- The paper introduces comprehensive MEV mitigation techniques across Ethereum and Layer-2 chains, emphasizing fair ordering, privacy-preserving methods, and proposer-builder separation.
- It evaluates approaches like delay encryption and shared sequencer networks, highlighting trade-offs between latency, security, and decentralization.
- Findings suggest that integrating privacy methods with PBS can enhance network integrity and support the development of robust, future-proof defenses.
Maximal Extractable Value Mitigation Approaches in Ethereum and Layer-2 Chains: A Comprehensive Survey
Introduction
Maximal Extractable Value (MEV) represents a growing concern in the Ethereum ecosystem, affecting the integrity and operations of both Layer 1 (L1) and Layer 2 (L2) networks. MEV, a practice where miners or validators manipulate transaction ordering to extract additional value, poses significant risks to user experience and the network's decentralization ethos. This paper provides a thorough survey of current MEV mitigation techniques, detailing novel categorizations and effectiveness across various strategies while assessing implementation challenges and network impact.
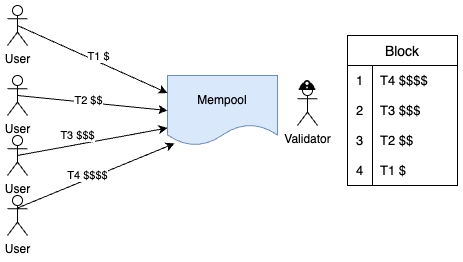
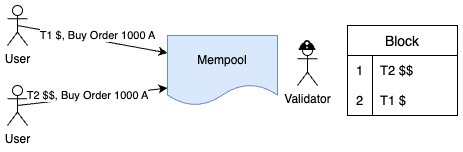
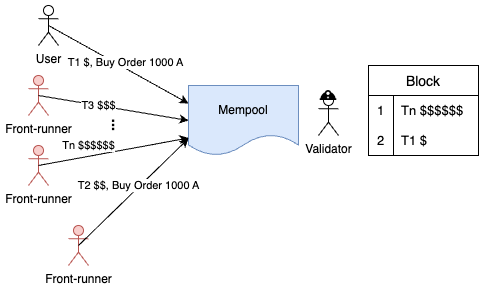
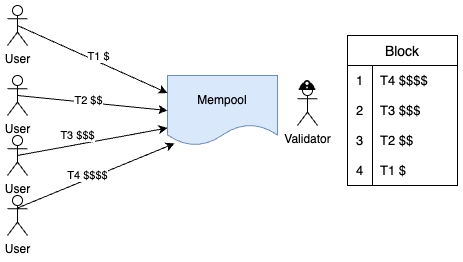
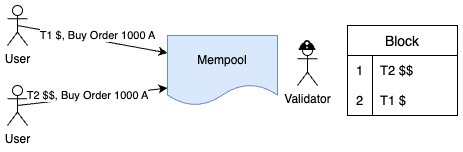
Figure 1: Opportunity for Front-running Attacks Arising from validators' Arbitrary Transaction Selection and Ordering.
Background
MEV manipulation primarily arises from strategies like DEX arbitrage and liquidations, where miners can exploit transaction ordering. This leads to financial risks for users and potential destabilization of network protocols. Front-running, a particularly prominent form of MEV extraction, involves rushing ahead of other transactions by exploiting higher transaction fees in the mempool (Figure 1).
Layer 2 solutions, specifically rollups, provide scalability by processing transactions off-chain but retain vulnerabilities to MEV through centralized or single-sequencer models.
Taxonomy of MEV Mitigation Strategies
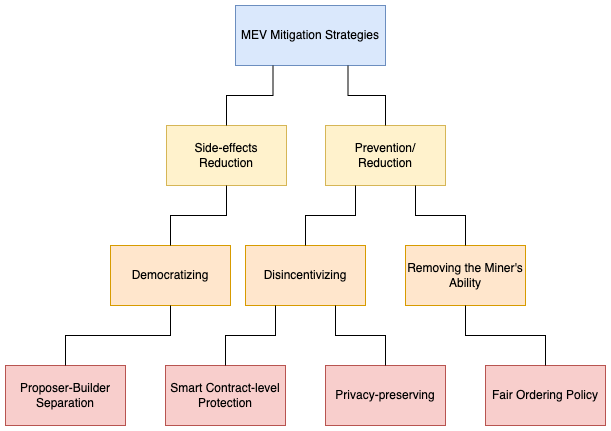
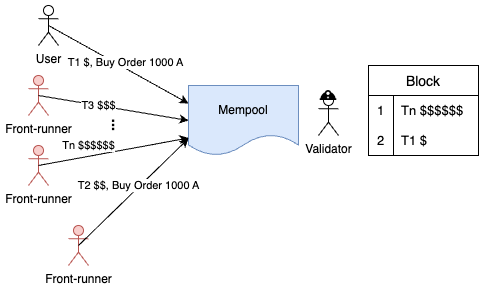
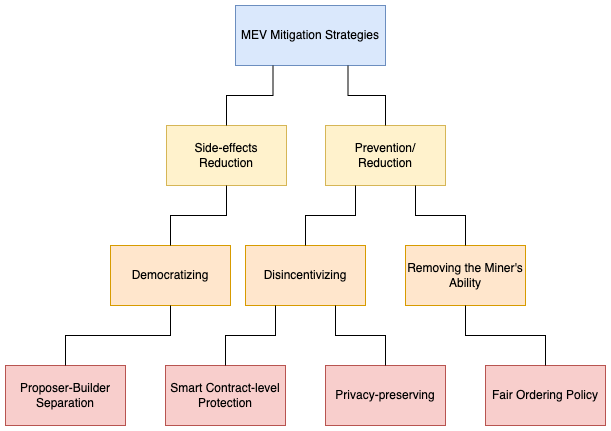
Figure 2: Taxonomy of MEV Mitigation Strategies.
Fig. 2 presents a taxonomy categorizing three principal MEV mitigation strategies:
- Fair Ordering Policies: Enforces transaction order based on explicit rules, such as First-Come-First-Serve (FCFS), to reduce front-running risks. Single sequencing strategies face latency wars and spam attacks but simplify implementation, evidenced by protocols like Arbitrum and Optimism. More advanced decentralized sequencing approaches, such as Themis and Wendy, propose committees with Batch-Order-Fairness and synchronized clocks, respectively.
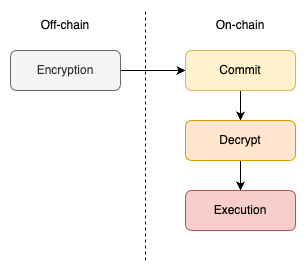
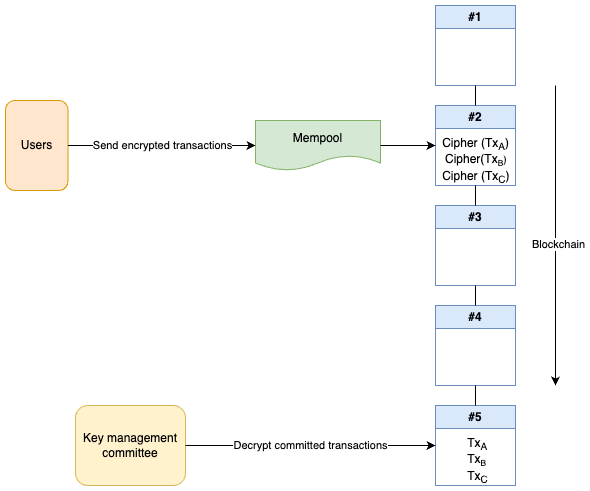
- Privacy-preserving Methods: Focus on transaction concealment before confirmation. Threshold encryption involves trusted key holders, while delay encryption leverages time-lock puzzles for trustless privacy (Figure 3).
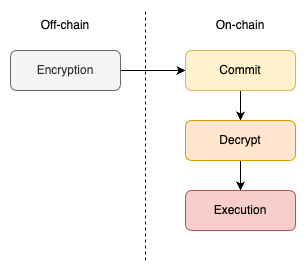
Figure 3: Mempool Encryption General Approach.
- Smart Contract-level Protection: Address MEV within application layers, using methods like commit-and-reveal and off-chain components. Solutions like CoWswap facilitate asset swaps while enhancing off-chain privacy protocols.
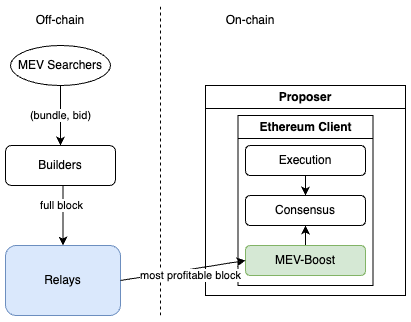
- Proposer-Builder Separation (PBS): Aims to democratize MEV by separating block proposers from builders, thereby decentralizing power (Figures 11).
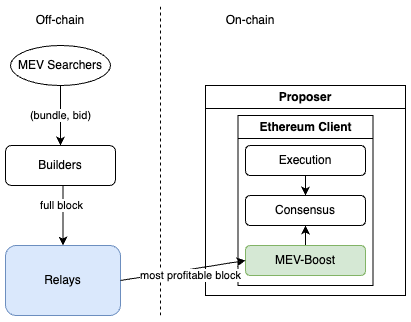
Figure 4: MEV-Boost Architecture.
Privacy-Preserving Techniques
Threshold Encryption (Figure 5) uses a committee for key management, with a risk of collusion among members. In contrast, Delay Encryption employs time-lock puzzles for trustless privacy, and TEEs offer hardware-based solutions. Challenges include computational overhead and hardware dependencies.
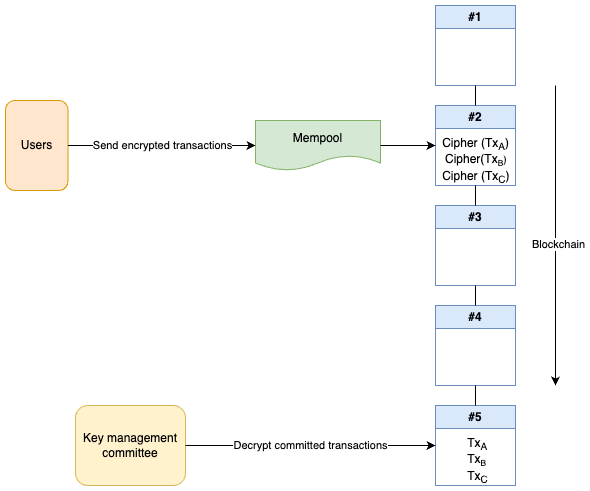
Figure 5: Sending Encrypted Transactions by the User Using the Threshold Encryption Method.
Shared Sequencer Networks
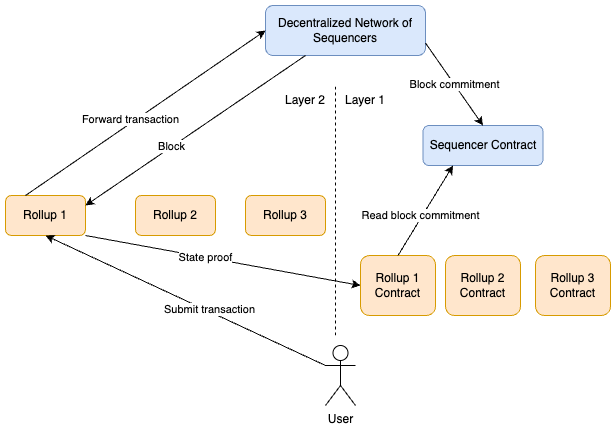
Espresso represents the architecture where Rollups share sequencer networks to reduce operational costs and improve decentralization (Figure 6). This model mitigates fragmentation risks but requires incentives for fair resource allocation among Rollup chains.
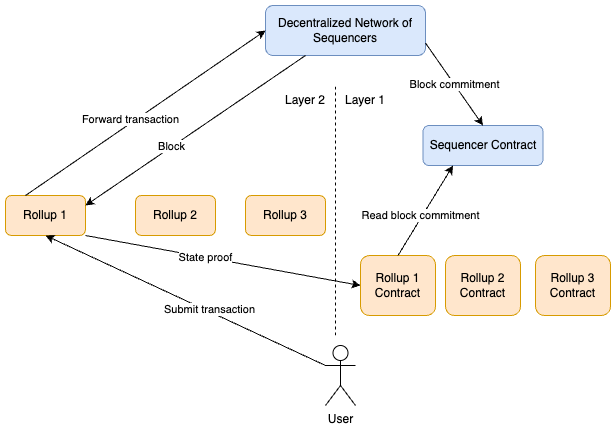
Figure 6: Espresso Network Architecture as a Decentralized Shared Sequencer.
Discussion
Implementation strategies differ in complexity and efficiency. Fair ordering offers simplicity but requires significant communication, whereas privacy-preserving methods introduce latency due to encryption/decryption processes. PBS, implemented off-chain via MEV-Boost, seamlessly integrates without adding network load.
The adaptability of privacy-preserving methods, especially delay encryption, and PBS to L1 protocols indicates promising integration paths. Further research in shared sequencing and Witness Encryption can foster more robust MEV defenses.
Conclusion
The survey highlights diverse strategies addressing MEV extraction with unique advantages and potential drawbacks. Privacy-preserving techniques, particularly Delay Encryption, coupled with PBS, emerge as viable MEV defenses. As research on shared sequencing and cryptography progresses, new solutions could emerge, emphasizing the need for continued exploration in these domains.