- The paper presents new bounds on identification capacity under distortion constraints with noisy feedback in 6G systems.
- It introduces joint coding schemes using superposition and random hashing, effectively achieving both identification and state sensing.
- The analysis provides practical insights for enhancing control and inference in next-generation wireless networks.
Joint Identification and Sensing with Noisy Feedback: A Task-Oriented Communication Framework for 6G
Introduction and Context
Task-oriented communication, in contrast to classical communication paradigms, optimizes information transfer for supporting task execution and decision making rather than for message reconstruction. Emergent 6G applications such as autonomous systems, industrial automation, and machine-type coordination demand stringent requirements where actionable messages, rather than high-throughput data, are central. Identification (ID) coding, as developed by Ahlswede and Dueck, offers a binary hypothesis test for whether a given message was sent, embodying task-centric communication with unique asymptotic properties distinct from Shannon transmission coding. The incorporation of feedback, especially noisy feedback as encountered in practical wireless systems, plays a non-trivial role in ID — a departure from its ineffectual role in boosting classical channel capacity.
Simultaneously, the integration of sensing with communication in wireless systems underscores the need for co-design strategies aligning communication efficiency with state estimation accuracy, particularly in state-dependent channels where feedback is inevitably corrupted. The work "Joint Identification and Sensing with Noisy Feedback: A Task-Oriented Communication Framework for 6G" (2603.29649) develops non-asymptotic and asymptotic bounds for the identification capacity under distortion constraints, providing theoretical foundations for state-aware task-driven wireless system design under realistic (i.e., noisy) feedback.
The system is a state-dependent discrete memoryless channel (SD-DMC), with transition law W(y,z∣x,s), where the input X, output Y, feedback observation Z, and state S are finite-alphabet, discrete random variables. The encoder does not have access to the channel output Y but instead observes Z — a strictly causal, possibly noisy function of Y. The state sequence Sn is independent and identically distributed (i.i.d), and the system imposes a per-symbol distortion criterion on the transmitter's state estimate, operationalized via a distortion function d(s,s^).
Task-oriented communication is instantiated as identification codes: the receiver does not decode the message but answers whether a specific message index was sent, with both type I and II error probabilities vanishing in the limit. Both deterministic and randomized identification code paradigms are considered.
The main performance metric is the capacity–distortion function, characterizing the tradeoff between the achievable identification rates (in the doubly exponential regime) and the sensing distortion under noisy strictly causal feedback.
Main Results: Bounds on Capacity–Distortion
The core results consist of nontrivial lower and upper bounds for both deterministic (DIF) and randomized (RIF) identification codes with sensing, under noisy strictly causal feedback. These bounds depend on the noise statistics of the feedback, the underlying state process, and the distortion threshold.
For deterministic identification codes, the DIF capacity–distortion function is bounded by
X0
where X1 is the admissible input symbol set for which the average distortion constraint is met. If the underlying channel capacity is zero, the identification capacity with feedback is also zero.
For randomized codes, the RIF capacity–distortion function is bounded by
X2
where X3 is the set of input pmfs meeting the average distortion constraint.
Key assertions include:
- Noisy feedback fundamentally reduces the identification capacity compared to noiseless feedback, due to both reduced codebook common randomness generation and degraded state estimation performance.
- The bounds collapse to the noiseless-feedback case when the feedback channel is error free (X4).
Coding Theorems: Achievability and Converse
The achievability schemes employ superposition coding and structured generation of common randomness leveraging noisy feedback, followed by random hashing for message indexing. In both deterministic and randomized scenarios, reliable identification is guaranteed provided the code construction carefully aligns the rate of common randomness with the task-dependent (distortion) constraints.
The converse bounds utilize type-enumeration and regular-subcode arguments to show that any identification code must obey the mutual information constraint linking the input–feedback process and the output observation, under distortion.
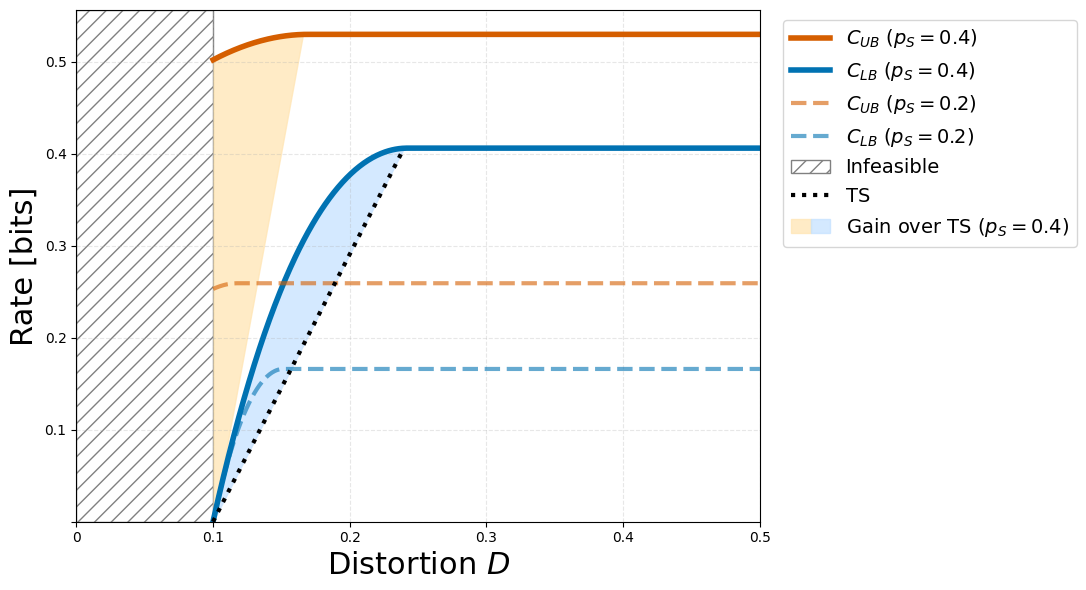
Numerical Example: Binary Channel Tradeoffs
A particular instantiation is considered: a binary state multiplicative channel with X5 and X6. With binary Hamming distortion and analytically tractable parameter regimes, the derived lower and upper bounds are evaluated against a time-sharing baseline. The results indicate a strictly positive capacity–distortion region wherein the proposed JIDAS co-design approach outperforms naïve time-sharing. Notably, increasing feedback noise (X7) diminishes the performance gap, highlighting the nuanced interplay between feedback noise and identification–sensing tradeoff.
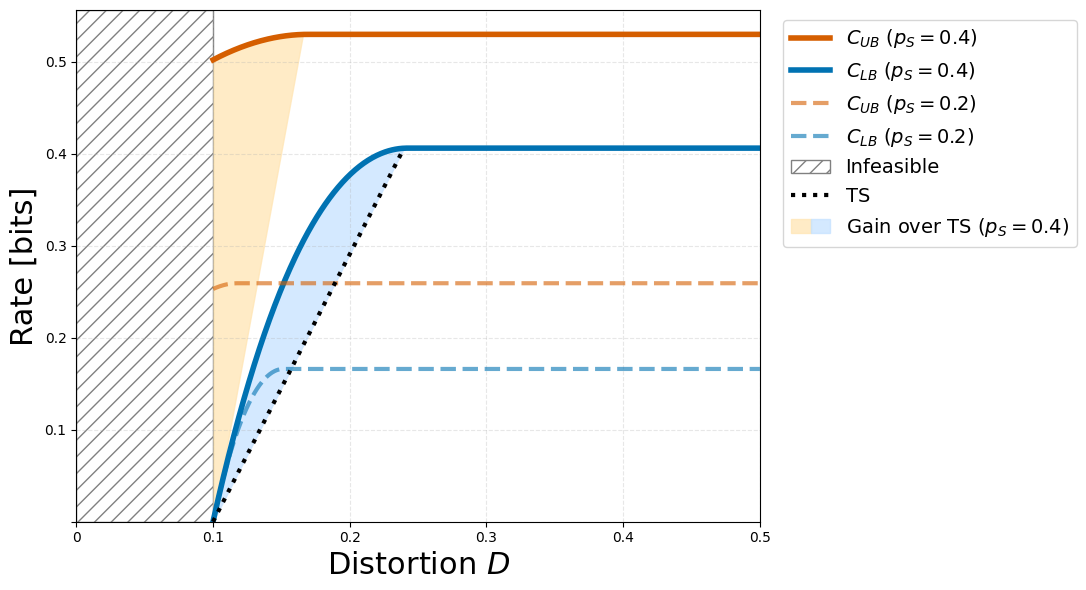
Figure 1: Lower and upper bounds on the capacity–distortion function X8 for X9 in the binary example; JIDAS outperforms conventional time sharing.
Theoretical and Practical Implications
The results rigorously delineate the role of strictly causal, noisy feedback in 6G-oriented task-driven physical-layer systems, clarifying both the limits and operative regimes for identification and state sensing co-design. They generalize the noiseless feedback paradigm, firmly rooting the framework in more realistic feedback environments.
Practically, such a characterization undergirds the design of closed-loop wireless systems for control, autonomy, and collaborative inference, tightly coupling perception and communication objectives—a foundational requirement for next-generation communication-control systems.
Theoretically, the identification–sensing framework exposes new operating points for wireless information theory, stimulating new research at the interface of random coding, feedback communication, rate–distortion theory, and action-oriented system design.
Future Directions
Several non-trivial research avenues emerge:
- Identifying parametric or structural conditions under which the presented lower and upper bounds coincide, i.e., capacity–distortion optimality.
- Extending the analysis to rate-limited or delayed feedback scenarios, which are ubiquitous in practical control and edge intelligence networks.
- Generalizing results to non-discrete (e.g., Gaussian or finite blocklength) channels, multiuser/multiaccess identification–sensing scenarios, and quantum communication frameworks.
Conclusion
The paper establishes a comprehensive information-theoretic foundation for joint identification and sensing in state-dependent channels with noisy feedback, enabling a precise understanding of the identification–sensing tradeoff relevant for 6G and beyond. Both achievability and converse bounds are developed, and the operational implications for task-oriented communication system design are elucidated. The integration of feedback noise considerations marks a critical advance in the theory and practice of wireless communication for control and inference (2603.29649).