- The paper identifies vulnerabilities in token management and consent mechanisms that risk exposing sensitive data.
- The paper introduces short-lived tokens, strong customer authentication, and granular access scopes to mitigate security threats.
- The paper’s empirical evaluation shows the enhanced protocol prevents data leakage under prompt injection attacks with minimal latency impact.
Improving Google A2A Protocol: Protecting Sensitive Data and Mitigating Unintended Harms in Multi-Agent Systems
Introduction
The "Improving Google A2A Protocol: Protecting Sensitive Data and Mitigating Unintended Harms in Multi-Agent Systems" focuses on addressing critical vulnerabilities in Google's Agent-to-Agent (A2A) protocol. Despite the protocol's structured framework for agent communication, designed for interoperability in multi-agent environments, it lacks provisions for handling sensitive information such as payment credentials securely. This essay explores identifying these vulnerabilities, proposing enhancements, and evaluating the improved protocol's efficacy.
Identified Vulnerabilities
Google’s A2A protocol provides a framework for communication between AI agents but displays significant security gaps when dealing with sensitive data. Key vulnerabilities identified include insufficient token lifetime control, lack of strong customer authentication (SCA), broad access scopes without sufficient granularity, and the absence of explicit consent mechanisms. These weaknesses render the protocol susceptible to unauthorized data access, privilege escalation, and other security threats, notably within environments handling sensitive tasks like financial transactions.
Illustrative Example:
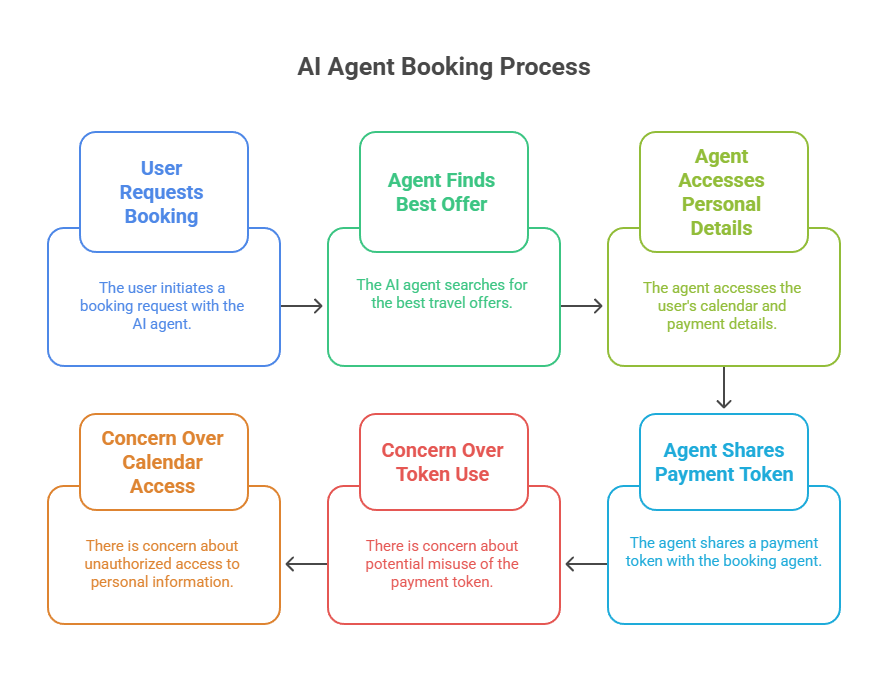
In a typical scenario, an AI agent tasked with booking a vacation might access excessive user calendar information and use long-lived tokens, increasing risks of unauthorized data access (Figure 1).
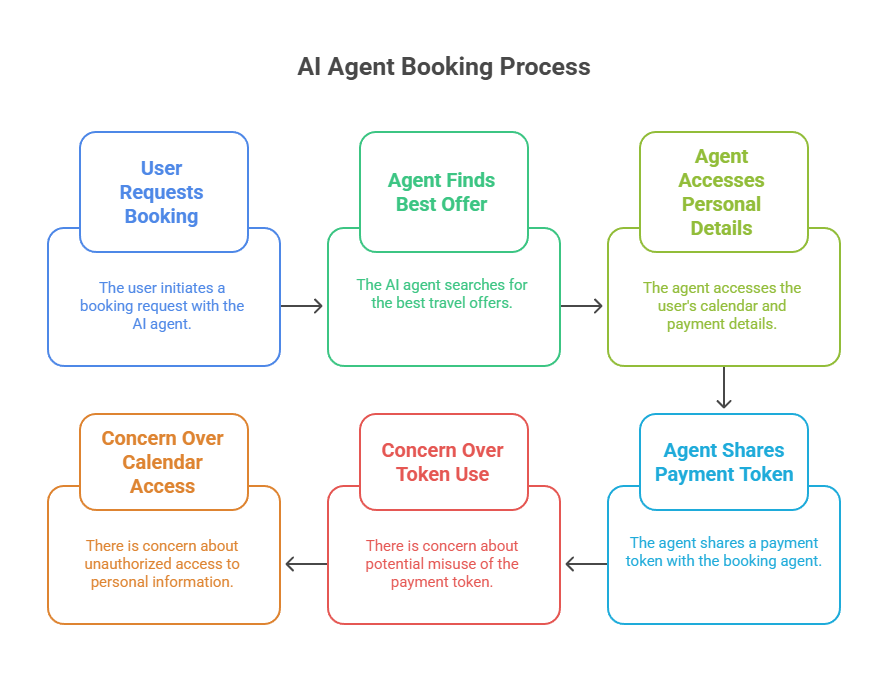
Figure 1: Example booking workflow in A2A illustrating overprivilege, long token lifetimes, and absence of explicit user consent.
Proposed Enhancements
To address these vulnerabilities, the paper proposes specific protocol-level enhancements:
- Token Management:
- Implement short-lived tokens (e.g., 30 seconds to 5 minutes) for sensitive operations to mitigate unauthorized reuse and extend least-privilege access restrictions.
- Strong Customer Authentication (SCA):
- Integrate SCA mechanisms such as multi-factor authentication to protect high-risk operations, aligning the protocol with industry security standards.
- Granular Access Scopes:
- Define precise permission scopes for each token, limiting access to necessary information and reducing potential for privilege escalation.
- Explicit User Consent:
- Establish protocol states that enforce explicit, user-approved consent before the exchange of sensitive information, enhancing user control.
- Direct Data Transfer:
- Enable direct user-to-service data channels to prevent unnecessary data exposure to intermediary agents.
- Regulatory Compliance:
- Align enhancements with privacy regulations such as GDPR and financial standards like PSD2 for secure, compliant operations in multi-agent systems.
These protocol enhancements address both structural security gaps and compliance requirements, aiming to build trust and protect user data in sensitive multi-agent environments.
Empirical Evaluation and Results
An empirical evaluation was conducted, focusing on the effectiveness of the proposed security enhancements under adversarial conditions. Experimental designs emphasized prompt injection attacks—commonly exploited vulnerabilities where malicious prompts trick agents into leaking sensitive information. The results demonstrated that the A2A protocol enhanced with specified controls effectively prevented data leakage when compared to standard practices.
Summary of Findings:
- The enhanced A2A protocol maintained zero leakage in controlled prompt injection attempts, substantiating the robustness of the proposed security framework.
- Minor performance trade-offs, such as increased response times, were within acceptable operational limits, demonstrating no significant latency impact.
Conclusion
The research conducted highlights the critical need for robust security enhancements in communication protocols for AI-driven multi-agent systems. By adopting the proposed enhancements, the A2A protocol transitions towards a framework that secures sensitive interactions, maintains user trust, and ensures compliance with stringent regulatory requirements. This sets a foundational precedent for evolving secure multi-agent systems that guard against unintended harms in increasingly autonomous environments.
Further adoption of these improvements within decentralized AI systems would not only mitigate current security challenges but foster a sustainable path towards secure, scalable, and trustworthy agent ecosystems.