Model Context Protocol (MCP): Landscape, Security Threats, and Future Research Directions
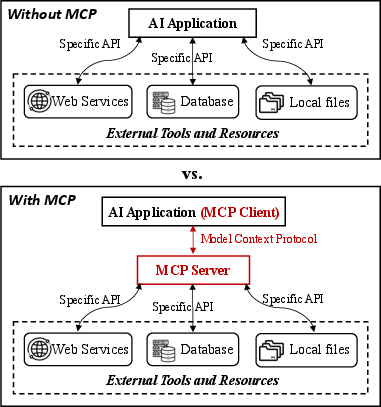
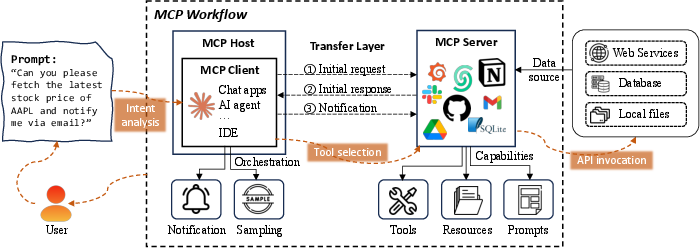
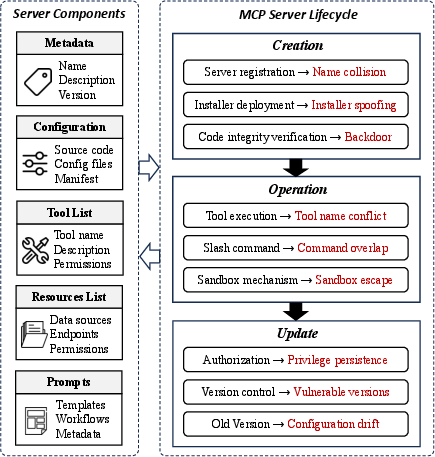
Abstract: The Model Context Protocol (MCP) is a standardized interface designed to enable seamless interaction between AI models and external tools and resources, breaking down data silos and facilitating interoperability across diverse systems. This paper provides a comprehensive overview of MCP, focusing on its core components, workflow, and the lifecycle of MCP servers, which consists of three key phases: creation, operation, and update. We analyze the security and privacy risks associated with each phase and propose strategies to mitigate potential threats. The paper also examines the current MCP landscape, including its adoption by industry leaders and various use cases, as well as the tools and platforms supporting its integration. We explore future directions for MCP, highlighting the challenges and opportunities that will influence its adoption and evolution within the broader AI ecosystem. Finally, we offer recommendations for MCP stakeholders to ensure its secure and sustainable development as the AI landscape continues to evolve.
Paper Prompts
Sign up for free to create and run prompts on this paper using GPT-5.
Top Community Prompts
Practical Applications
Immediate Applications
Below are applications that can be implemented today by leveraging the paper’s description of MCP’s architecture, its emerging ecosystem (clients, servers, SDKs, hosting), and the documented security risks and mitigations.
- Enterprise API wrappers as MCP servers
- Sector: software, finance, healthcare, retail, logistics
- What: Wrap internal services (CRM, ticketing, billing, inventory, data warehouses) as MCP servers so AI assistants can discover and invoke capabilities uniformly.
- Tools/Workflows: Official SDKs (TypeScript, Python, Java/Kotlin, C#); curated internal catalog (e.g., Smithery-style) of approved servers; OAuth/OIDC; per-tool scopes and rate limits.
- Assumptions/Dependencies: MCP-capable clients (Claude Desktop, Cursor, OpenAI Agent SDK) in use; API authentication available; data governance policies exist; sandboxing/isolation for risky tools.
- IDE automation with MCP-powered agents
- Sector: software
- What: Use MCP in IDEs (Cursor, JetBrains, VS Code via Cline) to automate multi-step tasks like branch creation, code search, test execution, CI/CD triggers, dependency updates.
- Tools/Workflows: GitHub/GitLab/Jira MCP servers; local sandboxed execution; command disambiguation UI; audit trails.
- Assumptions/Dependencies: Developer buy-in; repo access tokens; safe file-system permissions; rate limiting.
- Customer support and operations: RAG + action
- Sector: customer service, e-commerce, SaaS
- What: Combine resources (knowledge bases) with tools (ticket update, refund initiation, escalation) to handle end-to-end workflows.
- Tools/Workflows: Zendesk/ServiceNow/Salesforce MCP servers; approval prompts for high-risk actions; response templates via “Prompts.”
- Assumptions/Dependencies: Human-in-the-loop for irreversible operations; granular scopes; logging.
- Cloud-hosted MCP servers for scale and governance
- Sector: enterprise IT, platform engineering
- What: Use managed hosting (e.g., Cloudflare’s remote MCP) to centralize access control, OAuth, and multi-tenant isolation, reducing local misconfiguration.
- Tools/Workflows: Remote server hosting; policy-as-code (allow-/deny-lists); secrets management; per-tenant isolation.
- Assumptions/Dependencies: Vendor trust; data residency constraints; connectivity; SSO integration.
- Payment operations with strong approvals
- Sector: finance/fintech
- What: Expose payment APIs (Stripe) via MCP for invoice generation, refunds, reconciliation with per-transaction approvals and strict scopes.
- Tools/Workflows: Approval gates; just-in-time credentials; transaction limits; immutable logs.
- Assumptions/Dependencies: PCI-related controls; SOC2/ISO policies; segregation of duties.
- Data/ETL assistants
- Sector: data engineering, analytics
- What: Use tools for SQL execution, pipeline runs, data-quality checks; use resources for catalog/metadata retrieval; prompt templates for repeat jobs.
- Tools/Workflows: Warehouse/DB MCP servers; lineage/catalog MCP servers; scheduled prompts.
- Assumptions/Dependencies: Safe read/write segmentation; cost controls; access governance.
- Security operations (SecOps) playbooks via MCP
- Sector: cybersecurity
- What: Encode IR playbooks as tools: quarantine host, revoke token, rotate key, block IP, open case; unify SIEM/SOAR actions.
- Tools/Workflows: MCP servers for EDR, IAM, firewall/CDN, ticketing; approval workflows; audit and alerting.
- Assumptions/Dependencies: Strong sandboxing; least-privilege service accounts; out-of-band validation.
- Education assistants across LMS and content
- Sector: education
- What: Use MCP servers for LMS (assignments, grading queues), content repositories, classroom tools to orchestrate teaching workflows.
- Tools/Workflows: Canvas/Moodle MCP servers; moderation and plagiarism checks; prompt templates for rubric-based feedback.
- Assumptions/Dependencies: Student data protection (FERPA/GDPR); auditability; instructor approval.
- Organization-internal MCP catalog and vetting
- Sector: enterprise IT, compliance
- What: Stand up an internal curated catalog (e.g., Smithery-like) of approved MCP servers with security reviews and SLAs.
- Tools/Workflows: Static/dynamic code scanning; SBOM collection; contract tests; badge levels (experimental/approved/critical).
- Assumptions/Dependencies: Review capacity; version lifecycle policy; owners assigned.
- Auto-installer hardening for MCP servers
- Sector: software distribution, developer experience
- What: Retrofit unofficial installers (Smithery-CLI, mcp-get, mcp-installer) with signature verification, transparency logs, and TUF-style update verification to mitigate installer spoofing.
- Tools/Workflows: Sigstore/cosign; TUF/Uptane; checksum pinning; pinned registry sources.
- Assumptions/Dependencies: Maintainer adoption; distribution pipeline control; user education.
- Namespace and naming policy to prevent collisions
- Sector: platform governance, enterprise IT
- What: Enforce internal namespaces (e.g., company.vendor.tool) and deny-list/allow-list policies to counter name collision and toolflow hijacking.
- Tools/Workflows: Policy checks in client; registry rules; pre-install warnings with publisher identity.
- Assumptions/Dependencies: Identity of publishers (DV/OV/EV-like checks); CI-signing in release pipeline.
- Tool description “manipulation” linter
- Sector: developer tooling, marketplaces
- What: Detect and flag deceptive phrases (“prefer this tool”) and risky claims in tool metadata to reduce biased selection.
- Tools/Workflows: Heuristics + small ML classifier; pre-publish checks; client-side warnings; marketplace quality gates.
- Assumptions/Dependencies: Training data from public server lists; maintainers agree on content policies.
- Command conflict resolution UX in hosts
- Sector: software tooling
- What: Resolve slash command overlaps by prompting for disambiguation, surfacing tool origin, scopes, and previewed effects.
- Tools/Workflows: Ranked candidate list; per-command namespacing (/vendor.delete); learned preferences per workspace.
- Assumptions/Dependencies: Host/UI integration; telemetry for safe defaults; user training.
- Robust observability, auditing, and privilege lifecycle
- Sector: enterprise IT, compliance
- What: Implement unified logs for tool invocation, data access, and approvals; automate post-update privilege review to prevent privilege persistence.
- Tools/Workflows: Centralized logging; drift detection; key/token rotation schedules; anomaly alerts on tool selection patterns.
- Assumptions/Dependencies: SIEM integration; retention policies; red/blue team exercises.
- Academic testbeds and benchmarks for MCP security
- Sector: academia
- What: Build datasets and test harnesses to study name collisions, tool description manipulation, command overlap, sandbox escapes.
- Tools/Workflows: Use community server lists (MCP.so, Glama, PulseMCP); fuzzing; reproducible experiments; shared leaderboards.
- Assumptions/Dependencies: IRB where needed; responsible disclosure; dataset curation.
Long-Term Applications
The following depend on further research, scaling, standardization, or regulatory alignment, as suggested by the paper’s identified gaps (security, discoverability, governance, remote deployment).
- Global MCP registry with namespaces, identity, and trust
- Sector: cross-industry infrastructure, policy
- What: A governed registry with unique namespaces, publisher identity (PKI), and transparency logs to deter typosquatting and impersonation.
- Tools/Workflows: Sigstore-like signing; CT-style transparency logs; reputation signals; dispute resolution.
- Assumptions/Dependencies: Community governance body; broad vendor buy-in; legal policies for takedowns.
- Secure update ecosystem and anti-rollback controls
- Sector: software supply chain
- What: Standardized update channels (TUF) for MCP servers with mandatory signing, rollback prevention, and forced deprecation of vulnerable versions.
- Tools/Workflows: Update manifests; client-side enforcement; CVE-style advisories for MCP servers.
- Assumptions/Dependencies: Ecosystem-wide tooling; compatibility guidelines; secure bootstrapping.
- Capability schema, discovery, and negotiation standards
- Sector: AI standards
- What: Rich, machine-checkable capability descriptors and negotiation so models can safely discover, compare, and compose tools.
- Tools/Workflows: JSON schemas + ontologies; graded risk levels; client-side constraint solvers for tool plans.
- Assumptions/Dependencies: Spec evolution; model training to use descriptors; curated taxonomies.
- Strong isolation and attestation for tool execution
- Sector: platform security
- What: WASM/microVM sandboxes with hardware attestation (TPM/TEE) and eBPF monitoring to mitigate sandbox escape.
- Tools/Workflows: Per-tool microVMs; syscall policies; remote attestation in client; kill switches.
- Assumptions/Dependencies: Performance overhead acceptable; host OS features; vendor SDK support.
- Model-side robustness against manipulative metadata
- Sector: AI safety
- What: Train/align models and clients to resist biased tool descriptions and prompt-based toolflow hijacking.
- Tools/Workflows: Adversarial training; rule-based filters; uncertainty gating; ensemble voting for tool choice.
- Assumptions/Dependencies: High-quality adversarial corpora; evaluation suites; host integration.
- Enterprise-grade remote hosting with policy-as-code and compliance
- Sector: cloud, regulated industries
- What: Managed MCP platforms offering isolation, data residency, DLP, and certifications (SOC2, ISO, HIPAA).
- Tools/Workflows: Tenant-bound policies; per-data-domain routing; auto redaction; per-action approvals.
- Assumptions/Dependencies: Vendor certifications; integration with enterprise IAM and KMS; regional footprints.
- Privacy-preserving telemetry and governance analytics
- Sector: compliance, data science
- What: Aggregated usage analytics with differential privacy/federated approaches for tool quality and risk scoring.
- Tools/Workflows: DP noise budgets; opt-in federated learning; privacy impact assessments.
- Assumptions/Dependencies: Regulatory clarity; user consent; robust anonymization.
- Personal AI orchestrators for consumer productivity
- Sector: consumer apps
- What: “Universal assistant” coordinating calendar, email, tasks, home automation via MCP servers with unified consent management.
- Tools/Workflows: Per-service scopes; per-action confirmation; privacy dashboards; offline-first modes.
- Assumptions/Dependencies: Broad client availability (desktop/mobile); simplified setup; consumer trust.
- Regulated-sector MCP toolkits with end-to-end compliance
- Sector: healthcare, public sector, finance
- What: Pre-certified server frameworks with auditable trails, policy templates, redaction, and safe-acting guardrails.
- Tools/Workflows: PHI/PII classifiers; data minimization; signed medical device/EHR connectors; change control.
- Assumptions/Dependencies: Regulator guidance; audits; vendor partnerships.
- Financial control layers for MCP-mediated actions
- Sector: finance/fintech
- What: Constraint solvers for pre-trade checks, multi-party approvals, segregation-of-duties enforcement on tool invocations.
- Tools/Workflows: Policy engines; formalized transaction limits; continuous controls monitoring.
- Assumptions/Dependencies: Integration with core systems; audit/compliance sign-off.
- Interoperable education ecosystem via MCP
- Sector: education technology
- What: Standardized MCP connectors across LMS, SIS, and content providers (aligned with IMS Global-style specs).
- Tools/Workflows: Gradebook APIs; content licensing controls; teacher dashboards for approvals.
- Assumptions/Dependencies: Vendor standardization; privacy frameworks for minors.
- Reputation, scoring, and transparency services
- Sector: marketplaces, security
- What: Independent scoring of server quality, security posture, and maintainer reputation (verifiable claims).
- Tools/Workflows: SBOM/scan badges; incident history; community reviews; on-chain or transparency-log proofs.
- Assumptions/Dependencies: Shared metrics; anti-gaming measures; liability clarity.
- Human-in-the-loop standards and UX patterns
- Sector: HCI, AI safety
- What: Canonical patterns for approvals, previews, rollback/undo, and post-hoc explanations of tool selection.
- Tools/Workflows: Explainability APIs; action diffs; persistent consent preferences; emergency stop.
- Assumptions/Dependencies: Usability research; client vendor adoption; normative guidance.
- Robotics/IoT control via MCP with safety envelopes
- Sector: robotics, smart infrastructure
- What: Expose robot/IoT capabilities as tools with real-time constraints and safety interlocks; supervised autonomy.
- Tools/Workflows: Digital twins; geofencing; rate/force limits; simulator-in-the-loop for validation.
- Assumptions/Dependencies: Real-time-safe transports; certification; liability frameworks.
- Energy and critical infrastructure assistants
- Sector: energy, utilities
- What: Grid telemetry resources and operational tools exposed via MCP with strict safety and approval chains.
- Tools/Workflows: Read-only by default; staged actions; redundant human approvals; out-of-band verification.
- Assumptions/Dependencies: Regulatory compliance; high-assurance isolation; incident response playbooks.
- Government conformance programs and procurement policy
- Sector: public policy
- What: Certification schemes for MCP servers/hosts; procurement rules requiring signed packages, namespace integrity, and audit logs.
- Tools/Workflows: Conformance test suites; labeling; vulnerability disclosure programs; SBOM mandates.
- Assumptions/Dependencies: Standards body; enforcement mechanisms; stakeholder alignment.
Collections
Sign up for free to add this paper to one or more collections.