- The paper introduces a robust detection system that identified 270 million attack attempts and revealed an attack scale 13 times larger than earlier estimates.
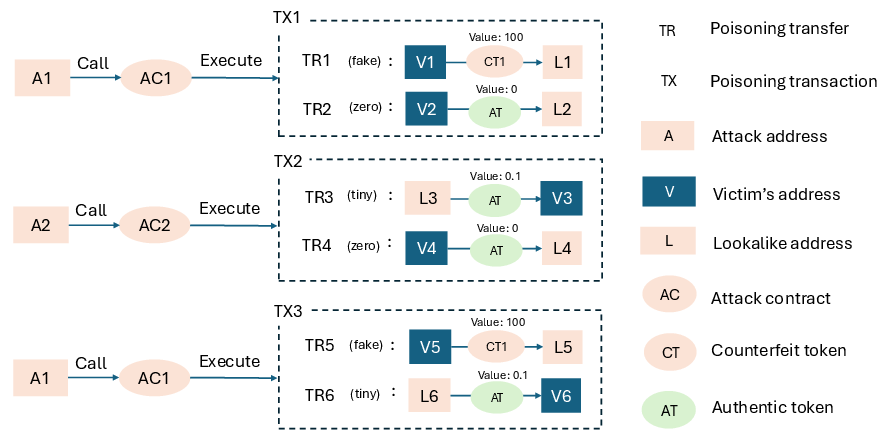
- The paper analyzes sophisticated attacker strategies, including tiny, zero-value, and counterfeit token transfers, using lookalike addresses to mislead users.
- The paper proposes defensive measures at protocol, wallet, and user interface levels to mitigate phishing risks in cryptocurrency transactions.
Blockchain Address Poisoning
Abstract
The paper "Blockchain Address Poisoning" (2501.16681) investigates a novel attack vector in cryptocurrency transactions where adversaries exploit the memorability issues associated with blockchain wallet addresses. The study focuses on blockchains such as Ethereum and Binance Smart Chain (BSC), where addresses typically consist of 40-digit hexadecimal strings. This complexity often leads users to rely on their transaction history, making them susceptible to address poisoning attacks. The adversary generates addresses visually similar to those the victim has interacted with, thus misleading them into sending tokens to incorrect addresses.
Detection System and Measurement
The paper introduces a robust detection system evaluated over two years, identifying a staggering 270 million attack attempts that affected approximately 17 million victims. Notably, 6,633 of these incidents resulted in losses exceeding 83.8 million USD, establishing blockchain address poisoning as one of the most significant phishing schemes in cryptocurrency history. The study’s detection methodology surpasses previous efforts, revealing attack scopes 13 times greater than reported earlier (2501.16681).
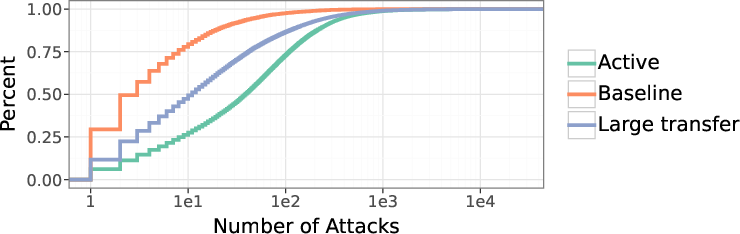
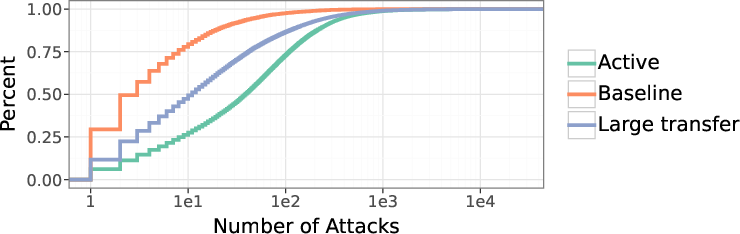
Figure 1: CDF showcasing the targeting intensity, highlighting more aggressive targeting in 'active' groups.
Attack Analysis and Strategies
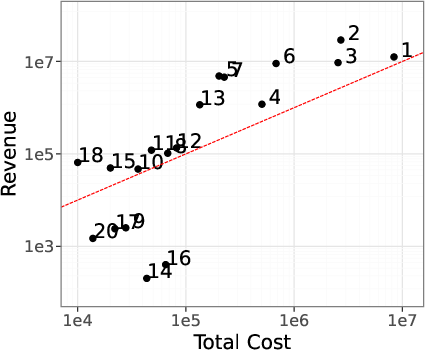
The analysis covers three specific transfer types—tiny transfers, zero-value transfers, and counterfeit token transfers—that adversaries use to infiltrate transaction histories. The paper uncovers a detailed picture of attacker operations, including bundling multiple transfers, address reusability, and cross-chain targeting. Attack profitability was explored by modeling attacker revenues and losses across distinct groups, revealing some structured entities managing consistently profitable operations.
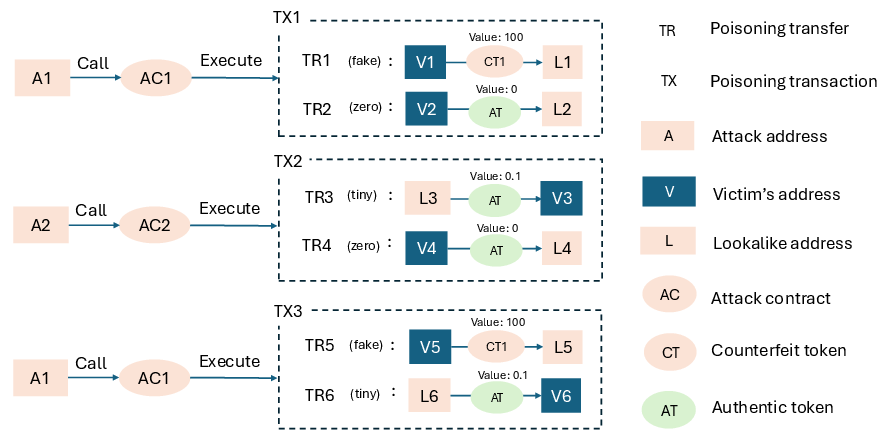
Figure 2: Illustration of the attack mechanism demonstrating the transfer poisoning strategy.
Technical Capacities and Simulation
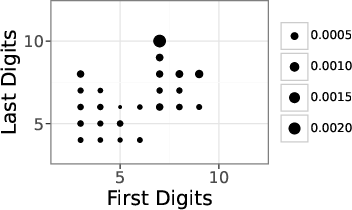
The researchers mathematically defined and simulated lookalike address generation techniques, observing varied attack capacities. They found evidence suggesting large-scale attackers employ GPUs, significantly bolstering the address generation rate compared to CPU-based operations.
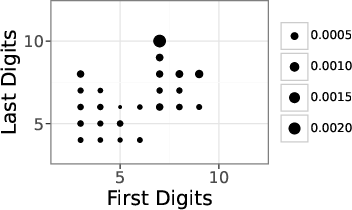
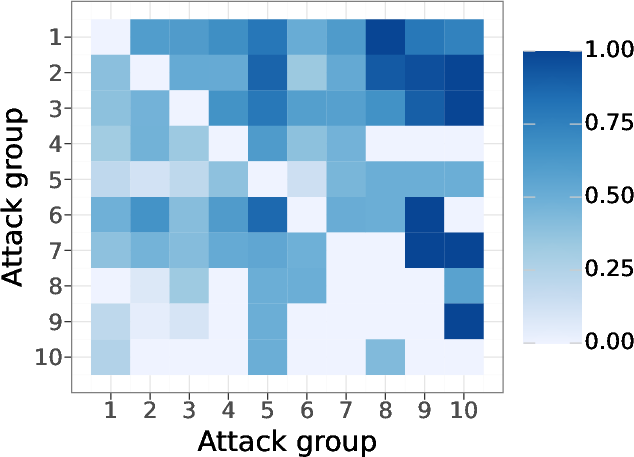
Figure 3: Success probability correlated to address similarity, emphasizing strategic address selection.
Implications and Future Directions
The paper’s findings have significant implications for blockchain security, particularly in designing user interfaces and transaction protocols to minimize human error and enhance address verification mechanisms. The authors propose several defensive measures spanning protocol, contract, wallet, and user-level solutions to mitigate the risks posed by address poisoning attacks.
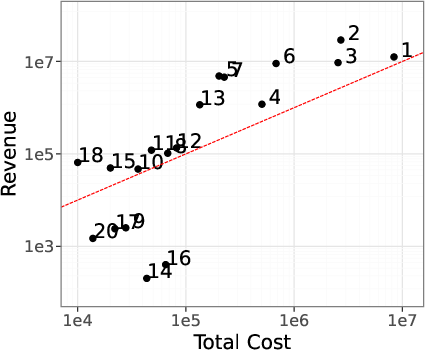
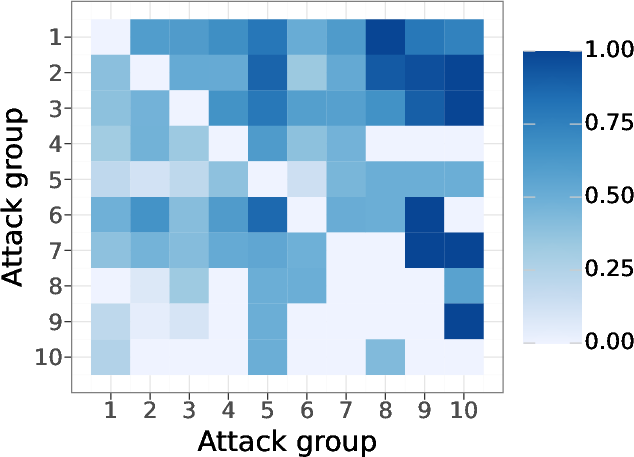
Figure 4: Visualizing attack profitability against incurred costs, illustrating variance in operation success.
Conclusion
Overall, "Blockchain Address Poisoning" provides a comprehensive exploration into a sophisticated financial attack, emphasizing the importance of proactive measures in the blockchain ecosystem to safeguard user assets from phishing schemes. The paper serves as a foundational study for further operational threat modeling and preventative defense architecture in cryptocurrency transactions.