- The paper introduces a tripartite taxonomy for agent infrastructure encompassing attribution, interaction, and response to ensure safe AI operations.
- It details methodologies for identity binding, secure agent channels, and incident rollback mechanisms, highlighting technical challenges and design trade-offs.
- It emphasizes the need for interoperable and legally aligned systems to manage the accountability and governance of autonomous, agentic AI in complex environments.
Infrastructure for AI Agents: An Analytical Summary
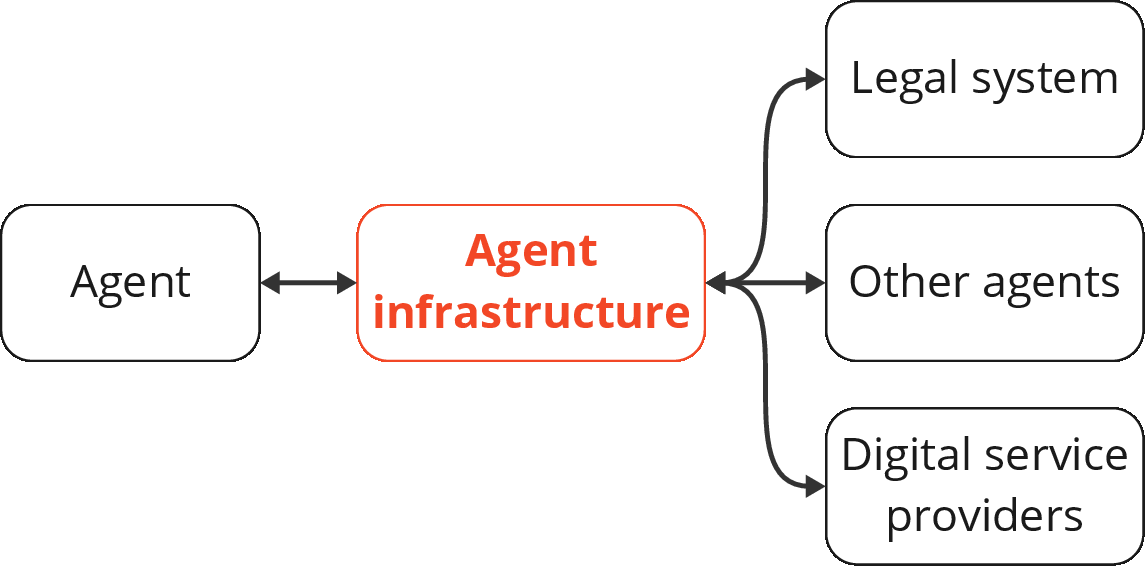
The paper presents a systematic analysis of the requirements and design principles for the infrastructure necessary to support ecosystems of increasingly capable AI agents. Rejecting the sufficiency of system-level interventions alone, the authors develop the concept of "agent infrastructure": technical systems and shared protocols external to agents, designed to mediate and regulate their interactions with other entities and institutional frameworks. The analysis is motivated by both the opportunities and significant governance gaps posed by recently emergent, highly capable agentic AI, which can autonomously plan and execute actions in open-ended environments. The work proposes a tripartite functional taxonomy for agent infrastructure—attribution, interaction, and response—and surveys concrete mechanisms for each, drawing connections to extant regulatory and technical infrastructure in other domains.
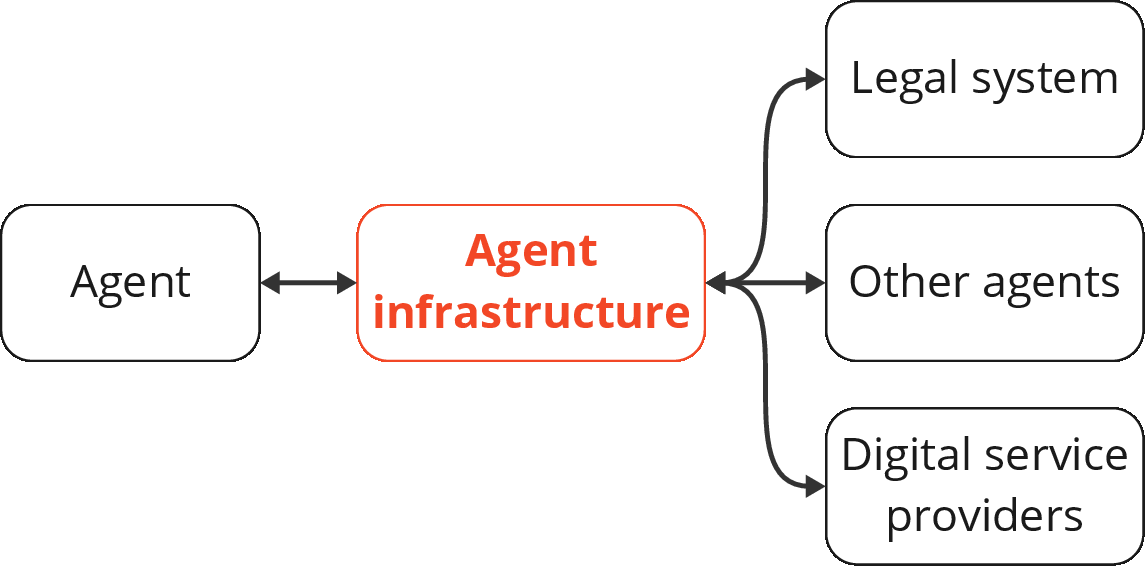
Figure 1: Agent infrastructure mediates interactions of AI agents with digital, organizational, legal, and economic environments via technical and protocol-level systems.
Functional Taxonomy of Agent Infrastructure
The central thesis is that the operationalization of safe, reliable, and beneficial agentic AI requires infrastructure external to any given agent, analogous to the critical role of protocols like HTTPS or TCP for the Internet. This agent infrastructure is required to enable three key functions:
- Attribution: Mechanisms for linking agent actions and properties to distinct agent instances, users, or other actors.
- Interaction: Protocols and systems to shape, constrain, and instrument the digital interactions of agents, both between agents and with external systems.
- Response: Systems for detecting, investigating, and remediating harmful agent behavior, including incident detection, reporting, and rollback capabilities.
The taxonomy reflects a judgment that neither alignment techniques nor traditional digital infrastructure (e.g., authentication, general resource monitoring) can support the combined requirements of attribution, credible recourse, agency management, and incident response at scale.
Attribution: Identity, Certification, and IDs
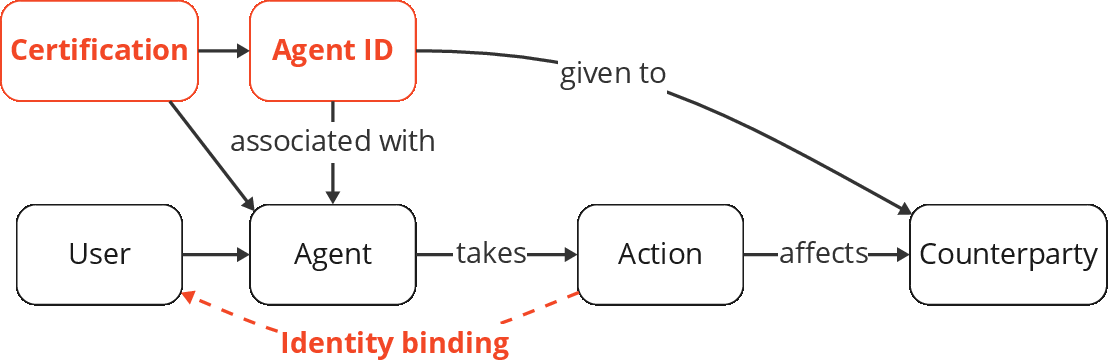
Identity Binding
A core challenge is reconciling the lack of legal status or personhood for agents with the need to allocate accountability. The paper defines identity binding as (1) authenticating an identity (user, organization, overseer, etc.), and (2) binding that identity to a particular agent or set of actions. This enables accountability and applies existing legal regimes to agent-driven actions. Concrete technical mechanisms include:
Key open problems include scalable mechanisms for agent-agent identity assurance, privacy-robust identity disclosure policies, and incentive-compatible adoption by platforms and users. Limitations stem from privacy risk, potential for abuse (e.g., doxxing, targeting), and the difficulty of binding identities to ephemeral or highly composable agent instances. The tradeoff between traceability and privacy is foregrounded, with the paper noting the need for proportional, context-dependent application.
Certification
Certification aims to assure counterparties of behavioral and operational agent properties via digitally signed claims. Example claims include:
- Tools accessible by the agent, e.g., cryptographically enforceable commitment devices.
- Boundaries on autonomy and overrides by oversight mechanisms.
- Data handling practices (e.g., protocols for forgetting sensitive information).
Technical open questions pertain to verifiable cryptographic credentials, key management, certificate revocation strategies, and the interface of certification with post-deployment adversarial adaptation and transformation. Adoption likely depends on sectoral requirements (health, finance, public sector), and obstacles include verification of dynamic or behavioral claims and incentives for certification authorities. The well-known pitfalls of "adverse selection" in self-issued digital certificates (e.g., the history of lax privacy labels) are explicitly noted.
Agent IDs
Agent IDs are unique, persistent (yet potentially privacy-preserving) identifiers, designed to support cross-platform incident response and targeted sanctions—for instance, in tracing a distributed Sybil attack performed via many ephemeral sub-agents. The design of such IDs must address spoofing resistance (via cryptography), privacy (linkability restrictions), and the ability to anchor certificates and attribute actions across digital domains. The authors propose that selective requirements for IDs (e.g., in high-stakes environments or for agent-to-agent protocols) can provide robust infrastructure for forensics and recourse.
Interaction: Channels, Oversight, Communication, and Commitments
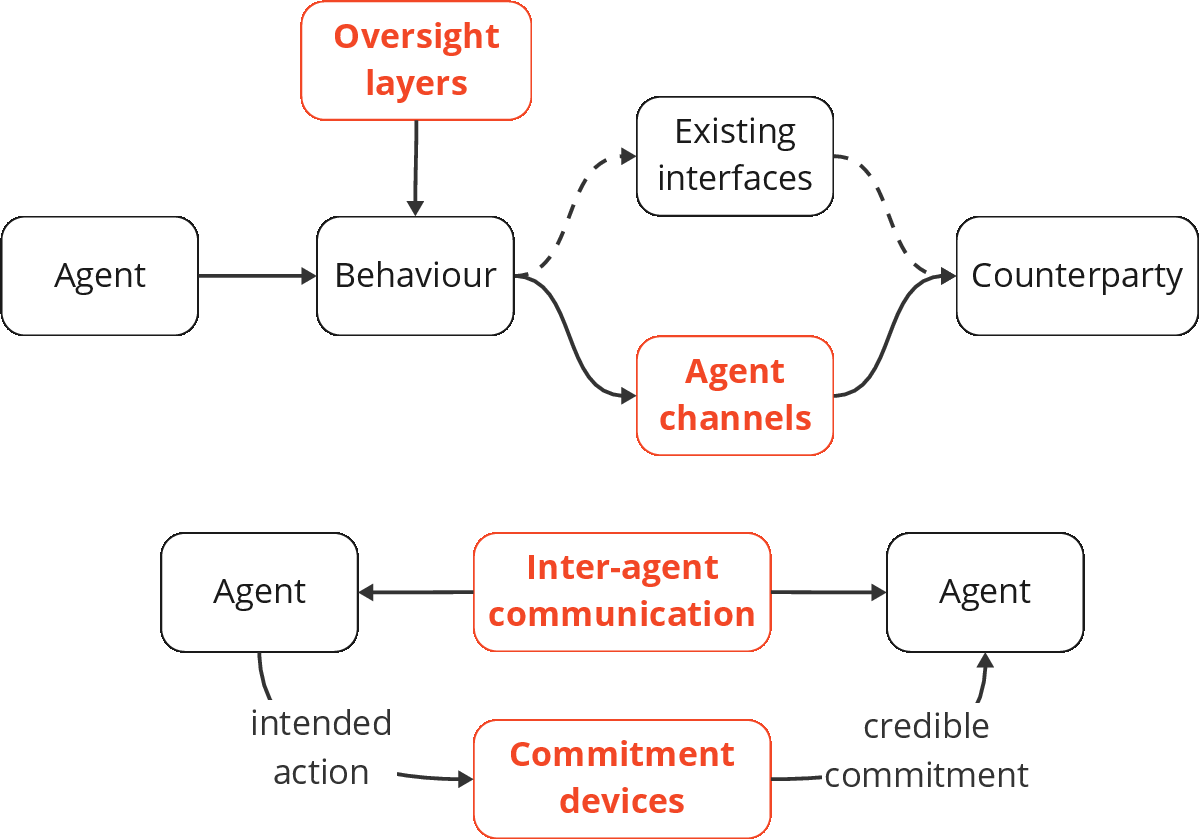
The interaction layer of agent infrastructure comprises mechanisms that modulate the affordances, risks, and social contracts of agent-environment and agent-agent engagements.
Agent Channels
The concept of agent channels—network or API-level separation between agent-originated and human-originated traffic—is introduced as a means to simplify monitoring, risk containment, and application of agent-specific security policies. This can be implemented at the software (specialized agent APIs, agent-optimized web interfaces) or network (dedicated IP space, network segmentation) layers. Adoption incentives include stricter rate-limiting, enhanced monitoring, and attack surface reduction (e.g., mitigations against prompt injection via simplified agent-focused APIs).
Oversight Layers
Oversight layers provide interruptible and inspectable execution for agents, via: (1) monitoring systems to flag anomalous or potentially harmful actions; and (2) UI/API affordances for human or automated approval/intervention. Analogous to approval chains in organizational processes, these layers generate explicit audit trails for actions and enable dynamic oversight—critical for financial transactions and high-consequence decisions. Practical challenges include preventing automation bias, designing interfaces for configurable oversight depth, and minimizing friction to avoid circumvention.
Inter-Agent Communication Protocols
Protocols for secure, authenticated, and optionally broadcast inter-agent communication are required for collaborative workflows, distributed negotiation, and multi-agent task allocation. The technical requirements include addressing (agent IDs), message confidentiality (e.g., mTLS), and abuse resistance (anti-spam). The interface with commitment devices (below) is noted, and strong analogies with multi-agent reinforcement learning communication protocols are drawn.
Commitment Devices
Commitment devices for agents are mechanisms—potentially including cryptographic escrow, on-chain contracts, or digitally enforced behavioral guarantees—that enable credible commitment to cooperative action or constraint adherence (e.g., not crossing capability/safety boundaries without peer signoff). Such devices are necessary to enable coordination games, public goods funding, and collective safety arrangements among potentially heterogeneous agent teams.
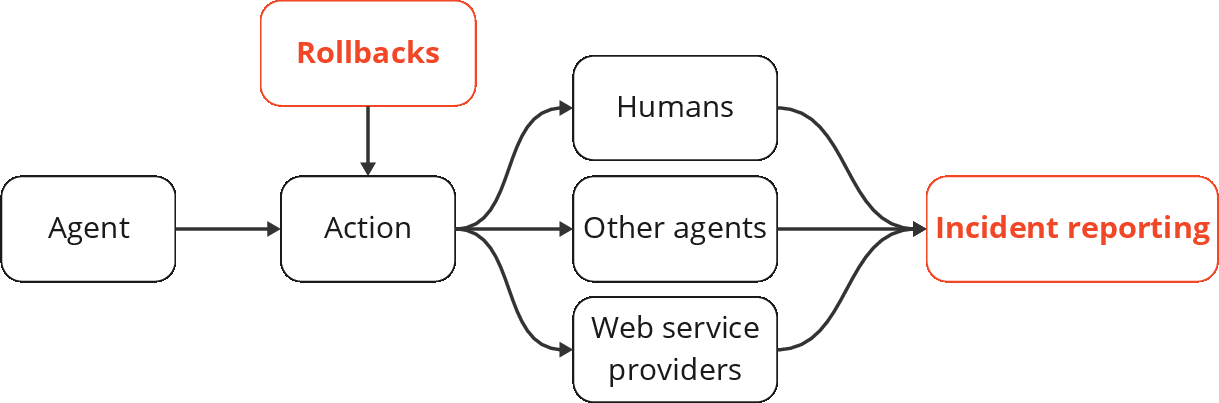
Response: Incident Reporting and Rollbacks
The response function of agent infrastructure deals with ex post detection and remediation of harmful or failed outcomes. Two main primitives are specified:
Incident Reporting
Incident reporting systems for agent ecosystems must support:
- High-volume, low-friction submission from both humans and agents for observed harms or failures;
- Filtering and aggregation to prevent Sybil/spam abuse—potentially via identity binding or credential requirements;
- Privacy-preserving routing of reports to appropriate authorities or stakeholders.
Current limitations in domain-specific incident reporting (e.g., model red-teaming frameworks, bug bounty programs) stem from lacking agent-oriented reporting schemas or mechanisms for linking incidents to specific agent instances or credentials.
Rollbacks
Rollback mechanisms provide standardized interfaces for invalidating or reversing agent actions (e.g., financial transactions, data modifications) and require both robust technical underpinnings (transactional consistency, audit trails) and clear policies for eligibility and invocation (who can trigger rollbacks, under what evidentiary conditions). The paper underscores that such mechanisms are only meaningful for digital (non-physical) actions and integrate closely with both certification and oversight layers.
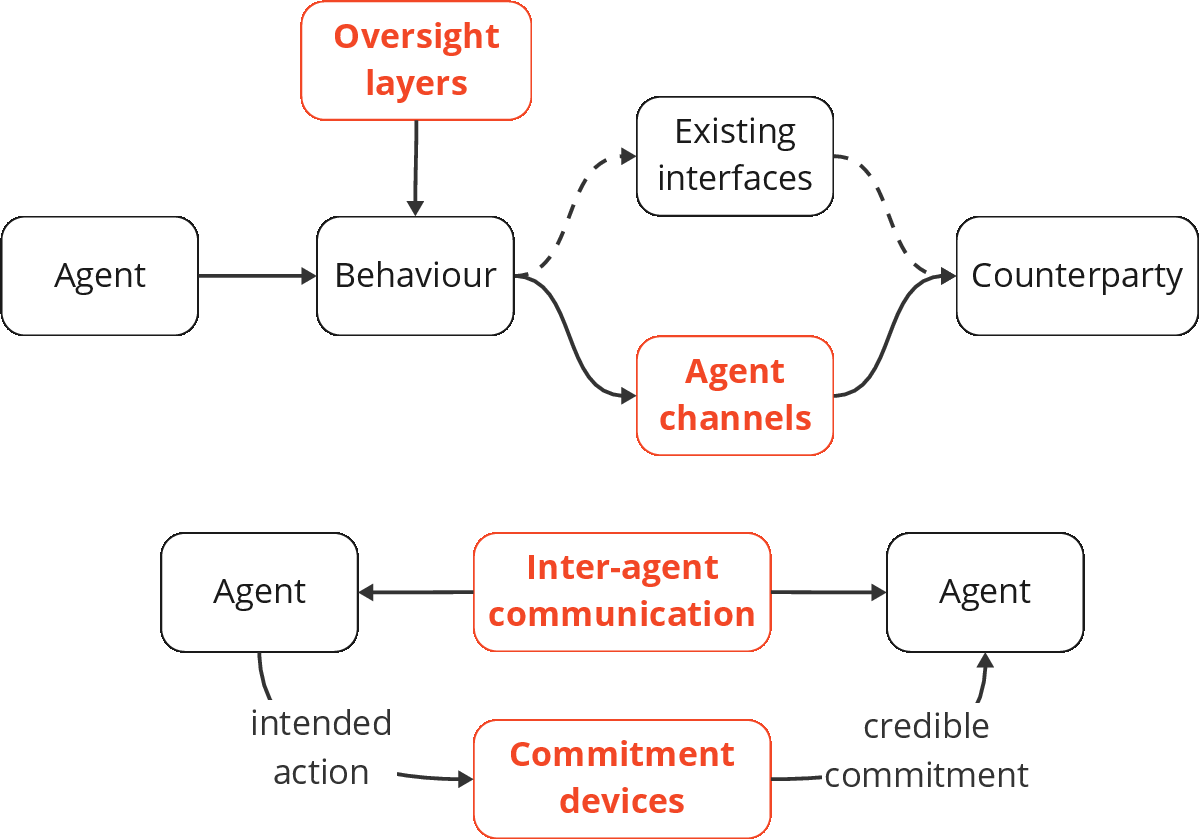
Figure 3: Response infrastructure for agent ecosystems including incident reporting pipelines and rollback pathways.
Implementation Trade-offs, Risks, and Open Problems
The authors document several recurrent and poorly resolved challenges across all proposed strata of agent infrastructure:
- Interoperability: Adoption of mutually incompatible protocols, certificates, and agent ID schemes can yield anti-competitive fragmentation and walled gardens, potentially requiring exogenous policy or regulatory interventions.
- Usability: Poorly designed or high-friction agent infrastructure risks circumvention, suboptimal adoption, and increased risk surface.
- Lock-In and Upgradability: Strong network effects in adopted protocols can inhibit critical updates or safety improvements, exemplified by the trajectory of network protocols like BGP and PKI.
- Security: All attribution and interaction mechanisms are subject to sophisticated adversarial exploitation, e.g., certificate authority compromise, subverted agent IDs, and Sybil attacks. These risks are exacerbated by the inherent distributed, compositional, and copyable nature of software agents.
- Privacy and Power Concentration: Attribution and monitoring infrastructure, while facilitating recourse, can centralize sensitive information and potentially empower intermediaries or authorities to exert disproportionate control or surveillance.
Societal and Theoretical Implications
For practitioners, the paper provides actionable conceptual blueprints for engineering safety, trust, and accountability into agentic digital ecosystems. Building agent infrastructure with formal linkages to legal, social, and economic frameworks will be essential as agents mediate larger swathes of commercial, governmental, and personal activity.
For theorists, the framing encourages research into incentive alignment and regulatory design that extends beyond system-level control to embrace network, protocol, and market-level governance, analogously to questions in Internet architecture, financial regulation, and institutional economics.
The infrastructure approach is explicitly not a complete solution—e.g., it does not resolve all liability allocation problems, nor can it, in isolation, address broad economic disruptions such as unemployment. Rather, it is best viewed as enabling substrate for (and subject to) higher-level legal, regulatory, and sociotechnical policies.
Conclusion
The paper foregrounds agent infrastructure as a necessary and complementary pillar to system-level technical interventions for governing agentic AI. The threefold taxonomy—attribution, interaction, and response—organizes both existing and novel infrastructural mechanisms, enables finer-grained accountability and recourse, and highlights new vectors for institutional evolution and technical research. The further development of agent infrastructure will require sustained cross-sector collaboration, strong emphasis on interoperability and usability, and ongoing adaptation to the evolving threat and opportunity landscape of general-purpose agentic AI.
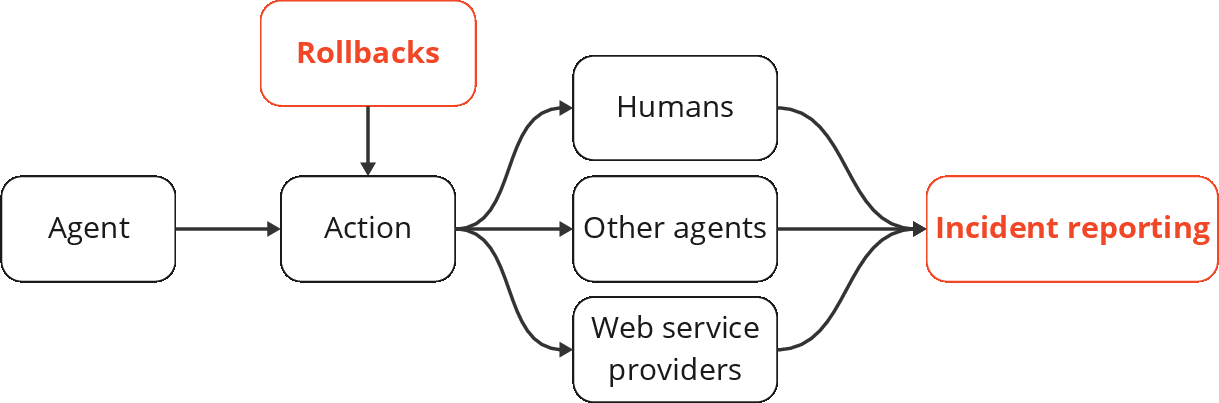
Figure 4: The infrastructure stack for agent-mediated digital environments, with interdependencies and cross-cutting implementation challenges highlighted.