LLMPot: Dynamically Configured LLM-based Honeypot for Industrial Protocol and Physical Process Emulation
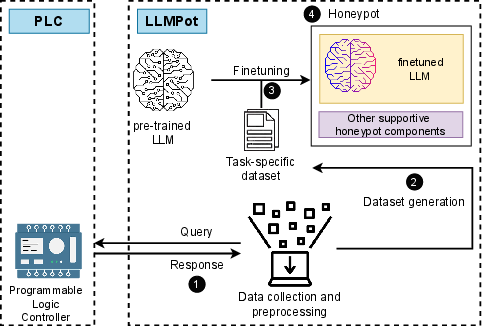
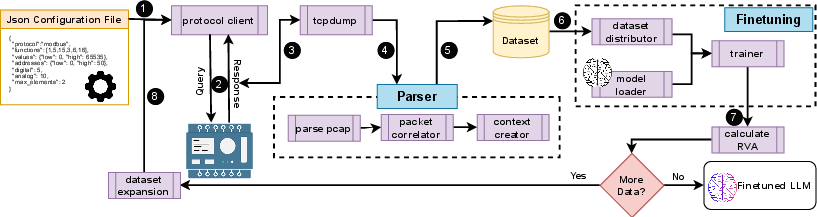
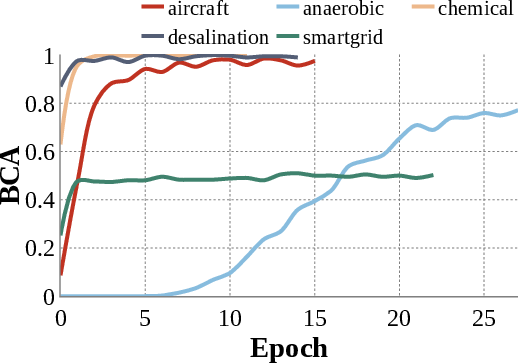
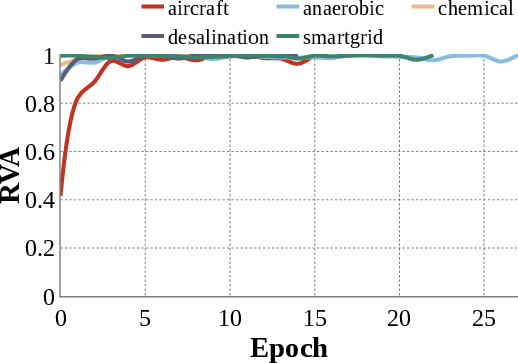
Abstract: Industrial Control Systems (ICS) are extensively used in critical infrastructures ensuring efficient, reliable, and continuous operations. However, their increasing connectivity and addition of advanced features make them vulnerable to cyber threats, potentially leading to severe disruptions in essential services. In this context, honeypots play a vital role by acting as decoy targets within ICS networks, or on the Internet, helping to detect, log, analyze, and develop mitigations for ICS-specific cyber threats. Deploying ICS honeypots, however, is challenging due to the necessity of accurately replicating industrial protocols and device characteristics, a crucial requirement for effectively mimicking the unique operational behavior of different industrial systems. Moreover, this challenge is compounded by the significant manual effort required in also mimicking the control logic the PLC would execute, in order to capture attacker traffic aiming to disrupt critical infrastructure operations. In this paper, we propose LLMPot, a novel approach for designing honeypots in ICS networks harnessing the potency of LLMs. LLMPot aims to automate and optimize the creation of realistic honeypots with vendor-agnostic configurations, and for any control logic, aiming to eliminate the manual effort and specialized knowledge traditionally required in this domain. We conducted extensive experiments focusing on a wide array of parameters, demonstrating that our LLM-based approach can effectively create honeypot devices implementing different industrial protocols and diverse control logic.
- CODESYS Automation Platform. https://www.codesys.com/products/codesys-engineering/automation-platform.html.
- HAProxy. https://www.haproxy.com/.
- OSCAT Basic Library Documentation. http://www.oscat.de/images/OSCATBasic/oscat_basic333_en.pdf.
- PyTorch Lightning Documentation. https://lightning.ai/docs/pytorch/stable/.
- Siemens Official Website. https://new.siemens.com/global/en.html.
- WAGO Official Website. https://wago.com/global/.
- Gpt-4 technical report. arXiv preprint arXiv:2303.08774 (2023).
- Towards high-interaction virtual ics honeypots-in-a-box. In Proceedings of the 2nd ACM Workshop on Cyber-Physical Systems Security and Privacy (2016), pp. 13–22.
- Minicps: A toolkit for security research on cps networks. In Proceedings of the First ACM workshop on cyber-physical systems-security and/or privacy (2015), pp. 91–100.
- Benjamin Allévy. Beanie - asynchronous python odm (object document mapper) for mongodb. https://github.com/roman-right/beanie. Last accessed: April 27, 2024.
- Numerical Analysis, 10th ed. Cengage Learning, Boston, MA, 2016.
- Cryplh: Protecting smart energy systems from targeted attacks with a plc honeypot. In Smart Grid Security: Second International Workshop, SmartGridSec 2014, Munich, Germany, February 26, 2014, Revised Selected Papers 2 (2014), Springer, pp. 181–192.
- A survey of honeypot research: Trends and opportunities. In 2015 10th international conference for internet technology and secured transactions (ICITST) (2015), IEEE, pp. 208–212.
- Dipot: A distributed industrial honeypot system. In Smart Computing and Communication: Second International Conference, SmartCom 2017, Shenzhen, China, December 10-12, 2017, Proceedings 2 (2018), Springer, pp. 300–309.
- Icspot: A high-interaction honeypot for industrial control systems. In 2022 International Symposium on Networks, Computers and Communications (ISNCC) (2022), IEEE, pp. 1–4.
- DNP Users Group. Dnp3 protocol specification. Tech. rep., DNP Users Group, Year. Last accessed: April 27, 2024.
- Docker, Inc. Docker - build, share, and run any app, anywhere. https://www.docker.com/. Last accessed: April 27, 2024.
- EtherCAT Technology Group. Ethercat technology. https://www.ethercat.org/. Accessed: April 27, 2024.
- GNU Project. Gnu wget - the non-interactive network downloader. https://www.gnu.org/software/wget/. Last accessed: April 27, 2024.
- Generative adversarial nets. Advances in neural information processing systems 27 (2014), 2672–2680.
- Long short-term memory. Supervised sequence labelling with recurrent neural networks (2012), 37–45.
- Reducing the dimensionality of data with neural networks. Science 313, 5786 (2006), 504–507.
- Scada honeypots: An in-depth analysis of conpot. In 2016 IEEE conference on intelligence and security informatics (ISI) (2016), IEEE, pp. 196–198.
- Threat analysis of blackenergy malware for synchrophasor based real-time control and monitoring in smart grid. In 4th International Symposium for ICS & SCADA Cyber Security Research 2016 (2016), BCS Learning & Development.
- Shape: A honeypot for electric power substation. Journal of telecommunications and information technology, 4 (2015), 37–43.
- Langner, R. Stuxnet: Dissecting a cyberwarfare weapon. IEEE Security & Privacy 9, 3 (2011), 49–51.
- Lannister, C. IHS GitHub Repository. https://web.archive.org/web/20220522113148/https://github.com/CarlosLannister/IHS.
- Rethinking the honeypot for cyber-physical systems. IEEE Internet Computing 20, 5 (2016), 9–17.
- Honeyplc: A next-generation honeypot for industrial control systems. In Proceedings of the 2020 ACM SIGSAC Conference on Computer and Communications Security (2020), pp. 279–291.
- Hybrid warfare and cyber effects in energy infrastructure. Connections 18, 1/2 (2019), 93–110.
- Modbus Organization. Modbus protocol specification. https://www.modbus.org/docs/Modbus_Application_Protocol_V1_1b3.pdf. Accessed: April 27, 2024.
- MongoDB, Inc. Mongodb - the most popular database for modern applications. https://www.mongodb.com/. Last accessed: April 27, 2024.
- Moore, C. Detecting ransomware with honeypot techniques. In 2016 Cybersecurity and Cyberforensics Conference (CCC) (2016), IEEE, pp. 77–81.
- Nmap in the enterprise: your guide to network scanning. Elsevier, 2011.
- Pallets. Flask - python web framework. https://flask.palletsprojects.com/. Last accessed: April 27, 2024.
- Active defence using an operational technology honeypot. In 11th International Conference on System Safety and Cyber-Security (SSCS 2016) (2016), IET, pp. 1–6.
- PROFINET International. Profinet technology. https://www.profibus.com/technology/profinet/. Accessed: April 27, 2024.
- Provos, N. Honeyd-a virtual honeypot daemon. In 10th dfn-cert workshop, hamburg, germany (2003), vol. 2, p. 4.
- {{\{{ICSPatch}}\}}: Automated vulnerability localization and {{\{{Non-Intrusive}}\}} hotpatching in industrial control systems using data dependence graphs. In 32nd USENIX Security Symposium (USENIX Security 23) (2023), pp. 6861–6876.
- Real Time Automation. Real time automation: Ethernet/ip. https://www.rtautomation.com/technologies/ethernetip/. Last accessed: April 27, 2024.
- Sheldon, R. A First Course in Probability. Pearson, 2018.
- Shodan. Shodan - the search engine for internet-connected devices. https://www.shodan.io/. Last accessed: April 27, 2024.
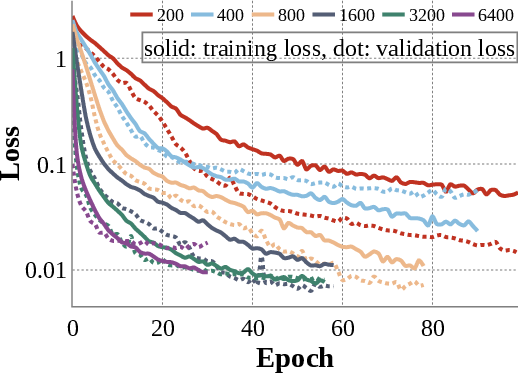
- Neuralpot: An industrial honeypot implementation based on deep neural networks. In 2020 IEEE Symposium on Computers and Communications (ISCC) (2020), IEEE, pp. 1–7.
- The OpenSSL Project. Openssl - the open source toolkit for ssl/tls. https://www.openssl.org/. Last accessed: April 27, 2024.
- The Tcpdump Group. tcpdump - a powerful command-line packet analyzer. https://www.tcpdump.org/. Last accessed: April 27, 2024.
- Llama: Open and efficient foundation language models. arXiv preprint arXiv:2302.13971 (2023).
- Weiler, N. Honeypots for distributed denial-of-service attacks. In Proceedings. Eleventh IEEE International Workshops on Enabling Technologies: Infrastructure for Collaborative Enterprises (2002), IEEE, pp. 109–114.
- The gaspot experiment: Unexamined perils in using. blackhat (2015).
- Wireshark. S7 communication protocol. https://wiki.wireshark.org/S7comm. Accessed: April 27, 2024.
- Transformers: State-of-the-art natural language processing. In Proceedings of the 2020 conference on empirical methods in natural language processing: system demonstrations (2020), pp. 38–45.
- S7commtrace: A high interactive honeypot for industrial control system based on s7 protocol. In Information and Communications Security: 19th International Conference, ICICS 2017, Beijing, China, December 6-8, 2017, Proceedings 19 (2018), Springer, pp. 412–423.
- Byt5: Towards a token-free future with pre-trained byte-to-byte models. Transactions of the Association for Computational Linguistics 10 (2022), 291–306.
Paper Prompts
Sign up for free to create and run prompts on this paper using GPT-5.
Top Community Prompts
Collections
Sign up for free to add this paper to one or more collections.