- The paper establishes a Θ(log² n) query complexity for Tarski(n,4) by matching lower and upper bounds using a novel framework.
- It introduces safe partial-information functions that efficiently shrink candidate sets and improve generic bounds for fixed k.
- The work deepens our understanding of fixed point computation in monotone lattices, impacting search problems in logic, verification, and economics.
The Query Complexity of Tarski Fixed Points: A Structural Characterization
Introduction
The paper "The Mystery Deepens: On the Query Complexity of Tarski Fixed Points" (2604.00268) delivers new insights into the query complexity of finding fixed points of monotone functions over finite lattices, specifically for the Tarski fixed point problem on the k-dimensional grid [n]k. This work resolves the precise query complexity for dimension k=4, demonstrating that Θ(log2n) queries suffice and are necessary, matching previous lower bounds. Further, it introduces a highly-structured framework based on safe partial-information functions to both advance upper bounds for higher dimensions and illuminate the deep combinatorial nature of these fixed point computations.
Context and Motivation
Tarski's fixed point theorem remains a central result in lattice theory and has rich implications for logic, formal verification, game theory, and economics. In computational terms, the complexity of finding such fixed points informs our understanding of several major total search problems, including those lying at the intersection of NP∩coNP but not known to be in P (e.g., parity games and stochastic mean-payoff games).
Prior approaches—ranging from straightforward iteration to iterative binary search—yielded O(nk) or O(logkn) upper bounds, with stronger lower bounds only recently established for small k. Fearnley et al. (2022) demonstrated surprising structural collapses in certain dimensions, notably showing that for k=3, the query complexity drops to Θ(log2n), shattering the expectation that the exponent must grow linearly with [n]k0.
However, for [n]k1, a gap remained: the lower bound was [n]k2 and the best known upper bound [n]k3. The present paper resolves this ambiguity for [n]k4, and improves bounds for all constant [n]k5, utilizing new algorithmic and structural techniques.
Core Contributions
Optimal Query Complexity for [n]k6
The primary technical contribution is an [n]k7-query algorithm for [n]k8, matching the [n]k9 lower bound and thus tightly characterizing the complexity for k=40. This closes a previously open case, showing that for k=41 the query complexity remains at k=42.
Improved Generic Bounds
Extending beyond k=43, the authors refine the best-known upper bound for constant k=44 from k=45 to k=46 for general k=47. This leverages a composition principle for their new algorithmic framework, suggesting further polylogarithmic improvements may be possible for higher dimensions.
A major conceptual contribution is the development and deployment of safe partial-information (PI) functions as an analytic and algorithmic tool. While the idea of safe PI functions originated in reductions relevant to unique fixed point problems, this work is the first to harness them directly for algorithm design. With this, the analysis and search for fixed points becomes a combinatorial game—termed the safe PI function game—where structure and inference play dominant roles, offering new levers for progress.
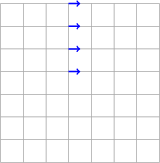
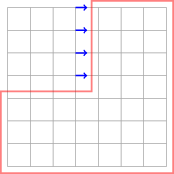
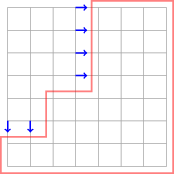
Figure 1: An illustration of information inferred via monotonicity from a query k=48, as captured by monotone PI functions.
Candidate Sets and Combinatorial Trimming
Central to the improved bounds is an intricate characterization of candidate solution sets compatible with accumulated partial information. Unlike naive set-counting approaches, the new definition of candidate sets crucially exploits the structure revealed by safe PI functions. The framework guarantees that after each batch of queries, a constant factor reduction in candidate set size can be enforced, which underlies the k=49 query bound.
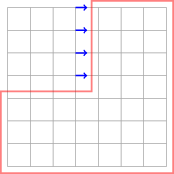
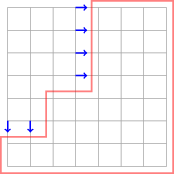
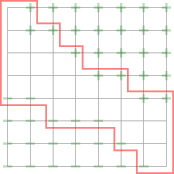
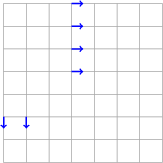
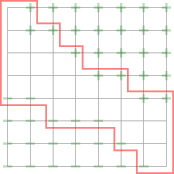
Figure 2: Visualization of a candidate set after querying Θ(log2n)0, showing the combinatorial trimming enabled by accumulated inferences.
Technical Insights
The methodology is rooted in a round-based query model, where the algorithm interacts with the unknown monotone function by successively issuing queries, refining its partial-information function at each step. The safe PI function formalism allows the algorithm to encode, propagate, and infer monotonicity-driven facts beyond direct query answers, broadly tightening the possible fixed point locations.
Key technical steps include:
- Monotone Partial-Information Functions: Encoding the closure of information inferred via monotonicity as a PI function whose symbol lattice tracks knowns, possible intervals, and indeterminacy.
- Safe PI Functions: Enriching PI functions by requiring that every slice (subgrid with fixed coordinates) still has at most one fixed point, enforcing a global structural constraint on feasible extensions.
- Candidate Set Construction: Advanced combinatorial techniques are used to construct and update sets Θ(log2n)1 of possible solutions, ensuring they shrink rapidly under carefully selected queries ("constant fraction reduction").
- Decomposition Theorem: For arbitrary Θ(log2n)2, candidate set reductions for lower dimensions can be composed using a slice-and-reduce approach, leading to the improvements in the exponent of the generic upper bound.
An important geometric lemma determines that, for subsets of Θ(log2n)3, one can always find a query point that splits the candidate set into well-balanced regions, guaranteeing progress at every stage.
Numerical and Structural Implications
The algorithm achieves the following:
- For Θ(log2n)4, both upper and lower bounds are sharp: query complexity is Θ(log2n)5.
- For constant Θ(log2n)6, the upper bound is improved to Θ(log2n)7 queries.
- For the relaxed Θ(log2n)8 problem (allowing an "oriented" solution), a Θ(log2n)9 exponent replaces the previous NP∩coNP0 in the upper bound, further bridging the remaining gaps.
No explicit time efficiency is claimed: the algorithms as described depend on combinatorial or brute-force enumeration that may be computationally intensive, focusing squarely on query efficiency.
The work also provides a pathway hinting that, up to small polynomial losses in NP∩coNP1, the query complexity for fixed NP∩coNP2 could remain NP∩coNP3, a point not foreclosed by existing lower bounds.
Theoretical and Algorithmic Implications
This work unveils the surprisingly rich structure inherent in fixed point search within monotone lattices. Safe PI functions abstract the type of logical closure seen in formal verification and model checking, potentially linking these complexity insights to structural results in logic (e.g., NP∩coNP4-calculus) and game-theoretic equilibrium computation.
Practically, the framework paves the way for more advanced fixed point and equilibrium finding algorithms in verification and economic modeling, where the black-box oracle model reflects limited access or high cost to solution space exploration.
The decomposition and candidate set techniques may be transferable to related search problems—such as contraction mappings or unique equilibrium settings—where inductive combinatorial structure is key.
Future Directions
The safe PI function framework creates a foundation for further tightening the query complexity of Tarski fixed points. Primary open challenges include:
- Extending the structural trimming approach beyond NP∩coNP5, potentially proving NP∩coNP6 sufficiency for all fixed NP∩coNP7.
- Developing fully time-efficient (not just query-efficient) algorithms under this framework.
- Illuminating connections to NP∩coNP8, NP∩coNP9, and other subclasses of TFNP, especially for classes of fixed point problems that avoid the exponential lower bounds observed in, for example, Brouwer settings.
Conclusion
This paper delivers a definitive characterization of the query complexity for the Tarski fixed point problem up to dimension four, unifying and extending prior lines of attack and establishing a new analytic toolkit for the domain. The introduction and direct use of safe partial-information functions not only advances upper bounds, but also deepens our understanding of the combinatorial landscape underlying fixpoint computation. The methods and results presented are likely to influence both the structural theory and the algorithmic practice of search problems in lattices, games, and beyond.