- The paper offers a comparative security analysis of MCP, A2A, Agora, and ANP protocols by highlighting their design-induced vulnerabilities.
- It employs a lifecycle-aware qualitative risk assessment based on NIST SP 800-30 to evaluate risks during creation, operation, and update phases.
- The study emphasizes the need for cryptographic identity anchoring, token rotation, and coordinated version management to mitigate systemic security threats.
Security Threat Modeling for Emerging AI-Agent Protocols: A Comparative Analysis of MCP, A2A, Agora, and ANP
Context and Motivation
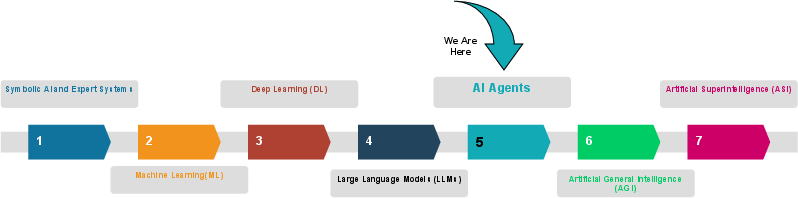
The transition from passive, standalone LLMs to agentic, autonomous AI systems introduces sophisticated inter-agent collaboration, tool invocation, and environmental integration. The proliferation of new communication protocols—including Model Context Protocol (MCP), Agent2Agent (A2A), Agora, and Agent Network Protocol (ANP)—addresses scalability, interoperability, and structured coordination across diverse environments. However, rapid protocol adoption exposes systems to substantial security challenges. Protocol-centric risk modeling, standardized threat taxonomies, and lifecycle-aware qualitative risk assessments remain largely absent, making the study of security exposure and systemic vulnerabilities critical.
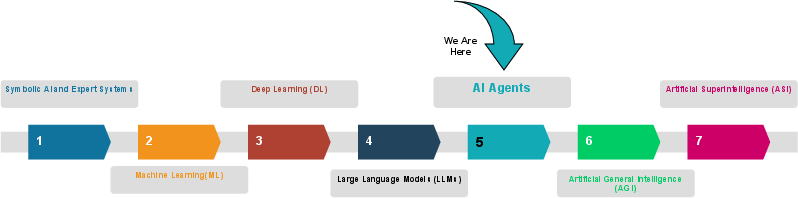
Figure 1: A visual representation of the evolution of artificial intelligence.
Protocol Architectures and Trust Models
Model Context Protocol (MCP)
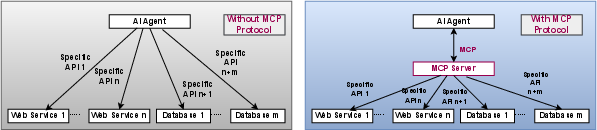
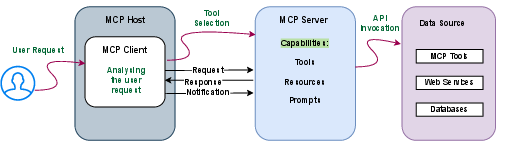
MCP, introduced by Anthropic, is platform-agnostic, open-source, and enables bidirectional agent-tool connectivity. Its architecture comprises the host (AI application), client (communication mediator), and server (resource manager), each with lifecycle stages: creation, operation, and update. The protocol exposes agents to tools and resources, supporting both structured and ad-hoc workflows, but lacks cryptographic binding between tool and provider identities, relying on name/description-based resolution.
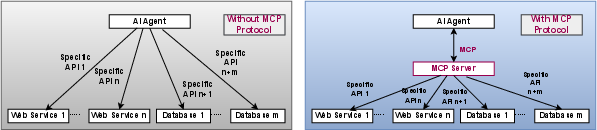
Figure 2: Role of MCP in connection of AI agent with external resources.
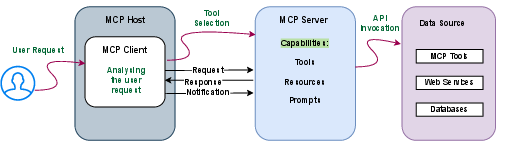
Figure 3: MCP Architecture and workflow.
Agent2Agent (A2A) Protocol
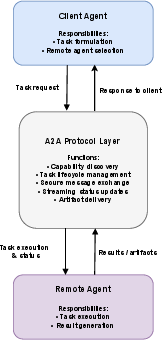
A2A, contributed by Google and partners, targets secure, cross-organization agent interaction with OAuth 2.0 and JWT for mutual authentication. The protocol’s Agent Card mechanism standardizes capability advertisement in JSON format and supports synchronous/asynchronous task execution, artifact-based result handling, and structured communication. However, token scoping and expiration are not consistently enforced, resulting in privilege escalation vectors and replay attack feasibility.
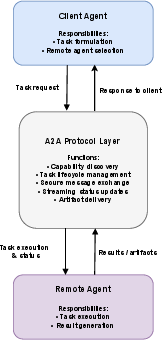
Figure 4: High-level architecture and interaction workflow of A2A.
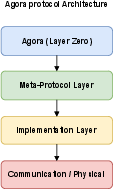
Agora
Agora addresses the agent communication trilemma (versatility, efficiency, portability) with protocol documents (PDs) enabling autonomous negotiation and adaptation, externalizing communication logic out of the agent. The protocol relies on decentralized storage and natural language for negotiation, which allows dynamic interoperability but increases ambiguity and absence of formal trust anchors.
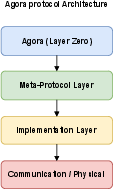
Figure 5: A conceptual layered interpretation of the Agora protocol.
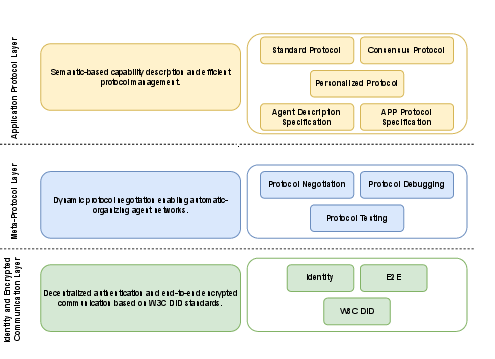
Agent Network Protocol (ANP)
ANP proposes a three-layered architecture integrating W3C Decentralized Identifiers (DIDs), meta-protocols for protocol negotiation, and application protocols for discovery and execution. Its design targets large-scale IoA, emphasizing encrypted communication and decentralized identity, but introduces new trust fragmentation risks, Sybil vulnerability, and onboarding exploitation through open registration.
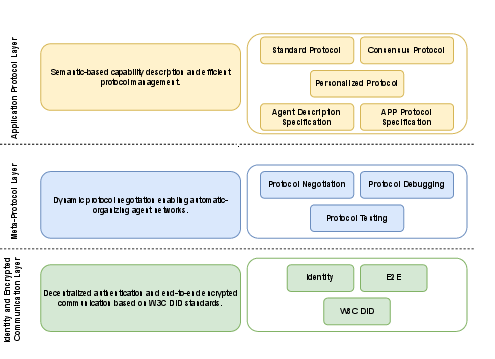
Figure 6: Layered architecture of ANP.
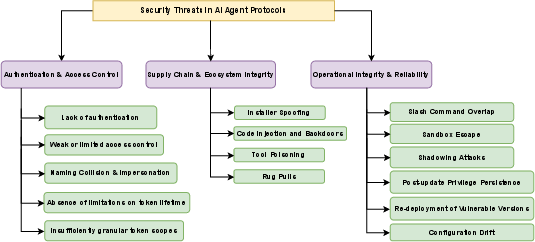
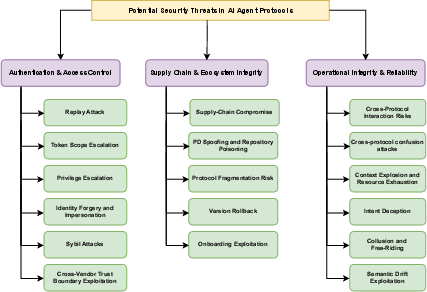
Threat Taxonomies and Vulnerability Surfaces
A comprehensive taxonomy is presented, categorizing threats across three domains: authentication/access control, supply chain/ecosystem integrity, and operational integrity/reliability. Key vulnerabilities include lack of authentication, coarse access control, naming collision/impersonation, overly broad token scopes, installer spoofing, backdoors, tool poisoning, rug pulls, command overlap, sandbox escape, privilege persistence, version rollback, configuration drift, and semantic drift exploitation.
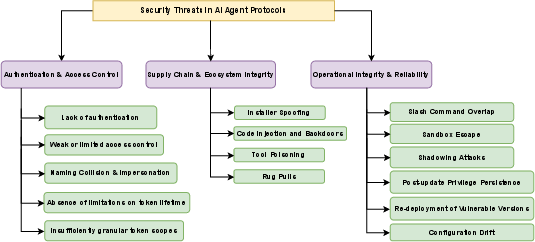
Figure 7: Taxonomy of security threats in AI agent communication protocols.
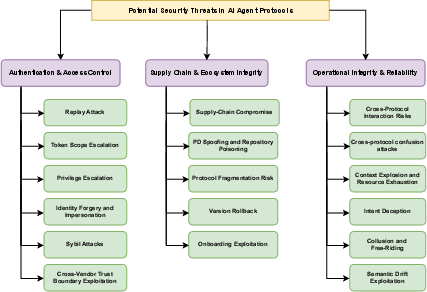
Figure 8: Taxonomy of potential security threats in AI agent communication protocols.
Authentication and Access Control
Protocols exhibit significant weaknesses in identity verification, session freshness, token scoping, and cross-vendor trust. Replay, privilege escalation, Sybil, and impersonation attacks are feasible due to absent global namespace enforcement, non-cryptographic identity binding, and weak onboarding.
Supply Chain and Ecosystem Integrity
Open-source and community-driven design in MCP, decentralized PD propagation in Agora, and ad-hoc onboarding in ANP permit installer spoofing, backdoor persistence, tool poisoning, repository poisoning, version rollback, protocol fragmentation, and supply chain compromise.
Operational Integrity and Reliability
Runtime threats include command ambiguity, sandbox escape, credential persistence post-update, cross-protocol confusion, context explosion, intent deception, collusion/free-riding, and semantic drift, especially pronounced in protocols supporting dynamic negotiation or ad-hoc tool invocation.
Qualitative Risk Assessment Framework
The study introduces a lifecycle-aware qualitative risk assessment adopting NIST SP 800-30 principles, evaluating risk as product of likelihood and impact across creation/configuration, operation, and update phases:
- Creation: MCP and Agora show high risk due to weak enrollment and identity assurance; A2A presents medium risk owing to limited OAuth2/JWT authentication; ANP delivers low-median risk via cryptographically strong DIDs.
- Operation: MCP and Agora remain highly vulnerable (code signing absence, dynamic PD negotiation); A2A is moderate (lack of semantic validation, token persistence); ANP shows mixed results (strong identity, high dependency risk).
- Update: All protocols manifest medium-high risk, especially from stale credentials, poisoned updates, and version drift.
Risk matrices systematically confirm none of the protocols provide comprehensive protection. Early-stage vulnerabilities persist, runtime behaviors propagate implicit trust, and update-phase weaknesses facilitate systemic compromise.
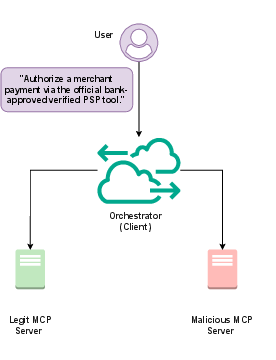
An empirical evaluation concretizes the hypothesized risk due to absent tool-provider binding. In a multi-server MCP environment, tool resolution is performed via heuristics rather than cryptographic means. When identical tool names are registered, orchestrator selection policies (first-match, best-match, random tie-break) result in consistent misbinding to attacker-controlled servers, evidenced by violation rates up to $1.0$ under malicious ordering and $0.52$ under random tie-breaking. This demonstrates that ambiguous tool identity translates to concrete, reproducible security failures.
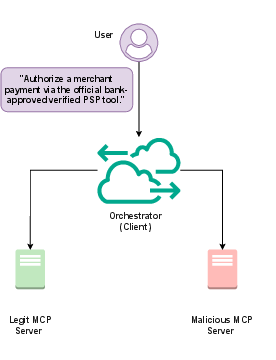
Figure 9: Experimental Architecture for MCP Tool Identity Ambiguity Evaluation.
Implications and Future Directions
The analysis shows MCP, A2A, Agora, and ANP are not yet suitable for high-assurance, cross-organizational, or enterprise workflows without substantial extension. Practical implications include the infeasibility of trust-based protocol composition, requisite for AGI/ASI-grade ecosystems. Theoretical consequences involve the unsuitability of decentralized, natural language-based negotiation in the absence of global identity enforcement and version control.
Future protocol design must address:
- Mandatory cryptographic identity anchoring and signed enrollment
- Ephemeral credential usage and protocol-level token rotation
- Global registry-based uniqueness enforcement and namespace isolation
- Coordinated version management and patch revocation mechanisms
- Cross-protocol interoperability and uniform validation semantics
Privacy-centric risk assessment, mitigation strategies, and systemic hardening must underpin subsequent research.
Conclusion
This work formalizes the security threat modeling space for emerging AI agent communication protocols, integrating documented threat vectors with architectural projections and empirical evaluation. Results underscore shared design-induced risk surfaces and protocol-specific vulnerabilities, providing actionable guidance for secure deployment and standardization. As agentic ecosystems expand, protocol-centric security frameworks must evolve in tandem to support trustworthy, scalable, and interoperable AI-driven systems.