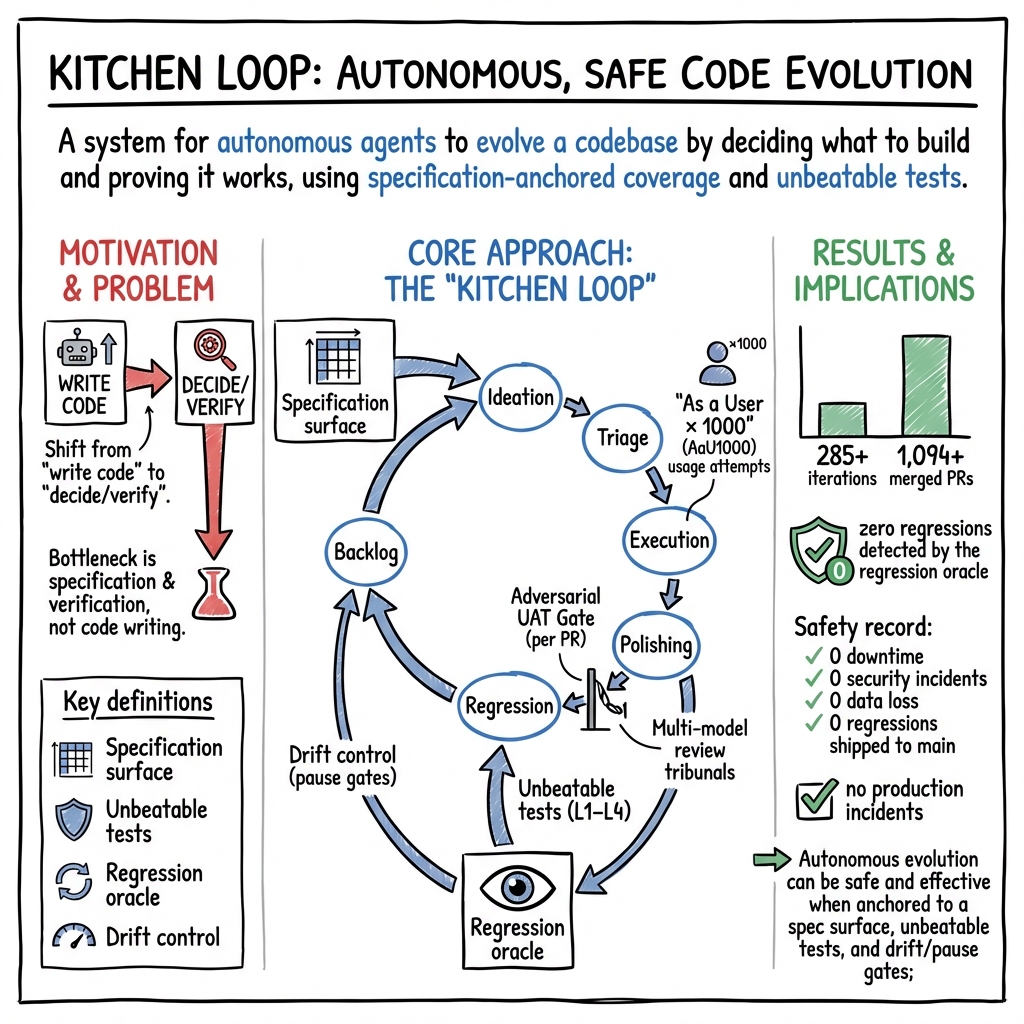
- The paper presents a six-phase Kitchen Loop that automates code evolution using user-specified verification and agent orchestration to shift the focus from code writing to precise specification.
- It employs a coverage-exhaustion testing model across foundational, compositional, and frontier tiers, achieving zero detected regressions and quality gate improvements from 76–91% to 100%.
- The framework demonstrates autonomous self-healing and meta-level improvements in production systems, validated in a DeFi context with over 1,094 merged PRs at an efficient cost of $0.38 per merge.
The Kitchen Loop: User-Spec-Driven Development for Autonomous Self-Evolving Codebases
Framework Overview and Core Contributions
The paper "The Kitchen Loop: User-Spec-Driven Development for a Self-Evolving Codebase" (2603.25697) presents a comprehensive system for autonomously evolving software based on specification-driven verification and agentic loop orchestration. The central premise is the commoditization of code production by LLM-based coding agents, shifting the bottleneck from code writing to specification articulation and verifiable correctness. The Kitchen Loop is structured around a six-phase improvement cycle: Backlog, Ideate, Triage, Execute, Polish, and Regress. Each phase is orchestrated by specialized AI skills operating against a unified trust model, which integrates a rigorous specification surface, unbeatable tests, regression oracle, and drift control mechanisms.
Figure 1: The Almanak SDK repository, exemplifying a production DeFi framework supporting 14 chains and 30+ protocol connectors.
This loop consistently yields robust results, demonstrated across two production systems with over 1,094 merged PRs and 285+ iterations, achieving zero detected regressions by the regression oracle, monotonically improving quality gates (76–91% to 100%), and highly efficient operation ($0.38$/PR merged).
Specification Surface and Coverage-Exhaustion Mode
The Kitchen Loop's pivotal innovation is shifting from task-completion paradigms (issue → patch) to coverage-exhaustion mode, systematically exercising the product's specification matrix—enumerating all feature, platform, and action type combinations. This ensures exhaustive validation rather than reactive patching. The loop's scenario generation employs a three-tier model:
- Foundation (T1, 30%): Tests basic, single-feature scenarios for critical baseline reliability.
- Composition (T2, 50%): Exercises multi-feature scenarios, targeting failures in combinatoric seams—superlinearly expanding coverage as the product matures.
- Frontier (T3, 20%): Identifies gaps and missing capabilities, producing actionable reports for next-generation features.
The self-expanding nature of this approach ensures that as new features are integrated, coverage grows not only linearly through foundational tests but superlinearly via composition scenarios, driving sustained product evolution.
Unbeatable Verification: Multi-Tier QA and Adversarial UAT
Correctness is established through a four-level testing pyramid:
- Unit Tests (L1): Isolated logic validation—rapid but low-trust.
- API/Adapter Tests (L2): Contract validation—medium trust.
- Integration Tests (L3): Pipeline verification against ground truth—high trust.
- End-to-End Scenario Tests (L4): Full user journey verification—highest trust.
A critical insight is the insufficiency of implementer-authored tests; adversarial UAT gates and cross-model review (Codex, Gemini, CodeRabbit) prevent green-check optimization and context leakage. Each PR is challenged by independent agents; implementer-written tests are never solely trusted. The regression oracle operates per-domain (e.g., demo strategies on Anvil forks for DeFi), running deterministic, bounded checks after every merge.
Anti-signal canaries (fabricated negative cases) further verify the efficacy of QA infrastructure, enforcing quality gates across four tiers of deceptiveness and ensuring resilience to environmental failures.
Drift Control, Pause Gates, and Operational Stability
The Kitchen Loop incorporates explicit drift control, monitoring quality metrics, test counts, bug discovery rates, and canary escape rates on a sliding-window basis. Automated pause gates respond to regression, backpressure, starvation, and drift thresholds, ensuring that the loop halts or warns operators when systemic degradation is detected. Drain mode and starvation gates are fully automated, maintaining operational stability and preventing runaway backlog growth or idle iteration.
Through this mechanism, the loop produces monotonically improving quality gates and confirms structural improvement trends (e.g., moving from partial to full canary capture rates over iterations).
Autonomous Self-Improvement and Loop Infrastructure Healing
A notable emergent property is meta-level self-improvement. The Kitchen Loop identifies and fixes its own infrastructure failures (e.g., merge automation bugs, memory allocation issues, cooldown phantoms) through standard loop cycles. The framework applies its own process to itself (“dogfooding”), demonstrating operational discipline and adaptability.
Case Study: DeFi Strategy Framework (Almanak SDK)
Validation is exemplified in the Almanak SDK, a production DeFi strategy framework:
- Specification matrix spans 14 chains, 30+ protocols, 21 intent types, yielding ~1,000 coverage combinations.
- Results: Over 122 loop iterations, 728+ merged PRs, 10,913 unit tests, 62 demo strategies.
- Security: No regressions introduced; critical bugs were discovered and fixed via coverage-exhaustion (e.g., router interface mismatches, silent reverts, missing native tokens).
- Infrastructure: The loop healed its own merge and state management failures, improving stability.
This confirms the scalability and reliability of the Kitchen Loop methodology, maintaining exhaustive verification as the system matures and expanding both breadth (chain/protocol coverage) and depth (intent diversity).
Implications for Agentic Software Engineering
Practically, the Kitchen Loop demonstrates that AI agents—when orchestrated with rigorous specification surfaces, unbeatable tests, and adversarial multi-model review—can autonomously evolve complex codebases with stringent production safety records. The human role moves to asynchronous specification design and backlog curation, not synchronous development or QA.
Theoretically, this reframes software engineering from productivity gains via code generation to structural advancements in specification-driven verification and autonomous evolution. The coverage-exhaustion regime mitigates common failure modes (local fix/global mismatch, Goodharting), and the framework supports broad generalization across domains where specification and regression oracles are enumerable.
Future Directions and Structural Limitations
The paper identifies several open problems: registry/transfer of regression oracles across domains, automated specification surface extraction from legacy codebases, multi-objective drift detection (including latency, security, fairness), and scaling sycophancy mitigation in larger multi-agent swarms. Additionally, parallelization beyond single-threaded execution and empirical validation in domains outside DeFi remain future work.
Adoption is bounded by oracle quality—the loop cannot catch failures not detectable by the regression oracle. Specification must be enumerable; exploratory or highly subjective domains lack the requisite structure.
Conclusion
The Kitchen Loop operationalizes a formal, specification-driven framework for safe autonomous evolution of software, emphasizing exhaustive coverage, unbeatable verification, and continuous quality trend monitoring. Across real deployments, it achieves high-throughput, low-cost, zero-regression evolution, structurally mitigating drift and operational failures. Its core claims—explicit coverage-based regime, adversarial UAT gates, multi-model tribunals, and compositional expansion—position it as a foundational architecture for agentic systems in domains where specification and verification can be rigorously defined. Practical adoption is immediate for domains with strong oracles and enumerable specifications; theoretical implications extend to the future evolution of automated software engineering.