- The paper presents a novel zero-trust IAM framework leveraging DIDs and VCs to dynamically authenticate and authorize AI agents.
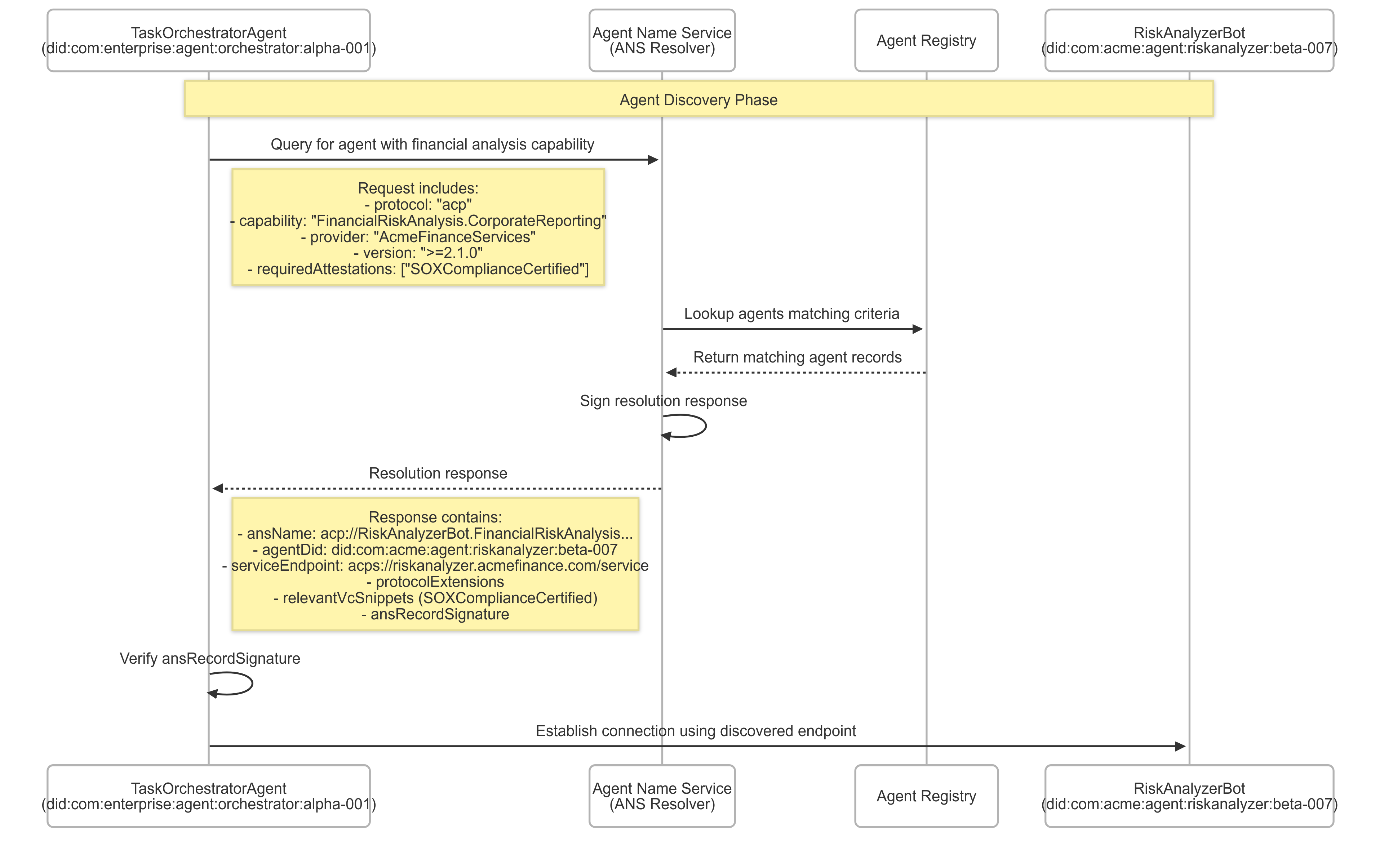
- It introduces an Agent Naming Service (ANS) and employs Zero-Knowledge Proofs to support confidential, capability-based agent discovery.
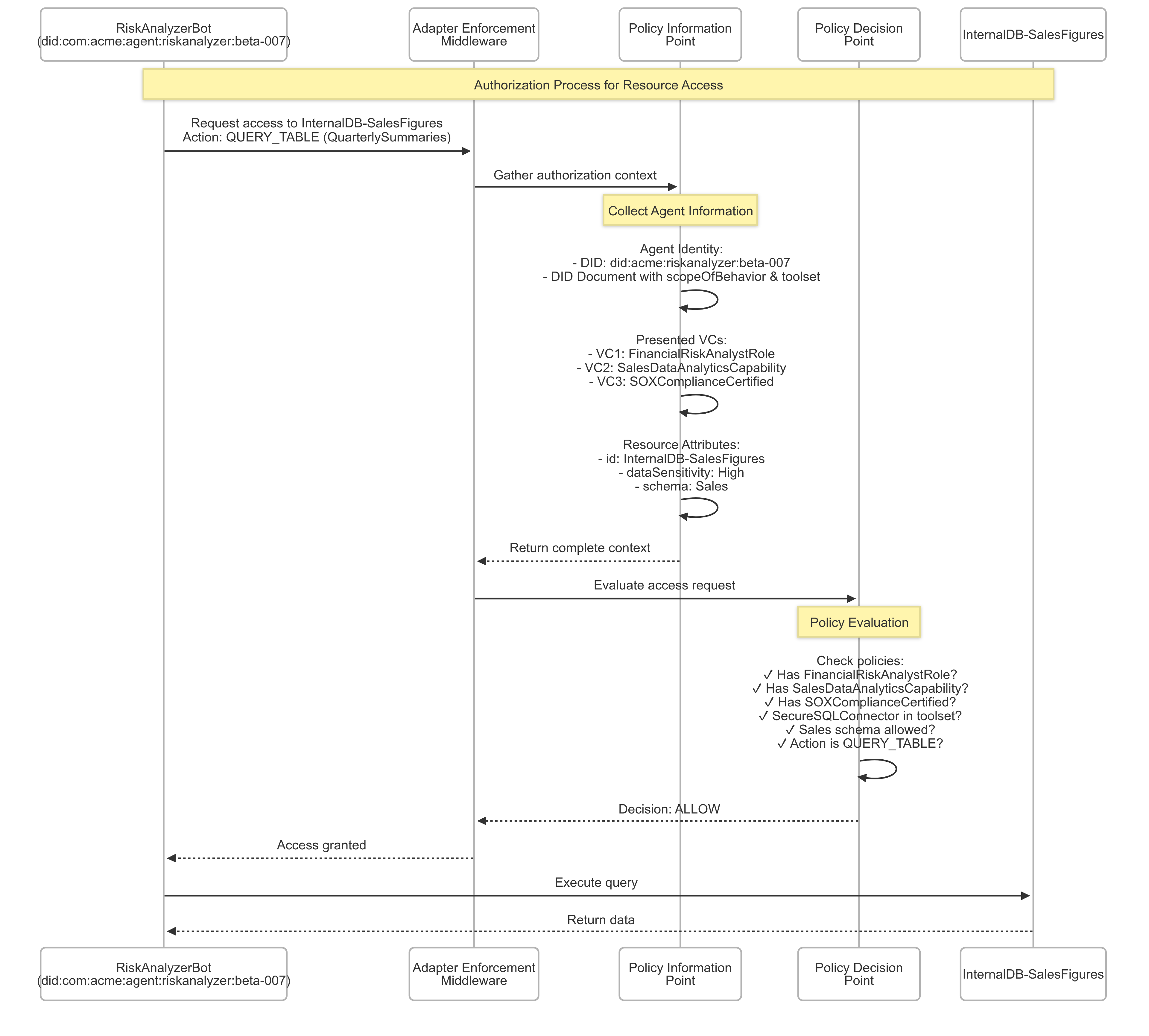
- The framework implements layered, dynamic access control combining static policies with context-aware enforcement to mitigate over-privileging.
A Novel Zero-Trust Identity Framework for Agentic AI: Decentralized Authentication and Fine-Grained Access Control
Introduction to Agentic AI and Identity Management
The transition to a world populated by autonomous Multi-Agent Systems (MAS) necessitates the development of an Identity and Access Management (IAM) framework fundamentally different from the traditional human-centered models. Traditional protocols such as OAuth 2.0, OpenID Connect (OIDC), and SAML are designed for static human users or simple machine identities and are unable to cater to the dynamic, ephemeral, and interdependent nature of AI agents in MAS. The paper proposes a novel IAM framework that utilizes Decentralized Identifiers (DIDs) and Verifiable Credentials (VCs) to encapsulate agent capabilities, provenance, and security postures. This enables the creation of sophisticated, fine-grained access control mechanisms crucial for secure agent interactions.
Architectural Framework and Key Features
The proposed framework integrates multiple technological advancements:
- Decentralized Identifiers (DIDs) and Verifiable Credentials (VCs): Leveraging DIDs provides globally unique and verifiable identities for agents. VCs allow for granular proof of an agent's attributes and capabilities, supporting dynamic updating and revocation as agent's capabilities evolve.
- Agent Naming Service (ANS): This service allows secure discovery of agents based on capabilities rather than names alone. ANS integrates with agent identities to ensure secure, capability-aware discovery processes.
- Zero-Knowledge Proofs (ZKPs): ZKPs are utilized to enable agents to verify credentials without disclosing sensitive information, enabling private and secure exchanges.
- Unified Global Session Management and Policy Enforcement: A session authority layer oversees policy enforcement and manages global logout mechanisms across heterogeneous communication protocols within MAS, ensuring consistent security posture throughout agent interactions.

Figure 1: Core Architecture and its layers.
Agent Identity and Lifecycle Management
The redefinition of an AI agent's identity is central to this framework. An agent's identity is a dynamic and cryptographically secured profile composed of:
- Cryptographic Anchor: Comprising a DID and associated key pairs for signing actions and encrypting communications.
- Core Attributes: Identifying information such as software version, creator, lifecycle status, and other metadata.
- Capabilities and Scope: Task-specific permissions and toolsets are specified to provide granular control over agent operations.
- Operational and Security Parameters: Communication protocols supported and any compliance or regulatory information pertinent to the agent's operations.
Additionally, agent identities can be dynamically adapted at runtime to enable specific task roles via ephemeral IDs or scoped VCs, allowing precise and flexible access control based on context and operational needs.
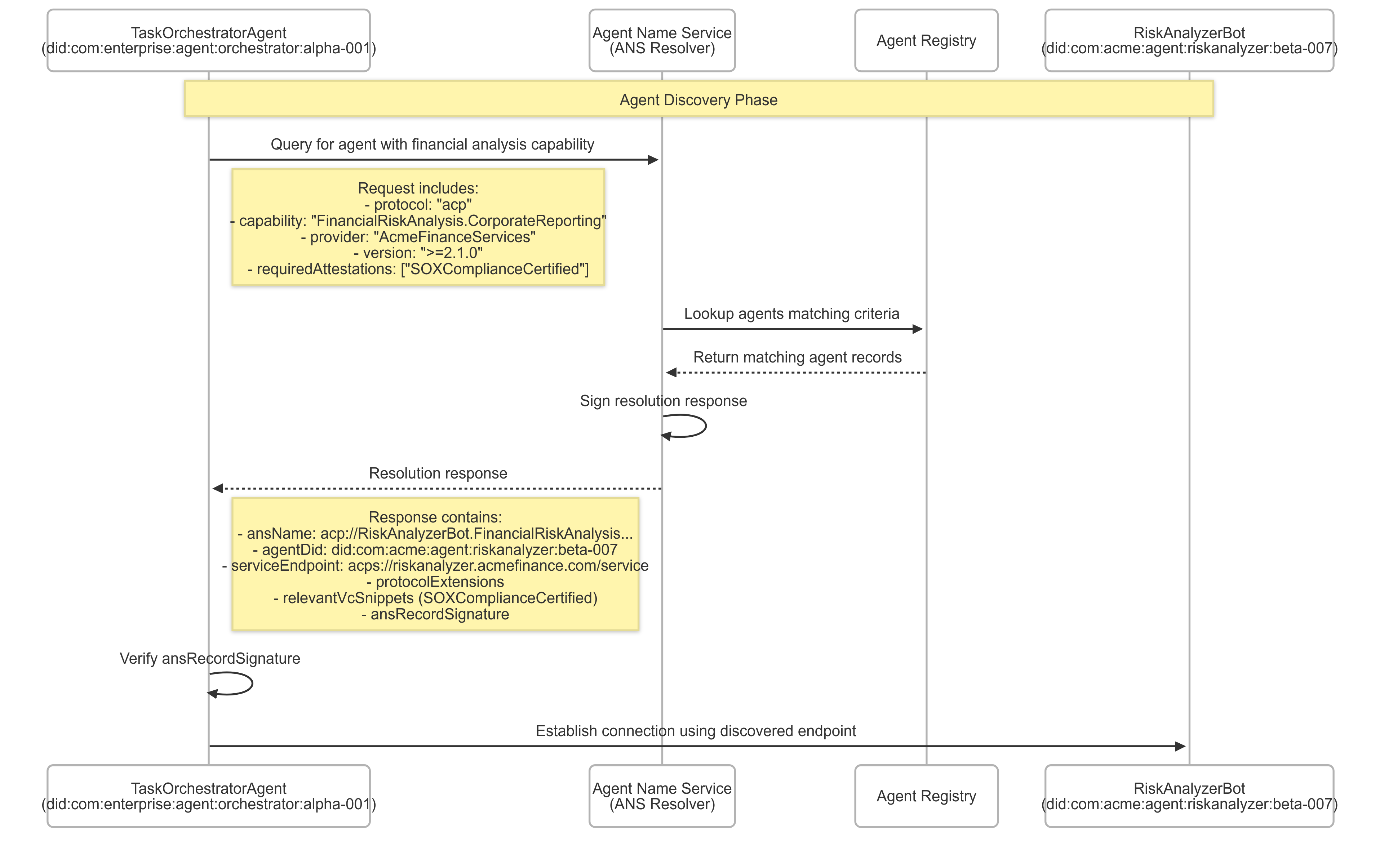
Figure 2: Agent discovery process using the Agent Name Service (ANS).
Implementing Fine-Grained Access Control
The framework employs a layered access control model that integrates static policies, dynamic conditions, and agent-specific attributes to govern decisions:
Implications and Future Work
The proposed framework sets the stage for more secure, efficient, and scalable AI ecosystems by addressing the unique identity challenges of AI agents. Future developments will focus on enhancing scalability, optimizing cryptographic operations, formalizing interoperability standards, and establishing robust governance models.
Potential research areas include leveraging advanced privacy-enhancing technologies, increasing inter-agent interoperability, and ensuring compliance with evolving regulatory landscapes. Comprehensive benchmarking and the development of developer-friendly tools will support broad adoption and facilitate seamless integration into existing IAM infrastructures.
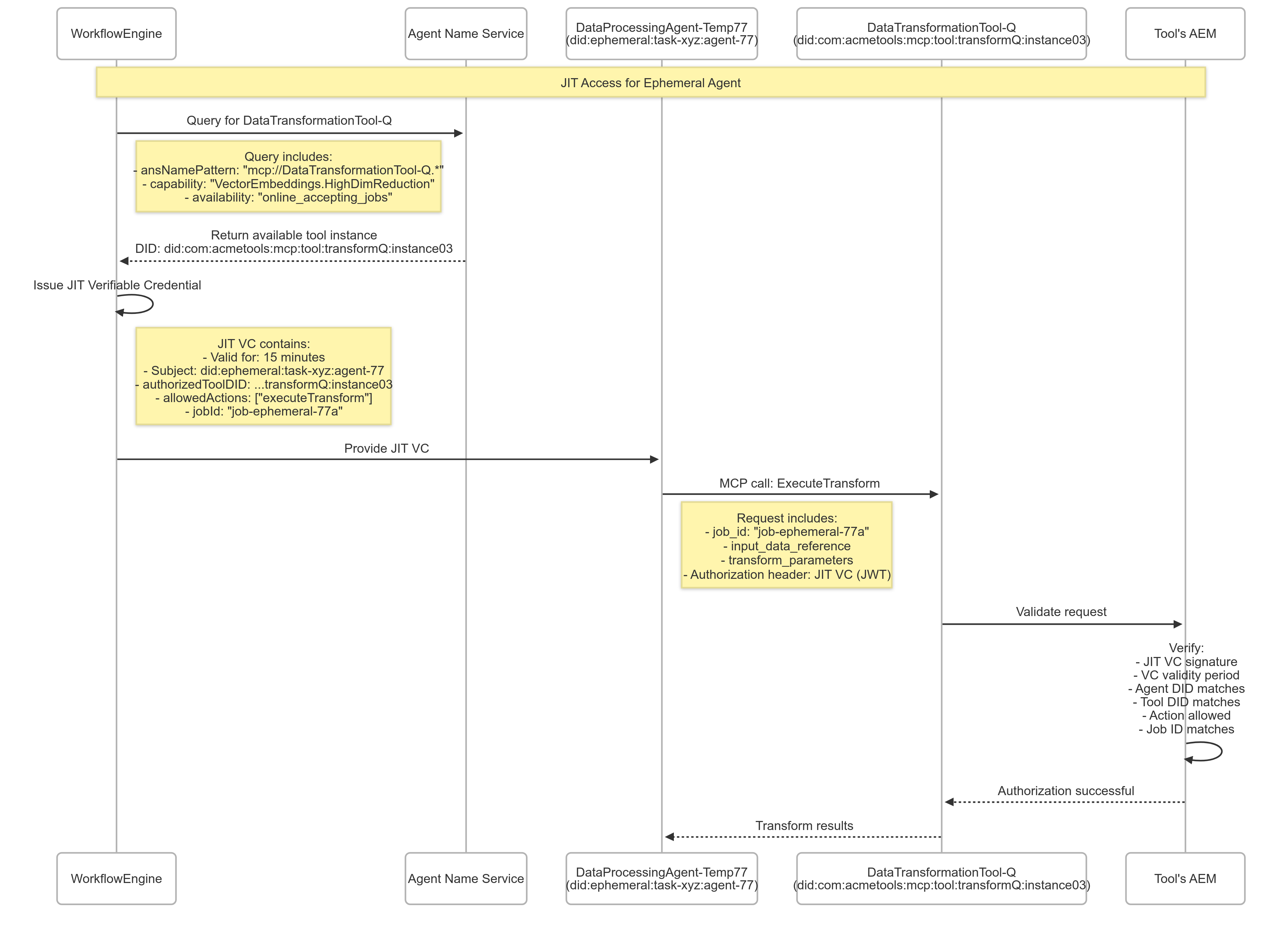
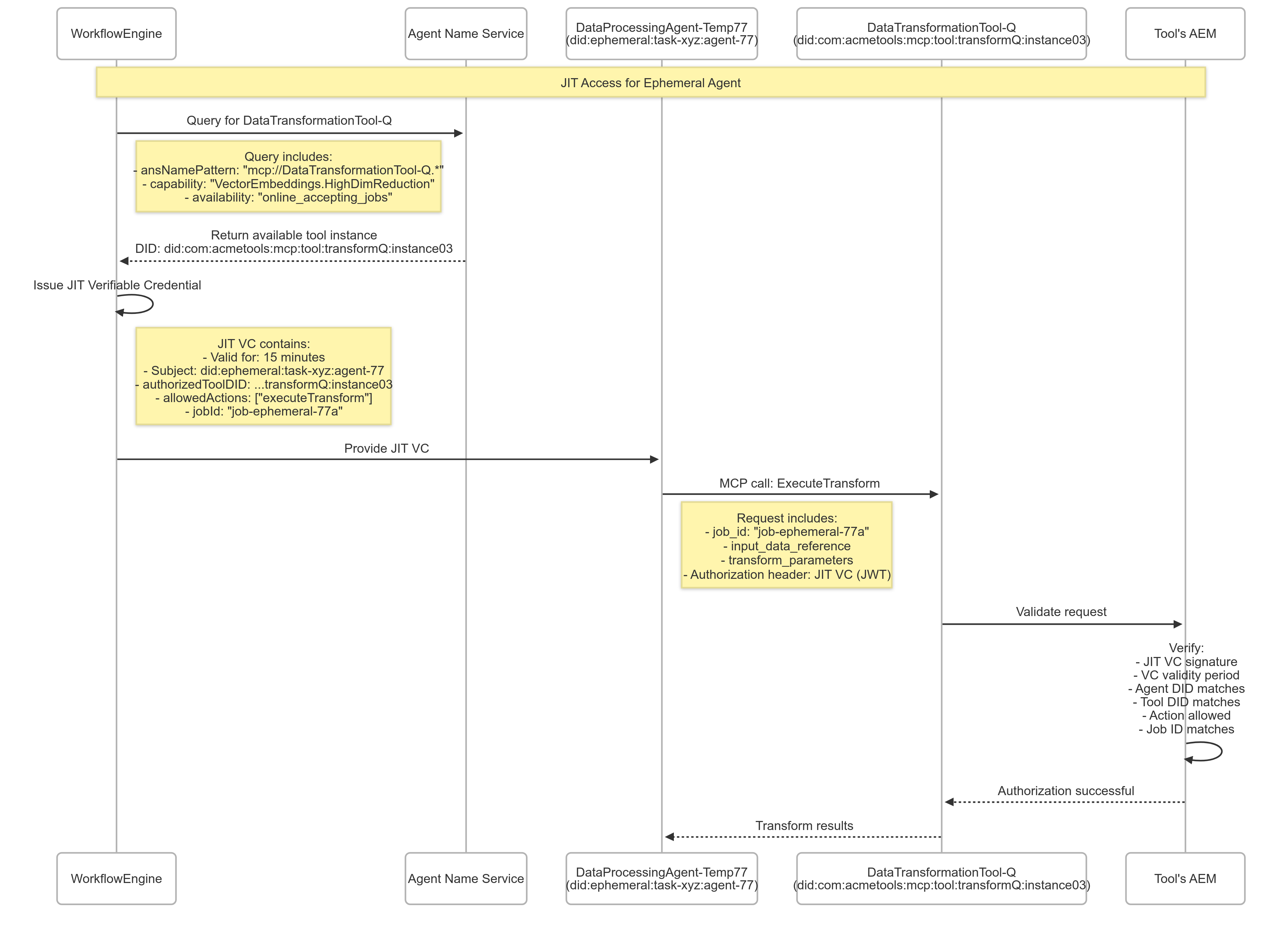
Figure 4: Ephemeral agent authorization using Just-In-Time (JIT) Verifiable Credentials for Model Context Protocol (MCP) tool access.
Conclusion
This paper presents a sophisticated IAM framework that empowers Agentic AI to operate securely within complex, interdependent ecosystems. By redefining identity through DIDs and VCs, instituting an Agent Naming Service for capability discovery, and proposing a forward-thinking architectural framework, it paves the way for secure and accountable agent interactions, advancing the capabilities of AI-driven systems in diverse applications. The innovative blend of technology and security considerations addresses critical shortcomings of existing IAM systems, underlining the necessity for such advancements to safely scale autonomous AI systems.