Using the NANDA Index Architecture in Practice: An Enterprise Perspective
Abstract: The proliferation of autonomous AI agents represents a paradigmatic shift from traditional web architectures toward collaborative intelligent systems requiring sophisticated mechanisms for discovery, authentication, capability verification, and secure collaboration across heterogeneous protocol environments. This paper presents a comprehensive framework addressing the fundamental infrastructure requirements for secure, trustworthy, and interoperable AI agent ecosystems. We introduce the NANDA (Networked AI Agents in a Decentralized Architecture) framework, providing global agent discovery, cryptographically verifiable capability attestation through AgentFacts, and cross-protocol interoperability across Anthropic's Modal Context Protocol (MCP), Google's Agent-to-Agent (A2A), Microsoft's NLWeb, and standard HTTPS communications. NANDA implements Zero Trust Agentic Access (ZTAA) principles, extending traditional Zero Trust Network Access (ZTNA) to address autonomous agent security challenges including capability spoofing, impersonation attacks, and sensitive data leakage. The framework defines Agent Visibility and Control (AVC) mechanisms enabling enterprise governance while maintaining operational autonomy and regulatory compliance. Our approach transforms isolated AI agents into an interconnected ecosystem of verifiable, trustworthy intelligent services, establishing foundational infrastructure for large-scale autonomous agent deployment across enterprise and consumer environments. This work addresses the critical gap between current AI agent capabilities and infrastructure requirements for secure, scalable, multi-agent collaboration, positioning the foundation for next-generation autonomous intelligent systems.
Paper Prompts
Sign up for free to create and run prompts on this paper using GPT-5.
Top Community Prompts
Knowledge Gaps
Knowledge gaps, limitations, and open questions
Below is a single, concrete list of unresolved issues that future researchers could address to strengthen and operationalize the NANDA framework and its enterprise use:
- Formalize the AgentFacts schema: define required/optional fields, canonical capability descriptors, versioning, extension mechanisms, and validation rules to ensure consistent cross-agent interpretation.
- Specify how “claimed vs actual” capabilities are attested: design dynamic capability attestation (e.g., challenge–response, remote attestation) and continuous verification beyond static credentials.
- Develop a rigorous threat model for agent ecosystems: enumerate attack surfaces (index poisoning, adapter exploits, protocol downgrade, semantic authorization bypass) and map defenses to specific adversary capabilities.
- Detail bootstrapping trust for “Newly Seen Agents” (NSAs): propose concrete risk mitigation policies (quarantine, probationary caps, reputation seeding, rate limits, supervised workflows) and decision algorithms.
- Provide scalability and performance designs for a global NANDA Index: replication strategy, sharding/partitioning, eventual consistency, Anycast routing, caching, and query latency targets under realistic load.
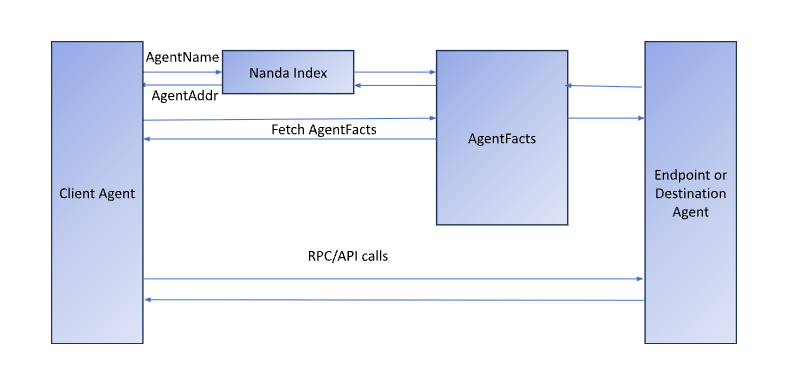
- Define name-to-agent addressing and resolution semantics: how agent identifiers (DIDs, URLs) map to endpoints across MCP/A2A/NLWeb/HTTPS, including fallback, aliasing, and resolution failure handling.
- Establish governance for credential issuers and cross-signing trust zones: admission criteria, audit regimes, revocation policies, dispute resolution, and mechanisms to prevent collusion or issuer cartels.
- Clarify revocation and key management workflows: DID rotation, credential expiry, VC-Status-List propagation latencies, rollback procedures, and recovery after compromised private keys.
- Design a portable policy language for ZTAA: formal syntax/semantics, composability (enterprise, departmental, personal policies), conflict resolution, and machine-checkable enforcement artifacts.
- Integrate ZTAA with enterprise IAM and posture assessment: methods for agent MFA, device/agent posture attestation, SBOM/SLSA checks, and alignment with existing zero-trust stacks (e.g., ZTNA).
- Specify least-privilege context sharing: define granular scopes, resource capabilities, consent flows, and standard authorization semantics analogous to OAuth/OpenID but tailored to agents.
- Address privacy and data protection in AgentFacts and logs: minimization, linkability risks, use of selective disclosure/zero-knowledge proofs, GDPR-compliant retention/deletion, and cross-jurisdiction data flows.
- Standardize “Agentic SafeSearch” taxonomies: create shared, verifiable safety labels (e.g., political, adult, medical), handle cultural/regional differences, and measure false positive/negative rates.
- Design robust reputation systems: Sybil resistance, weighting of issuer credibility, game-theoretic manipulation defenses, fairness across domains, transparency of scoring, and calibration benchmarks.
- Provide formal security assurances: proofs or model checking showing that bilateral authentication, capability filtering, and adapter mediation prevent spoofing, reflection, amplification, and privilege escalation.
- Define interoperability semantics across MCP/A2A/NLWeb: capability mapping, context translation, error handling, transactional guarantees, and resolution of semantic mismatches during protocol translation.
- Analyze adapter security: how protocol translation preserves authorization scopes and context boundaries; mitigations for semantic drift that could elevate privileges or leak data.
- Specify monitoring, logging, and audit requirements: standard log schema, tamper-evident records, secure time-stamping, redaction policies, and forensics workflows that balance compliance and privacy.
- Operationalize DLP for agent-to-agent traffic: content classification methods, encryption-aware inspection, policy-triggered transformations (masking, tokenization), and performance impacts.
- Define lifecycle management for agents: provisioning, versioning, migration, provenance tracking, deprecation/retirement, and continuity of identity/capabilities across updates.
- Clarify multi-tenancy and isolation: cross-organization boundaries, tenancy-aware discovery and policy enforcement, side-channel risks, and noisy-neighbor effects in shared infrastructures.
- Provide concrete compliance enforcement mappings: translate OFAC sanctions, GDPR obligations, geofencing, and sectoral regulations into NANDA policies and demonstrate automated enforcement.
- Address NANDA Index security and resilience: access controls, rate limiting, DoS/DDoS defenses, integrity protections against data corruption/poisoning, and disaster recovery plans.
- Specify cryptographic primitives and hardware trust anchors: recommended algorithms, key sizes, HSM/TEE use, remote attestation protocols, and interoperability with existing PKI/DID stacks.
- Develop evaluation methodologies and benchmarks: empirical measurements of discovery accuracy, latency, throughput, security incident prevention rates, and end-to-end success in enterprise workflows.
- Offer reference implementations and testbeds: open-source adapters, sample agents, conformance suites, and interop labs to validate cross-protocol operation under real-world constraints.
- Address economics and incentives: cost of credential issuance/maintenance, funding models for index operation, preventing pay-to-play bias in reputation, and sustainability of third-party attestors.
- Plan for offline/asynchronous agents: delayed discovery/attestation, message queueing, eventual reconciliation, and policy enforcement when real-time verification is unavailable.
- Define policy conflict resolution between personal and enterprise agents: precedence rules, consent mechanisms, and escalation paths when policies or safety requirements diverge.
- Clarify legal liability and contract enforcement: non-repudiation mechanisms, signed task receipts, accountability chains among agent owners, issuers, and index operators.
Practical Applications
Immediate Applications
Below are concrete, deployable use cases that can be adopted now by enterprises, researchers, public sector teams, and end users. Each item notes sectors and likely tools/products/workflows, plus key dependencies.
- Enterprise agent registry and discovery hub
- Sector: Software/IT, Enterprise Security
- What: Stand up an internal NANDA Index instance as a single source of truth for agent identities, capabilities, and trust metadata; onboard internal/external agents; expose REST API + web UI to product teams.
- Tools/workflows: NANDA Index (REST + UI, Google OAuth), CRUD onboarding, capability tagging with AgentFacts, internal change-control workflow.
- Dependencies: Availability of NANDA Index deployment; basic PKI and identity; initial AgentFacts metadata from owners or trusted issuers.
- Cross-protocol agent bridging for existing apps
- Sector: Software, Productivity, CRM/ERP
- What: Use the NANDA Adapter to let MCP-based assistants call A2A or NLWeb agents (e.g., MCP assistant orchestrates NLWeb calendar and A2A inventory).
- Tools/workflows: MCP/A2A/NLWeb protocol adapters, HTTPS fallbacks, connector catalog.
- Dependencies: Stable endpoints for target agents; adapter coverage for chosen protocols; network egress controls.
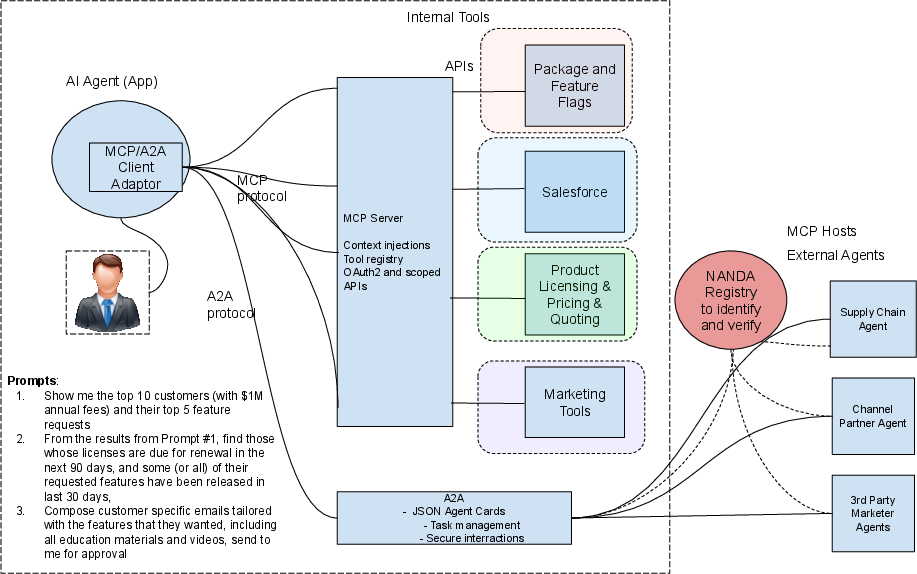
- Sales and marketing orchestration (paper’s exemplar)
- Sector: Enterprise SaaS (Sales/Marketing/RevOps)
- What: Orchestrate agents for Aha! features, Salesforce CRM, pricing/licensing, and email campaigns to auto-generate targeted outreach, POCs, and collateral.
- Tools/workflows: MCP/A2A agents for CRM/PLM/tools, LLM summarization, policy-check via NANDA before contacting external agents.
- Dependencies: API access to owned systems; basic SafeSearch policies; human-in-the-loop sign-off for outbound communications.
- Agentic SafeSearch enforcement
- Sector: Enterprise Security, Education, Consumer Safety
- What: Translate safety policies into NANDA search filters (e.g., requires_cert=kid-safe-cert-v1; exclude_flags=political) before any inter-agent call.
- Tools/workflows: NANDA /search API with AgentFacts trust_certifications, reputation_scores, content_flags; policy templates by audience.
- Dependencies: Availability of signed certifications; reputation feeds from third parties; policy authoring by IT/Admin.
- Zero Trust Agentic Access (ZTAA) policies at the edge
- Sector: Security (ZTNA/ZTAA), Network/Cloud
- What: Gate outbound/peer agent calls by identity, capability attestation, geography, and reputation score; treat “Newly Seen Agents” with quarantine or reduced privileges.
- Tools/workflows: Policy engine leveraging NANDA queries; DLP inspection on agent payloads; allow/deny lists, mTLS/TLS; least-privilege context templates.
- Dependencies: AgentFacts verifications; DLP stack; SIEM/SOAR for alerting; enterprise identity posture.
- Agent Visibility and Control (AVC) for oversight, billing, and audits
- Sector: IT Operations, FinOps, Compliance
- What: Track agent identity, tasks, timestamps, and durations; expose dashboards for pause/disable; generate chargeback and compliance reports.
- Tools/workflows: AVC dashboards, log pipelines to SIEM; export to billing/ERP; kill-switch operations.
- Dependencies: Standardized activity logs; time and usage metrics; access controls for administrators.
- Compliance gating (OFAC/GDPR) for agent interactions
- Sector: Finance, Public Sector, Global Enterprises
- What: Filter agent targets by sanctioned entities/regions; apply data residency and consent checks before data sharing.
- Tools/workflows: NANDA filters by geography/trust zones; audit logging; policy packs for OFAC/GDPR.
- Dependencies: Up-to-date sanctions lists; data classification labels; legal sign-off.
- Internal marketplace of vetted agents
- Sector: Procurement, App Marketplaces, Enterprise Platforms
- What: Curate a catalog of pre-approved agents with verifiable capabilities, certifications, and reputation scores; one-click registration/consumption.
- Tools/workflows: NANDA-backed catalog UI; approval workflows; versioning and revocation via VC-Status-List.
- Dependencies: Review board to issue approvals; VC issuance and revocation hygiene.
- Third-party certification and reputation services
- Sector: Security/Compliance Vendors, Auditing
- What: Launch services that issue W3C VC v2 credentials (e.g., HIPAA-ready, kid-safe, SOC 2 posture) and reputation scores attached to AgentFacts.
- Tools/workflows: VC issuance pipelines; DID methods; periodic posture assessments; revocation lists.
- Dependencies: Broad acceptance of VC/DID; agreed taxonomies; liability frameworks for attestations.
- SOC integration for agent traffic and actions
- Sector: Security Operations
- What: Ingest AVC logs into SIEM; alert on policy violations, unusual agent-to-agent patterns, and NSA interactions.
- Tools/workflows: Log forwarders; correlation rules; playbooks for isolate/rollback.
- Dependencies: Consistent, signed logs; time sync; SOC runbooks for agent incidents.
- Data loss prevention for agent contexts
- Sector: Healthcare, Finance, Enterprise IT
- What: Apply DLP and redaction on prompts/responses before external agent calls; enforce least-privilege context sharing.
- Tools/workflows: Context sanitization middleware; PII/PHI detectors; policy tags in AgentFacts (e.g., HIPAA-compliant).
- Dependencies: Accurate data classification; performant in-line filtering; exception handling.
- Developer toolchain integration for auto-registration and checks
- Sector: Software Engineering
- What: Client libraries/CI steps to auto-register agents with the NANDA Index and validate dependencies’ credentials before release.
- Tools/workflows: SDKs for MCP/A2A/NLWeb; pre-deploy “capability attestation” checks; SBOM-like AgentFacts manifests.
- Dependencies: Maintained SDKs; developer policy adoption; pipeline permissions.
Long-Term Applications
These opportunities are plausible but depend on maturation of standards, scaling of infrastructure, or broader ecosystem and regulatory buy-in.
- Federated, cross-signed global agent identity and trust networks
- Sector: Internet Infrastructure, Standards
- What: Interoperable trust zones with cross-signing between industries and regions; universal discovery with portable credentials.
- Dependencies: W3C VC v2 and DID method convergence; cross-signing governance; global revocation and audit norms.
- Autonomous inter-enterprise workflows (supply chain to settlement)
- Sector: Manufacturing, Retail, Logistics, Finance
- What: Vendor–buyer agents negotiate terms, check compliance (OFAC/GDPR), orchestrate fulfillment, and trigger automated payments.
- Dependencies: Standardized capability schemas; liability frameworks; payment rails integration; robust reputation systems.
- Regulated-sector agent ecosystems
- Sector: Healthcare, Finance, Energy, Public Sector
- What: HIPAA-attested clinical agents exchanging EHR data; KYC/AML-attested trading agents; grid-balancing energy agents.
- Dependencies: Sector-specific certifications embedded as VCs; regulator acceptance; auditability and incident response protocols.
- Agent liability, warranties, and insurance underwriting
- Sector: Insurance, LegalTech
- What: Use AVC logs, reputation, and certifications to price risk and offer agent liability coverage and warranties.
- Dependencies: Legal standards for agent accountability; forensic-quality logs; actuarial models for agent risk.
- Consumer “agent OS” for homes and families
- Sector: Consumer Tech, Education, Smart Home
- What: A home gateway implementing ZTAA + SafeSearch; manages kid-safe certifications; mediates smart device and web agent interactions.
- Dependencies: Affordable, user-friendly appliances; simplified policy UX; sustained issuer ecosystem for family-safety credentials.
- Robotics/IoT cross-protocol control via certified agents
- Sector: Robotics, Industrial IoT, Warehousing
- What: Safety-certified agents mediate commands between enterprise planners and robots across heterogeneous protocols.
- Dependencies: Safety standards for agent mediation; real-time guarantees; hardware vendor participation.
- Agent billing and settlement rails
- Sector: FinTech, Cloud Platforms
- What: Metered, auditable micro-billing based on AVC usage data; cross-organization settlement; per-capability pricing.
- Dependencies: Standard metering formats; payment integration; dispute resolution processes.
- National/sector registries and mandated audits
- Sector: Policy/Regulation
- What: Government or industry bodies require registration of agents operating in critical domains; integrate with NANDA-compatible indices.
- Dependencies: Legislation; privacy safeguards; public–private governance models.
- Standardized reputation schemas and Sybil-resistant scoring
- Sector: Security, Marketplaces
- What: Shared, tamper-resistant reputation metrics for agents (reliability, safety, fairness), portable across platforms.
- Dependencies: Anti-Sybil mechanisms; data-sharing agreements; incentive alignment to prevent gaming.
- Privacy-preserving attestation (e.g., ZK proofs over AgentFacts)
- Sector: PrivacyTech, IP-heavy industries
- What: Prove compliance or capabilities without revealing proprietary details using zero-knowledge methods.
- Dependencies: Practical ZK protocols for complex claims; verifier adoption; performance optimizations.
- Edge and air-gapped deployments with periodic trust sync
- Sector: Defense, Critical Infrastructure
- What: On-prem/fog NANDA mirrors for disconnected environments; scheduled sync of revocation and certifications.
- Dependencies: Offline-first VC stacks; secure sync channels; watchlist propagation.
- Evidentiary chains for legal/compliance proceedings
- Sector: LegalTech, Compliance
- What: Notarized, time-stamped AVC records (e.g., anchored to trusted ledgers) to establish chain-of-custody for agent decisions.
- Dependencies: Standards for admissibility; tamper-evident logging; retention and privacy policies.
- Adapter marketplaces and runtime standardization
- Sector: Developer Platforms, Cloud
- What: Commercial ecosystems of protocol adapters, policy packs, and monitoring modules that snap into NANDA-compatible runtimes.
- Dependencies: Stable protocol baselines (MCP/A2A/NLWeb); versioning and certification programs for adapters.
Notes on common assumptions and dependencies
- Cryptographic identity and claims: Broad adoption of W3C Verifiable Credentials v2, DID resolution, and VC-Status-List for revocation is pivotal for AgentFacts integrity.
- Protocol maturity: Continued stabilization and support for MCP, A2A, NLWeb, and HTTPS-based agent patterns.
- Governance: Clear cross-signing rules, trust-zone governance, and standardized taxonomies (capabilities, safety categories, reputation metrics).
- Security stack: DLP, SIEM/SOAR, least-privilege context controls, and hardened defenses against prompt injection and data poisoning.
- Legal/regulatory alignment: Sector-specific compliance (OFAC, GDPR, HIPAA, KYC/AML) encoded as enforceable policies and auditable logs.
- Ecosystem services: Emergence of independent certification authorities, reputation providers, and red-teaming/evaluation services to enrich AgentFacts.
Collections
Sign up for free to add this paper to one or more collections.