- The paper introduces a protocol leveraging zero-knowledge proofs and graph signatures to validate inter-network paths without revealing provider topologies.
- The method employs Pedersen commitments and path padding to obscure node identities and actual hop counts while ensuring verifiable connectivity.
- The protocol ensures soundness, topology hiding, and composability, offering a robust solution for secure, federated QKD inter-networking.
Topology-Hiding Connectivity Assurance for QKD Inter-Networking
Introduction and Motivation
Quantum Key Distribution (QKD) networks, despite guaranteeing information-theoretic security at the physical link layer, remain fundamentally constrained by their reliance on trusted intermediate nodes—so-called trusted repeaters. The presence of such repeaters introduces implicit trust dependencies; any compromise of a repeater along the key relay path breaks the end-to-end security semantics. As QKD infrastructure deployments expand beyond national silos to form interconnected, multi-provider, and potentially adversarial domains, the challenge emerges: users must be able to verify inter-network path availability and properties (e.g., path existence, hop count thresholds, disjointness) without learning sensitive internal topology information of competing providers.
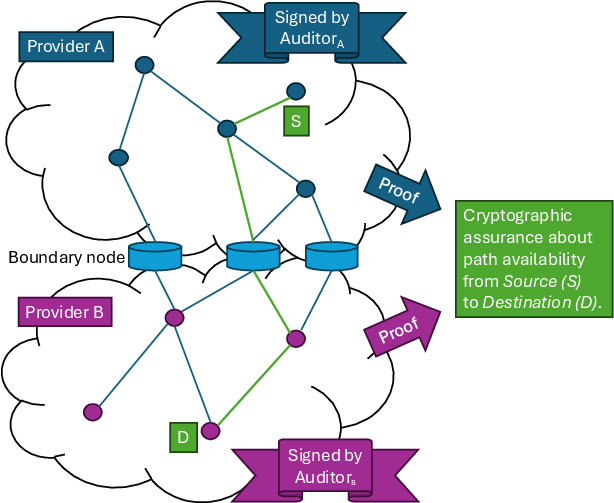
The work "Topology-Hiding Connectivity-Assurance for QKD Inter-Networking" (2604.01876) presents a cryptographic protocol that allows independent QKD network providers to jointly, yet privately, prove the existence of an end-to-end connection. The proposed scheme extends and generalizes the committed graph signature paradigm to multigraphs with endpoint hiding and path length camouflaging, leveraging advanced zero-knowledge (ZK) proof techniques to deliver privacy-preserving connectivity attestations.
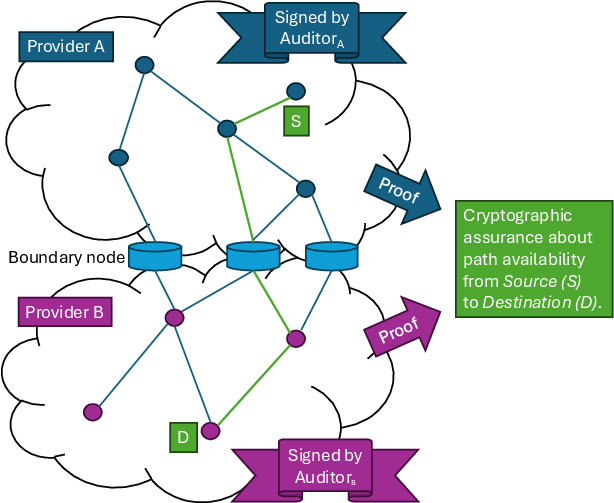
Figure 1: Users are able to obtain cryptographic assurance about inter-network path availability without revealing the underlying network topology.
Technical Construction
Preliminaries and Building Blocks
The protocol is constructed atop the following cryptographic primitives:
- MoniPoly-based Graph Signatures: A q-SDH–based signature scheme supporting signatures on committed graph structures, as described in [cryptoeprint:2020/1403], is extended from simple graphs to labeled, loop-augmented multigraphs.
- Pedersen Commitments: For hiding node identities, perfectly hiding and computationally binding commitments are used, instantiated in prime order groups under the discrete log assumption.
- Zero-Knowledge Proofs: Statements about path existence, node identifiers, and path padding are proven in ZK without revealing underlying secrets using the Camenisch-Stadler notation and efficient sigma protocols.
Topology-Hiding Protocol Overview
The proposed scheme proceeds in two major phases:
Phase 1: Network Topology Certification and Padding
Each network provider P obtains from its respective certification authority (e.g., a governmental agency) a signature on its network topology, modeled as a multigraph GP. To support path length hiding, for each boundary node, the provider computes the maximal shortest-path distance to any internal node (ℓP) and pads each such node with ℓP self-loops. This augmentation enables any real path of arbitrary (shorter) length to be padded with indistinguishable loops up to the certified bound, rendering the actual number of hops on the provider's internal segment information-theoretically hidden.
The resulting multigraph is signed using the q-SDH–based signature scheme, binding the committed topology to the provider's certified identity.
Phase 2: Zero-Knowledge Path Existence with Endpoint Hiding
In the online phase, to prove the existence of a path between endpoint S (in domain A) and D (in domain B):
- Providers locally compute per-domain shortest paths from endpoint to all boundary nodes.
- Providers execute a secure Multi-Party Computation (MPC) to jointly select a boundary node that minimizes total path costs, without revealing internal metrics.
- The selected boundary node is committed to (via Pedersen commitments), and the opening is shared under secure channels to establish consistency between providers.
- Each provider constructs a ZK proof that:
- They possess a valid certified signature on their padded multigraph.
- There exists a path from their domain's endpoint to the boundary node, of fixed (padded) length, using edges in the signed multigraph.
- The boundary node identities used in both proofs are bound to the same commitments, ensuring a continuous path.
- The user (customer) verifies both ZK proofs; acceptance guarantees a connection exists as specified, without learning the internal structure, path length, or any auxiliary topology data from either provider.
Path Existence Proof in ZK
The core ZK proof employs pairing-based cryptography and encodes the existence of a path between two hidden nodes (or a public node and a hidden node) in the signed, padded multigraph. Padding with labeled loops ensures non-disclosure of exact path length. Commitment to endpoints and the use of joint openings guarantee atomicity across cross-domain paths, preventing adversaries from coupling information across multiple protocol runs.
Security Properties
The protocol achieves the following security targets:
- Soundness: Adversarial providers cannot prove false path existence without forging a graph signature (assumed hard under q-SDH).
- Topology Hiding: The protocol provably leaks no information on internal topology—neither the number of hops, internal node identities, nor edge labels outside what is inherent to the claim (i.e., the existence of a path of at most ℓ edges).
- Unlinkability: Even across multiple sessions, providers cannot learn incremental topology information, due to the use of session-dependent pseudonyms and credentials.
- Composability: The protocol naturally supports deployment scenarios where each provider may be certified by different authorities and does not require global naming aside from boundary nodes.
Extensions and Functionality
The construction admits nontrivial generalizations:
- Multi-Path Guarantees: By encoding per-node random attributes and issuing session-bound pseudonyms, the protocol can be extended to give ZK proofs of k disjoint paths for multipath QKD, increasing repeater trust robustness.
- Quality Attribute Statements: Providers can additionally prove path properties (e.g., minimum bandwidth, certification level) if such attributes are committed per node/edge, yielding expressive path attestation policies.
- Post-Quantum Considerations: The current protocol relies on number-theoretic hardness (q-SDH). An open problem is achieving comparable soundness with post-quantum primitives while preserving privacy and efficiency.
Practical and Theoretical Implications
This protocol realizes, for the first time, robust topology-hiding path claims across federated QKD domains. For practical QKD-as-a-service or multi-national QCI deployments, it enables network users to obtain cryptographically strong, auditor-certified assurance of service reachability without disclosing providers’ sensitive business or infrastructure data. This protects competitive interests while enabling operational transparency and trust.
From a theoretical perspective, the scheme demonstrates the applicability and flexibility of graph signature–based cryptographic certifications, and pushes the boundary of privacy-preserving, decentralized network attestation beyond conventional cloud and classical networking use cases.
Conclusion
A topology-hiding, ZK-based connectivity-assurance protocol for QKD inter-networking has been defined, analyzed, and instantiated with efficient pairing-based constructions. It achieves strong privacy and composability properties, aligning with both user security requirements and provider confidentiality. Future advancements may focus on realizing similar guarantees with quantum-secure primitives and scaling performance across realistic topologies. This work establishes a practical, deployable foundation for verifiable, privacy-preserving network assurance as QKD infrastructure matures and interconnects globally.