- The paper introduces a protocol that validates path-level policy compliance in QKD networks using cryptographic primitives like NIZKs, pseudonyms, and structure-preserving signatures.
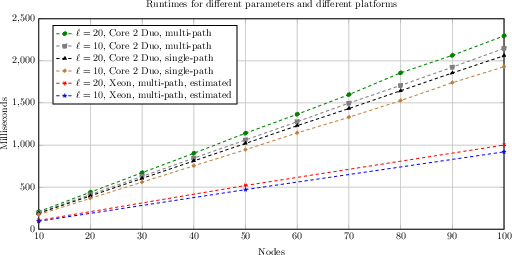
- It demonstrates practical efficiency with verification times below 2.5 seconds and communication overhead under 70 KB for paths with 100 nodes.
- The protocol ensures topology-hiding by exposing only entry and exit nodes, enabling auditable compliance without revealing the intermediate network structure.
Topology-Hiding Path Validation for Large-Scale Quantum Key Distribution Networks
Introduction and Problem Setting
Ensuring secure, long-distance communications in Quantum Key Distribution (QKD) networks relies intrinsically on trusted repeater nodes distributed along transmission paths. While QKD protocols offer unconditional security rooted in physical principles, practical realizations demand intermediate trusted repeaters to overcome quantum signal attenuation over long distances. The presence of these repeaters introduces an inherent vulnerability: a compromised node may subvert the security guarantees of the overall network. Reducing the necessity for trust in these intermediates is thus a central challenge in scaling QKD deployments.
Current measures such as multi-path QKD and secret sharing provide partial mitigation by distributing key material over disjoint network paths, thereby reducing dependence on any single node. However, the security properties of such schemes fundamentally rely on the network operator’s fidelity in routing keys over genuinely disjoint and policy-compliant paths. Since operators may have financial or operational incentives to violate these constraints covertly, technical and auditable mechanisms, rather than mere contractual guarantees, are required to enforce and verify compliance, while simultaneously protecting the operator’s confidential network topology.
This work presents a cryptographically rigorous protocol for path validation in QKD networks. The protocol is designed to enable receivers to audit path-level policy compliance—such as verifying device certification and enforcing path disjointness—without revealing sensitive details about the underlying network topology to clients. The construction achieves practical efficiency: even for transmission over 100 nodes, computational costs remain in the range of $1$–2.5s with communication overheads below 70kB per session at the receiver.
The protocol is structured as a modular extension suitable for deployment in arbitrary QKD networks. The foundation is a cryptographic compositional framework with clearly defined syntax and adversarial goals:
- Path-Hiding: The protocol guarantees that, aside from entry and exit nodes (trivially exposed due to QKD network architecture), the receiver learns no meaningful information about the intermediate topology, such as which nodes participated or the structure of the network. This is realized through an indistinguishability game which formalizes adversarial attempts to distinguish between different transmission paths given full topological knowledge.
- Policy Compliance: Receivers are cryptographically guaranteed that all repeaters involved in their key exchange strictly satisfy the agreed-upon policy constraints (e.g., certification levels, manufacturer, geographical location), and that the protocol correctly enforces path disjointness.
The security model permits a malicious network operator who can arbitrarily choose paths and install or remove nodes, under the assumption that the cryptographic identities of repeaters are bound by a prior certification process—an assumption consistent with operational QKD network security practices.
Protocol Construction
Generic Design
The protocol exploits the synergy between several core primitives:
- Structure-Preserving Signatures: All nodes are equipped with a credential in the form of a signature on their identity and attributes issued by a trusted authority.
- Scope-Exclusive Pseudonym Schemes: For each session, nodes derive unlinkable pseudonyms based on their secret keys and session IDs. These pseudonyms remain stable only within a session's scope and cannot be linked across sessions.
- Simulation Sound Non-Interactive Zero-Knowledge Proofs (NIZKs): Nodes generate zero-knowledge proofs asserting both knowledge of a credential and compliance with the path policy, binding their proof to the session context without revealing their identity or the underlying topology.
In the single-path scenario, every node along the path produces, appends, and forwards a NIZK proof attesting to compliance with the path policy. In the multi-path setting, each node additionally generates a session-specific pseudonym and proves this pseudonym is derived from the key certified in their attribute-based credential. At the terminus, the receiver verifies all proofs and asserts that pseudonyms across all paths are pairwise distinct, providing cryptographic evidence of node disjointness.
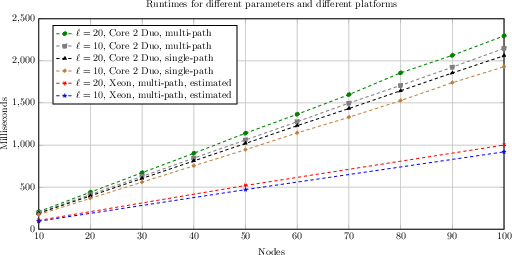
Figure 1: Runtime evaluation for receiver B demonstrates linear scaling with path length and practical runtimes even for 100-node scenarios.
Practical Instantiation
The instantiation employs Groth's G1-structure preserving signature for credential issuance, a Diffie-Hellman-style scope-exclusive pseudonym scheme, and Schnorr-type NIZK proofs rendered non-interactive via the Fiat-Shamir heuristic. All cryptographic computations are carried out using bilinear group settings (e.g., BLS12-381), ensuring compatibility with state-of-the-art cryptographic libraries and accelerating implementations.
Security guarantees are formally preserved under standard assumptions: unforgeability of the signature scheme, collision resistance and unlinkability of the pseudonym system, and simulation sound extractability of the NIZK.
Numerical Evaluation
Benchmarks indicate the protocol's computational and bandwidth overhead is well aligned with operational requirements for real-world QKD deployments. Specifically, with 100 nodes and up to 20 certified attributes per node, receivers incur a computation delay below $2.5$ seconds (Intel Xeon Platinum, AWS) and communication overheads remain beneath 70kB. The dominant computational effort is incurred by the receiver during verification; per-node runtime is negligible and easily amortized by QKD’s batch processing nature.
Theoretical and Practical Implications
This protocol achieves, for the first time in the QKD context, cryptographic enforcement of path-level policy compliance in a topology-hiding manner. Unlike previous path-verification schemes, which presume sender awareness of routing paths (an impractical assumption in QKD networks), this approach provides verifiable evidence decoupled from path transparency, thus directly supporting the operational reality of managed, SLA-driven QKD networks.
- For regulatory and compliance contexts: The protocol enables external auditors or high-assurance clients to verify compliance with jurisdictional, manufacturer, or certification constraints without providing competitors or adversaries with sensitive network topology intelligence.
- For multi-domain QKD integration: The framework accommodates multi-authority scenarios (e.g., cross-border QKD) by leveraging issuer-hiding credentials, which is critical for broader European or global network scenarios.
- Beyond QKD: The design paradigm—topology-hiding, verifiable path attestation—may generalize to other settings necessitating both routing confidentiality and externally auditable compliance (e.g., managed government networks, critical infrastructure backbones).
Future Work
While the current construction is practical for moderate hop counts and session durations, the protocol's verification cost increases linearly with path length. As such, scaling to massive path lengths motivates investigation into succinct proof systems. The authors propose recursive SNARK techniques as a promising avenue for achieving constant-size proofs of path compliance and node-disjointness, albeit noting challenges in maintaining efficiency and privacy properties. Other open challenges include achieving index hiding, so that a node cannot infer its honest position within the forwarding path—further reducing information leakage.
Conclusion
The paper presents a protocol that cryptographically enforces and audits path-level policy compliance in QKD networks while maintaining strict confidentiality of network topology. By integrating structure-preserving signatures, scope-exclusive pseudonyms, and simulation-sound NIZKs, it offers a practical, efficient, and formally secure scheme. This protocol not only enhances trust minimization in the rollout of future large-scale QKD infrastructures but also establishes foundational techniques that may be relevant for path attestation in privacy-sensitive classical networks. The approach’s extensibility to multi-authority settings and its empirical practicality substantiate its relevance in future high-security communication deployments.