- The paper introduces two novel classes of social engineering attacks—address manipulation and homograph deception—that exploit human cognitive biases.
- It evaluates the practical feasibility by analyzing 85,656 open-source smart contracts and highlights vulnerabilities in popular tokens like Tether USD.
- The study recommends human-centered defense strategies, emphasizing visual verification and audit measures to counter non-code based security threats.
Targeting the Weakest Link: Social Engineering Attacks in Ethereum Smart Contracts
Introduction to Social Engineering Attacks in Ethereum
The paper investigates novel security threats against Ethereum smart contracts, focusing on social engineering attacks exploiting human cognitive biases instead of technical vulnerabilities. Unlike the well-known code-centric attacks, such as reentrancy and integer overflow, these social engineering attacks target the "human factor" associated with the system, which often remains unguarded. The authors describe how these attacks can deceive users into erroneous interactions with smart contracts, leading to potential financial losses.
Social engineering within smart contracts leverages elements such as address manipulation and homographic deception, which exploit visual cognitive biases and preconceived notions about the blockchain. The study introduces two novel classes of social engineering attacks: Address Manipulation and Homograph, along with six specific attack vectors. The paper challenges existing assumptions about smart contract security and reveals vulnerabilities that arise not from the contracts themselves, but from erroneous human interpretations.
Address Manipulation Attacks
Address manipulation relies on deceiving users regarding the nature and role of Ethereum addresses. These attacks exploit several misconceptions, such as the assumptions of immutability and their association to either EOAs or smart contracts:
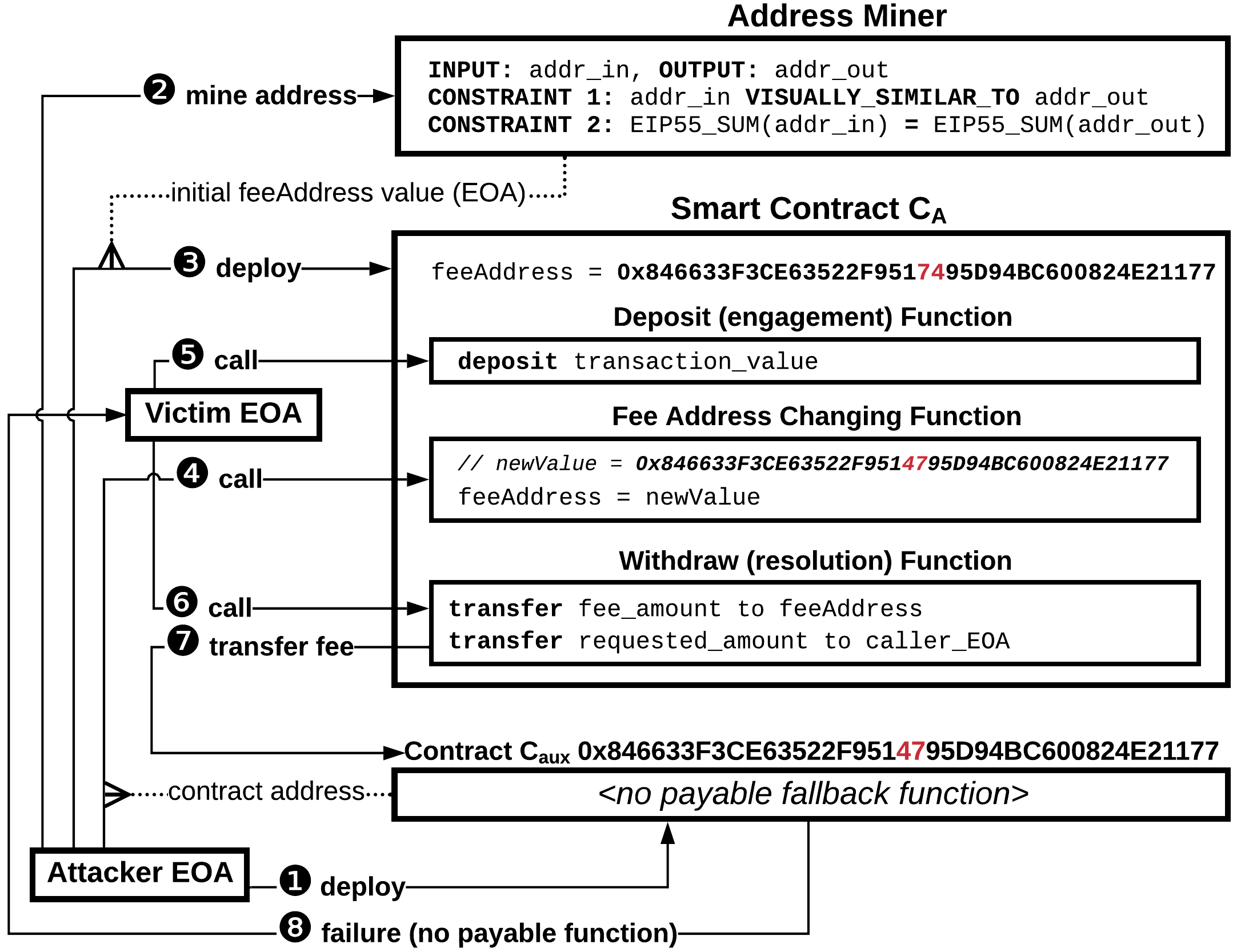
- Attack Ⅰ: This attack involves substituting an apparent EOA address with a smart contract address lacking a payable fallback function, causing transaction failures and blocking fund withdrawals by the user. The manipulated address remains seemingly similar to the original, leveraging cognitive bias that validates addresses on a visual basis.
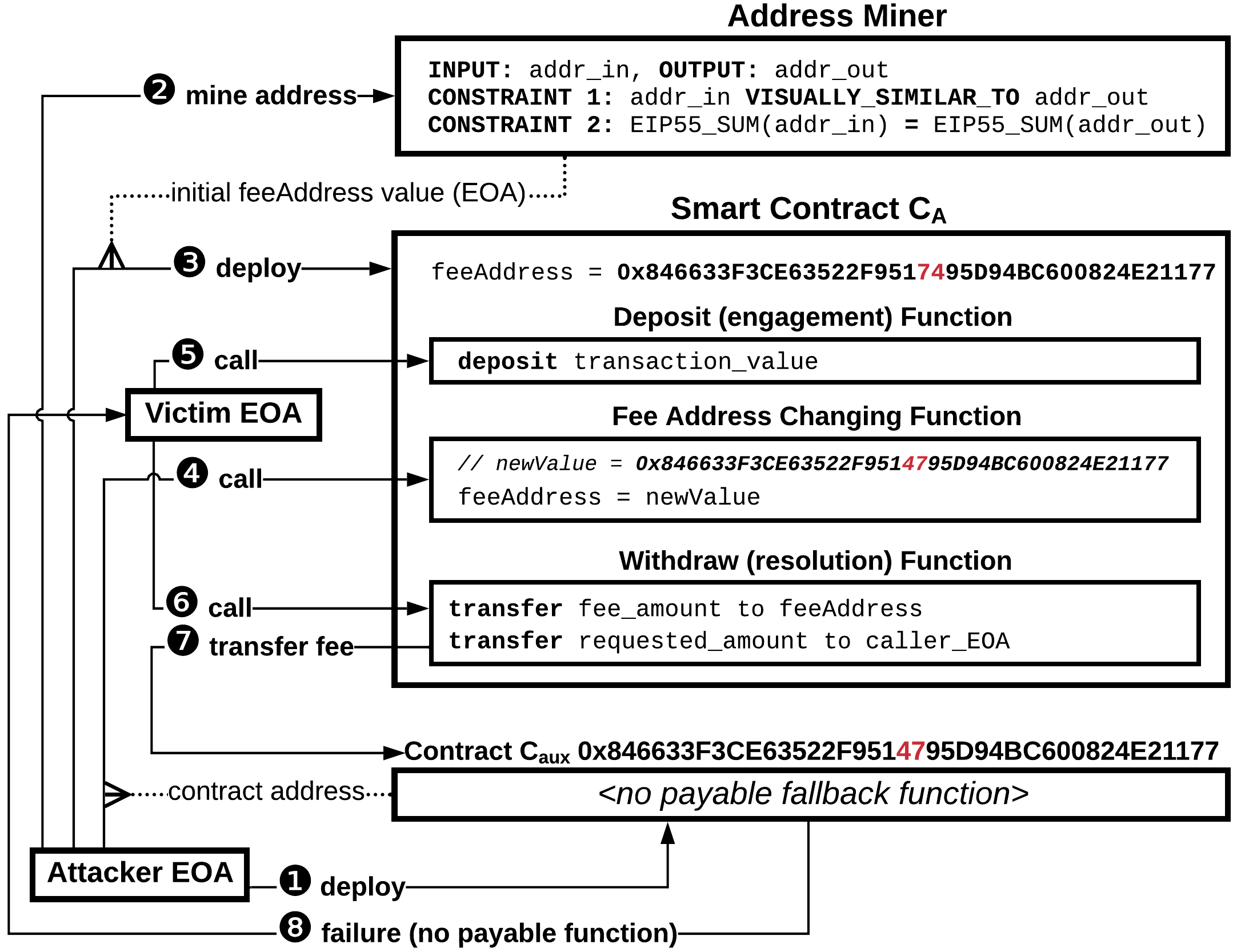
Figure 1: Attack $\ workflow.</p></li>
<li><strong>Attack Ⅱ:</strong> Here, the attacker pre-calculates the address where a future smart contract will be deployed, and dynamically changes the reference from an EOA to the contract without the user's realization. The methodology exploits the deterministic nature of Ethereum address generation.
<img src="https://emergentmind-storage-cdn-c7atfsgud9cecchk.z01.azurefd.net/paper-images/2105-00132/a2-slim1.png" alt="Figure 2" title="" class="markdown-image" loading="lazy">
<p class="figure-caption">Figure 2: Attack $\ workflow.
- Attack Ⅲ: By targeting accounts with lowercase EIP-55 checksums, this attack capitalizes on unverified assumptions of uniform security across Ethereum accounts despite checksum cases. This deceives users during identification checks which, when mistaken, result in transaction reversals.
The paper outlines computational feasibility for the generation and exploitation of addresses with lowercase EIP-55 checksums and illustrates its practical application.
Homograph Attacks
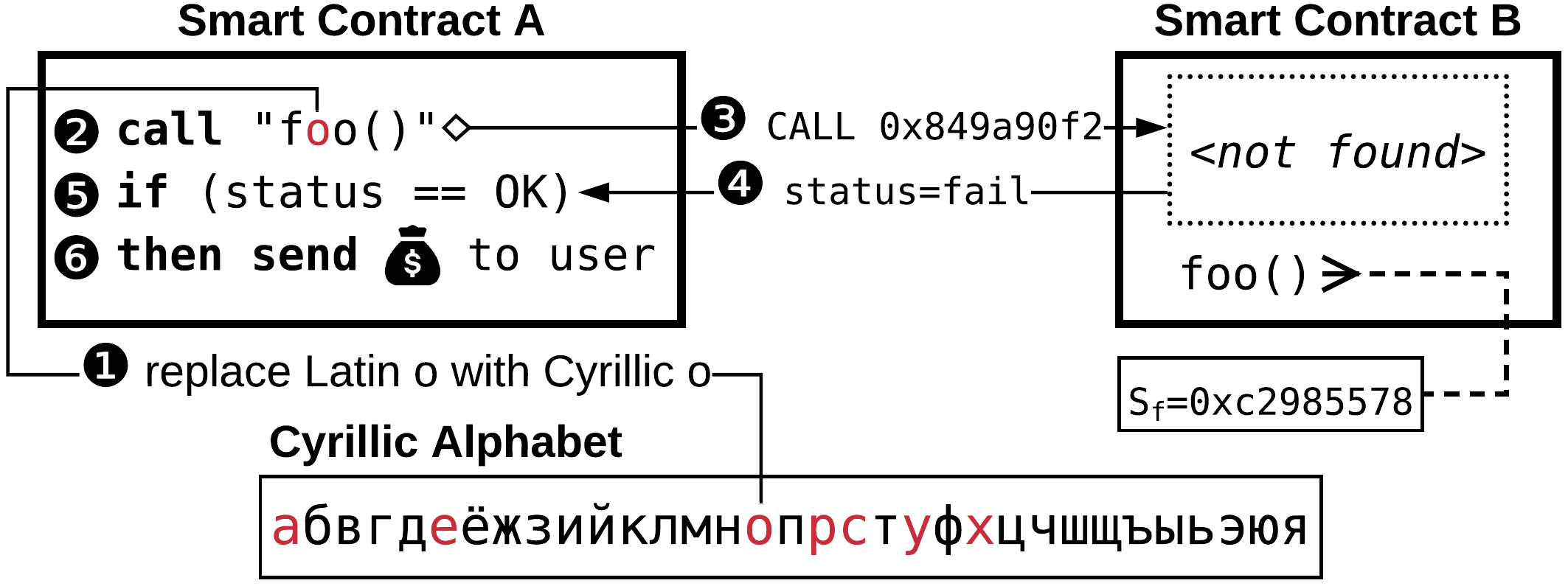
Homograph attacks take advantage of identical-looking Unicode symbols within smart contract strings:
Practical Evaluation of Social Engineering Attacks
To evaluate the practical feasibility of these attacks, the authors examine five widely used smart contracts (Table 1), such as Tether USD and Binance Token. By embedding attack patterns within existing and popular smart contract source codes, the study demonstrates that these manipulations can go undetected during testing phases and activate unpredictably in production environments.
The authors further analyze 85,656 open-source smart contracts, discovering 1,027 contracts potentially vulnerable to social engineering attacks.
Defense Strategies and Recommendations
The paper provides practical recommendations for human-centered prevention of social engineering attacks, emphasizing the importance of audit measures like: visual double-checks of Ethereum addresses, rejecting contracts employing dynamic address changes, and employing hex viewers to verify ICC call arguments, especially in contexts that involve string manipulation and comparisons.
Conclusion
Social engineering attacks in the Ethereum ecosystem highlight the necessity of integrating human-centered security evaluations alongside technical audits. This work calls for a shift in emphasis from purely identifying code vulnerabilities to addressing the broader spectrum of cognitive biases in blockchain interactions, ensuring a more robust security paradigm in decentralized finance systems.