisted networking of cryogenic sensors (e.g., dark-matter detectors, superconducting magnetometers) for correlated measurements.
- Sectors: sensing, fundamental physics, healthcare (future cryogenic diagnostics).
- Potential workflows: Time-synchronized entanglement distribution; fidelity-aware sensor fusion.
- Assumptions/dependencies: Shared low-loss links; precise timing; robust long-duration squeezing.
- Standardization and certification programs for practical quantum teleportation
- What: Sector-wide benchmarks that incorporate finite-energy codebooks (F_nc(σ,N)) and public-channel secure fidelity F_s(S,G).
- Sectors: policy/standards, certification bodies, procurement.
- Outputs: Profiles for “public-channel-only” vs “full adversary” threat models; minimum squeezing requirements; channel-loss classes.
- Assumptions/dependencies: Community consensus; interop testbeds; regulatory alignment for microwave spectrum usage.
- Hybrid microwave–optical quantum networks
- What: Bridge microwave teleportation inside cryostats with optical carriers over distance, leveraging finite-codebook security analysis across both domains.
- Sectors: telecom, quantum internet R&D.
- Potential products: Transducers with teleportation-aware control; cross-domain security toolchains.
- Assumptions/dependencies: High-efficiency, low-noise microwave–optical transduction; coordinated parameter optimization across layers.
Notes on feasibility across applications:
- Many benefits hinge on keeping the entanglement-distribution channel cold and low-loss; feedforward can tolerate higher temperature if η is small and G is sufficient.
- JPAs (or next-gen paramps) are critical components; compression and gain-dependent noise must be managed.
- Security outcomes depend on accurate modeling of codebooks and threat models; classical post-processing (sifting, error correction, privacy amplification) is assumed where relevant.
- While the analysis is carrier-agnostic, microwave deployment faces materials and thermal constraints not present in optics; conversely, optical deployment must still respect finite-energy codebooks and threat-model changes.
Glossary
- Analog CV quantum teleportation: A teleportation protocol that uses continuous-variable states and analog (classical) feedforward signals to reconstruct quantum states at a remote node. "Here, we focus on an analog CV quantum teleportation scheme with an input codebook formed by coherent states~\cite{DiCandia2015}."
- Asymptotic classical threshold: The maximum average fidelity achievable without entanglement for an unbounded coherent-state codebook. "an infinitely large codebook of coherent states gives the asymptotic classical threshold fidelity "
- Asymptotic no-cloning threshold: The fidelity bound above which unconditionally secure communication is possible against optimal cloning when using an unbounded coherent-state codebook. "unconditionally secure communication is achieved if an average teleportation fidelity exceeds the asymptotic no-cloning threshold "
- Balanced beam splitter: A 50:50 linear optical/microwave element that mixes two modes with equal splitting ratio. "superimposing two orthogonally squeezed states with a squeezing level at a balanced beam splitter."
- Bell-type measurement: A joint measurement that extracts correlated information suitable for teleportation by projecting combinations of input and entangled modes. "Alice performs a Bell-type measurement operation on an input code state superimposed with her part of the entangled state."
- Codebook: The probability distribution or ensemble from which communication states are drawn in a protocol. "The input states are drawn from an ensemble of code states. The latter forms a certain codebook, which is represented by a truncated Gaussian distribution in this particular scheme."
- Coherent state: A minimum-uncertainty quantum state characterized by a complex phase-space displacement. "Every input quantum state to be teleported is assumed to be a pure coherent state with a complex displacement amplitude ."
- Conjugate quadrature measurements: Simultaneous measurement of orthogonal field quadratures (e.g., p and q) used in continuous-variable protocols. "The Bell-type measurement operation by Alice consists of conjugate quadrature measurements."
- Continuous-variable (CV): A quantum information framework encoding information in continuous quadratures of bosonic modes. "Originally, quantum teleportation was demonstrated at optical carrier frequencies in both discrete-variable~\cite{Bouwmeester1997} and continuous-variable (CV) regimes~\cite{Furusawa1998}."
- Covariance matrix formalism: A Gaussian-state representation using first and second statistical moments of quadrature operators. "we can apply the covariance matrix formalism in the phase space spanned by electromagnetic field quadratures "
- Degenerate gain: Phase-sensitive amplification in which the signal and idler coincide, yielding high gain for a selected quadrature. "in the limit of a high JPA degenerate gain "
- Displacement-matching condition: A gain/coupling constraint ensuring the teleported output displacement equals the input displacement. "Satisfying this displacement-matching condition allows the output state displacement to match the input state displacement."
- Displacement operation: A unitary phase-space translation that shifts the quadrature means of a mode. "The unitary operation by Bob is a displacement operation in phase-space defined by the feedforward signal."
- Displacement photon number: The mean photon number associated with the coherent-state amplitude |α|2. "for higher displacement photon numbers ."
- Entanglement distribution channel: The physical link used to share entanglement between parties, whose loss and noise affect performance. "entanglement distribution channel losses and noise temperature "
- Entanglement resource: A pre-shared entangled state enabling teleportation or other quantum communication tasks. "using a shared entanglement resource and a classical feedforward~\cite{Bennett1993}."
- Entangling cloner: An optimal Gaussian cloning attack implemented with entangled ancilla modes. "can be achieved by an entangling cloner attack~\cite{Braunstein2001a}."
- EPR-type entanglement: Strong two-mode correlations characteristic of Einstein–Podolsky–Rosen states enabling near-perfect correlations of conjugate quadratures. "we have perfect, EPR-type, entanglement and the TMS variance covers the entire signal space"
- Feedforward channel: The classical communication link carrying Alice’s measurement outcomes to Bob for conditional operations. "Her measurement outcome, referred to as the feedforward, is transmitted to Bob through a corresponding lossy and noisy feedforward channel."
- Gaussian codebook: A codebook where coherent-state displacements are drawn from a Gaussian distribution. "as opposed to typical Gaussian codebooks with infinite tails."
- Gaussian operations: Linear optics and squeezing transformations that map Gaussian states to Gaussian states. "the analog coherent state teleportation protocol involves only Gaussian operations"
- Heaviside step function: A unit step function used to truncate distributions in phase space. "where is the Heaviside step function."
- Holevo quantity: An upper bound on the classical information accessible to an eavesdropper from a quantum ensemble. "the information accessible to Eve is bounded from above by the Holevo quantity "
- Josephson parametric amplifier (JPA): A superconducting nonlinear device used to generate squeezing and low-noise amplification at microwave frequencies. "produced by using superconducting Josephson parametric amplifiers (JPAs)~\cite{Fedorov2018}."
- Measurement-device-free scheme: A setup where effective measurements are realized via interferometric amplification rather than explicit detectors. "Such an approach is also known as a measurement-device-free scheme~\cite{Yamashima2025}."
- Mutual information: A measure of the shared information between two parties’ random variables or ensembles. "The information shared between Alice and Bob is characterized by their mutual information "
- No-cloning theorem: The principle that unknown quantum states cannot be copied perfectly. "Due to the no-cloning theorem, neither lost signal nor added noise in the entanglement distribution channel can be compensated for by a simple amplification or attenuation."
- No-cloning threshold: The maximum average fidelity achievable by an optimal eavesdropper’s cloning attack for a given codebook. "derive modified no-cloning thresholds as a function of the codebook configuration."
- One-time pad encryption: A classical cryptographic scheme with perfect secrecy, used here as an analogy for infinite-noise masking via maximal entanglement. "which is analogous to a one-time pad encryption~\cite{Schumacher2006,Brandao2012}."
- Phase space: The plane of conjugate quadratures (p, q) representing bosonic modes’ states. "phase space spanned by electromagnetic field quadratures "
- Privacy amplification: Post-processing that reduces an eavesdropper’s information to ensure secure keys/messages. "assuming appropriate sifting and privacy amplification steps"
- Projective quadrature measurement: An ideal measurement projecting onto quadrature eigenstates, achievable in the high-gain limit. "coincides with a projective quadrature measurement in the limit of a high JPA degenerate gain "
- Signal-to-noise ratio (SNR): The ratio of signal strength to noise level determining information throughput. "I(\mathrm{A}:\mathrm{B}) \sim \ln(1+\mathrm{SNR}),"
- Squeezing factor: The natural-log parameter r relating to the amount of quadrature squeezing. "r = S/20\ln(10) is the squeezing factor"
- Squeezing level: The squeezing strength expressed in decibels (dB). "superimposing two orthogonally squeezed states with a squeezing level at a balanced beam splitter."
- SU(1,1) nonlinear interferometer: An interferometric device using parametric amplification (rather than beam splitting) to perform joint quadrature measurements. "The Bell-type measurement can be implemented by using a SU(1,1) nonlinear interferometer, which consists of two balanced beam splitters that allow two JPAs to amplify orthogonal field quadratures with a measurement gain "
- Truncated Gaussian codebook: A Gaussian-distributed codebook restricted to a finite radius in phase space and renormalized. "The truncated Gaussian codebook is described by a Gaussian codebook with variance and a cutoff photon number , rescaled for normalization."
- Truncated uniform codebook: A uniform codebook limited to a finite disk in phase space. "The truncated uniform codebook is described by a cutoff photon number and is normalized to unit probability."
- Two-mode squeezed (TMS) vacuum state: An entangled Gaussian resource state generated by two-mode squeezing of vacuum. "the entanglement resource is a two-mode squeezed (TMS) vacuum state."
- TMS correlations: The strong inter-mode correlations characteristic of a two-mode squeezed state. "optimizing the interference between the TMS correlations of the two paths."
- Uhlmann fidelity: A measure of similarity (overlap) between quantum states, used here to assess teleportation performance. "using the Uhlmann fidelity~\cite{Weedbrook2012,Scutaru1998}"
- Von Neumann entropy: The quantum analogue of Shannon entropy quantifying a quantum state’s uncertainty. "H(\cdot) is the von Neumann entropy,"
Collections
Sign up for free to add this paper to one or more collections.